Recently, Abdalla et al. proposed a new gateway-oriented password-based authenticated key exchange (GPAKE) protocol among a client, a gateway, and an authentication server, where each client shares a human-memorable password with a trusted server so that they can resort to the server for authentication when want to establish a shared session key with the gateway. In the letter, we show that a malicious client of GPAKE is still able to gain information of password by performing an undetectable on-line password guessing attack and can not provide the implicit key confirmation. At last, we present a countermeasure to against the attack.
Deep Dive into Weakness Analysis and Improvement of a Gateway-Oriented Password-Based Authenticated Key Exchange Protocol.
Recently, Abdalla et al. proposed a new gateway-oriented password-based authenticated key exchange (GPAKE) protocol among a client, a gateway, and an authentication server, where each client shares a human-memorable password with a trusted server so that they can resort to the server for authentication when want to establish a shared session key with the gateway. In the letter, we show that a malicious client of GPAKE is still able to gain information of password by performing an undetectable on-line password guessing attack and can not provide the implicit key confirmation. At last, we present a countermeasure to against the attack.
The gateway-based authenticated key exchange (GAKE) protocols are important cryptographic techniques for secure communications. Conceptually, a typical three-party password-based authenticated key exchange protocol works as follows. As requirement, each client C shares a human-memorable password with a trusted server so that they can resort to the server S for authentication when want to establish a shared session key with the gateway G .
Among the various means of authentication that can be considered, the most interesting one from a practical point of view is the password-based setting in which a simple human-memorizable secret, called a password, is used for authentication.
In 2005, Abdalla et al. proposed the first gateway-oriented password-based authenticated key exchange (GPAKE) scheme among a client, a gateway, and an authentication server [1]. Even though Abdalla et al. had proved the session key semantic security of their scheme in a formal model, Byun et al. reported an undetectable on-line guessing attack on the GPAKE protocol where a gateway can iteratively guess a password and verify its guess without being detected by the server [2]. Byun et al. also proposed an improved scheme to eliminate the security vulnerability of Abdalla et al.’s scheme. However, Wu et al. [3] found that Byun et al.’s scheme still cannot resist the on-line undetectable guessing attack.
Very recently, Abdalla et al. [5] present a new variant of the GPAKE scheme of Abdalla et al.
[1]. They used the Schnorr’s signature [6,7] in the new scheme in order to guarantee the security of the new scheme. The new scheme can withstand the attack by Byun et al. [2].
In this letter, we review Abdalla et al.’s new protocol [5], and show that it does actually leak information of password to a malicious client and can not provide the implicit key confirmation. Especially, we show that Abdalla et al.’s new scheme is susceptible to an undetectable on-line password guessing attack by a malicious client. We also give a countermeasure against the attack by letting the client generate a message authentication code of keying material.
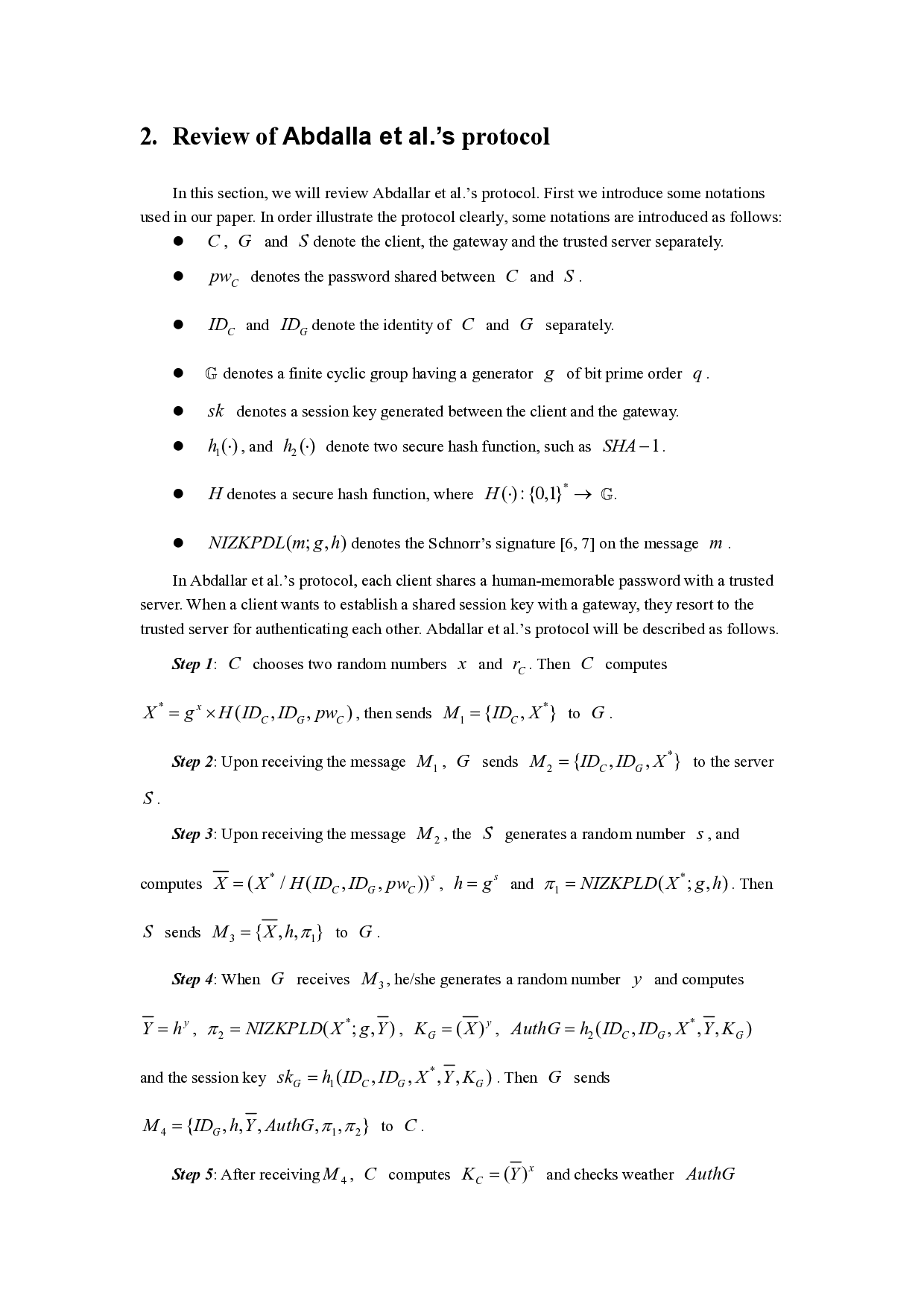
In this section, we will review Abdallar et al.’s protocol. First we introduce some notations used in our paper. In order illustrate the protocol clearly, some notations are introduced as follows:
C , G and S denote the client, the gateway and the trusted server separately. G denotes a finite cyclic group having a generator g of bit prime order q . sk denotes a session key generated between the client and the gateway. ( ; , ) NIZKPDL m g h denotes the Schnorr’s signature [6,7] on the message m . In Abdallar et al.’s protocol, each client shares a human-memorable password with a trusted server. When a client wants to establish a shared session key with a gateway, they resort to the trusted server for authenticating each other. Abdallar et al.’s protocol will be described as follows.
Step 1: C chooses two random numbers x and C r . Then C computes * ( , , )
Step 2: Upon receiving the message
Step 3: Upon receiving the message 2 M , the S generates a random number s , and
Step 4: When G receives 3 M , he/she generates a random number y and computes
Step 5: After receiving 4
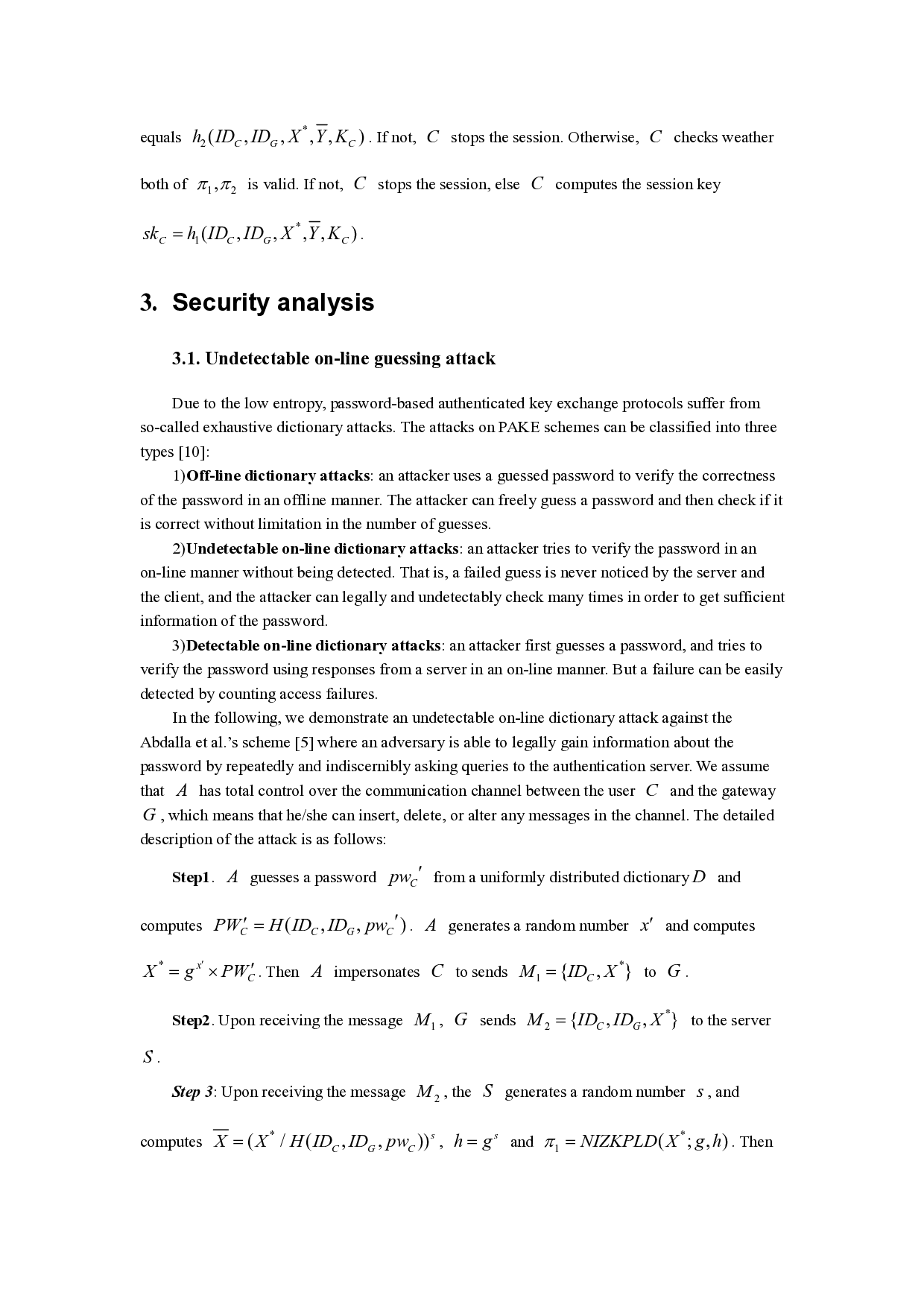
Due to the low entropy, password-based authenticated key exchange protocols suffer from so-called exhaustive dictionary attacks. The attacks on PAKE schemes can be classified into three types [10]:
1)Off-line dictionary attacks: an attacker uses a guessed password to verify the correctness of the password in an offline manner. The attacker can freely guess a password and then check if it is correct without limitation in the number of guesses.
2)Undetectable on-line dictionary attacks: an attacker tries to verify the password in an on-line manner without being detected. That is, a failed guess is never noticed by the server and the client, and the attacker can legally and undetectably check many times in order to get sufficient information of the password.
3)Detectable on-line dictionary attacks: an attacker first guesses a password, and tries to verify the password using responses from a server in an on-line manner. But a failure can be easily detected by counting access failures.
In the following, we demonstrate an undetectable on-line dictionary attack against the Abdalla et al.’s scheme [5] where an adversary is able to legally gain information about the password by repeatedly and indiscernibly asking queries to the authentication server. We assume that A has total control over the communication channel between the user C and the gateway G , which means that he/she can insert, delete, or alter any messages in the channel. The detailed description of the attack is as follows:
Step1. A guesses a password C pw ′ from a uniformly distributed dictionary D and computes ( , , )
. A generates a random number x′ and computes
Step 3: Upon receiving the message 2 M , the S generates a random number s , and
Step 4: When G receives 3 M ,
…(Full text truncated)…
This content is AI-processed based on ArXiv data.