Attacking an OT-Based Blind Signature Scheme
In this paper, we describe an attack against one of the Oblivious-Transfer-based blind signatures scheme, proposed in [1]. An attacker with a primitive capability of producing specific-range random numbers, while exhibiting a partial MITM behavior, i…
Authors: Stylianos Basagiannis, Panagiotis Katsaros, Andrew Pombortsis
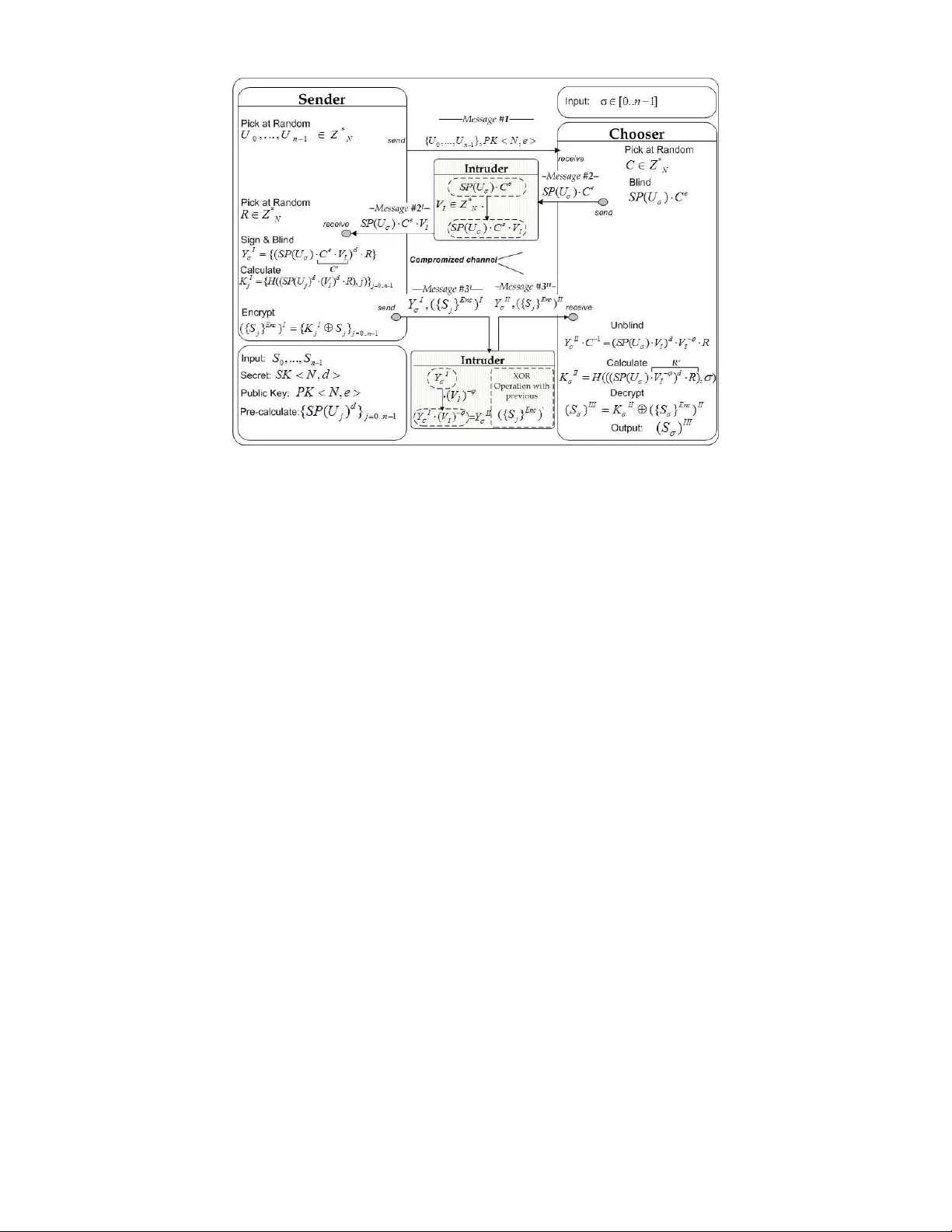
1 Ab st rac t — In thi s pap er, w e des crib e an att ack a gai nst on e of the O bliv ious - Tra nsfe r - bas ed bl ind s ign atur es sc heme, pr opos ed in [1 ]. An atta ck er w it h a primi tive cap abil ity of prod ucin g spe cif ic - rang e ran dom numb ers , w h ile ex hi biti ng a p arti al M ITM beh avio r , is abl e to co rrup t the co mmunic atio n betw e en the pro toc ol pa rti cipa nts. Th e at tack is q uite ef fici ent as i t l ead s to a pro toc ol commun icat i on co rrup tion and ha s a sou nd -min imal co mputat ion al co st . W e prop ose a s olut ion to f ix the sec urit y f law . In de x T erm s — O bliv ious T rans fer , b lind si gna ture s. I. I NTR OD UC TI ON B LI VIOU S T R ANS FER ( OT ) c ons titu tes a p owe rful t oo l us ed to da y in m od ern cr ypto gr ap hy . I n th e fir st in tro du cti on o f th e 2 1 OT me cha nis m by R ab in [ 2 ], i t is a ssu med tha t in a co mmu nic ati on s yste m , A lice tra nsm it to Bo b a two -pa rt me ssa ge, wh er e o nly th e o ne p ar t is th e se cre t tha t Ali ce wa nts to sh are . F rom B ob ’s s ide , B o b d oe s no t kn ow whi ch o ne of th e two is th e re al sec re t, so h e s ele cts o ne o f th em wit h p rob ab ili ty ½ o f suc ce ss ( or ½ of fail ure ). In th e re la ted b ibl iog rap hy, O T b as ed s ecu rity p ro toc ol s [ 3 ] [ 4 ] th at ai m to gu ara nte e a v ari ety o f se cu rity pr op er ties suc h as a no nymit y o r p ri vac y o f th e p ar tic ipa nts , e spe cia lly wh en O T is co mbi ned with o the r cr ypto gr ap hic p rim itiv es, e. g. b lin d s ign atu res [ 5 ]. T hro ugh the se wor ks , OT has be en invo lv ed in to s eve ral imp ro vem ent s r ega rd ing effic ien cy a nd o f the O T - b ase d co m m unic at ion sys tems . T he b asi c 2 1 OT , de scr ibe d ab ov e, has be e n rep la ced by mec han isms o f 1 n OT sh own i n [ 3 ], whe re th e S e nd er d isp atc h N me ssa ge to th e C ho os er , a nd th e Ch o ose r se lec ts the a pp ro pr iate m ess age wit h o ut kno wing th e in i tial se lec tio n o f th e S en de r . In rep o rts [ 6 ] a nd [7 ] , t he O T m ech ani sm is c omb in ed wit h va rio us c ryp tog rap hic t ech niq ue s , in ord er t o p ro vid e the in vol ved p ar tic ipa nts wi th ev en mo re s ec urit y g uar ant e es . O T is co mb ined with s igna tur e sc hem es p ro vid ing st ro ng fa irne ss , an on ymity an d p riva cy o f t he co mmu nic ati on. B o th o f t h e re po rts a lso pro vi de a de ta iled a na lysis o f th e p ro to co l in te rms o f a no nymit y an d p riv ac y. T he re a re a lso re po rt s lik e [ 8 ] , whe re se cur ity t hre ats ove r th e O T -b as ed p r oto co l sc he mes ha ve b ee n c lass ifie d in to hi gh a nd l ow co st a tta cks . A ll the se ki nd s o f se cur ity th rea ts a re m ana ge d t o su cce ed re gar din g th e co mp uta tio nal co st of t he enc ryp tio n us ed be twee n th e p rot oc ol s ’ pa rti cip an ts, wher e a n ad ver sar y is c ons ide r co nt a ini ng t he m axi mum co mp uta tio nal p owe r, p erfo rm in g a va rie ty o f at tac k a cti ons . In thi s pa pe r, we p re sen t an at tac k aga inst the OT -b as ed Th e au tho rs are wi th t he Dep t. of Info r m ati cs, Aris tot l e U niv ersity of Th essa lonik i , 54 12 4 , Greec e . E ma il: { b asa gs, k ats aros, apo mb o }@ csd .au th. gr . d oub le b lin d si gna tur e sc hem e p ro toc ol d esc rib ed i n [ 1 ] . M or e p rec ise ly, we sh ow th at a p art ial M IT M i ntr ude r wit h a lo w co mp uta tio nal c os t ca n c or rup t t he p ro to co l’s c omm unic at ion b y int egr ity vi ola tin g o ne o f the pr ot oc ols ’ exc han ged me ssa ges ( by tag ging s pe cifi c r and om nu mb ers ) . As a r esu lt th e p ro toc ol s’ a gen ts wil l a cce pt the co rr up tio n o ccu rre d , whi ch misin ter pr ets th e o ver all co mmu nic atio n. II . T H E O T - BAS ED BLIN D SIGN ATUR E P RO T OC OL T his p ap er fo cus es o n th e an alys is o f a v ari ant 1 -o ut - of - n O bli vio us T ra nsfe r ( 1 n OT ) ba se d o n b lin d s igna tur es p ro toc ol . T he sp ec ific p ro to co l inc or po ra tes a bl ind mec ha n ism fr om b oth the S en d er ’s an d th e C h oo ser ’s sid e. T o ac hie ve cr ypt ogr ap hic e fficie nc y th e pr oto co l invo lve s a s eri es of se cur ity pe rsp ec tive s suc h a s p ub lic k ey c ryp to gra phy, b lin d sig nat ure s a nd a keye d has h fun cti on. A ran do m n umb er ge ner ato r fo r b ot h of th e p ar tic ipa nts is al so us ed in o rd er to o ver co me p re di cta bil ity a tta cks ca use d b y a n In tru de r . T h e fo llo wing no tati on is used t hro ugh ou t th e p ap er : N RS A mod ulu s { 0 1 , ..., n S S } S end er p o sses in itia lly n sec ret str ing s S i σ Ch o ose r po sse s i niti ally an in t ege r σ [0.. 1 ] n H P re - agr eed H as h F unc tio n , SK N d Se cr et Ke y , PK N e P ub lic Ke y { 0 1 , ..., n U U } Ra nd om num be rs * 0 1 , ..., n N U U Z ( ) SP Se cu re pa dd ing sch eme fo r R SA C Ra nd om num be r * N C Z R Ra nd om num be r * N R Z Y B lind S ign atu re for the S end er 0.. 1 j n K E ncr ypti on Ke ys for the S en de r X OR o pe rat or d 1> >d 2 Ri ght shi ft -b it op er ato r T h e S en de r h as n in put s ec ret s trin gs, { 0 1 , ..., n S S } a nd the Ch o ose r ’s i npu t is a n int ege r σ [0.. 1 ] n . B ec aus e of th e 1 n OT , th e C ho ose r s hou ld lea rn a se cr et S an d n oth ing o n an y ot her { 0 1 , ..., n S S } - { S }. O n th e ot her h and , th e S en der sh oul d le arn n oth ing a bo ut . T he p ro toc ol d esc rib ed he re p rov id es unc on dit ion al p rot ec tio n fo r the Ch o ose r an d co mp uta tio nal p ro te ctio n i n th e r and o m o r acl e m od el for th e S end er . D ue to th e O T o per ab ilit y, th e sp ec ific p ro to co l ma y b e o ften in vok ed mu ltip le tim es be twee n t he p ar tici pa nts. T he b asi c s tep s o f th e d esc rib ed p ro toc ol ar e i llus tra ted in Fi g . 1 a nd ca n b e summ ar ize d a s fo llo ws: A ttackin g an OT -B ased B lind Sig natu re S cheme St ylia nos Bas agia nni s , Pan agio tis Ka tsar os a nd A nd rew Pomb ort sis O 2 Fig . 1 . The Dou ble B lin d P roto col S chem e B as ed o n O bliv iou s Tra nsfer 1 ) In itia lly t he Se nd er p ick s n ra nd om n umb ers { 0 1 , ..., n U U } an d th e C ho o ser in pu ts a n int ege r σ o ver th e ra nge [0 .. 1 ] n . T he n, S en de r se lec t s h is R SA k eys a nd sen d s th em a lo ng with the set o f its num be rs to the Ch oo se r . 2 ) U po n th e fir st m ess age i s re ce ip ted , the C ho os er wil l ra nd oml y ( acc or din g to σ ) s ele ct a nu mbe r U a nd co mp ute th e ( ) SP U , whi ch in tur n, it is bli nd ed with a r and om se lec ted nu mbe r C , in o rd er to pr od uc e ( ) e SP U C . He t hen se nd s t he me ssa ge to Se nd er . 3 ) W he n t he S en de r r ece ive s th e se co nd me ssa ge , he ra nd oml y se lec ts h is b lind fa cto r R ( ran do m nu mbe r) . T he n he sig ns (wi th S K< N , d> ) and b lin ds (wi th R ) the m ess age , cr ea ting {( ( ) ) } e d Y SP U C R . O n the ne xt ste p, th e S en de r cr ea tes j K ke ys wi th 0.. 1 j n us ing the p re - ag ree d has h fun ctio n H . T h o s e k eys wi ll b e us ed to en cryp t all th e n str ing se cre t me ssa ges { 0 1 , ..., n S S } us ing the o per ato r. 4 ) O nc e th e S en de r c om ple tes th e e nc rypt ion , o f 0.. 1 { } { } Enc j j j j n S K S , he di spa tch es the th ird m ess age to t he C h oo ser , wh ich co nta in s the b lin d s igna tur e Y an d th e en cryp te d se t o f mes sag es { } Enc j S . A t t his p oin t S en de r ac co mp lish es h is p ar tici pa tio n to t he pro to co l. 5 ) C ho os er r ec eiv es t he t hird me ssa ge a nd mo ve s o n t o un - b lind in g Y with 1 C . W hil e a cq uir ing 1 ( ) d Y C SP U R , he us es his in itia l c ho ice σ to co mp ute the a pp ro pri ate K fo r re vea lin g o nly th e S se cre t me ssa ge. K will be co mpu ted b y ap pl ying the ha sh fun cti on H to the re main ing ( ) d SP U R , re sul ting to (( ( ) ), ) d K H SP U R . 6 ) Onc e K ha s b ee n co mpu ted , th e C ho ose r wi ll a pp ly it in to th e e ncr ypte d se t o f m ess age s { } Enc j S o bta inin g a t a fi nal sta ge , S b y { } Enc S K S , and thu s co mp let ing th e p rot oc ol. At this p o int , the Ch oo se r wi ll ha ve k no wled ge o f S with ou t b ein g a ble to k now a nythi ng e lse of t he s et { } Enc j S . As a s ec urit y -co ns equ enc e of the pro to co l’s co mpl eti on, th e o utc o me will be the pr ese rv atio n o f info rm atio n -th eo ret ic p riva cy fo r the S en de r and co mpu tati on al p riva cy for th e Ch o ose r ac co rdi ng to [ 1 ] . II I. A NALY SIS O F THE ATT AC K Si mila r s ecu r ity a nal ysis rep or ts, suc h as [ 8 ], hav e in dic ate d se cur ity th rea ts t hat ma y be la un c hed i n O T -b ase d co mmu nic ati on syst ems . T h e maj or ity of the m a re b ase d ov er an in trud er t hat ea ves dr op all the p ro toc ol s’ me ssa ges , co nta ini ng a lso a de gr ee o f co mp uta tio nal p o wer tha t ma y re vea l t o h im, pr evi ou sly u nkn own info rma tio n. An In tru de r ma y lau n ch a s eri es o f ac tio ns t hat co uld lea d th e p rot oc ols ’ pa rtic ip ant s into sec uri ty fail ure s, su ch a s a Do S at tac k fr om the C ho o ser ’s s ide , o r imp ers on atio ns us ing p rev iou sly re co rd ed S en de r ’s me ssag es i n o the r ( sa me p rot oc ol) se ssio ns . W hil e t he p ro to co l a vo id s th os e k ind s o f at tac ks b y u sing d ou ble - bl ind si gna tur es for b oth o f it s p art icip an ts, i t ma y al low In tru d er’ s in teg rity vi ola tio ns, by le ad ing to a co rr upt co mm unic ati on. In the re st o f th is se ctio n, we pr es ent th e at tac k whe re an I ntr ud er , be in g pla ce d as a M IT M e ntit y may co rr up t th e p ro po sed p ro toc ol . A . D esc rip tio n of the A tta ck T he nec ess ary pr ere qu isit es for the In tru de r are th e fo llo wing : a) T he I ntr ud er is a M IT M e ntity am on g th e p ro to co ls’ p art icip an ts tha t eav esd ro ps all the m ess age s, b ) h e ha s th e ab ili ty o f g ene ra ting ra nd om num ber s o ver a s pec ific r ang e o f va lue s a nd c) he c an co nc ate nat e pre vio us ly in ter ce pte d me ssa ges with d ata th at he h as cr ea ted . Fi g . 2 p ro vid es a d eta iled des cr ipt ion o f th e att ack m ou nted ag ain st th e p ro to co l . 3 Fig . 2 . Th e pro pos ed a tta c k T he pr op os ed at tac k is d esc rib ed as fo llo ws: 1 ) In the first ste p, the In tru de r lea ve s the firs t me ssag e un inte rru pt ed to rea ch its inte nd ed de stin ati on. C ho os er u po n re ce ipt of th e me ssa ge , se lec t s, un der un ifor m pr ob ab ilit y d istr ib ut ion , a nu mbe r U ac co rdi ng to his in pu t σ t hat h e ha d in itia lly cho sen ; th e n h e g ene ra te s ra nd om nu mbe r C b lind in g ( ) SP U to fo rm the se co nd mes sag e. 2 ) T h ro ugh a c omp ro mis ed c ha nne l, t he In tru de r r ec eiv es th e sec on d me ssa ge ( ) e SP U C o rigi nat ed fr om th e C ho o se r . T he n , the I nt rud er , u sing a ra nd om nu mbe r gen era to r, co rr upt s th e me ssa ge wi th a r an do m num be r * I V Z cre ati ng ( ) ( ) e I I C V C e I I SP U C V SP U C . T h e S en de r wil l the n cr ea te ( ( ) ) I d SP U C , b lin din g it with * N R Z , h avi ng * * ( ) ( ) I N I N C R Z V C Z , wit h t he ov era ll sig nat ure b eing {( ( ) ) } I I d Y SP U C R . 3 ) P r od uci ng t he a pp ro pr iat e k eys 0.. 1 j n K , th e co rr up ted p rod uc t wi ll b e i nte rse cte d i nto th e (( ( ) ( ) ) d d j I H SP U V R cr ea t in g fals ie I j K s. A s a c on seq uen ce , t he en cryp te d s et { } Enc j S will be e ncr ypte d usin g t he wro ng k eyse t. 4 ) S en der d isp atc hes m essa ge 3 I to th e I n tru de r wh o fro m hi s sid e, co mpu tes aga in a ran do m ( ) , I V d own -b lin din g sig nat ure I Y to ( ) I V I II Y Y with d I C V . A dd itio na lly, th e I ntr ud er se ts {{ } } Enc I j S ' {{ } } Enc j S = {{ } } Enc II j S usi ng a p rev iou sly i nter ce pte d s et o f ' {{ } } Enc j S , fo rwar di ng th e ne w me ssa ge 3 II to th e Ch oo se r . 