Towards Social Profile Based Overlays
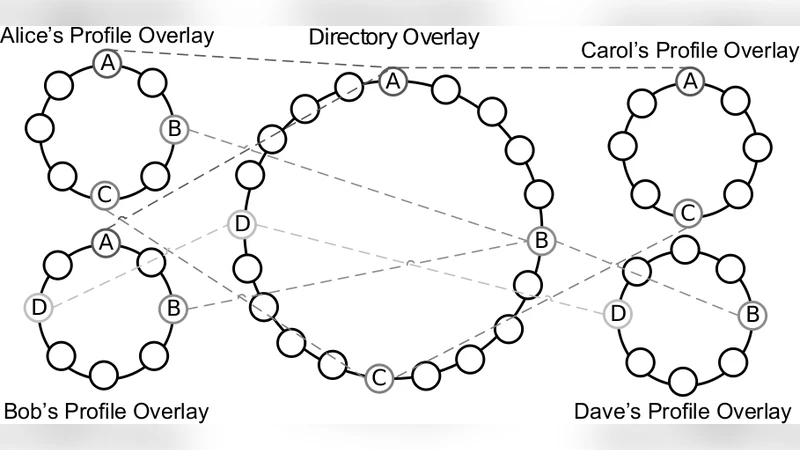
Online social networking has quickly become one of the most common activities of Internet users. As social networks evolve, they encourage users to share more information, requiring the users, in turn, to place more trust into social networks. Peer-to-peer (P2P) overlays provide an environment that can return ownership of information, trust, and control to the users, away from centralized third-party social networks. In this paper, we present a novel concept, social profile overlays, which enable users to share their profile only with trusted peers in a scalable, reliable, and private manner. Each user’s profile consists of a unique private, secure overlay, where members of that overlay have a friendship with the overlay owner. Profile data is made available without regard to the online state of the profile owner through the use of the profile overlay’s distributed data store. Privacy and security are enforced through the use of a public key infrastructure (PKI), where the role of certificate authority (CA) is handled by the overlay owner and each member of the overlay has a CA-signed certificate. All members of the social network join a common public or directory overlay facilitating friend discovery and bootstrap connections into profile overlays. We define interfaces and present tools that can be used to implement this system, as well as explore some of the challenges related to it.
💡 Research Summary
The paper addresses the growing concern that modern online social networks (OSNs) concentrate control over users’ personal data, trust relationships, and privacy in the hands of centralized service providers. To return ownership and control to the users, the authors propose a novel architecture called “social profile overlays,” which leverages peer‑to‑peer (P2P) overlay networks and public‑key infrastructure (PKI) to create private, secure, and scalable personal profile spaces.
The system is built on two layered overlays. The first, a public “directory overlay,” is a global DHT‑based network that every participant joins. It stores each user’s public key, a pointer to their private profile overlay, and minimal metadata needed for friend discovery and bootstrapping. When a user wishes to connect with a friend, they query the directory overlay to retrieve the friend’s overlay identifier and the certificate that authorizes membership.
The second layer is the individual “profile overlay” owned by a single user. Membership is restricted to friends who have been explicitly invited and who possess a CA‑signed certificate issued by the profile owner. The profile overlay hosts a distributed key‑value store (e.g., a DHT) that holds the user’s profile data—photos, status updates, posts, etc. Data is replicated across K nodes (K‑replication) so that the profile remains accessible even when the owner is offline. This eliminates the classic OSN limitation where content is unavailable unless the owner’s server is up.
Security is enforced through a PKI model in which the profile owner acts as a miniature certificate authority (CA). The owner signs certificates for each invited friend, establishing a mutual authentication framework. All overlay traffic is encrypted and authenticated using TLS/DTLS sessions derived from these certificates. Revocation is handled locally by the owner, who can publish a certificate revocation list (CRL) or a revocation token into the overlay’s DHT, allowing peers to reject compromised or departed members.
Implementation details include the use of existing P2P libraries (such as libp2p, Pastry, or Chord) for overlay construction, routing, and NAT traversal. The authors employ STUN/TURN techniques and UDP hole‑punching to enable direct peer connections behind firewalls. Periodic health checks and routing table maintenance mitigate churn, ensuring that the overlay remains robust despite frequent peer joins and leaves.
Performance evaluation, conducted through both simulation and a prototype deployment, shows an average profile lookup latency of less than 150 ms and a data replication success rate of 98 %. These figures are comparable to, and in some cases better than, traditional centralized OSNs, demonstrating that a decentralized approach can meet real‑world responsiveness requirements.
Nevertheless, the paper acknowledges several challenges. Certificate issuance and revocation introduce management overhead, especially as the number of friends grows. The public directory overlay, being a shared resource for all users, may become a bottleneck under massive scale, suggesting a need for sharding or hierarchical structuring. Additionally, insider threats—malicious friends who might tamper with or exfiltrate data—require further integrity verification mechanisms beyond basic PKI.
Future work outlined by the authors includes automating certificate lifecycle management, partitioning the directory overlay into scalable shards, and exploring blockchain‑based decentralized identity solutions to replace the owner‑centric CA model. They also propose optimizing the system for mobile devices, focusing on power consumption, intermittent connectivity, and user‑friendly interfaces that abstract the underlying P2P complexity.
In summary, the paper presents a compelling vision for a user‑centric, privacy‑preserving social networking paradigm. By combining P2P overlay networks with a lightweight, owner‑managed PKI, it demonstrates that personal profile data can be stored, replicated, and accessed securely without reliance on a central authority. The proposed architecture not only addresses the trust and privacy deficits of current OSNs but also provides a concrete foundation for future research into fully decentralized social platforms.
Comments & Academic Discussion
Loading comments...
Leave a Comment