Improving Classical Authentication with Quantum Communication
We propose a quantum-enhanced protocol to authenticate classical messages, with improved security with respect to the classical scheme introduced by Brassard in 1983. In that protocol, the shared key is the seed of a pseudo-random generator (PRG) and…
Authors: F. M. Assis, P. Mateus, Y. Omar
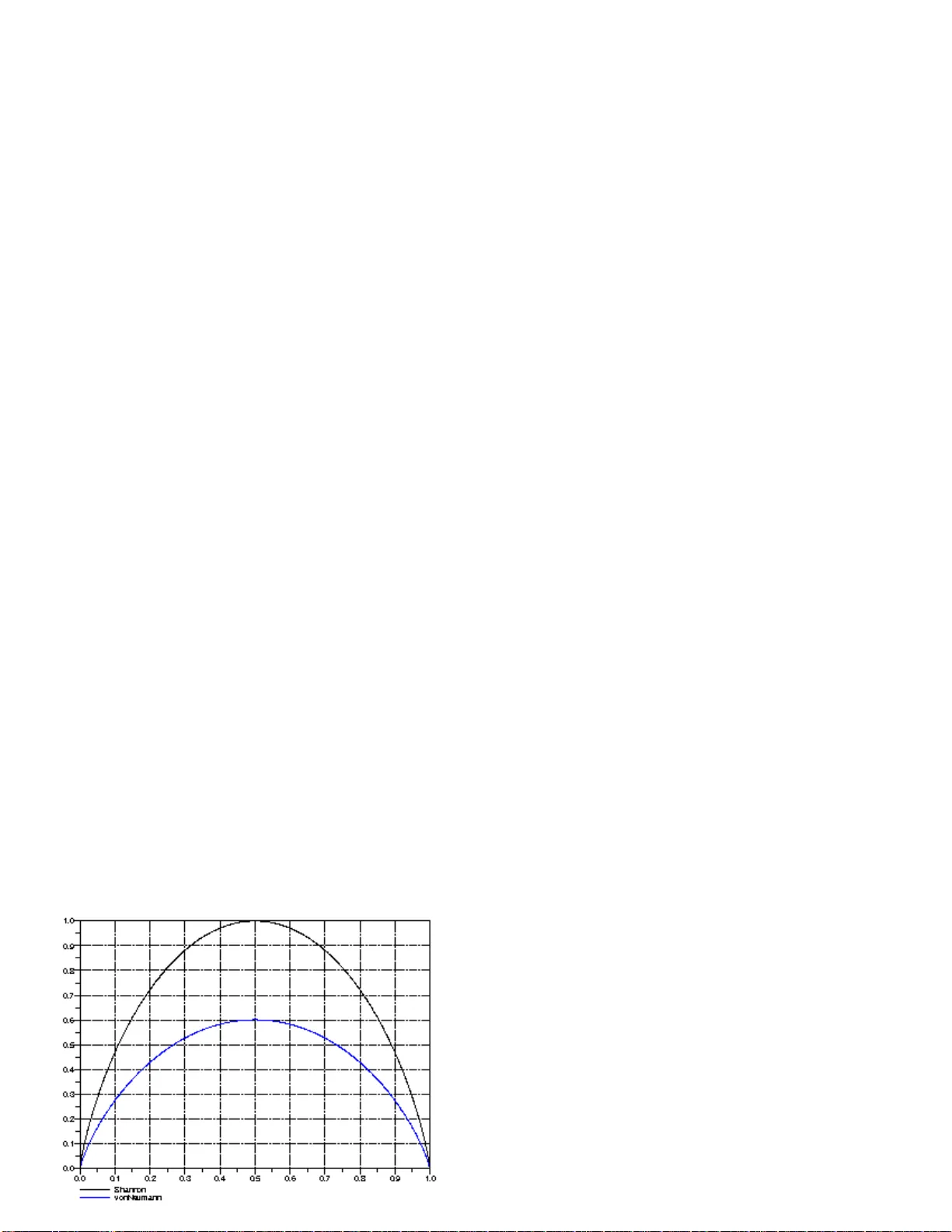
Impro ving Classical Authen tication with Quan tum Comm unication F. M. Assis Dep artament of Ele ctric al Engine ering UFCG, Universidade F e der al de Cam p ina Gr ande , Br azil P . Mateus IST, T e chn ic al University of Lisb on, P-1040-001 Lisb on, and S QIG, Instituto de T ele c omunic a¸ c˜ oes, P-1049-001 Lisb on, Portugal Y. Omar CEMAPRE, ISEG, Universidade T´ ecnic a de Lisb o a, P-1 200-781 Lisb on, and SQIG, Instituto de T ele c omunic a¸ c˜ oes, P-104 9 -001 Lisb on , Portugal (Dated: 11 F ebruary 2010) Abstract W e prop ose a quantum-enhanced proto col to authentica te classical messages, with improv ed securit y with resp ect to the classical sc heme in tro d u ced b y Brassard in 1983 . In that p roto col, th e shared ke y is the seed of a pseudo-rand om generator (PRG) and a hash f unction is used to create the authenti cation tag of a pub lic message. W e sho w that a qu an tum enco din g of secret bits offers more secur it y than the classical X OR fun ction introd u ced by Brassard. F ur thermore, w e establish the relationship b etw een the bias of a PR G and the amoun t of information ab out the k ey th at the attac ker can retriev e from a blo c k of authentic ated messages. Finally , we p ro v e that quantum resources ca n impro ve b oth the secrecy of the ke y generated by the PRG and the secrecy of the tag obtained with a hidden hash f u nction. 1 I. INTR ODUCT I ON The authen tication of public messages is a fundamen tal problem now adays for bipartite and net w ork communic atio ns. The scenario is the follo wing: Alice sends a (classical) message to Bob through a public channel, together with an authen tication ta g through a priv ate or public c hannel. The ta g will allo w Bob to v erify if t he message he receiv ed via the public c hannel has b een t amp ered with or if it is indeed the authen tic message, originally sen t by Alice. A third c hara cter, Ev e, w an ts to sab otage this sc heme b y in tercepting Alice’s message and sending her own message to Bob, tog ether with a false tag whic h will con vince Bob he is receiving the authen tic message. F or instance, one could imagine that Alice is sending to Bo b her bank accoun t n umber, to whic h Bo b will transfer some money , and Ev e w ants to in terfere in the comm unication in suc h a w a y that Bob will r eceiv e her bank accoun t n um b er b elieving it is Alice’s o ne, th us g iving his money to Ev e. The use of authen tication tags allo ws to separate t he secrecy problem in message transmission f r o m the authen tication problem and it is useful ev en if a secure comm unication channel is a v ailable [2]. In 1983, G. Brassard prop osed a computationally s ecure sc heme of classical a uthen tication tags based on the sharing of short secret ke ys [1]. Brassard’s sc heme is itself an impro v emen t of the W egman-Carter proto col [2]. Brassard show ed that a relativ ely short seed of a PRG can b e used as a secret k ey shared b etw een Alice and Bob whic h will allow the exc hange of computationally secu re authen tication tags. This metho d yields a mu ch mor e practical proto col, where the requiremen ts o n the seed length grow reasonably with the n um b er of messages we w ant to authen ticate, as o pp osed to the W egma n- Carter prop osal. The securit y o f PR Gs is based on the alleged hardness of some problems o f n um b er theory , e.g., the factorizatio n of a large n um b er with classical computers. Ho w ev er, sev eral of these problems are pro v a bly solv able if quan tum computers are a v a ilable. Consequen tly , the securit y of the PR Gs migh t b e compromised. Assuming Alice and Bob comm unicate quan tically , can Ev e ye t menacing the PRG securit y? This question is our main motiv ation to write t his article. In this w ork, w e extend Brassard’s proto col to include quan tum-enco ded authen tication tags, which w e prov e will offer, under certain conditions, informat io n-theoretical securit y for 2 the authen tication o f classical messages. W e observ e that our sc heme can authen ticate t he quan tum c hannel itself, whic h is a n imp ortant part of the quantum cryptograph y: in fact, it is the crucial first step of quan tum k ey distribution proto cols. I I. PRELIMINARIES In this section we set up basic notation, briefly review the description o f the Brassard’s proto col and describ e our new prop osal. W e conclude the section with a negativ e result on the robustness of an atta ck a ble PRG when its output is hidden b y a specific quan tum co ding. W e denote M the set of messages and T the set o f tags, where log |M| >> log |T | . As ha sh functions are an imp ortan t ingredien t for all proto cols describ ed here we start b y presen ting t heir formal definition [6]: Definition I I .1 ( ε − almost strongly univ ersal-2 hash functions) L et M and T b e finite sets and c al l functions fr om M to T hash functions. L et ε b e a p ositive r e al numb er. A se t H o f hash functions i s ε − almo s t str ongly universal-2 if the fol lowing two c ondition s ar e satisfie d 1) The numb er of ha sh functions in H that takes an arbitr ary m ∈ M to an arbitr ary t ∈ T is ex a ctly |H| / |T | . 