5 ) Ch oo ser un -b lin ds si gna tur e II Y with 1 C in o rd er t o ca lcu lat e fro m his s ide th e rig ht key K (fa lse I K ) t o de cryp t hi s in itia l c hoi ce S σ . D ue to the p rev io us I ntr ud er ’s o pe ra tio n, Ch o ose r man age s to de cryp t the wro ng S σ ( ( ) III S ) wi tho ut kn owin g it , and th us acc ep tin g th e c or r u pti on mad e. IV . F IXING TH E F LAW AND C O NC LUSION W he n exc ha ngin g th e se co nd an d the th ird m ess age , t he p art icip an ts ma y re - use the alr ead y imp le men ted ha sh fun cti on H wh ich is pr ed ete rmi ned b y t he pr ot oco ls ’ s pe cific at ion s up on t he a gen ts. W hi le s eal ing e C wi th th e ( , ) e f C whe re f i s the ke yed h ash func tio n o f H fro m t he C ho ose r’s sid e , a nd ( , ) R f Y R fro m the Se nd er’ s sid e, an y a lte ra tion ma de to t he e xch ang ed me ssa ges wi ll b e d isca rd ed . S uch a n o pti miza tio n r eq uire s o ne m or e o f ex ec utio n o f the k eye d ha sh fun ctio n fo r b o th o f th e p ar tic ipa nts wh en th e p ro toc ol is co mp let ed , i n o rd er to id ent ify p oss ibl e i ntru de r c or rup tio ns . T he pr ese nte d O T -b ase d b li nd sig nat ure sch eme s ha ve b ee n ad op te d in syste ms suc h as e - auc tio ns an d on lin e -g ami ng , whe re p riva cy re main s the fir st o bj ect ive . H owe ver , suc h co mmu nic ati on pr oto typ es hav e t o p ro vid e , a t the end , ac cu rac y o f the d eli ver ed se rvic es , when the p ro toc ol fina liz es. R EFE RE NC ES [1 ] D . M alk hi an d Y . Sella. “Ob livi ous tran sfer ba sed o n b lind sig nat ures ”, Te ch . R epo rt 20 03 -3 1, Le ibn iz Cen te r, H ebr ew Un ive rsi ty , 2 00 3. [2 ] M . O . R abi n, “H ow to exch an ge sec rets b y obli viou s t ran sfer”, Te ch . M emo TR -81 , A ike n C om pu ta tio n L ab . , H arv ard U niv ersi ty , 198 1. [3 ] M . N aor an d B . P in kas , “Effi cien t Ob livi ous Tran sfer P rotoc ols” , In 1 2 th AC M -SIA M, p. 44 8 -4 57, 20 01 . [4 ] J. Ca men isc h, G . N even, a nd A . S helat , ” Si mula tab le a da pti ve o bliv iou s tra nsfer ”, In E URO CR YPT , p . 57 3 - 59 0 , 20 07. [5 ] C hau m, D .: B lind si gna tures for u ntra ceab le p aym ent s. In C RYP TO, p . 19 9 – 2 03 , 19 83 . [6 ] M . Green and S . Hoh enb erger , “ Blin d id ent ity - ba sed enc rypt ion a nd si mula tab le obli viou s t ran sfer ” , In A SIA CR YPT, p . 26 5 - 28 2 , 20 07 . [7 ] Y . Ish ai, J . Kili an, K . Nis sim , and E . Pet ran k , ” E xten din g o bliv iou s tra nsfers effi ci ently ”, In C RYP TO, p . 1 45 - 16 1 , 20 03. [8 ] S. Lau r a nd H . Lip ma a, “C onsi s ten t Ad apt ive T wo - Pa rty C omp ut atio ns” in IAC R epr int ar ch ive 20 06 /08 8 , 20 06 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment