This note proposes a method of space efficient secret sharing in which k secrets are mapped into n shares (n>=k) of the same size. Since, n can be chosen to be equal to k, the method is space efficient. This method may be compared with conventional secret sharing schemes that divide a single secret into n shares.
Deep Dive into Space Efficient Secret Sharing.
This note proposes a method of space efficient secret sharing in which k secrets are mapped into n shares (n>=k) of the same size. Since, n can be chosen to be equal to k, the method is space efficient. This method may be compared with conventional secret sharing schemes that divide a single secret into n shares.
A k-out-of-n secret sharing scheme conventionally encodes a single secret s in n shares such that any k of them can be used to reconstruct the secret (Shamir's scheme [1]). However, Shamir's scheme is not space efficient because it leads to a n-fold increase in total storage requirement. Some efforts have been made to create space efficient schemes [5,6] under certain restrictions, but most other techniques achieve this in the general case by compromising security constraints and adopting a computational security model [2,3,4], which is weaker compared to that of Shamir's scheme.
We present an algorithm to split k secrets of length b each into n shares such that each share is effectively of size (n/k) • b. Since, n/k can be chosen to be close to 1, our algorithm is space efficient.
Our proposed scheme is based on interpolation just like Shamir’s scheme, but unlike Shamir we use the k secrets to obtain a polynomial and then create n shares by finding the values of the polynomial at n new points. Without knowledge of at least k of these shares, equal to the number of coefficients associated with the polynomial, the original secrets, defined for pre-fixed points of the variable, cannot be found.
The proposed algorithm is as follows. Consider that k secrets s 0 , s 1 , …, s k-1 are numbers from the finite field Z p , where p is prime.
- The shares are then given by (k,
Reconstruction of the secrets involves first interpolating any k shares to recreate f (x) and then evaluating it to reveal the secrets
Reconstruction of the secrets in Algorithm A can be viewed as solution to a set of linear equations A • v = F , where A is a k × k Vandermonde matrix [7] (generated using the x-coordinates of any k shares), v is a k × 1 vector of unknowns (polynomial coefficients a i ’s) and F is the k × 1 vector of the y-coordinates of the shares. Without loss of generality, assume we have k -1 shares (k, D 1 ), (k +1, D 2 ), …, (2k -2, D k-1 ). We can explicitly write the system of equations as follows,
Clearly to find the value of a i ’s one would need to invert the Vandermonde matrix (find A -1 ) and also know the values of D i , 1 ≤ i ≤ k -1. Further, since we have distributed the secrets among the coefficients of the polynomials, one needs to reconstruct the coefficients a i , 0 ≤ i ≤ (k -1), in order to obtain any and all of the secrets.
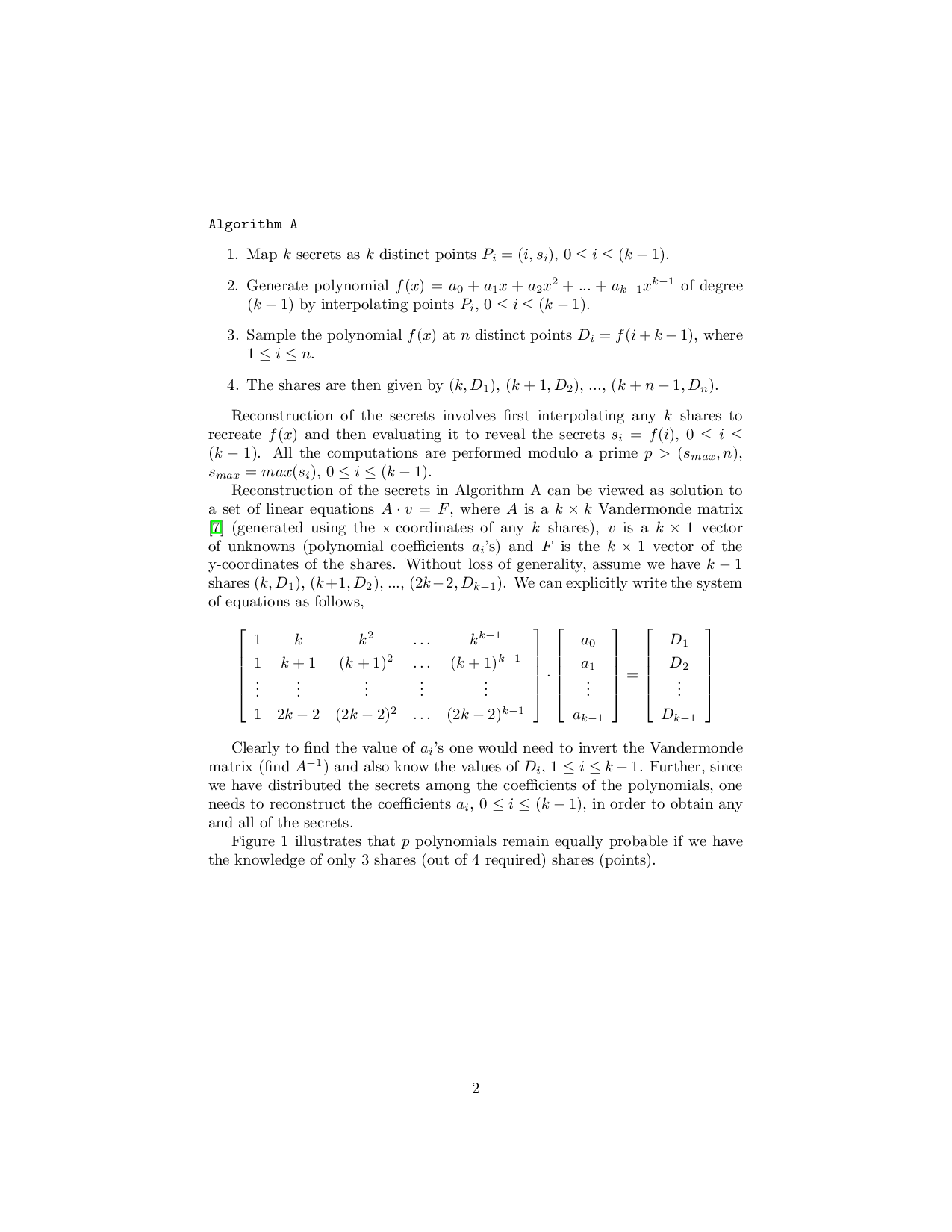
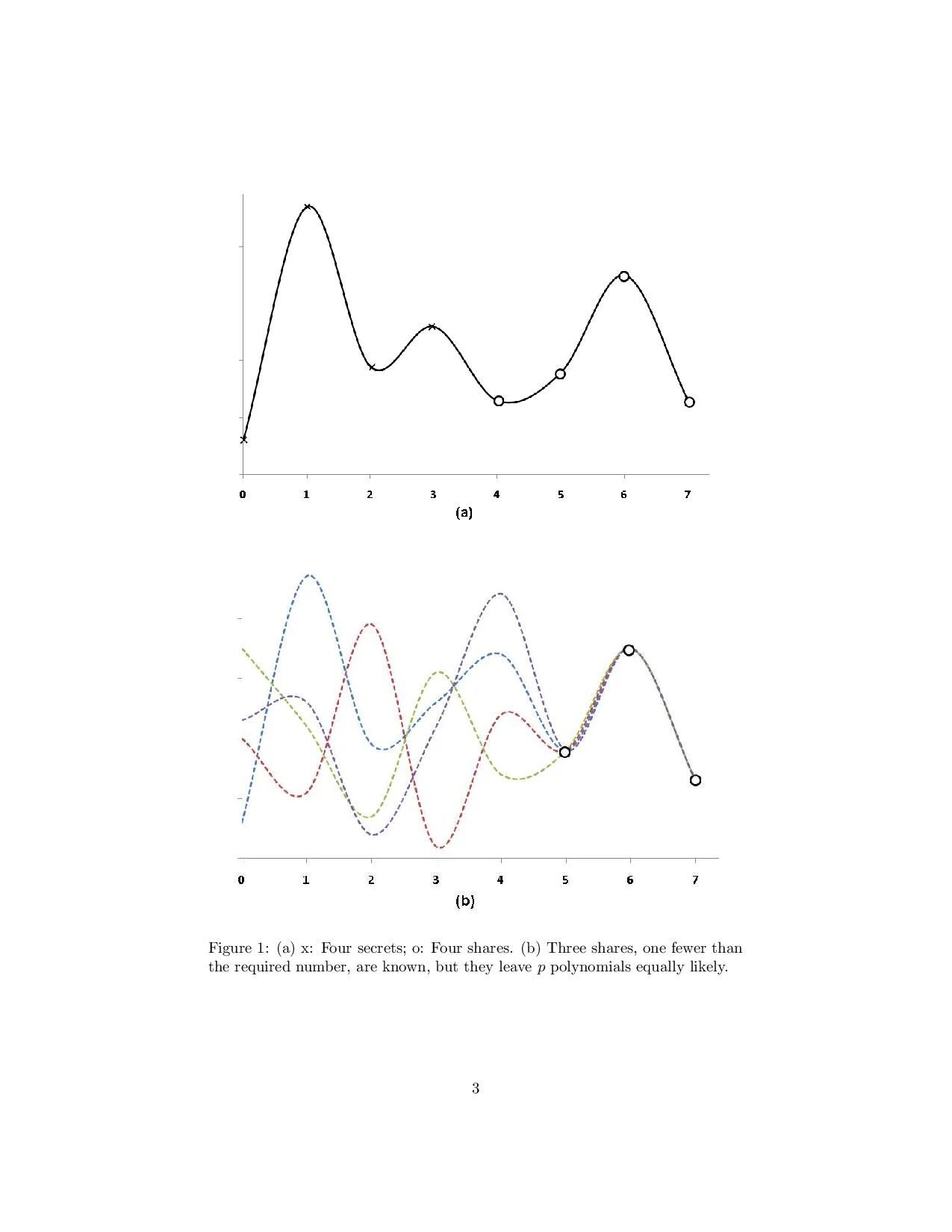
Figure 1 illustrates that p polynomials remain equally probable if we have the knowledge of only 3 shares (out of 4 required) shares (points). Example. Let s 0 = 10, s 1 = 23, s 2 = 16, and s 3 = 25 be four secrets that are to be shared between 6 players such that any 4 of them can reconstruct all the 4 secrets, i.e. n = 6 and k = 4. Let p = 31. We apply Algorithm 2 as follows, 1. Map the 4 secrets as 4 distinct points P 1 = (0, 10), P 2 = (1, 23), P 3 = (2, 16), and P 4 = (3, 25).
- Generate a polynomial f (x) by interpolating points P 1 , P 2 , P 3 , and P 4 as follows, 4. The shares are given by (4,24), (5,18), (6,12), (7,11), (8,20), and (9,13).
This completes the construction of the shares by the algorithm. The reconstruction phase uses any four shares from step 4 above and interpolates them to compute f (x). Then sampling f (x) at points x=0, 1, 2 and 3 would reveal s 0 , s 1 , s 2 , and s 3 respectively.
If an adversary or colluding players determine three shares out of the required four shares in the above example, only a quadratic polynomial can be reconstructed leaving 31 possibilities for the fourth share equally likely. Each of these 31 possibilities give rise to 31 unique cubic polynomials. Only one of these 31 polynomials will pass through all the secrets. Hence the probability of computing the secrets even after the knowledge of k -1 = 3 shares is 1 p = 1 31 . In practice, the primes chosen are very large (on the order of 1024 bits). Since the secrets can be random numbers from the field, the knowledge of k -1 shares leaves p possibilities for the last share, which can only be guessed correctly with a small probability on the order of 1 2 1024 . Consequently, knowledge of only k -2 shares reduces the probability to ( 1 2 1024 ) 2 , and so on in general if t shares are known then the secret can be guessed with a small probability of ( 12 1024 ) k-t . This level of security may be sufficient in many applications, such as the sensor networks where at any given time only a few sensor may be compromised.
A variant of Algorithm A is the case where the interpolating points are randomly chosen with the constraint that they don’t overlap with the x-coordinates of the shares.
We have presented a space efficient secret sharing scheme. The proposed method can also be used to encode a large secret, by dividing the secret into smaller pieces that are shared between several parties. Further it may be used for secure transmission of data over parallel communication channels or secure online data storage, providing efficiency higher than the method of Garay et al. [8].
This content is AI-processed based on ArXiv data.