2) The fr action of those functions that a l s o takes Y ′ 6 = Y in M to an arbitr a ry T ′ ∈ T (p os sibly e qual to T ) is no mor e than ε. The n um b er ε is related to the probability of guessing the correct tag with resp ect to a n arbitrary message Y . Notice that the smaller ε is, the larger is |H| . F or a dditional details X (n) X = {X i } Z = X T U (l) PRG h Alice XOR Public Channel Bob Eve Y T=h(Y) FIG. 1: Brassard’s classical authentic ation proto col [1] 3 on univ ersal-2 functions w e p oin t the reader to [2]. Brassard’s proto col (see Figure 1) mak es use of tw o secret k eys. The first one, U ( l ) , sp ecifies a fixed univ ersal-2 ha sh function h ∈ H , where l = ⌈ log |H|⌉ . The sec ond sp ecifies the seed X ( n ) ∈ Z n 2 , for a PRG, a sequ ence of n bits. The main ing redien t of our first quantum - enhanced proto col prop osed here (see Fig ure 2) is replacing the classical gate XOR o f Brassard proto col b y a quantum enco der similar to t ha t used in the BB84 proto col [11]. After some dev elopmen ts, w e shall v erify that the k ey U ( l ) is no lo nger necessary . Assume that Alice and Bob agree on tw o orthonormal bases B 0 and B 1 for the 2- dimensional Hilb ert space, B 0 = {| 0 i , | 1 i} and B 1 = | + i = 1 √ 2 ( | 0 i + | 1 i ) , |−i = 1 √ 2 ( | 0 i − | 1 i ) These bases will b e used to prepare fo ur quan tum states. W e shall r efer to this prepara tion pro cess as quantum c o ding . F or eac h bit of the k = ⌈ log | T | ⌉ bits long tag T Y = h ( Y ), Alice prepares a quan tum state | ψ i = | ψ i ( X i , ( T Y ) i ) determined b y the bit X i from the PR G and the corresp onding bit ( T Y ) i of 2-radix represen tation of the ta g T Y . Then, if the bit X i = 0 , Alice prepares | ψ i using basis B 0 , suc h tha t | ψ i = | 0 i if ( T Y ) i = 0 | 1 i if ( T Y ) i = 1 . (1) Similarly , if the bit X i = 1, Alice prepares | ψ i using basis B 1 , suc h that | ψ i = | + i if ( T Y ) i = 0 |−i if ( T Y ) i = 1 (2) After the qubits generatio n, Alice sends the separable state | ψ Y i ⊗ k to Bob through a noiseless quan tum c hannel and the message Y thro ug h an unauthen ticated classical c hannel. At the reception, Bob p erforms measuremen ts to obta in a sequence of k bits from the quan tum enco ded v ersion of h ( Y ) . F or the i -th receiv ed qubit, Bob measures it using the basis B 0 or B 1 dep ending on the i − th bit of X is 0 or 1, resp ectiv ely , reco v ering a k -bit long string T ′ = h ′ | ψ i ⊗ k . Because the quan tum c hannel is a ssumed to b e p erf ect, Bob recognizes that the message is authentic if h ′ = h ( Y B ), where Y B is the message receiv ed from the classical channel. Otherwise, Bob assumes that Ev e tried to send him an unauthen tic message. This concludes 4 the authen tication proto col for one message. Throughout this a rticle it is alwa ys assumed that the ab o v e co ding rule is public. Ev en though we assume a noise-free quantum c hannel, w e observ e that if the quan tum c hannel is noisy , the only piece of information requiring error-pro t ecting co ding is the blo ck of bits ( T Y ) i of the tag T Y . The sequence of ba ses to b e prepared by Alice and Bob is kno wn a priori, determined lo cally b y the sequence of bits fro m the PR G . A future task is ev aluating the effects of the utilization o f error-correcting co des to the bits of T Y . X (n) X = {X i } ψ i { } POVM U (l) PRG h Alice QC Classical Public Channel Eve Bob Y T = h(Y) FIG. 2: First prop osal of quantum-enhanced authen tication sc heme In a warning against alleged collectiv e attac ks, w e notice that our a na lysis allows Ev e to mak e general pro cedures (suggested in Figure 2 by the blo c k la b eled POVM ) without b eing detected. Our results are robust to suc h p ow erful a nd unrealistic assumption for the attac k er. Note that our quan tum sc heme aims at minimizing the k ey length for one-w ay transmission. Another example of suc h an approach is giv en in [15]. Next w e fo cus on crucial asp ects of the PRGs. W eak pseudo-random generators Clearly , it is important to un derstand ho w s ecure the a uthen tication code desc rib ed ab ov e is. As we shall see, the securit y of the authen tication co de is deeply related with to qualit y of the pseudo-random generator. The qualit y of a pseudo-random generator is ev aluated b y the hardness to discriminate its pseudo-random sequence output fro m a truly random sequence or by the hardness to find its seed. The first qualit y ev aluat io n relat es to the PR G’s robustness against distinguishing attacks , the second relates to the so-called state r e c overy attacks . In [8] it is sho wn that a state recov ery attack is a sub class of the distinguishing attac ks. 5 As a matter of fact, if the pseudo-random generator can b e attac k ed by a quan tum computer so do es the a uthen tication co de. T o set this result we refer to Figure 3, that describes a simple sc heme to assist us the pro of. In this sc heme, w e simply allo w Ev e to compare a sequence { Y i } of classical bits with the corresp onding sequence { Z i } obtained from the measuremen t apparat us PO VM. Recall that a pseudo-random generator is a p olynomial- time family of functions G = { G n : Z n 2 × N → Z 2 } n ∈ N where Z 2 is the set { 0 , 1 } and G n is the pseudo-generator for seeds with size n , that is, G n ( X ( n ) , i ) returns the i -th bit generated from n bits long seed X ( n ) . Pseudo-random generators are exp ected to fulfill an indistinguishabilit y prop erty that w e will not detail here for t he sak e of simplicit y (more details on [7]). In the f o llo wing definition w e write X p ( n ) = G ( X ( n ) , i 1 ) , G ( X ( n ) , i 2 ) , . . . , G ( X ( n ) , i p ( n ) ) to denote a subseq uence of p ( n ) (not necessarily con tiguous) bits generated b y G. Definition I I .2 W e say that a pseudo-random generator G is attackable in (quantum/pr ob a- bilistic) p olynomial time if there exists a (quantum/probabilistic) p olynomial time algorithm P and p olynomial p suc h that if P is fed with a subsequence of p ( n ) ( no t necessarily con- tiguous) generated bits X p ( n ) of G we hav e that: H ( X ( n ) | P ( X p ( n ) )) ∈ O (2 − n ) . F or a pseudo-random generator to b e atta c k able, there must exist an algo rithm (quantum or probabilistic) that receiv es a subsequence of p ( n ) generated bits ( no t necessarily con tigu- ous) and is able to compute the seed up to a negligible uncertain ty . W e observ e that the securit y/randomness of the pseudo-random g enerator can not b e grounded in the fact that the attac k can only b e p erfo rmed to a con tiguo us subsequence of generated bits. This is due to the fact tha t the generator could alw ay s hide some bits if the attac k required this t yp e of sequences . A simple example of a pseudo-random generator that can b e attack able in p olynomial time are the pseudo-n um b er generators based on linear congruence [8]. Theorem I I .3 If a pseudo-random generator G is attackable in (quantum/pr ob abilistic) p olynom ial time then the sc heme presen ted in F ig ure 3 is not secure in p olynomial-time for a quan tum adv ersary that has access to Y = { Y i } . Pro of. Since G is attac k able there exists a quan tum p olynomial t ime algorithm P and a p olynomial p suc h that if P is f ed with p ( n ) bits of the string X g enerated b y G then P 6 X (n) X = {X i } Y = {Y i } |ψ i PRG + x QC Alice Classical Public Channel POVM Eve Z FIG. 3: Auxiliary sc heme f or Theorem I I.3 pro of computes (up to negligible uncertain t y) the seed X ( n ) of G . So it is enough to sho w that Ev e, up on capturing the qubits generated by QC , is able to reco v er (with non-negligible probabilit y) p ( n ) bits of X . Indeed, a ssume that Ev e has captured 8 p ( n ) qubits | ψ i i , i : 1 . . . 8 p ( n ) and has measured them in a random basis (tha t is, either the computational or the diagonal basis). Ev e can no w v erify if Z i = Y i . If this o ccurs Eve do es not no w if the basis c hose to enco de the Y i bit w as the basis she measured or if she go t with 1 2 probabilit y the correct bit due to enco ding in the o ther basis. Ho we ve r, if the outcome is differen t (that is, Y i 6 = Z i ), then she kno ws that the basis a t the i − th bit is the basis she did not choo se t he measure, b ecause no mismatc h w ould b e p ossible if the enco ding was p erformed with the same basis. I n the latter case, she kno ws that X i is either 0 or 1 dep ending if she measured in the diagonal or t he computational basis, resp ectiv ely . Moreo v er, this happ ens with 1 / 4 probability . So the pro ba bilit y of Ev e not obtaining p ( n ) elemen ts o f X b y measuring 8 p ( n ) qubits is giv en b y the cum ulativ e function of a binomial distribution with 1 / 4 Bernoulli trial, 8 p ( n ) trials and success of at most p ( n ). By Ho effding’s inequalit y this probability is upp er- b ounded b y exp − 2 (8 p ( n ) / 4 − p ( n )) 2 p ( n ) ) = exp( − 2 p ( n )) whic h decreases expo nentially with n , and so in other w ords, Eve has an expo nentially increasing pro babilit y of obtaining p ( n ) bits of X with 8 p ( n ) qubits measuremen ts. Since G is att a c k able by kno wing p ( n ) bits of X , Ev e is able to p erfo rm this at t a c k up t o negligible proba bilit y . Corollary 1 If a pseudo-random generator G is a t tac k a ble then the sc heme presen ted in Figure 2 is not secure in p olynomial-time for a quan tum adv ersary that has a ccess to hash function h. Pro of. Ev e is able to calculate h ( Y ) from Y that is public. Therefore she can apply Theorem I I.3 by observing a num b er N of tags suc h that N log | T | ≥ 8 p ( n ) . 7 Although Theorem I I.3 p oints t hat the quantum co ding o f Figure 3 is not b etter asymp- totically than the classical co ding (where w e simply replace the quan tum co der QC by a XOR gate), it seems harder to atta c k the quan tum sc heme. W e will now sho w that this is true for the simple case where the enco der is fed b y an indep enden t a nd iden tically distributed (i.i.d.) Bernoulli sequence. The follow ing example illustrates that this is true ev en fo r a v ery simple generator. Example I I.4 (State Recov er y A tt ac k for Linear Congruentia l Generator(LCG)) Let A b e a p ositiv e in teger and Z A the set of in tegers mo dulo A. The seed of the LCG is the ve ctor X ( n ) = ( A, s 0 , a, b ), where s 0 , a, b ∈ Z A . The length of the seed is n = 4 ⌈ log A ⌉ . A binary pseudorandom sequence with length N × ⌈ log A ⌉ bits is obtained from the 2- radix expansion of the sequence s = { s 1 , s 2 , . . . , s N } created by the following recursion: s i = as i − 1 + b mo d A, i = 2 , 3 , . . . , N (3) It is we ll know n (see [8]) that for all i, i = 1 , 2 , . . . , N − 3, the num b ers δ i = det s i s i +1 1 s i +1 s i +2 1 s i +2 s i +3 1 are m ultiple of A . As a consequence, the greatest common divisor GCD of some δ ′ i s giv es the v a lue of A . The r est of the seed, that is a, b and s 0 , follow then from a system o f linear equations. In practice fiv e v alues o f δ i are enough. Figure 4 (righ t) displays a simplified v ersion of the sc heme show n in Figure 3, where X stands for the pseudo-random sequence from the output of the PRG. The le ft side o f Figure 4 displa ys the situation when a gate XOR is utilized. W e notice that the state reco v ery attack is applicable without c hange to the XOR -based sc heme. It is enough to compute X = Z ⊕ Y b efore applying t he algorithm. In con trast, f or the quan tum sc heme, Ev e is submitted to an irreducible uncertain t y on the X v alues due to quantum co ding. In pa rticular, if she emplo ys the pro cedure described in t he pro o f of the Theorem I I.3 it is exp ected only one fourth of the X ’s are exp ected to b e correct. The problem from Ev e’s p o in t o f view is how to solv e the seed fro m a degraded ve rsion of the algorithm input X . 8 I I I. COMP ARING XOR WITH Q UANTUM CODING In t he last section w e hav e considered the problem of the state reco v ering attac k and defined t he w eakness of a PR G. In this section w e mak e a rigor o us comparison b etw een the XOR and the quantum co ding p erformances using information-theoretical measures. T o t his Y Z Y X XOR ψ Y QC POVM Z Y X FIG. 4: XOR (left) and quantum co d ing (right) end consider Figure 4 where b o th classical and quan tum enco dings are display ed. The QC denotes the quan tum enco der defined before, in (1) and (2), where X is the v ariable that sets the basis. The blo ck POVM stands for the measuremen t apparatus defined b y the p ositiv e op erator- v alued measure Z = { E m ( Y ) } m ∈ O where O is the set of outcomes. Observ e t ha t t he measuremen t ma y dep end on the message Y , whic h is public. The goa l of Ev e is to maximize the know ledge of X , that is, minimize the en tropy H ( X | Y , Z ). W e consider the classical and quan tum sc heme presen ted in Figure 4 in t w o w a ys: Firstly , w e will assume that X is a seque nce of fair and indep enden t Bernoulli random v a riables, that is, the PR G describing X is p erfect. Secondly , w e consider a biased PRG (unfair) to describe X and in tro duce blo ck s of random v ariables into the analysis. F air input single-sized blo c k W e start with the simple case of a single-sized blo c k a nd where X ∼ Ber 1 2 . In the classical XOR enco ding case w e hav e that Z = X ⊕ Y and th us H ( X | Y , Z ) = 0, and so Ev e has no doubt ab out X . In the quantum enco ding case, the Holev o b ound states t ha t I ( X ; Z | Y ) ≤ S ( ρ ( Y )) − 1 X i =0 1 2 S ( | φ i ( Y ) ih φ i ( Y ) | ) (4) 9 where ρ ( Y ) is the densit y op erator describing the enco ding by QC that is ρ ( Y ) = 1 2 | φ 0 ( Y ) i h φ 0 ( Y ) | + 1 2 | φ 1 ( Y ) ih φ 1 ( Y ) | , (5) where | φ 0 (0) i = | 0 i , | φ 1 (0) i = | + i , | φ 0 (1) i = | 1 i and | φ 1 (1) i = | −i . W e shall need a w ell kno wn prop erty o f the von Neumann en trop y ( see [4] for more details). Prop osition I I I.1 Let ρ b e a quan tum state and S ( ρ ) its en tropy , then S ( ρ ) ≥ 0, and the equalit y ho lds iff ρ is a pure state. Th us, thanks to Prop o sition I I I.1 we can simplify (4) to I ( X ; Z | Y ) ≤ S ( ρ ( Y )) . (6) Moreo v er, one can compute easily the v on Neum ann en tro py of S ( ρ ( Y )) = S ( ρ (0)) = S ( ρ (1) ) and is S ∗ = S ( ρ ( Y )) = − 2 cos 2 π 8 log cos π 8 − 2 log sin π 8 sin 2 π 8 . (7) And so, since H ( X | Z , Y ) = H ( X | Y ) − I ( X ; Z | Y ) and H ( X | Y ) = 1, the minimum uncer- tain ty t ha t Ev e may at t a in ab out X is giv en b y H ( X | Y , Z ) = 1 − S ( ρ ( Y )) . (8) The Holev o b o und can b e achiev ed b y a simple v on Neumann measuremen t [12, pp.421] described by the Hermitian A = 0 | ψ θ ih ψ θ | + 1 | ψ ⊥ θ ih ψ ⊥ θ | (9) with ψ θ = cos( θ ) | 0 i + sin( θ ) | 1 i , ψ ⊥ θ = sin( θ ) | 0 i − cos ( θ ) | 1 i and θ = − π 8 . F air input k -blo cks First, consider the classical setup, t hen H ( X k | Y k , Z k ) = 0 , since the blo c k X k is com- pletely determined fr o m the knowle dge of Y k and Z k . F or the quantum setup, the subsystem that Ev e ow ns is describ ed b y ρ Y k = k O i =1 1 2 | φ 0 ( Y i ) ih φ 0 ( Y i ) | + 1 2 | φ 1 ( Y i ) ih φ 1 ( Y i ) | . (10) 10 By the Holev o b ound w e get tha t H X k | Y k , Z k ≥ H ( X k ) − S ( ρ Y k ) . (11) Example I I I.2 T able I illustrates the scenario for k = 2 . Ro ws are indexed b y the four p ossible v alues o f Y 2 and columns are indexed b y the bases corresp o nding to the f o ur v a lues of X 2 . Notice that Ev e is not able to distinguish whic h column is b eing used. Then, her uncertain t y is lo we r b ounded by the von Neumann en tro p y o f the quantum system fo rmed b y states listed in row indexed b y the v alues of Y 2 that she can access. T ABLE I: Enco ding for b lo c ks of length 2 Bases Y 2 B 0 B 0 B 0 B 1 B 1 B 0 B 1 B 1 00 | 00 i | 0+ i | + 0 i | + + i 01 | 01 i | 0 −i | + 1 i | + −i 10 | 10 i | 1+ i | − 0 i | − + i 11 | 11 i | 1 −i | − 1 i | − −i Recall the fo llowing prop ert y concerning the v on Neumann en tro py . Prop osition I I I.3 Let ρ and σ b e quan tum states, then S ( ρ ⊗ σ ) = S ( ρ ) + S ( σ ) . As a conseque nce of Equation (1 0) and Prop osition I I I.3, for a sequence of fair Bernoullis w e hav e S ( ρ Y k ) = k S ∗ , (12) where S ∗ is giv en by (8). So w e ha v e that H X k | Y k , Z k ≥ k − k S ∗ . (13) Again, the equality can b e ac hiev ed by a simple von Neumann measuremen t, namely that defined by A ⊗ k . This is the b est scenario one can imagine to defeat Ev e. How ev er, for the proto col to b e practical, the X ′ s should b e generated b y a PR G, whic h is the case w e examine next. 11 Unfair input k - blo c ks The results ab ov e where obt a ined assuming that { X i } w as a seque nce of i.i.d. fair Bernoulli random v ariables. In this section we study the general case, with the purp ose of clarifying how the use of a real PR G affects the uncertaint y ab out X . Consider k − length blo c ks X k , Y k and Z k , where X k = X i +1 , X i +2 , . . . , X i + k is a con tigu- ous subsequence of { X i } and similarly t o Y k and Z k . No te tha t , to ease nota tion, w e omit the index i in defining X k . How ever, it is crucial to remark that the probability distribution of X k is, in general, dep enden t on i . As a matter of fa ct, p X k = ( p 0 , p 2 , . . . , p 2 k − 1 ) can ev en degenerate to a distribution with a single comp onen t equal to 1, dep ending on the robustness of the PR G. W e shall simplify the notation denoting p X k b y p . Concerning the unfairness of { X i } , the b est strategy for Ev e to get information from X k is to prepare a measuremen t (PO VM) ov er t he all k qubits sen t, giv en t hat she kno ws Y k . Again, the Holev o b o und giv es us H X k | Y k , Z k ≥ H ( X k ) − S ( ρ Y k ) = H ( X k ) − H ( λ ) (14) where λ = ( λ 1 . . . λ 2 k ) is the sp ectrum of ρ Y k and ρ Y k = 2 k − 1 X j =0 p j | φ j ih φ j | (15) where t he states | φ j i = ⊗ k i =1 | φ j i ( Y i ) i and j i is the i -th bit of the binary represen tation o f j . Note that ρ Y k is a mixture o f pure states w eighted by the probabilities p j , j ∈ { 0 , . . . , 2 k − 1 } . Accordingly , w e write p j = Pr[ X k = j ] where j is seen in its binary represen ta tion (e.g., for k = 2 , p 0 = Pr[ X 2 = 00] , p 1 = Pr[ X 2 = 01] , . . . ). Observ e that S ( ρ Y k 1 ) = S ( ρ Y k 2 ) since there exist a unitar y tra nsformation U suc h that U ρ Y k 1 U − 1 = ρ Y k 2 . W e no w establish a relationship betw een the probability v ectors p X k and the low er b o und giv en in Equation (14). Denote by ρ the uniform distribution, that is, q j = 1 / 2 k , j = 0 , . . . , 2 k − 1 . In this section w e shall v erify that if the probabilit y distribution of a blo c k X k from the PR G, sa y p , is near enough the distribution ρ , for a blo c k of size k , then the low er b ound of (14) will b e k ept significan tly near of k − k S ∗ , whic h is the b est one can a c hiev e. Let σ Y k b e the densit y op erator corr espo nding to a k − length blo c k X k generated b y a 12 fair Bernoulli sequence giv en t hat the k -length blo c k Y k is kno wn, that is σ Y k = 2 k − 1 X j =0 q j | φ j ih φ j | . (16) In t his section w e establish some results relating von Neumann entrop y with the trace distance D ( ρ Y k , σ Y k ) b etw een ρ Y k and σ Y k . R ecall that the tra ce distance b etw een t w o quan tum states ρ and σ is defined b y D ( ρ, σ ) = 1 2 tr | ρ − σ | where | A | = √ A † A . W e shall also need the trace distance b et w een probability ve ctors, sa y a and b , defined by D ( a , b ) = 1 2 X j | a j − b j | . The trace distance can b e used to measure ho w biased a probabilit y distribution is com- pared t o a fair Bernoulli sampling. Given a probability distribution p , we call the bia s of p the v a lue B ( p ) = D ( p , ρ ) where ρ is the