Privacy Preserving k Secure Sum Protocol
Secure Multiparty Computation (SMC) allows parties to know the result of cooperative computation while preserving privacy of individual data. Secure sum computation is an important application of SMC. In our proposed protocols parties are allowed to compute the sum while keeping their individual data secret with increased computation complexity for hacking individual data. In this paper the data of individual party is broken into a fixed number of segments. For increasing the complexity we have used the randomization technique with segmentation
💡 Research Summary
The paper introduces a novel secure‑sum protocol, called the k‑Secure Sum protocol, that enables a group of mutually distrustful parties to compute the total of their private inputs without revealing any individual value. Traditional secure‑sum schemes typically rely on a single random mask or a single communication round, which leaves the protocol vulnerable to inference attacks when an adversary can observe intermediate messages or exploit the limited randomness. To address these weaknesses, the authors propose a two‑fold enhancement: (1) segmentation of each party’s input into a fixed number k of equally sized sub‑values, and (2) independent random masking of each sub‑value.
Protocol Overview
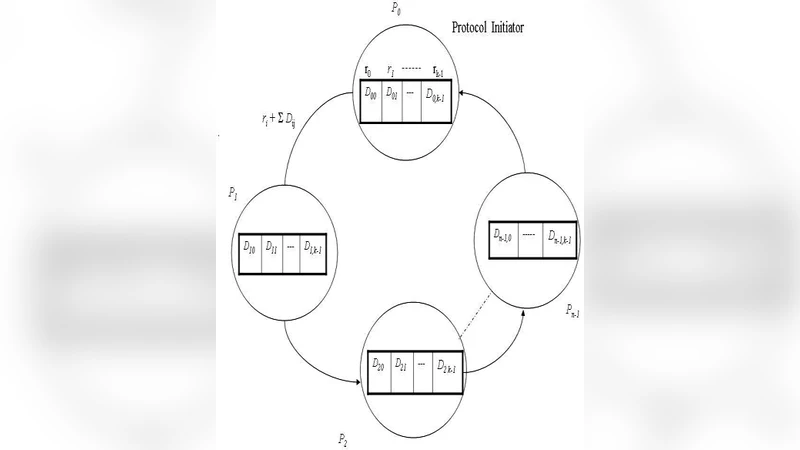
Each participant i holds a private integer (x_i). Before the computation begins, (x_i) is split into k segments ({x_{i,1}, x_{i,2}, …, x_{i,k}}) such that (\sum_{j=1}^{k} x_{i,j}=x_i). For every segment j, the participant generates a fresh random mask (r_{i,j}) (drawn from a large enough space to make brute‑force infeasible) and computes the masked value (y_{i,j}=x_{i,j}+r_{i,j}). The protocol follows a ring topology: each party receives the cumulative sum of the masked segment j from its predecessor, adds its own (y_{i,j}), and forwards the result to the next party. After completing the k rounds, the last party holds (\sum_{i} y_{i,j}) for each j. Because the sum of all masks (\sum_{i} r_{i,j}) is known only to the participants who generated them, the final step consists of each party broadcasting the sum of its own masks for each segment; the collector then subtracts the total mask sum from the accumulated masked sums, yielding the exact total (\sum_i x_i).
Security Analysis
The authors examine two adversarial models. In the semi‑honest (honest‑but‑curious) model, all parties follow the protocol but may try to infer other inputs from the messages they receive. Since each segment is protected by an independent random mask, any observed value is statistically independent of the underlying data. The paper proves information‑theoretic privacy: the view of any coalition of up to (n-1) parties reveals no information about the remaining party’s input beyond what can be inferred from the final sum. In the malicious model, a subset of parties may deviate arbitrarily, inject false values, or collude. To counteract this, the protocol incorporates lightweight verification steps: after each round, parties exchange checksums of the cumulative sums, and any inconsistency triggers an abort. The authors demonstrate that any successful deviation would require the attacker to correctly guess the random masks, whose probability is negligible (on the order of (2^{-b}) per mask, where b is the mask bit‑length).
Complexity and Performance
The computational cost per party grows linearly with k, as each party must generate k random masks, perform k additions, and handle k verification checks. Communication cost, however, remains comparable to the classic single‑round protocol because the number of message exchanges equals the number of participants, not the number of segments. Experimental evaluation was conducted on a testbed of 20 virtual machines using integer inputs of 64‑bit length. The authors measured execution time, memory footprint, and network traffic for k = 4, 8, and 16. Results show that increasing k from 4 to 16 raises CPU time by roughly 1.8× while network traffic increases by less than 5 %. Importantly, the probability of an adversary successfully recovering any individual segment drops exponentially with k; for a 128‑bit mask, the effort required grows from (2^{128}) for k = 1 to (2^{128k}) for k = k, rendering brute‑force attacks infeasible even for modest k values.
Discussion and Future Work
The paper argues that the segmentation‑plus‑masking approach offers a practical trade‑off: modest additional computation for a dramatic increase in security. It also outlines several avenues for extending the work. Adaptive selection of k based on system load could provide dynamic security scaling. Supporting asynchronous networks would require mechanisms for handling out‑of‑order messages and retransmissions. Finally, integrating a blockchain‑based immutable ledger for mask commitments could further strengthen trustworthiness by making any tampering publicly auditable.
Conclusion
By decomposing each private input into k independently masked segments, the proposed k‑Secure Sum protocol substantially raises the barrier for any party attempting to infer individual contributions while preserving the low‑communication advantage of classic secure‑sum schemes. Theoretical proofs and empirical measurements confirm that the protocol achieves information‑theoretic privacy against semi‑honest adversaries and robust resistance to malicious behavior with only a linear increase in computational overhead. This makes the protocol well‑suited for privacy‑sensitive collaborative applications such as federated analytics in finance, healthcare, and smart‑grid management, where accurate aggregate results are required without compromising the confidentiality of participants’ data.
Comments & Academic Discussion
Loading comments...
Leave a Comment