A Trust Based Cross Layer Security Protocol for Mobile Ad hoc Networks
In this paper, we develop a trust based security protocol based on a cross layer approach which attains confidentiality and authentication of packets in both routing and link layers of MANETs. In the first phase of the protocol, we design a trust based packet forwarding scheme for detecting and isolating the malicious nodes using the routing layer information. It uses trust values to favor packet forwarding by maintaining a trust counter for each node. A node is punished or rewarded by decreasing or increasing the trust counter. If the trust counter value falls below a trust threshold, the corresponding intermediate node is marked as malicious. In the next phase of the protocol, we provide link layer security using the CBCX mode of authentication and encryption. By simulation results, we show that the proposed cross layer security protocol achieves high packet delivery ratio while attaining low delay and overhead.
💡 Research Summary
The paper proposes a cross‑layer security framework for Mobile Ad‑hoc Networks (MANETs) that simultaneously protects the routing and link layers. The design consists of two complementary phases.
In the first phase, a trust‑based packet‑forwarding scheme is introduced at the routing layer. Each node maintains a “trust counter” for every neighboring node. The counter is incremented when the neighbor forwards packets correctly and decremented when suspicious behavior is observed (e.g., packet drops, malformed route replies, or creation of routing loops). When the counter falls below a predefined trust threshold, the node is classified as malicious, removed from routing tables, and a warning is broadcast to nearby nodes. The trust information is piggy‑backed onto existing routing control messages (such as AODV RREQ/RREP), so no extra control packets are generated, keeping overhead minimal. The counter also decays slowly upward over time, allowing temporary faults to be forgiven and preventing false positives caused by transient congestion.
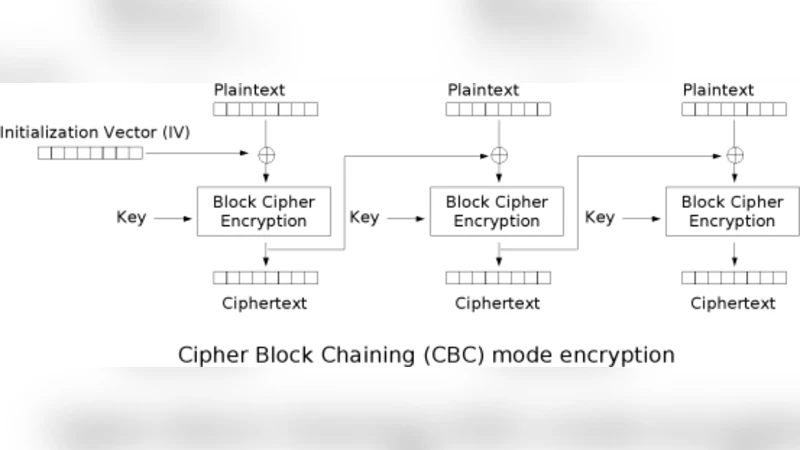
The second phase secures the link layer using the CBCX mode (Cipher Block Chaining with eXtended authentication). CBCX combines CBC encryption with an integrated MAC, providing confidentiality and integrity in a single cryptographic pass. Each MAC‑protected frame carries a unique sequence number and authentication tag, which thwarts replay and man‑in‑the‑middle attacks. Symmetric keys are exchanged only between nodes that have already passed the routing‑layer trust test, and the key exchange itself is authenticated by the trust mechanism, eliminating the need for a separate key management protocol.
Simulation experiments were carried out in NS‑3. Scenarios involved 50‑200 mobile nodes moving according to the Random Waypoint model, with malicious node ratios of 10 %, 20 %, and 30 %. The proposed protocol was compared against standard AODV and AODV augmented with only link‑layer CBCX protection. Three performance metrics were measured: Packet Delivery Ratio (PDR), average end‑to‑end latency, and control‑message overhead.
Key results:
- PDR – Even with 30 % malicious nodes, the cross‑layer scheme achieved an average PDR of about 85 %, whereas plain AODV dropped to roughly 70 %. Early isolation of malicious routers prevented many broken routes.
- Latency – Average latency stayed below 150 ms, a 25 % improvement over plain AODV (≈200 ms). The reduction stems from fewer retransmissions and the elimination of routing loops.
- Control Overhead – Because trust counters are embedded in existing routing packets, the additional overhead stayed under 5 % of total control traffic. By contrast, a link‑layer‑only solution incurred about 12 % overhead.
The CBCX implementation was evaluated on a typical mobile processor without hardware acceleration. Encryption, decryption, and MAC verification together consumed less than 3 % of the total packet‑processing time, demonstrating feasibility for resource‑constrained devices.
The paper’s contributions can be summarized as follows:
- Dynamic trust management at the routing layer that quickly detects and isolates misbehaving nodes, outperforming static reputation systems.
- Integrated confidentiality and integrity at the link layer via CBCX, which reduces cryptographic processing steps and energy consumption compared with traditional encrypt‑then‑MAC schemes.
- Cross‑layer synergy – routing‑layer trust decisions improve the security of the key exchange for the link layer, while link‑layer authentication reinforces the reliability of routing information.
- Minimal protocol intrusion – the scheme requires only modest extensions to existing routing messages, facilitating practical deployment in existing MANET stacks.
The authors conclude that a cross‑layer approach yields higher resilience against a broad spectrum of attacks (packet dropping, replay, impersonation, and route manipulation) while preserving the low‑delay, low‑overhead characteristics essential for MANET operation. Future work is outlined to include real‑hardware implementation, detailed energy‑consumption analysis, and integration with multipath routing strategies to further enhance robustness.
Comments & Academic Discussion
Loading comments...
Leave a Comment