uniform distribution. Prop osition I I I.4 Let ε > 0 b e an arbitra ry real n umber. If B ( p ) ≤ ε (17) then D ( ρ Y k , σ Y k ) ≤ ε (18) where ρ Y k is the state defined in Equation (15). Pro of. Denote γ j = | φ j ih φ j | . F rom the strong conv exit y o f the t r a ce distance w e ha v e: D 2 k − 1 X j =0 p j γ j , 2 k − 1 X j =0 1 2 k γ j ≤ D ( p , ρ ) + 2 k − 1 X j =0 p j D ( γ j , γ j ) (19) = D ( p , ρ ) (20) whic h concludes the pro of. In t he pro of of the next prop osition w e shall apply F annes’ inequality (see [14] f or more details ab out this equalit y): | S ( ρ ) − S ( σ ) | ≤ 2 D ( ρ, σ ) ln N 2 D ( ρ, σ ) (21) where it is assumed that D ( ρ, σ ) ≤ 1 / (2 e) a nd N is the dimension of the Hilb ert space dimension where t he states liv e in. 13 Theorem I I I.5 If the conditions in Prop osition I I I.4 hold, that is, if B ( p ) ≤ ε , then | H ( X k ) − S ( ρ Y k ) − ( H ( X k ) − S ( σ k )) | = | S ( ρ Y k ) − S ( σ k ) | (22) ≤ 2ln2 ( k − 1) ε + 2 ε ln 1 ε . (23) Pro of. Observ e that the function − x ln x is monotonous in the interv al (0 , 1 /e ). Therefore, assuming 0 ≤ ε ≤ 1 /e and for N = 2 k , w e hav e: | S ( ρ Y k ) − S ( σ k ) | ( a ) ≤ 2 D ( ρ Y k , σ k )ln 2 k 2 D ( ρ Y k , σ k ) ( b ) = 2 ln2 ( k − 1) D ( ρ Y k , σ k ) + 2 D ( ρ Y k , σ k )ln 1 D ( ρ Y k , σ k ) (24) ( c ) ≤ 2ln2 ( k − 1) ε + 2 ε ln 1 ε (25) where ( a ) r esults fr o m F annes’ inequalit y , ( b ) is due to logarithm prop erties and, ( c ) is due to Prop osition I I I.4. This result states that if a PRG is suc h that the probability distribution of its output X k , sa y , p (p ossibly conditioned on the past), is near enough the fair distribution ρ , then Ev e’s uncertain t y is k ept near the maxim um H X k | Y k , Z k = k − k S ∗ (see Equation (1 3)). Note t ha t the distribution of p is induced by the ra ndom secret seed of t he PR G, X ( n ) , whic h is ch osen with uniform distribution. Consequen tly , an y practical use of Equation (2 3) will dep end on the Ev e’s capabilit y to estimate that distribution a nd clearly , on the PR G b eing used. F or instance, supp o se w e w ant to upp er bound the r ig h t side of (23) with a giv en toler anc e defined by a p ositiv e real n um b er δ . After some simple algebraic manipulation we obtain that k < 1 + 1 2ln2 δ ε − ln 1 ε ln2 . (26) F or the case of ε = δ we get the simple b ound k < 1 + 1 2ln2 − ln 1 ε ln2 ≤ 1 + 1 2ln2 + 1 ε − 1 ln2 ≤ 1 + 1 ε ln4 . (27) Additionally , when the conditio ns of Prop osition I I I.4 hold, that is, for bia s B ( p ) < ε , w e can rewrite (26) as k < 1 + 1 2ln2 δ B ( p ) − ln (1 /B ( p )) ln2 . (28) 14 Note that the rig h t-hand side o f (28) approximates 1 2ln2 δ B ( p ) as B ( p ) tends to zero. In detail, Equation (28), at the ligh t of Theorem I I I.5, pro vides a w ay to compute the largest blo c k whose uncertain t y remains near k − k S ∗ (up t o ε ), giv en an upp er b ound of the bias of p . How ev er, a w ord o f advice is necessary: from its v ery definition, p dep ends on k and also on the p osition i the blo c k start, b ecause X k = X i +1 , X i +2 , . . . , X i + k . So, the use of Equation (28) to establish a b ound of a secure blo c k relies o n a bias difficult to compute f or standard PRG’s. The follow ing corollary clarifies the meaning o f Theorem I I I.5 from an asymptotic p oin t of view. Corollary 2 Giv en a PR G, let p b e the probabilit y distribution of a k -length generated blo c k, and let f ( k , n ) and g ( n ) p ositiv e functions suc h that: • lim n →∞ g ( n ) = + ∞ • lim n →∞ g ( n ) f ( g ( n ) , n ) = 0. Then, if B ( p P RG ) ≤ f ( k , n ) and k ≤ g ( n ), lim n →∞ | S ( ρ Y g ( n ) ) − S σ g ( n ) | = 0 . W e now discuss the results ab ov e. The idea is that n is the size of the seed of the P RG and k is the size of the blo ck . If one chooses k ≤ g ( n ) for some g and the bias of the PRG is smaller the f ( k , n ) for some f fulfilling the conditions o f Corollary 2, then the info r mation Ev e can retriev e from blo ck s of size g ( n ) is as close to the ideal case as desired, just b e c ho osing a larger n . A go o d PRG is o ne fo r whic h n << g ( n ), so that the blo ck size could b e larger tha n the seed and still, lit t le information ab out t he seed is reve aled. In the next section we make a comparison b et we en classical XOR and quan tum QC Bras- sard’s sc hemes for authentication of classical messages. IV. IMPR OVING KEY-T A G SECRECY In the last section w e compared Ev e’s equiv o cation on X for the XOR and QC sc hemes when she has access b oth to the message Y and its quan tum enco ded v ersion, whic h she observ es from the quan tum c hannel. W e concluded that the equiv o cation is k ept ab ov e some low er 15 b ound dep ending o n t he quality of the PR G. In this section w e include a hash function h in the sc heme (see Figure 5) in such a w a y that Ev e only accesses the public message Y and the quan tum encoded v ersion of t he tag T = h ( Y ). Thanks to that mo dification w e shall demonstrate that is feasible to impro v e the secrecy o f the k ey and of the ta g sim ultaneously . By information-theoretic secrecy , as usually , w e mean I ( W ; V ) = 0 + O (2 − n ) or equiv a- len tly , the equiv o cation H ( W | V ) = H ( W ) − O (2 − n ), where W is t he secret to b e protected and V is the piece of data av aila ble to the eav esdropp er. Our deriv a tions will fo cus in the equiv o cation H ( W | V ) t o measure the qualit y of the sc heme. Then, the information to b e protected is W = T , X k and the informa t io n a v a ilable, from Ev e’s viewp oin t, is V = ( Y , Z ). W e in v estigate t he uncertaint y of t he ta g H ( T | Y , Z ) and the uncertain ty of the ke y H ( X k | Y , Z ) . W e assume t ha t X k , is indep endent o f the message Y and that the X (n) X = {X i } ψ i X k POVM PRG Alice QC h Eve Bob Z T=h(Y) Y Classical Public Channel FIG. 5: Authentica tion scheme w ith a single key X ( n ) hash function is selected from the ε − almost univers al- 2 class of hash functions, whic h w e refer in the follow ing just as hash functions . Mo dified classical case Consider a simple mo dified setup where a XOR gate is tak en in pla ce of the QC blo c k in the sc heme displa y ed in Figure 5. If { X i } is a fair Bernoulli and a k − blo c k of bits suc h that k = max {⌈ log | T |⌉ , ⌈ log | H|⌉ } it is utilized p er message, then the sc heme turns to b e equiv alen t to t he W egman-Carter one-time pad sc heme. Indeed, in this situation h is in fact drawn unifo rmly from H , then H T , X k | Y , Z k ( a ) = H ( T | Y , Z k ) + H ( X k | T , Y , Z k ) (29) ( b ) = H ( T | Y , Z k ) (30) ( c ) = H ( T | Y ) (31) 16 ( d ) = lo g | T | . (32) Where equalit y ( a ) is due to c hain rule for Shannon en tropy , ( b ) is due to the fact that in the classical setup X k = T ⊕ Z k . The equality (c) is harder to obtain, indeed it fo llo ws f rom t he prop erties of the ε − almost univ ersal-2 class of hash function. Note that T = h X k ( Y ) has a uniform distribution. Moreo v er T | x k = h x k ( Y ) has also uniform distribution, and therefore, T is indep enden t of X k . Since Z k = f ( X k , Y ) we ha ve that H ( T | Y , Z k ) = H ( T | Y ). Equalit y ( d ) is also due to the prop erties of hash functions. On t he ot her hand, if { X i } comes from a PR G, the Ev e’s uncertaint y on the tag can, ev en tually , decreases by observing the random v ariable Z k . Indeed, in general, H T | Y , Z k < H ( T | Y ). Consequen tly , unconditional secrecy relativ e to T , H ( T | Y , Z k ) = lo g |T | cannot b e a ssured. Uncertain ty of the tag in the quantum case In this subsection w e in tro duce a conditio n to attain unconditional securit y of the tag in terms of conditioned m utual information b et w een T and the k − blo c k of bits of the key . Prop osition IV.1 If I T ; X k | Y , Z k = H ( T ) then the tag is secure in the information theoretical sense, that is, H ( T | Y , Z k ) = H ( T ). Pro of. F rom the standard c hain rule of Shannon en trop y w e ha ve : H T , X k | Y , Z k = H X k | Y , Z k + H T | X k , Y , Z k (33) = H T | Y , Z k + H X k | T , Y , Z k . (34) Then, comparing (33) and (34) w e obta in H T | Y , Z k ( a ) = H T | X k , Y , Z k + H X k | Y , Z k − H X k | T , Y , Z k (35) ( b ) = H T | X k , Y , Z k + I T ; X k | Y , Z k (36) ( c ) = I T ; X k | Y , Z k (37) Where ( a ) is due to a simple manipulat io n of (33) and (34), ( b ) is definition of mutual information and ( c ) follows b ecause t he hash function is determined b y X k and so, then 17 T = h ( Y ) is immediately calculated. That is, H ( T | X k , Y , Z k ) = H ( T | X k , Y , T = h ( Y )) = 0 . The results follo ws fro m (3 7). Eq. (37) clearly indicates that in or der to increase Ev e’s uncertaint y ab out T w e m ust max- imize the m utual inf o rmation b et w een the blo c k X k and the tag T . This is the inform ation- the or etic a l hin t that motiv ates the sc heme presen ted in Figure 5. Note that in this case w e mak e the tag T depend o f X k , increasing th us their m utual information. In Brassard sc heme (see Figure 1) the hash function is fixed in the b eginning, and therefore I T ; X k | V ′ = 0 where V ′ is the observ a tion that Ev e can p erform in Brassard’s sc heme. It is remark able to b e p o ssible to atta in unconditiona l securit y of the tag using non- fair Bernoulli for X with the prop osed of Fig ure 5. This fact is in sharp contrast with the classical setup for whic h only Bernoulli sequences can assure that requiremen t. Th us, a go o d a ppro ximation is to use PRG for the sequence of X , and the m utual information I ( T ; X K | Y , Z k ) is as high as the PR G is unbiase d, since that m utual information is mediated by the random v ariable Z k . It is clear that, if we are dealing with real PR G s (that do not generate a sequence o f fair Bernoullis), then the conditions of Theorem I I I.5 should b e considered in order to ev aluate the n umber of messages that can b e authen ticated b efore leaking to o m uc h information. Another p ossibilit y to apply the sc heme of F igure 5 is to spend just k = log |T | key bits p er message to protect t he curren t tag. This approach is similar to Brassard’s sche me, but impro v es it since the tag is protected by the quan tum co ding. Observ e that as log |T | < log |H| , this sc heme is less costly in terms o f k ey consumption. Uncertain ty of the k ey in t he quan tum case In this case, t he b ounds deriv ed in Section I I I remain v alid, namely t he inequalit y (14) that w e recall H X k | Y k , Z k ≥ H ( X k ) − S ( ρ Y k ) = H ( X k ) − H ( λ ) . (38) In this case, since the measuremen t Z k is on the quantum enco ding of the ta g, and not o n the quan tum enco ding of Y , the uncertain t y is greater than that of t he case discus sed in Section I I I. So, with the sc heme of F ig ure 5 , not only we o btain a high equiv o cation ab out the tag, but we also increase the uncertain ty of the sequence X k and, therefore, also of the seed X ( n ) 18 of the PR G. O bserv e that Theorem I I I.5 and inequalit y 26 are also v alid for this sc heme, and can b e used to get b ounds ab out the size of k for whic h a threshold of information is leak ed to Ev e. V. SUMMAR Y In this work w e ha ve in v estigated how quan tum resources can improv e the securit y of Brassard’s classical message authentication proto col. W e hav e started b y showin g tha t a quan tum co ding of secret bits offers more securit y than the classical XOR function in tro duced b y Brassard. Then, we ha v e used this quantum co ding t o prop ose a quan tum-enhanced pro- to col t o authen ticate classical messages, with improv ed security with resp ect to the classical sc heme introduced b y Brassard in 1983. Our proto col is also more practical in the sense that it requires a shorter k ey than the classical sc heme b y using the pseudorandom bits to c ho ose the hash function. W e then establish the relationship b etw een the bias of a PRG and the amoun t of information ab out the k ey t ha t the attac ke r can retriev e from a blo c k of authenticated messages. Finally , w e pro v e tha t quantum r esources can impro v e b oth the secrecy of the ke y generated by the PR G and the secrecy of the tag obtained with a hidden hash function. Ac kno wledgments F. M. Assis ac knowle dges pa r t ial support from Brazilian National Council for Scien- tific and T echnological D evelopme nt (CNPq) under Gran ts No. 302499/2 003-2 and CAPES- GRICES No. 160. P . Mateus and Y. Omar thank the supp ort from pro ject IT-Quan tT el, as w ell as from F unda¸ c˜ ao para a Ci ˆ encia e a T ecnologia (P ortugal), namely through pro- grams POCTI/POCI/PTDC a nd pro j ects PTDC/EIA/67661/2006 Q Sec a nd PTDC/EEA- TEL/103402/20 0 8 QuantPrivT el, partially funded b y FEDER (EU). [1] G. Brassard, “On computationally secure authentic ation tags r equiring s hort secret shared k eys”, in A dvanc es in Cryptolo gy (Spr inger-V erlag, 1983), pp. 79–86 . 19 [2] M. N. W egman and J. L. Carter, “New hash fun ctions and their us e in authentic ation and set equalit y .” J. Comput. Syst. Sci. , 22:26 5–279 (1981) . [3] M. Blum and S. Micali, “Ho w to generate cryp tographically strong sequences of pseud o- random bits”, SIA M J. on Computing , 13(4):850– 864 (1984). [4] M. A. Nielsen and I. L. Chuang, Quantum Computatio n and Quantum Information (Cam- bridge Unive rsity Press, New Y ork, 2000). [5] W. Stallings, Crypto gr aphy and Network Se curity: Principles and Pr actic e (Pr en tice-Hall, Inc., New Jersey , 2nd edition, 1998). [6] J. Cederl¨ orf and J. L ars son, “ Securit y Asp ects of the Authen tication Used in Qu an tum Cryptography ”, IE EE T r ansactions on Information The ory , 54(4):1 735–1741 (2008). [7] O. Goldreic h, Mo dern Crypto g r aphy, Pr ob abilistic P r o ofs and Pseudor andomness , (Sprin ger, 1999) [8] A. Sidorenko and B. Sho enmak ers, “State Reco v ery A ttac ks on Pseudorand om Generators”, in Western Eur op e an Workshop on R ese ar c h in Cryptolo gy, L e c tur es Notes in Info rmatics (LNI) , 74:53–63 (2005). [9] T. P . S piller, “Quantum inf ormation pro cessing: cryptograph y , computation, and telep orta- tion”, Pr o c e e dings of the IEE E , 84(12): 1719–174 6 (1996). [10] C . H. Bennett and P . W. Shor, “Quan tum information theory”, IE EE T r ansactions on Information The ory , 44(6):27 24–2755 (1998). [11] C . H. Benn ett and G. Brassard , “Quantum cryptograph y: public-k ey distribution and coin tossing”, in Pr o c e e dings of IE EE Interna tional Confer enc e on Computers, Systems, and Signal Pr o c essing, Bangalor e, India, 1984 (IEEE Pr ess, New Y ork, 1984), pp . 175–179. [12] M. G. A. P aris and J . Reh ´ acek, L e ctur e s Notes in Physics, Quantum State Estimation Springer, Berlin, 2004 [13] P . W. Sh or, “Algorithms for quant u m computation: Discrete logarithms and factoring”, in IEEE Symp osium on F oundations of Computer Scienc e , p p. 124– 134, (1994). [14] I. Bengtsson and K. Zyczko wski, Ge ometry of Quantum States (Cambridge Unive r s it y Pr ess, 2006) . [15] I. Damgaard, T. P edersen, L. S alv ail, quan t-ph/0407066 (2004). 20 21 Y, θ Z =0 Y, θ Z =1 θ X=0 Y=0 X=0 Y=1 X=1 Y=0 X=1 Y=1
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment