Information Flow in Secret Sharing Protocols
The entangled graph states have emerged as an elegant and powerful quantum resource, indeed almost all multiparty protocols can be written in terms of graph states including measurement based quantum computation (MBQC), error correction and secret sharing amongst others. In addition they are at the forefront in terms of implementations. As such they represent an excellent opportunity to move towards integrated protocols involving many of these elements. In this paper we look at expressing and extending graph state secret sharing and MBQC in a common framework and graphical language related to flow. We do so with two main contributions. First we express in entirely graphical terms which set of players can access which information in graph state secret sharing protocols. These succinct graphical descriptions of access allow us to take known results from graph theory to make statements on the generalisation of the previous schemes to present new secret sharing protocols. Second, we give a set of necessary conditions as to when a graph with flow, i.e. capable of performing a class of unitary operations, can be extended to include vertices which can be ignored, pointless measurements, and hence considered as unauthorised players in terms of secret sharing, or error qubits in terms of fault tolerance. This offers a way to extend existing MBQC patterns to secret sharing protocols. Our characterisation of pointless measurements is believed also to be a useful tool for further integrated measurement based schemes, for example in constructing fault tolerant MBQC schemes.
💡 Research Summary
The paper investigates the interplay between graph‑state secret‑sharing schemes and measurement‑based quantum computation (MBQC) by using the concept of flow as a unifying graphical framework. Graph states are known to underpin a wide range of multipartite quantum protocols, and the authors exploit this universality to express both secret‑sharing access structures and MBQC patterns in a single language.
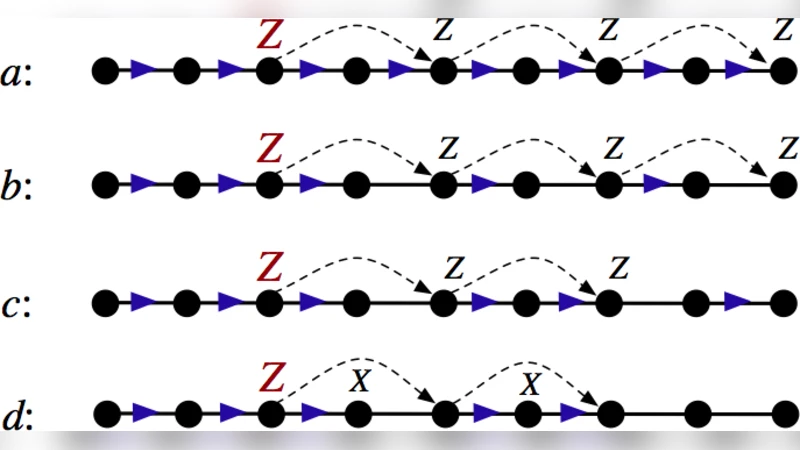
The first major contribution is a purely graphical characterization of which subsets of players can reconstruct the secret in a graph‑state secret‑sharing protocol. By mapping each player to a vertex and the secret to a distinguished vertex, the authors show that a subset can recover the secret exactly when there exists a flow from the secret vertex to all vertices in the subset. If a flow exists, the measurement outcomes of the involved vertices can be combined (using the usual stabilizer correction rules) to retrieve the secret; if the flow is blocked, the outcomes are completely random, guaranteeing information‑theoretic security. This graphical description is concise, avoids heavy algebra, and enables the direct application of known graph‑theoretic results—such as minimum cuts, connectivity, and matchings—to design new access structures. Using these tools the authors generalize several existing schemes and propose new secret‑sharing protocols with provable security properties.
The second contribution addresses the question: when can a graph that already possesses a flow be extended by adding vertices that do not affect the implemented unitary? The authors introduce the notion of pointless measurements—measurements whose outcomes have no influence on the overall computation. They derive necessary conditions for a vertex to support a pointless measurement: (i) the vertex must belong to a subgraph that is independent of the flow‑determined dependency graph, and (ii) the phases on edges incident to the vertex must satisfy a specific algebraic relation that cancels any by‑product operators. When these conditions hold, the added vertex can be interpreted either as an unauthorised player in a secret‑sharing scenario or as an error‑qubit in a fault‑tolerant MBQC scheme. Crucially, the presence of such vertices does not destroy the original flow, so the computational power of the pattern is preserved.
Combining the two results, the authors construct integrated protocols where a flow‑based MBQC pattern is augmented with pointless‑measurement vertices to simultaneously achieve secret sharing and error detection/correction. They present explicit constructions, analyze resource overhead (additional qubits and measurement depth), and demonstrate via numerical simulation that the integrated patterns retain the efficiency of the original MBQC while providing the desired security guarantees.
In the discussion, the paper emphasizes that the graphical flow formalism offers a powerful design tool: access structures become visual cut‑sets, and the ability to insert pointless measurements provides a systematic way to embed unauthorised parties or ancillary error‑correction qubits without compromising the implemented unitary. The authors suggest several avenues for future work, including extending the analysis to more general flow variants (g‑flow, Pauli‑flow), handling multiple secrets, and experimental implementation on photonic or superconducting platforms. Overall, the work bridges two previously separate strands of quantum information—secret sharing and measurement‑based computation—by showing that they can be treated within a common, graph‑theoretic language, thereby opening the door to more integrated and resource‑efficient quantum network protocols.
Comments & Academic Discussion
Loading comments...
Leave a Comment