Formal Modelling of a Usable Identity Management Solution for Virtual Organisations
This paper attempts to accurately model security requirements for computational grid environments with particular focus on authentication. We introduce the Audited Credential Delegation (ACD) architecture as a solution to some of the virtual organisations identity management usability problems. The approach uses two complementary models: one is state based, described in Z notation, and the other is event-based, expressed in the Process Algebra of Hoare’s Communicating Sequential Processes (CSP). The former will be used to capture the state of the WS and to model back-end operations on it whereas the latter will be used to model behavior, and in particular, front-end interactions and communications. The modelling helps to clearly and precisely understand functional and security requirements and provide a basis for verifying that the system meets its intended requirements.
💡 Research Summary
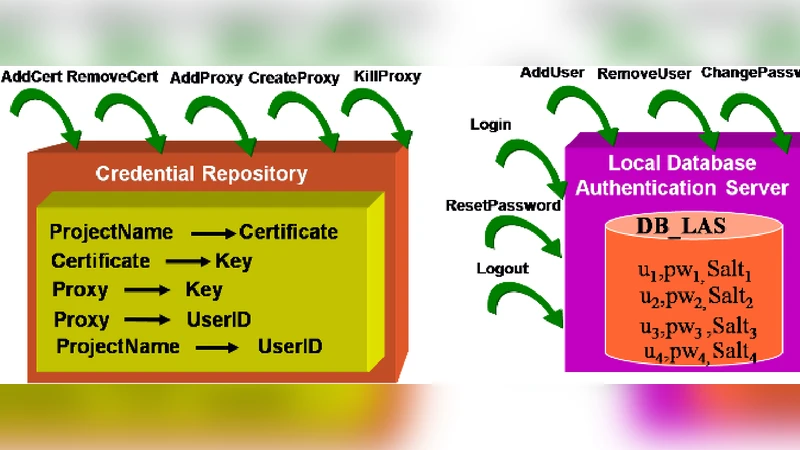
The paper addresses the well‑known usability challenges of identity management in virtual organisations (VOs) that operate computational grids. Traditional grid middleware such as Globus and UNICORE rely on Public Key Infrastructure (PKI) and X.509 certificates, requiring end‑users—often scientists with limited security expertise—to generate short‑lived proxy certificates, manage private keys, and sometimes share credentials in insecure ways. To mitigate these problems, the authors propose the Audited Credential Delegation (ACD) architecture. ACD hides all certificate handling behind a gateway that provides a Local Authentication Service (LAS) and a Credential Repository. Users authenticate locally with a simple username/password mechanism (or other familiar methods such as Kerberos or Shibboleth), while the gateway obtains and stores the necessary grid certificates and proxies on their behalf. The repository also maintains mappings between projects, resources, certificates, private keys, and issued proxies, enabling fine‑grained authorization decisions.
The contribution of the paper lies not only in the architectural design but also in a rigorous, dual‑formal specification. The authors employ two complementary formal methods: Z notation for a state‑based model and Hoare’s Communicating Sequential Processes (CSP) for an event‑based model. The Z model captures the static aspects of the system: the set of registered users, the password database (pwdDB), per‑user salts, and the encryption function. Invariants guarantee that every registered user has an associated password and salt. Three core operations—Login, ChangePassword, and AddCredential—are defined as Z schemas with explicit pre‑conditions (e.g., the username/password pair must exist in pwdDB) and post‑conditions (updates to pwdDB and salting). Errors such as “user not in use” or “invalid credentials” are handled through a totalising technique that introduces a Report datatype (Success | Failure), ensuring that every operation yields a well‑defined outcome.
The CSP model derives an interface from the Z specification. It defines channels for each request/response pair (LoginRequest, LoginResponse, ChangePasswordRequest, etc.) and models the authentication server as a process DB(state). The process synchronises on these channels, checks the Z‑derived pre‑conditions, and emits either a Success or Failure report. The CSP description also distinguishes between normal user actions and privileged administrator actions (e.g., adding or removing credentials, resetting passwords), although the latter are omitted for brevity. By composing the client process with DB using the CSP parallel operator with hand‑shaking on the operation channels, the authors illustrate a complete interaction trace: a client sends a LoginRequest, the server validates the credentials against the Z‑specified pwdDB, and returns a LoginResponse indicating success.
For external authentication, a second Z model is introduced. It defines abstract types for UserID, Subject, Data, Key, SerialNb, CipherAlgName, and CertAuthorityName. The state includes sets of certificates, project and resource names, a key‑association relation linking certificates to private keys, a cert‑association function linking projects to certificates, and a mapping of issued proxy certificates to their issuers. This model formalises how the gateway stores and retrieves grid certificates, creates proxies, and enforces project‑level access control.
The paper’s structure proceeds as follows: Section 1 motivates the problem and outlines the ACD concept; Section 2 describes the architecture (gateway components, LAS, repository, integration with the Application Hosting Environment); Sections 3 and 4 present the Z and CSP specifications for local and external authentication respectively; Section 5 concludes with a discussion of related formal frameworks (Circus, CSPkB) and future work, notably a planned deployment on TeraGrid, NGS, and DEISA within twelve months.
Key insights include: (1) the separation of “front‑end” user interaction (modeled in CSP) from “back‑end” data management (modeled in Z) provides a clear verification boundary; (2) totalising error handling in Z combined with explicit CSP reports yields a complete, executable specification that can be checked with tools such as ZTC and CSP model‑checkers; (3) the ACD architecture reduces the cognitive load on end‑users while preserving strong cryptographic guarantees, thereby improving both usability and security; (4) the dual‑formal approach facilitates systematic refinement from specification to implementation, as Z’s mathematical notation aligns closely with conventional programming constructs.
In summary, the authors deliver a formally verified, usability‑focused identity management solution for virtual organisations, demonstrating how rigorous state‑ and event‑based models can be integrated to capture both the static constraints and dynamic behaviours of a complex security infrastructure. The work paves the way for trustworthy, user‑friendly grid authentication services that can be confidently deployed in production scientific environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment