Steganography An Art of Hiding Data
In today’s world the art of sending & displaying the hidden information especially in public places, has received more attention and faced many challenges. Therefore, different methods have been proposed so far for hiding information in different cover media. In this paper a method for hiding of information on the billboard display is presented. It is well known that encryption provides secure channels for communicating entities. However, due to lack of covertness on these channels, an eavesdropper can identify encrypted streams through statistical tests and capture them for further cryptanalysis. In this paper we propose a new form of steganography, on-line hiding of information on the output screens of the instrument. This method can be used for announcing a secret message in public place. It can be extended to other means such as electronic advertising board around sports stadium, railway station or airport. This method of steganography is very similar to image steganography and video steganography. Private marking system using symmetric key steganography technique and LSB technique is used here for hiding the secret information.
💡 Research Summary
The paper presents a novel application of steganography for real‑time secret communication through public digital billboards. While traditional encryption protects the content of a message, it leaves the existence of a protected stream visible to an observer; steganography, by contrast, aims to hide the very presence of the secret. The authors review basic steganographic concepts, compare it with encryption and digital signatures, and list the essential requirements for any digital hiding technique: integrity of the hidden data, imperceptibility of the stego object, non‑interference with watermarking, and the assumption that an attacker knows a secret exists.
After summarising fragile versus robust steganography and enumerating common media (binary files, text, images, audio, video) and embedding methods (LSB, DCT, wavelet), the authors focus on a specific scenario: embedding secret information into the frames that are displayed on an electronic advertising board. The system is split into three functional units. Unit 1 creates ordinary advertisement content; Unit 2 applies a private‑key LSB embedding algorithm before the data are sent to the display; Unit 3 shows the resulting frames on the billboard, captures them with a camera, and runs a decoder to retrieve the hidden message.
The embedding algorithm works as follows. A secret key of 24 bits is generated: the first 8 bits (red) specify the number of rows R, the next 8 bits (blue) specify the number of columns C, and the following 16 bits (green) constitute a pattern that determines which LSB (first or second) of each pixel will be altered. The cover image is divided into R × C blocks; each block carries exactly one secret bit, which is spread across the block according to the pattern. If a pattern bit is 0, the first LSB of the pixel is forced to match the secret bit; if it is 1, the second LSB is used. This redundancy makes the scheme tolerant to minor pixel modifications. For longer messages the data are split across multiple frames. Decoding simply reverses the process using the same key; without the key the stego image appears identical to the original to the naked eye.
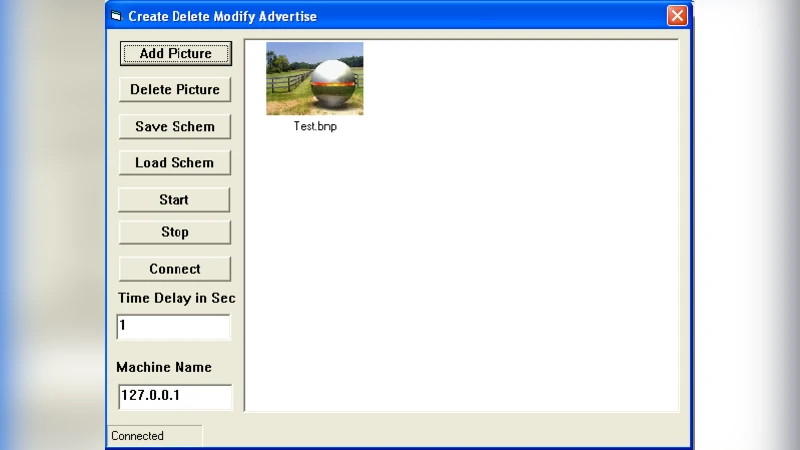
Performance is evaluated on three criteria: (1) integrity of the hidden data after embedding, (2) visual imperceptibility of the stego frames, and (3) accuracy of the recovered message. Four software modules were implemented to create, modify, embed, display, and decode the data. Sample results show that the stego images are visually indistinguishable from the originals and that the secret bits can be perfectly extracted from captured frames.
In the conclusion the authors acknowledge that many existing steganographic techniques are still vulnerable to statistical detection and removal, and they call for more rigorous robustness definitions and benchmark watermarking tests. Nevertheless, the proposed billboard‑based scheme demonstrates that large volumes of secret information can be transmitted covertly in a public setting, especially when combined with conventional encryption to further obscure the hidden payload. Potential applications span personal privacy, corporate communication, and military operations, though practical deployment would require stronger key‑distribution mechanisms, resistance to compression artifacts, and quantitative assessments of processing speed and image quality (e.g., PSNR, SSIM).
Comments & Academic Discussion
Loading comments...
Leave a Comment