Space Efficient Secret Sharing
This note proposes a method of space efficient secret sharing in which k secrets are mapped into n shares (n>=k) of the same size. Since, n can be chosen to be equal to k, the method is space efficient. This method may be compared with conventional secret sharing schemes that divide a single secret into n shares.
💡 Research Summary
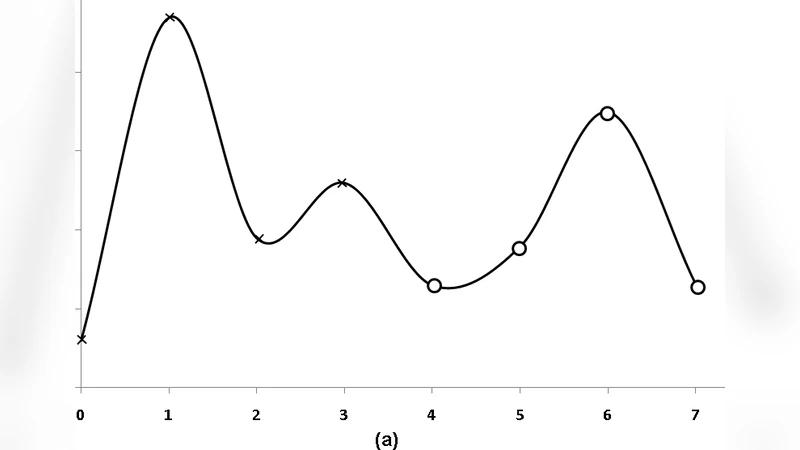
The paper introduces a space‑efficient secret‑sharing scheme that simultaneously distributes k secrets among n participants (with n ≥ k). Unlike the classic Shamir scheme, which encodes a single secret into n shares and incurs an n‑fold storage overhead, the proposed method maps each of the k secrets to a distinct point (i, s_i) in the finite field ℤ_p (p a large prime). Using Lagrange interpolation, a degree‑(k‑1) polynomial f(x) is constructed whose coefficients are linear combinations of the secrets. The polynomial is then evaluated at n new x‑coordinates (k, k+1, …, k+n‑1), producing shares of the form (x, f(x)).
Reconstruction requires any k shares. By interpolating these k points (or equivalently solving a Vandermonde linear system), the original polynomial f(x) is recovered, and evaluating f at x = 0,…,k‑1 yields the original secrets s_0,…,s_{k‑1}. Because the polynomial’s degree equals the number of unknown coefficients, fewer than k shares leave one coefficient undetermined, making the secret space uniformly large. With only k‑1 shares, the missing share can be any of the p possible field elements, giving an adversary a success probability of 1/p. In practice p is chosen to be on the order of 2^1024, rendering brute‑force guessing infeasible; the probability drops exponentially as (1/p)^{k‑t} when t shares are known.
The scheme’s storage efficiency stems from the fact that each share contains essentially (n/k) times the size of a single secret. By setting n = k, each share is the same size as one secret, eliminating the multiplicative storage blow‑up of traditional schemes. Computationally, the algorithm requires only finite‑field arithmetic, Lagrange interpolation, or the inversion of a k × k Vandermonde matrix—operations that are polynomial‑time and well‑understood.
A concrete example with k = 4, n = 6, and p = 31 demonstrates the construction: the secrets (10, 23, 16, 25) are interpolated into f(x) = 6x³ + 3x² + 4x − 21 (mod 31). Six shares are generated, and any four suffice to recover the original polynomial and thus the four secrets. The authors also discuss a variant where the interpolation points are chosen randomly, provided they do not collide with the share x‑coordinates, further enhancing flexibility.
Potential applications include sensor networks where only a few nodes may be compromised at any time, parallel data transmission over multiple channels, and secure distributed storage of large secrets split into smaller pieces. Compared with the Garay‑et‑al. (1997) distributed storage scheme, the proposed method offers higher storage efficiency while preserving the information‑theoretic security guarantees of Shamir’s original construction.
In summary, the paper contributes a novel “k‑out‑of‑n” secret‑sharing protocol that (1) compresses k independent secrets into a single polynomial, (2) achieves near‑optimal storage overhead by allowing n = k, (3) retains unconditional security—knowledge of fewer than k shares yields only a negligible guessing advantage, and (4) remains computationally lightweight, making it attractive for resource‑constrained or high‑security distributed systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment