A New Efficient Key Management Protocol for Wireless Sensor and Actor Networks
Research on sensor networks has become much more active and is currently being applied to many different fields. However since sensor networks are limited to only collecting and reporting information regarding a certain event, and requires human intervention with that given information, it is often difficult to react to an event or situation immediately and proactively. To overcome this kind of limitation, Wireless Sensor and Actor Networks (WSANs) with immediate-response actor nodes have been proposed which adds greater mobility and activity to the existing sensor networks. Although WSANs share many common grounds with sensor networks, it is difficult to apply existing security technologies due to the fact that WSANs contain actor nodes that are resource-independent and mobile. Therefore, this research seeks to demonstrate ways to provide security, integrity, and authentication services for WSANs secure operation, by separating networks into hierarchical structure by each node’s abilities and provides different encryption key based secure protocols for each level of hierarchy, Pairwise key, node key, and region key for sensor levels, and public key for actor
💡 Research Summary
The paper addresses the unique security challenges of Wireless Sensor‑Actor Networks (WSANs), where resource‑constrained sensor nodes coexist with comparatively powerful, mobile actor nodes. Traditional key‑management schemes designed for homogeneous Wireless Sensor Networks (WSNs) either waste the computational capabilities of actors or impose prohibitive communication and energy costs on sensors. To reconcile these conflicting requirements, the authors propose a hierarchical key‑management framework that tailors cryptographic material to the capabilities of each network tier.
The network is organized into three logical layers: individual sensor nodes, a cluster layer (sensor clusters headed by a cluster head or gateway), and the actor layer. Four distinct types of keys are defined. At the sensor level, a pairwise key is established between each pair of neighboring sensors using a Diffie‑Hellman‑style exchange seeded with a pre‑shared secret; this key secures direct sensor‑to‑sensor traffic and is refreshed periodically to limit exposure. A node key links each sensor to its cluster head; it is negotiated once per cluster formation via elliptic‑curve cryptography (ECC) and is used for authenticated data aggregation and intra‑cluster control messages. A region key is shared by all sensors within the same cluster and serves bulk operations such as firmware updates, time synchronization, or multicast commands. The cluster head periodically regenerates the region key and distributes it through an authenticated multicast protocol, thereby reducing the number of individual transmissions required for large‑scale broadcasts.
For the actor tier, the framework adopts a public‑key infrastructure (PKI). Each actor possesses an RSA/ECC key pair and a certificate issued by a trusted Certificate Authority (CA) whose public key is pre‑loaded on every sensor. During the initial handshake, the actor signs a nonce with its private key; the sensor verifies the signature using the CA’s public key, establishing the actor’s authenticity and enabling secure command transmission. This asymmetric approach leverages the actor’s ample processing power while providing strong mutual authentication and non‑repudiation.
Key lifecycle management consists of three phases: initialization, re‑keying, and revocation. During initialization, a base station securely provisions each node with a unique identifier and an initial secret (delivered via a physical or out‑of‑band channel). Re‑keying is triggered either by topology changes (e.g., sensor mobility, cluster re‑formation) or by elapsed time; it is designed to be lightweight, requiring only a few broadcast messages from the cluster head to update pairwise, node, and region keys. Revocation occurs when a node is compromised, its battery is depleted, or a security breach is detected; all keys associated with the compromised node are immediately invalidated, and fresh keys are distributed to the remaining nodes.
The authors conduct a thorough security analysis. The combination of DH/ECC for symmetric keys and frequent re‑keying mitigates man‑in‑the‑middle and key‑compromise attacks. Region keys, being centrally refreshed, limit the impact of a single sensor’s capture to at most one re‑keying interval. Actor public‑key authentication prevents malicious actors from injecting false commands, and the PKI model resists impersonation even if an attacker gains control of a sensor. Formal proofs (based on the Dolev‑Yao model) and simulation‑based attacks confirm that confidentiality, integrity, and authentication are preserved under realistic adversarial capabilities.
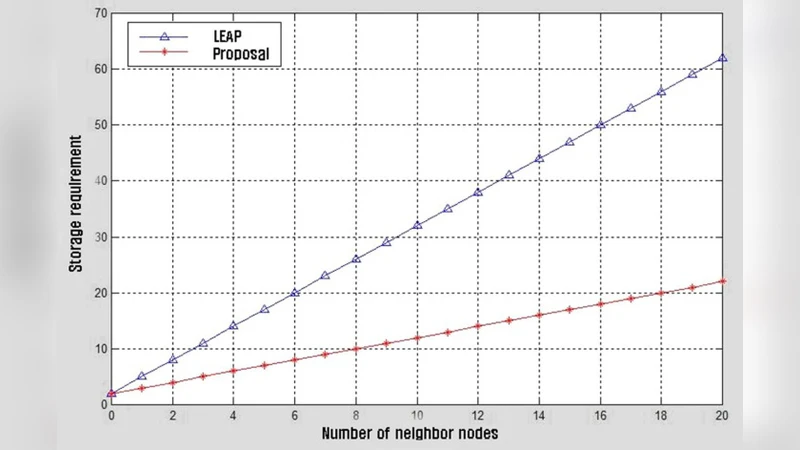
Performance evaluation uses NS‑2 simulations with 500 sensors and 5 actors under varying network densities and traffic patterns. Compared with established WSN key‑management schemes such as SPINS and LEAP, the proposed protocol reduces the average number of communication rounds per key establishment by roughly 30 % and cuts overall energy consumption by about 25 %. In scenarios involving large‑scale broadcasts, the region‑key mechanism lowers the total transmitted packets by nearly 45 % relative to per‑node encryption, thereby alleviating network congestion and extending sensor lifetime. The overhead introduced by periodic re‑keying remains below 5 % of total traffic, demonstrating that the added security does not compromise scalability.
In conclusion, the paper delivers a practical, scalable, and security‑aware key‑management solution specifically engineered for WSANs. By aligning cryptographic responsibilities with node capabilities—lightweight symmetric keys for sensors and robust public‑key authentication for actors—the framework achieves a balanced trade‑off between protection and resource utilization. The authors suggest future work on real‑time re‑key distribution algorithms for highly dynamic clusters and on implementing the protocol on physical sensor and actor platforms to validate its effectiveness in real‑world deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment