Approximation Algorithms for Link Scheduling with Physical Interference Model in Wireless Multi-hop Networks
The link scheduling in wireless multi-hop networks is addressed. Different from most of work that adopt the protocol interference model which merely take consideration of packet collisions, our proposed algorithms use the physical interference model …
Authors: Shuai Fan, Lin Zhang, Yong Ren
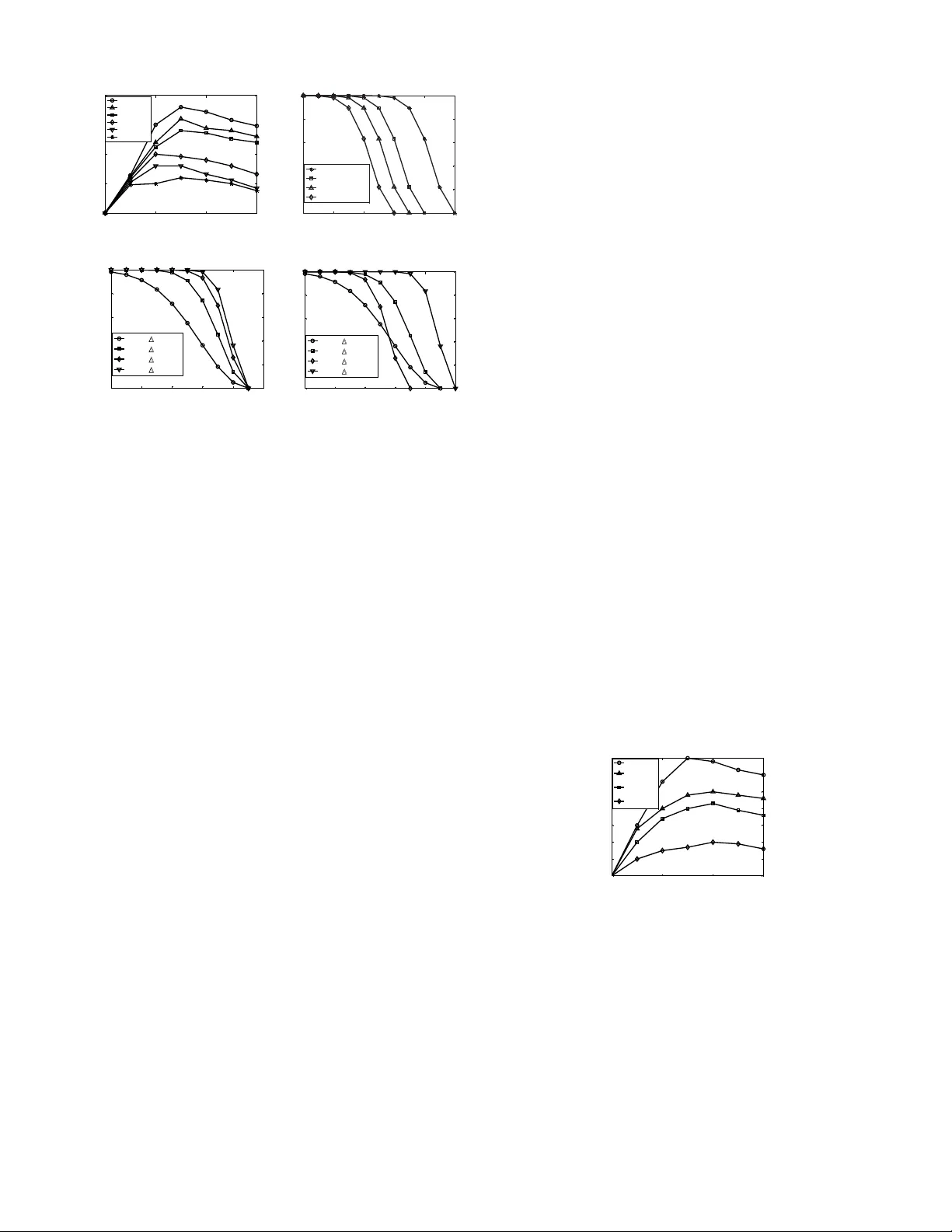
Approximation Algorithms for Link Scheduling with Physical Interfe rence Model in W ireless Multi-hop Netw orks Shuai Fan Departmen t of E lectronic En gineerin g Tsinghua U niv ersity Beijing, P .R . China fans05@mails.tsinghua .edu.cn Lin Zhang Departmen t of Electronic E ngineer ing Tsinghua U niv ersity Beijing, P .R . China Email: linz hang@tsingh ua.edu. cn Y ong Ren Departmen t of E lectronic Engineer ing Tsinghua U niv ersity Beijing, P .R. Chin a Email: re ny@tsinghua.edu .cn Abstract —The link scheduli ng in wireless m ulti-hop networks is addressed. Different from most of work that adopt the protocol interference model which merely take consideration of packet collisions, our pro posed algorithms use the physical interference model to reflect the aggr egated signal to interference and noise ratio (SINR), whi ch is a mo re accurate abstraction of the real scenario. W e first propose a cen tralized scheduling method b ased on the Integer Linear Programm ing (ILP ) and resolve it by an approximate solution based on the randomized rounding method. The probability bound of gettin g a gu aranteed app roximate factor is giv en. W e then extend the centralized algorithm to a distributed solution, which i s fav orable in wireless networks. It is prov en that with the d istributed schedul ing method, all li nks can transmit without interference, and th e approximate ratio of the algorithm is also given. I . I N T RO D U C T I O N In wi reless multi-hop networks, concur rent transm issions that share a comm on channel may cau se interferen ce, and if too many devices transmit simultaneo usly , the interf erence will prev ent an intended recei ver from recei ving the signal, and causes message loss. On the other hand, if too fe w nodes trans- mit at the same tim e, v aluable bandwid th is wasted and the overall throug hput may degenerate. Hence, the classic problem faced by the MA C lay er sch eduling pr otocols is to select an approp riate set o f d evices for concur rent transmissions, so that the interferen ce d oes no t cause message loss. In slotted wireless mu lti-hop networks, a natu ral and imp ortant goal of scheduling algorith ms is to maximize the total throug hput with the interferen ce re striction. Hence, an accurate mo del of interf erence is fund amental in order to deri ve theoretica l or sim ulation-b ased results. There are two main interferen ce mo dels u sed, namely the p rotoco l interferen ce model and the phy sical interference models [1]. In the pro tocol model, a co mmunicatio n from node u to nod e v is successful if n o other n ode within a cer tain interf erence range from v is simu ltaneously transmittin g. Due to its simplicity and to the fact th at it c an be used to m imic the b ehavior o f CSMA/CA ne tworks such as IEEE 802 .11, this model h as been widely used in the literature. Howev er , it doesn’t reflect the ad vanced physical layer techn ologies that a llow concurrent multiple signal reception . In the phy sical interference mo del, a com municatio n between nodes u and v is successful if the Signal to Inter ference and Noise Ratio (SINR) at receiver v is above a certain threshold. This model is less restrictive than the protoco l inter ference model, and thus higher network c apacity can b e ach iev ed by applying the physical inter ference m odel. Clearly , th e inter ference in the protocol model is a tremen- dous simplificatio n of the phy sical reality faced in the wireless multi-hop networks. Particularly , th e interference c aused by different tran smitters may accu mulate and is n ot binar y , i.e ., does not vanish beyond a ny specific bor der . M oreover , a node m ay su ccessfully recei ve a message e ven when there are oth er co ncurren tly transmitting nod es in its interference range. In [ 2], [3], it is argued that the performan ce of protoco l model based a lgorithms is inferior to tho se with mo re r ealistic and funda mental physical interfer ence model. More recen tly , Moscibrod a et al. [4] show experimentally that the theore tical limits of any protocol, which o beys th e laws of p rotocol inter- ference model, c an be broken by a pr otocol explicitly de fined for the physical inte rference mo del. Howe ver , altho ugh the physical interferenc e m odel enjoy a mu ch better pe rforman ce, the sch eduling problem under this model is notor iously hard to reso lve. In this pap er , we stud y the link sched uling pro blem un der the p hysical inter ference model. First, we formu late the prob - lem as an Integer Lin ear Pro gramm ing (ILP) pro blem, wh ich is similar to th e work in [ 5]. Since it is NP-com plete [6], we get the appro ximate algorithm by u sing the r andom ized round ing method , and the pr obability bo und of getting a guaran teed ap prox imate r atio is given. Unlike the work in [5] , we adjust the results of the ro unding pr ocedur e based o n a ll the co nstraints, and no iteration proced ure is n eeded. Since the centralized algorith m needs the global info rmation of the n etwork to d o th e sche duling, inc luding the lo cation of all nodes, the load of the links to be scheduled in a certain time slot, etc., co llecting the require d information may causes a lot of bandwid th overhead , especia lly when the network scale is large. Moreover , in som e c ases, the inform ation is hard to g et. The difficulties in the im plementatio n of centralized algorithm 2 call for the distributed sche duling scheme that m ay achieve a fraction o f the overall optimal p erform ance. W e then p ropose a distributed appro ach based on ph ysical interfer ence mo del. Each send ing no de implem ents the app roach in three phases at each time slot, and all the constrain ts of the ILP problem in the centralized algor ithm are satisfied. T o analyze the perfor mance of th e algorithm, the appr oximation ratio is gi ven. The rest of the pap er is organize d a s follows. After gi ving an overview o f related work in Section II, the network and interferen ce mo del is de scribed in Section III . In Section IV, sch eduling problem u nder p hysical interf erence mod el is formu lated a nd we present th e cen tralize algorith m to get the approx imate solution. I n sectio n V, a distributed ap proach is propo sed. Section VI presents the simulation results of the propo sed alg orithmss and Sectio n VI I con cludes the pap er . I I . R E L A T E D W O R K The pro blem of sched uling link transmissions in a wir eless network in order to optimize one or more of perf ormance objectives (e.g. through put, delay , fairness or en ergy) under interferen ce constraints has be en a sub ject of m uch interest over th e past decad es. As mentioned in th e previous section, an accurate m odeling of interference is fundamental t o the scheduling problem. Most of the sch eduling mechanism s proposed for wireless mu lti-hop networks use the protoco l interferen ce model, such as [ 7]–[1 1]. These algorithm s usually employ an implicit or explicit color- ing strategy , and simply neglect the ag gregated inter ference of nodes located farther away . Howe ver, the inter ference c aused by a transmitter is n ot binar y , i.e., it d oes not vanish beyond any specific border, and may accumulate a mongst m ultiple concur rent transmissions. Only a f ew latest work have conside red p hysical interfer - ence in the context [12]–[20] , etc. In [12 ], Jain, et al. formulate the pro blem of sched uling under phy sical interference mod el as an LP problem. Un fortun ately , no polyn omial time solution and s imulation-b ased evaluation of s cheduling is given. [ 13] also provides an exponen tial-time LP for mulation. In [14], Brar et al. present a heuristic schedu ling method th at is based on a gr eedy assignment of weig hted links. Althou gh it is based on physical i nterferen ce mo del, the approximation factor of the algorithm is given only wh en nod es are u niform ly distributed. The work of [15] con siders phy sical interf erence in the min imum length sched uling prob lem. It uses a power - based in terferen ce graph mode l, which describes the interfer- ence relation ship of e very tw o links ac cording to the SINR of the rec eiv er . Howe ver, th e mod el fails to consider th e accumulatio n effect o f interfe rence. In [ 16], appr oximation algorithm s for packet s cheduling to minimize end- to-end delay with physical in terferen ce model are pro posed. The works of [17], [18 ] study the p roblem of sched uling edges with SINR constraints to ensur e that some pr operty (e. g., conn ectivity) is satisfied. Similar with the work of [19 ], [20], they take p ower control, scheduling o r ro uting tog ether into accoun t. The work of [5 ] is similar to ou r cen tralized alg orithm discussed in section IV. I t also for mulates th e sched uling problem as ILP , but the ran domized roundin g p rocedu re uses an iter ation me thod wh ich is mor e time-con suming than ours. Because the roundin g pr ocedur e would not stop until a feasible solution is fou nd, it costs a very long time to con verge, and in som e cases, it may not co n verge at all. V ariou s distributed a lgorithms have been proposed for find- ing goo d approx imations o f the schedu ling proble m b ased on the protoco l interferen ce mod el (e.g. [ 21]–[ 23], etc.). Only a few previous work propo se distributed alg orithm based on the p hysical inter ference model. T he work of [24]–[ 26] propo se distributed algorithms based on the physical inter- ference mod el, which is lattice- throug hput-o ptimal. But the approx imation ratio is no t given. Th e work of [ 27] d ev elops a constant-time distributed rand om access algorithm for schedul- ing and gives the p erfor mance bo und of the alg orithm. In [28], a distributed and random ized protocol is prop osed, which uses phy sical carrier sensin g to r educe me ssage overhead. It is similar to o ur approach discu ssed in section V. But the protoco l in [2 8] is sensitive to the scale of th e netw ork an d spends much time to learn this inf ormation . I I I . N E T W O R K A N D I N T E R F E R E N C E M O D E L S W e abstract a wireless multi-hop n etwork as a directed gr aph G ( V , E ) wher e V is a set of vertices d enoting the n odes comprising the network an d E is a set o f directed edges between vertices repr esenting inter-node wireless link s. The Euclidean distance between any two nod es v i , v j ∈ V , is denoted by d ( v i , v j ) . Let e ij ∈ E de notes th e edge between v i and v j . Each node is assumed to be e quipped with a sing le transceiver working in the half-duplex way , and all nodes share a common channel. So a node can not send and recei ve packets simultaneou sly . All antenn as are omnidir ectional. It is a ssumed that the network is using Time D i vision Multiple Access (TDMA) MA C proto col. The time is divided into slots o f fixed leng th, which are gro uped into frames. T o increase capacity , spa tial reuse TDMA (STDMA) [29] can be used, which is an extension of TDMA. The c apacity is increased by spatial reuse of the time slots. W e use the p hysical interference model [1 ] to descr ibe the interferenc es b etween active links. In this mo del, the successful r eception of a tr ansmission dep ends on the rec eiv ed signal stren gth, the interf erence cau sed b y n odes tr ansmitting simultaneou sly , and the amb ient no ise le vel. The received power P r ( s i ) of a sign al transmitted by sen der s i at an intended receiv er r i is P r ( s i ) = P ( s i ) · g ( s i , r i ) , where P ( s i ) is the transmission power of s i and g ( s i , r i ) is the pro pagation attenuation (link g ain) modeled as g ( s i , r i ) = d ( s i , r i ) − α . The path-loss expo nent α is a constan t between 2 an d 6, whose exact value depen ds on external co ndition s of the medium (humid ity , obstacles, etc.), as well as the exact sender-receiv er distance. As common , we a ssume that α > 2 [1]. Gi ven a send er-recei ver pair ( s i , r i ) , we use the notation I r ( s j ) = P r ( s j ) for interfer ence from any oth er sender s j 3 concur rent to s i . The total interferen ce I r at the rec eiv er r i is th e sum of th e inter ference power caused by all no des that transmit simultan eously , except the inten ding send er s i . Mathematically , we have I r := P s j ∈ V \{ s i } I r ( s j ) . Finally , let N denote th e ambien t noise power level. Th en, r i receives transmission successfully f rom s i if and only if S I N R ( r i ) = P r ( s i ) N + P s j ∈ V \{ s i } I r ( s j ) = P ( s i ) · g ( s i , r i ) N + P s j ∈ V \{ s i } P ( s j ) · g ( s j , r i ) = P ( s i ) d ( s i ,r i ) − α N + P s j ∈ V \{ s i } P ( s j ) d ( s j ,r i ) − α ≥ β , where β is the m inimum S I N R threshold req uired f or a successful m essage reception. I V . T H E C E N T R A L I Z E D A P P R OX I M A T I O N A L G O R I T H M In this section, we first fo rmulate th e link scheduling prob - lem u nder the ph ysical interf erence model as a n I nteger Linear Programm ing pro blem, then g iv e a n appr oximate algorithm using randomized ro undin g method, which can be done in polyno mial tim e. A. Pr oblem formulation W e d enote by V T ⊆ V an d V R ⊆ V the set of transmitting and rece i ving nod es respectiv ely . The time is di vided into slo ts of fixed leng th a nd a frame is compo sed of T times slots, the length of which is c onstant. In time slot t ∈ [1 , T ] , there exists at least on e edg e being scheduled to tr ansmit. W e denote b y b ij ( e i,j ∈ E ) the to tal traffic rate thr ough link ( i, j ) an d we use the se to measure throug hput. Th e g oal of the sche duling method is to tran smit all th e edges in a fr ame to g ain the maximum through put. T o form ally formulate the problem, the boolean variables x t ij is d efined as x t ij = 1 if link e ij is scheduled to b e tran smit in slot t 0 other wise Based o n ab ove assumptions, the linear integer pro gram- ming formulation can be written as fo llows, max 1 T T X t =1 X e ij ∈ E b ij x t ij s.t. T X t =1 x t ij ≥ 1 , ∀ e ij ∈ E (1) X v i ∈ V T x t ij ≤ 1 , ∀ v j ∈ V R , ∀ t (2) X v j ∈ V R x t ij ≤ 1 , ∀ v i ∈ V T , ∀ t ( 3) X v j ∈ V T x t ij + X v k ∈ V T x t ki ≤ 1 , ∀ v i ∈ V S ∩ V R , ∀ t (4) P ( v i ) d ( v i ,v j ) − α x t ij + (1 − x t ij )∆ N + P e kj ∈ E \{ e ij } P ( v k ) d ( v k ,v j ) − α x t kj ≥ β , ∀ e ij ∈ E , ∀ t (5) x t ij ∈ { 0 , 1 } , ∀ e ij ∈ E , ∀ t (6) The objective fun ction of the formu lation is to maxim ize the total network through put, which is d efined as the total traffic transmitted per slot. Con straint (1) guar antees that each active edge should be scheduled at least o nce. Con straint (2) and constraint (3) make sur e that each node can only recei ve or send signal fro m or to on e another node. This is because each node h as o nly o ne tr ansceiver . U nder constraint (4), each node can not send and receiv e at the same time because it work in a half-dup lex way . Constraint (5) expresses the req uired SINR threshold that should be satisfied in order to have a successful reception at the receiver . The item (1 − x t ij )∆ ensures that the inequality is also satisfied when link e ij is n ot sched uled in time slot t (i.e. x t ij = 0 ) , fo r a sufficiently large value o f ∆ . B. Appr ox imate algorithm with randomized r oundin g Since I LP problem s are NP-complete, there is no efficient algorithm known for solving them in bou nded time (and there can not e xist any unless P = N P ). The above form ulation does not help us solve the schedulin g p roblem. Howe ver, it does guide u s to a natura l relaxation which he lps to find a good a pprox imate algorithm. 1) R ando mized r ounding pr oc edur e: W e can use r andom- ized ro undin g m ethod to find efficient and near o ptimal solutions [3 0]. In this procedu re, eac h variable x t ij will b e relaxed to be in the ra nge fr om zero to o ne and therefo re conv erted from integer variables to fractio nal o nes, i.e., x t ij ∈ [0 , 1] , f or ∀ e ij ∈ E , ∀ t . The IL P pro blem is then relaxed to be a linea r prog ramming prob lem, which is called LP- relaxation. The optimal solution o f the LP-relaxation can be treated as a probability vector with which we choose to include a link to a spe cific times lot. Denote the o ptimal solutio n a s ˆ x t ij . In that sense, if ˆ x t ij is near one, it is likely tha t this link will be includ ed in the current times lot. If, on th e oth er hand, the optimal solution of the LP-relaxation problem is near zero, it will prob ably not be includ ed in th e cu rrent tim es lot. More specifically , the r ound ing procedur e can be descr ibed as follows, x t ij = 1 , with probability ˆ x t ij 0 , with probability 1 − ˆ x t ij (7) Howe ver, after th e round ing proced ure, all the c onstraints may not be satisfied. For example, we sup pose in con straint (2), for ∀ v j ∈ V R , ∀ t , there are two n odes v 1 , v 2 ∈ V T . If ˆ x t 1 j = 0 . 3 and ˆ x t 2 j = 0 . 7 , con straint (2) is satisfied. But after th e round ing proced ure, x 1 j = 1 with pro bability 0.3, and x 2 j = 1 with p robability 0.7 . So P v i ∈ V T x t ij = 2 with probab ility 0.21. That is with probab ility 0.21, constraint (2) is not satisfied. T o overcom e this p roblem , the work in [5 ] u ses a iteration meth od. T he rou nding pro cedure would n ot sto p u ntil a feasib le solutio n is foun d, which costs a very long tim e to conv erge. Even worse, it may no t find any f easible solution 4 Algorithm 1 Centralized Approxim ate Algorithm 1: Consider all links in E : 2: Relax th e integer linear program ming problem to b e a linear p rogra mming problem (LP-relaxation ); 3: Find the solutions of the relaxed LP { ˆ x t ij : ∀ e ij ∈ E , t ∈ T } ; 4: Do r andom ized ro undin g an d get the rou nding solution { x t ij : ∀ e ij ∈ E , t ∈ T } fr om equ ation (7 ); 5: f or ea ch t ∈ T do 6: Get the set ˆ φ t = { e ij : x t ij = 1 } ; 7: Consider all link s e ij ∈ ˆ φ t in n on-dec reasing order of ˆ x t ij : 8: if constraint 2 or constraint 3 or con straint 4 is not satisfied t hen 9: x t ij = 0 ; 10: Move e ij away from ˆ φ t ; 11: end if 12: Consider all link s e ij ∈ ˆ φ t in n on-dec reasing order of ˆ x t ij : 13: if constraint 5 is not satisfied then 14: x t ij = 0 ; 15: Move e ij away from ˆ φ t ; 16: end if 17: end for 18: Consider all links e ij ∈ E : 19: f or each link e ij ∈ E do 20: if P T t =1 x t ij < 1 then 21: Consider th e biggest elemen t ˆ x t ij for all t ∈ T : 22: ˆ x t ij = 1 ; 23: Execute from line ( 5) to (1 7) 24: end if 25: end for in the end. Unlike the work in [5], we a djust the results of the roundin g pr ocedur e based on a ll the c onstraints, and no iteration pr ocedur e is needed. The detail of o ur p ropo sed algorithm is discussed in the following part. 2) Appr o ximate algorithm: we d enote by ˆ φ t = { e ij : x t ij = 1 } the set of edges that will be tran smitted after the r ound ing proced ure at time slot t . As discussed above, all the constraints of the ILP pro gram may n ot b e satisfied. So the solu tion of the round ing proced ure will be adjusted in algorithm 1 to satisfy all the co nstraints. As th e solution of th e relaxed LP pr oblem { ˆ x t ij : ∀ e ij ∈ E , t ∈ T } is the pr obability f or th e wireless links to tran smit, we reo rder the elements in ˆ φ t accordin g to the probab ilities in the non- decreasing order . Algorithm 1 pro ceeds in two p hases: phase 1 is correspon d- ing to line 1 to 4; while ph ase 2 is correspondin g to th e r est o f the alg orithm. I n p hase 1, the ILP pro blem is relaxed to be a linear p rogra mming pro blem which is solved b y the ran dom- ized round ing proced ure. As mention ed before, there exists a problem that th e round ing solutio n { x t ij : ∀ e ij ∈ E , t ∈ T } may not satisfy all the constraints in the ILP prob lem. It can be resolved in phase 2 . Fr om line 5 to 17, it is checked slot by slot wheth er co nstraints (2) to (5) are satisfied. The solutio n of the relaxed LP { ˆ x t ij : ∀ e ij ∈ E , t ∈ T } can b e viewed as the prob ability of the tran smission o f the links. The links with larger value o f ˆ x t ij have hig her pr iority to transmit. So we check the links in a no n-decr easing ord er of ˆ x t ij . In each slot, if a link doe sn’t satisfy any of the constra ints of (2),(3 ) or (4), it will not transmit in the cu rrent slot. After all lin ks in ˆ φ t are ch ecked, con straint (5) is ch ecked fro m line 12 to 1 6. Because co nstraint (5) is the interference constra int, with which th e transmission o f a link is r elated to all the other tran smitting lin ks, it is ch ecked after constraint (2 ) to (4) bein g checked. Con straint (1) guaran tees th at each active link should be schedu led at least o nce in a frame. Howe ver, after th e pr ocedur e o f randomiz ed r ound ing and the check of constraint (2) to (4), x t ij of a lin k e ij may be ro unded to 0 , or adjusted from 1 to 0, leading that c onstraint (1) is n ot satisfied. From line 18 to 2 5, co nstraint (1) is ch eck. For a link e ij that doesn’t satisfy co nstraint (1), find the time slot t in which it h as the largest pro bability to tra nsmit (line 21). Th en let e ij has pr obability 1 to tran smit, which guarantees th at e ij is scheduled o nce. Con straint (1 ) is the n satisfied. 3) P erformance an alysis: In this pa rt, th e per forman ce of algorithm ? ? is an alyzed, inclu ding the com plexity an d the approx imation r atio. It ca n be seen th at algorith m 1 can finish in polyn omial time, and the proba bility lower bo und of being a (1 − θ ) -ap proxim ation algo rithm ( ∀ 0 < θ < 1 ) is calculated. The complexity of phase 1 depends on the algorithm solving the LP-relaxed pro blem. Let it be denoted by O ( P ) . Since it is a linear prog ramming prob lem, it runs in polyn omial time. Thus P is polyn omial. Let N be th e total n umber of the links in E . It can be easily seen that th e complexity f rom line 5 t o 17 in algorithm 1 is O ( N T ) , becau se th ere are two loops there. Similarly , the complexity f rom line 18 to 25 is O ( N 2 T ) . T hus the co mplexity of the wh ole algo rithm is O ( max ( P, N 2 T )) , which is poly nomial. The approx imate ratio of alg orithm ?? can be got from the following theorem : Theor em 1 (Appr oximate ratio of the centralized a lgorithm): For ∀ 0 < θ < 1 and − θ < ∆ A/ ˆ A < 1 − θ , the prob ability of algorithm ?? being (1 − θ ) -app roximate to the o ptimization is lower bound ed by 1 − e − ( θ + ∆ A ˆ A ) 2 ˆ A 2 , where ˆ A is thr ough put calculated by the LP-relaxatio n, ∆ A is the variation of the throug hput in ph ase 2. Pr oof: In p hase 1, let A r and and ˆ A be total throu ghpu t calculated by the r andom ized ro undin g in phase 1 and LP- relaxation r espectively , i.e. A r and = 1 T P T t =1 P e ij ∈ E b ij x t ij , and ˆ A = 1 T P T t =1 P e ij ∈ E b ij ˆ x t ij . Fro m equatio n (7) , we can get E ( x t ij ) = ˆ x t ij . Thus, E ( A r and ) = E ( 1 T T X t =1 X e ij ∈ E b ij x t ij ) = 1 T T X t =1 X e ij ∈ E E ( b ij x t ij ) 5 = ˆ A (8) According to equ ation (8 ) and Cherno ff Boun d [30 ], we can get the fo llowing b ound , P r ( A r and ≥ (1 − δ ) ˆ A ) = 1 − P r ( A r and < (1 − δ ) ˆ A ) ≥ 1 − e − δ 2 ˆ A 2 , 0 < δ < 1 (9) Let A be the final solutio n of algorithm ?? and A Opt be th e optimal solution of the ILP problem. Obviou sly , A ≤ A Opt ≤ ˆ A (10) In ph ase 2, the r andomiz ed ro undin g solu tion is checked whether it satisfies a ll the co nstraints in th e ILP pro blem, and some ad justments are m ade, leadin g th at the th rough put changes. Su ppose the through put cha nges b y ∆ A af ter ph ase 2, an d it follows th at A = A r and + ∆ A (11) Substituting eq uation (1 1) into (9 ), we can derive P r ( A ≥ (1 − δ + ∆ A ˆ A ) ˆ A ) ≥ 1 − e − δ 2 ˆ A 2 , 0 < δ < 1 (1 2) In p hase 2, the worst c ase is that all links are adju sted not to transmit, leading the throu ghput A = 0 , i.e. A r and + ∆ A = 0 ; while the b est case is that after the ad justment, the solu tion approa ches to the optimal, leading A = A r and + ∆ A ≤ ˆ A . Thus w e can get the variation range of ∆ A as follows, − A r and ≤ ∆ A ≤ ˆ A − A r and (13) Let θ = δ − ∆ A ˆ A . Since 0 < δ < 1 , it can be der i ved that − θ < ∆ A/ ˆ A < 1 − θ . E quation (12) can b e written as follows, P r ( A ≥ (1 − θ ) ˆ A ) ≥ 1 − e − ( θ + ∆ A ˆ A ) 2 ˆ A 2 , (14) where − 1 + A rand ˆ A ≤ θ ≤ 1 + A rand ˆ A (from equation (13)), and − θ < ∆ A/ ˆ A < 1 − θ . Because (0 , 1) ⊂ [ − 1 + A rand ˆ A , 1 + A rand ˆ A ] , accord ing to equation (10)(14 ), we can get P r ( A ≥ (1 − θ ) A Opt ) ≥ P r ( A ≥ (1 − θ ) ˆ A ) ≥ 1 − e − ( θ + ∆ A ˆ A ) 2 ˆ A 2 (15) where θ ∈ (0 , 1) , and − θ < ∆ A/ ˆ A < 1 − θ . V . T H E D I S T R I B U T E D A L G O R I T H M The approxim ate algorith m d iscussed in sectio n IV uses th e physical inter ference model to repr esent the inter ference and has a good perform ance. Howev er , as mentioned in section I, th e centralized algo rithm re quires the glob al infor mation of the network to do th e sched uling. Collec ting the require d informa tion may causes a lot of ban dwidth overhead, espe- cially wh en th e n etwork scale is large. Moreover , in som e cases, th e inform ation is ha rd to g et. Th e difficulties in the implementatio n of centralized algorithm call for the distrib u ted scheduling scheme that may ac hieve a f raction of the overall optimal perform ance. In th is part, we extend the centralized algor ithm ?? to a d istributed solu tion, wh ich takes the p hysical in terferenc e model into accou nt and im plements in thr ee phases. It is assumed that n odes in the network can perform physical carrier sensing, and they can set th e carrier sensin g rang e to different values. As we show in the f ollowing part, by prop erly tuning the carrier sensing range, all t he constraints of the ILP problem in sectio n IV can be satisfied. Th e appr oximation ratio is also proved. A. Carrier sen sing range calcu lation Let d max and d min be the maximu m and minim um link length in the network respectively . The leng th diversity k is defined as k = ⌊ log ( d max /d min ) ⌋ ( 16) Suppose each node transm its at the same power P . As the ambient noise power is much less tha n the interference p ower , it is o mitted here. The following theo rem describes how to tune the car rier sen sing r ange for each nod e. R C R C R C ring 0 ring 1 ring 2 Vi Vj Fig. 1. The E uclide an plane is divide d into a series of rings Theor em 2 (Carrier sensing range): If the carrier sensing range is set to be R C = ρ 2 k , the transmitting links in the network will not b e inte rfered b y all the other links, wher e ρ is d efined as ρ = 4(2 π β α − 1 α − 2 ) 1 α , (17) α is the path- loss expo nent and β is the minim um S I N R threshold) . Pr oof: W ithout loss of gen erality , suppose link e ij ∈ E is transmitting data fr om node v i to v j . we normalize th e minimum link length d min to b e 1. From the definition o f the length diversity , we can get 2 k ≤ d max ≤ 2 k +1 . The length of link e ij satisfies d ij ≤ d max ≤ 2 k +1 , thus the p erceived power a t v j from v i is at least P ij ≥ P 2 ( k +1) α (18) The plane can be divided into a series o f rings with the center located at send ing nod e v i , which can be seen in figur e 1. They are denoted as ring 0 , 1 , · · · , respectively . Since the 6 region of ring 0 is in the carrier sensing rang e of the sendin g node v i , ther e are no other sending nod es locating in ring 0 . For a sending nodes v m located in ring 1 , it must be at least d mj ≥ R C − 2 k +1 away from v j . Since each send ing node must b e outside the carrier sensing ran ge of o ther send ing nodes, there ar e at most π / a r csin( 1 2 ) = 6 sending nodes can transmit co ncurr ently in ring 1. Consequ ently , the aggregated interferen ce at v j is 6 X l =1 P lj = 6 X l =1 P d α lj ≤ 6 P ( R C − 2 k +1 ) α In ring 2 , the sending nodes are at least 2 R C − 2 k +1 away from v j . there ar e at m ost π / arcsin( 1 4 ) ≤ π 1 / 4 = 4 π sen ding nod es can transmit con curren tly . So the aggregated inter ference a t v j is 4 π X l =1 P lj ≤ 4 π P (2 R C − 2 k +1 ) α Similarly , in rin g m , th e sending nodes are at least m R C − 2 k +1 away f rom v j . th ere are at mo st π / arcsin( 1 2 m ) ≤ π 1 / 2 m = 2 mπ sending nodes can tran smit concu rrently . So the aggregated in terferen ce at v j is 2 mπ X l =1 P lj ≤ 2 mπ P ( mR C − 2 k +1 ) α Consequently , th e accumu lated interfer ence at the rec eiving node v j is u pper b ounded b y I v j ≤ ∞ X m =1 2 mπ P ( mR C − 2 k +1 ) α = ∞ X m =1 2 mπ P ( mρ 2 k − 2 k +1 ) α = 2 π P 2 kα ∞ X m =1 m ( mρ − 2) α (19) ≤ 2 π P 2 kα ∞ X m =1 m ( mρ/ 2) α = 2 π P 2 kα ( ρ/ 2) α ∞ X m =1 1 m α − 1 ≤ 2 π P 2 ( k − 1) α ρ α α − 1 α − 2 (20) where (19) follows b ecause x − 2 > x/ 2 , ∀ x > 4 and ρ > 4 , giv en that β ≥ 1 and α ≥ 2 ; and ( 20) f ollows from a b ound on Riemann’ s zeta func tion [6] . From equ ation (1 7), ( 18) an d (20), we can get the S I N R at the recei v ing n ode v j as follows: S I N R v j = P ij I v j ≥ P 2 ( k +1) α 2 π P 2 ( k − 1) α ρ α α − 1 α − 2 = β B. Algorithm d escription The frame structu re is shown in Figur e 2. A f rame is composed of fixed length time slots. A time slot is divided into 3 phases, namely , car rier sen sing phase, R TS-CTS phase and data-ack pha se. Our distributed schedulin g approac h allows each node to implemen t it in each o f the th ree phases. Next, we will present the details of the approach an d sho w that a fter the three ph ases, a ll the constraints in the ILP p roblem are satisfied. Ă Ă Fig. 2. Frame structure in distr ibut ed approach 1) Ca rrier sensing pha se: Th e purpose of this phase is to guaran tee that ther e are n o other n odes sen ding data in the carrier sensing range of a transmitting n ode. Each n ode in the network sets its carr ier sensin g range to be R C , which is calculated in th eorem 2. So accordin g to theorem 2, th e no de will transmit its data with out any interferenc e. Constraint (5) in the ILP is satisfied. Consider a transmission slot starts at time t. The car rier sensing ph ase begins at the beginnin g of each time slot. I t lasts for a period o f t c . Each no de that wants to tr ansmitting d ata random ly selects a time t s and sends a SENSING signal, which lasts fo r a period of τ ( t ≤ t s ≤ t + t c − τ ). The purpose of the SENSING signal is to let each node sense whether th ere are other transmitting node s in its c arrier sensin g range. If a node do no t sense any signal befor e sending the SENSI NG signal, it will occupy this time slot, and en ter pha se 2; othe rwise, the node r andom ly selects anoth er time slot an d waits to tran smit again. So the nodes loca ted in each other’ s c arrier sensing range will transmit in different slots, and no inter ference will occur . For each node, the pur pose of rando mly s electing a time to send SENSING sign al is to p revent that all no des send the SENSING signal concu rrently , a nd they all will sense nothing. If a link is scheduled , the sendin g nod e will n ot sen d the SENSING signal again until it can sense n othing, i.e., all the sending n odes th at ha ve been scheduled a t least once will wait for the nodes that haven’t been scheduled to transmit. This rule guaran tees that all the links are scheduled at least onc e in a frame. So con straint (1) is satisfied. 2) R TS-CTS phase: In this p hase, the send ing nod e first sends R TS sign al to the co rrespon ding receiving node. If the receiving node r eceiv es R TS, it will respon d CTS signal to the sending no de. If the sendin g node receives CTS signal, it will 7 enter ph ase 3. Oth erwise, it will ran domly select anothe r time slot to tra nsmit. This phase gu arantees that constraint (2) in th e ILP is satisfied, i.e., a node can not receiv e data from m ore than one no des simultaneo usly . A n example can be seen in figu re 3. Node A and B ar e b oth tran smitting to nod e C. Sin ce n ode B is o utside th e carr ier sensing range of n ode A, A a nd B can tra nsmit simultan eously in pha se 1 without inte rference . Because C can not rec eiv e data from m ore than one node simultaneou sly (constrain t 2) , the data f rom A or B will not be rec eiv ed. Thro ugh the R T S-CTS pro cedure, A or B will transmit in an other slot, and constrain t (2) is satisfied. R C A C B Fig. 3. An example in phase 2 3) Data-ack phase: In this phase, the sendin g nod e sends data t o the receiving nod e, an d waits for the ack s ignal from th e receiving no de. I f the re ceiving nod e rec eiv es d ata correctly , it sends back ack signal to co nfirm the correct r eception. If the sending nod e do esn’t r eceive the ack sign al, it will transmit the data ag ain in the next slot. Because of the d istribution feature of o ur appro ach, a n ode can decide no t to sen d d ata to mor e th an one receiving node s simultaneou sly . So co nstraint (3) is satisfied. Usually , the carrier sensing rang e is larger than the transmission range. Thus, when a node is tran smitting, no other nodes will transmit to it. I n ad dition, b ecause of the h alf duplex ch aracter o f wireless nod es, a no de will no t send d ata to other s wh en it is receiving data. So co nstraint (4) is satisfied. In phase 1, constraint ( 1) and ( 5) are satisfied. Constraint (2 ) is satisfied in phase 2. So all th e constrain ts ar e satisfied in our distributed approa ch, which can be viewed as a distributed solution o f the IL P . Next, we will a nalyze the appro ximation ratio o f the distributed appr oach. C. P erformance analysis The app roximatio n ratio of th e distributed app roach can be described in the following theore m: Theor em 3 (App r oximatio n ratio of the d istrib uted appr oa ch): The ap proxim ation ratio of the distributed appro ach is at most d α max ( ρ + 2) α /β , i.e., the distributed appro ach is an O ( d α max ) ap prox imate algor ithm ( ρ , α a nd β are th e same as defined in theorem 2, and d max is th e norm alized maximum link len gth). Pr oof: It c an b e seen that each sending node in the network can be located in a certain circle with radiu s being the car rier sensing range R C . W itho ut lo ss o f gener ality , we consider a cir cular area Φ v i with a send ing node v i located in the cen ter . Node v i is send ing data to v j . Assume an optima l algorithm OPT can schedule at most q links in T OP T = 1 slot whose sending node is located in Φ v i . Accord ing to th eorem 2, to schedu ling these q link s, ou r pr oposed appr oach needs T ≤ q time slots. So th e approxim ation ra tio is T T OP T ≤ q Next, we will calcu late the maximum value of q . The best case is that ther e are no nod e sending da ta outside Φ v i , and all the link s in Φ v i can transmit successfully . For node v j , the perceived SINR le vel is S I N R ( v j ) = P /d α ij P q k =1 P /d α kj ≤ P q P / ( ρ 2 k + 2 k +1 ) α (21) = S I N R M AX ( v j ) where (2 1) follows be cause d ij ≥ 1 and d kj ≤ 2 k +1 . According to S I N R M AX ( v j ) ≤ β , we can get q ≤ 2 kα ( ρ + 2) α /β ≤ d α max ( ρ + 2) α /β (22) = O ( d α max ) where (22) follows fro m th e defin ition of diversity ( 16). From th eorem 3 we can see tha t th e p erform ance of the distributed algo rithm is closely related to the lin k le ngth div ersity . The appro ach perfor ms well w hen th e diversity is small. It can be seen distinctly fr om simulation (section VI). V I . S I M U L AT I O N S In this section , we present the simulatio n results that verify the pe rforman ce o f ou r pr oposed app roximate algor ithms in this paper . A. Simulation scen ario W e cr eate a scenar io where wireless nodes are unifor mly distributed in a 100 × 100 squ are. I n the simulation, we normalize th e transmission range of a no de to be R T = 1 , and the in terferen ce r ange to b e R I = 2 . 5 . For simp licity , all nodes are supp osed to transmit at the same power level. W e also assume N = − 90 dB m , β = 10 dB , an d α = 4 , whic h are similar with [ 2] and [24]. Let th e frame len gth be T = 100 . The whole sim ulation ru ns 100 time s. In ea ch simu lation, n commun ication p airs are ran domly selected . Sup pose each of the selected links ha s the same traffic ra te which is norm alized to be 1. 8 0 20 40 60 0 5 10 15 20 Number of communication pairs n Normalized throughput OPT Bound OPT APP PCG PG PM (a) 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 Approximation ratio (1- ) Probability bound n=50, /A=0 n=50, /A=-0.2 n=50, /A=-0.3 n=50, /A=-0.4 (b) 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 Approximation ratio (1- T ) Probability bound n=10, ' /A=-0.1 n=30, ' /A=-0.1 n=60, ' /A=-0.1 n=90, ' /A=-0.1 (c) 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 Approximation ratio (1- T ) Probability bound n=10, ' /A=-0.1 n=30, ' /A=-0.1 n=60, ' /A=-0.3 n=90, ' /A=0 (d) Fig. 4. The performance of the centraliz ed algorithm B. Centralized algorithm W e first compare the thro ughp ut perfo rmance between o ur propo sed alg orithm an d several o ther centr alized algor ithms. The algo rithm in [10] is based on protoco l in terferenc e m odel and a po lynomia l-time coloring algorith m is used. T o express conv eniently , we call it Algo rithm Protocol Mode l ( PM). In [14], the algorithm is b ased on p hysical in terferenc e mod el, which is the same as ours. I t is a heuristic schedulin g method that is b ased o n a g reedy assignmen t of weighte d links. W e call it A lgorithm Physical Gre edy (PG). The a uthors in [ 15] construct the conflict grap h u sing the physical interferen ce model, wh ich do es not consider the accumulation effect either . It is called Algorithm Phy sical Conflict Graph (PCG). The throug hput co mparison of the several a lgorithms is shown in Fig.4(a). The notatio n OPT Bound here stands for the optimal solution of the LP-relaxation . The n otation OPT is the op timal solution o f IL P , wh ich is got by trav ersal search ing. Algorith m APP im plies our ap prox imate a lgorithm. It can be seen that our pro posed APP alg orithm is well approx imate to the optima l solution of ILP , which is a little lower th an the upp er bound . It also outper forms the protoc ol interferen ce model based alg orithm (PM algorithm ) and other physical interference mo del b ased heuristic algorithms (PG and PCG alg orithms). It per forms ever b etter when m ore nodes begin to tran smit. The P M algorithm performs the worst, because it uses the protocol interfer ence model, wh ich is less precise than th e physical interf erence model. When m ore and more nod es begin to transmit, th e throu ghpu t dro ps for all th e algorithm s. This is be cause w hen interferen ce is m ore sev ere, more transmissions b egin to conflict with each other . Then we ev aluate the influence of the parameter ∆ A/ ˆ A (defined in theorem 1) to the ( 1 − θ )- approx imate lower bou nd. Here we d enote ∆ A/ ˆ A by ∆ A/ A in the legen ds of Fig . 4. It can be seen from Fig. 4(b) th at the lower bou nd decreases while ∆ A/ ˆ A d ecreases, which is fro m the fact th at mo re adjustments are made in the ph ase 2 of the alg orithm 1 . In our simulatio n, ∆ A/ ˆ A is rarely smaller than -0.3, im plying that the approx imation ratio is larger th an 0.5 with prob ability larger than 0.7, and the appr oximation ratio larger than 0 .4 with pr obability la rger than 0.9. When m ore links begin to transmit, more ad justments are made in algorithm 1, i.e., ∆ A decrease. The influence of the network scale n to th e perform ance ca n be seen in Fig.4(c) and 4(d). W e can get the f ollowing conclusions when n increases: 1) If ∆ A/ ˆ A d oesn’t dec rease, the prob ability lower bo und increases. In Fig .4(c), ∆ A/ ˆ A is fixed to be 0 .1. The proba bility lower boun d increases wh ile more lin ks begins to transmit. If ∆ A/ ˆ A increases, the proba bility lower bou nd also inc reases (see plot ( n = 6 0 , ∆ A/ A = − 0 . 8 )and ( n = 90 , ∆ A/ A = 0 ) in Fig.4 (c)). 2) If ∆ A/ ˆ A decrease, th e prob ability lo wer bou nd dereases. It can be seen in Fig.4(c)). C. Distrib ute d algorithm In this simu lation, n odes are not uniform ly distributed, which is different from the scen ario in the centralize d algo- rithm. W e selec t the tran smission pairs pro perly to contr ol the link len gth di versity k . In Fig . 5, the throu ghput of th e centr alized algor ithm and distributed approa ch are co mpared . It c an b e seen that th e distributed algorithm approa ches th e cen tralized algo rithm well when k = 0 . The thro ughpu t of k = 0 and that of k = 1 are very close to each other ; while it decreases sha rply whe n k = 2 . It is becau se the app roximatio n r atio is O (2 kα ) , which is exponen tial to k . Howe ver, in real scenario k is not very large, typically k ≤ 2 . The d istributed alg orithm pro posed in the paper is pr eferred to be implem ented in the scenario that the link le ngth di versity is small. Th e ideal scen ario is th at th e nodes are located unifo rmly . 0 20 40 60 0 2 4 6 8 10 12 14 Number of conmmunication pairs n Normalized throughput Centralized Distributed , k=0 Distributed , k=1 Distributed , k=2 Fig. 5. The performance of distrib uted algorithm V I I . C O N C L U S I O N In th is pap er we study the link sch eduling p roblem with the physical interfere nce mod el, which is more accurate than the protocol interference model but notorio usly har d to handle with. The sched uling pro blem is f ormulated to be a I LP problem , and we p ropo se o ur centralized algo rithm based on rando mized roun ding. W e analyze the perfo rmance of the algorith m and giv e th e proba bility b ound of ge tting the guaran teed ap proxim ation ratio. As a distributed solution of 9 the ILP problem, we also prop ose a distributed app roach, which uses physical carrier sensing and implement in pha ses. The appro ximation ratio is also gi ven, which is associated with the link len gth diversity . A C K N O W L E D G M E N T This re search is supported in part by the National Science Foundation of Chin a (Gr ant No .606 72107 , 6067 2142 an d 60772 053) , the Hi-tech Research an d Development Pro gram of China (Gr ant No.2006 AA10Z2 61, 2006AA1 0A301, and 2007AA10 0408) , the China 973 Pr oject ( Grant No.200 7CB30710 0 / 2007CB30 7105) and the China Postdoctoral Scien ce Found ation grants 20080 43040 0. R E F E R E N C E S [1] P . Gupta and P . K um ar , “The capacity of wireless networks, ” Information Theory , IEEE T ransact ions on , vol. 46, no. 2, pp. 388–404, 2000. [2] A. Behza d and I. Rubin, “On the performance of graph-based scheduling algorit hms for packet radio network s, ” in Global T elecommuni cation s Confer ence, 2003. GLOBECOM’03. IEE E , vol. 6, 2003. [3] J. Gr ¨ onkvist and A. Hansson, “Compari son between graph-ba sed and interfe rence-b ased STDMA scheduli ng, ” in MOBIHOC 2001 . Pr oceed - ings of the 2nd ACM internati onal symposium on Mobile ad hoc networki ng & computin g . A CM Ne w Y ork, NY , USA, 2001, pp. 255– 258. [4] T . Moscibroda, R. W attenhofer , and Y . W eber , “Protocol Design Beyond Graph-Base d Models, ” in A CM HotNets , 2006. [5] V . Friderikos, K. Papadaki, D. Wi sely , and H. Aghvami, “Non- indepen dent randomized roundi ng for li nk sched uling in wireless mesh netw orks, ” in 2006 IEEE 64th V ehicular T echnol ogy Confer ence, 2006. VTC-2006 F all , 2006, pp. 1–5. [6] O. Gousse vskaia, Y . Oswal d, and R. W attenhofer , “Complexi ty in geometri c SINR, ” in MOBIHOC 2007. P r oceed ings of the 8th ACM internat ional symposium on Mobile ad hoc networking and computing . A CM New Y ork, NY , USA, 2007 , pp. 100–109. [7] B. Hajek and G. Sasaki, “Link scheduling in polynomial time, ” Informa- tion Theory , IEEE T ransacti ons on , vol . 34, no. 5, pp. 910–917, 1988. [8] V . Kumar , M. Marathe, S. Parthasar athy , and A. Sriniv asan, “End-to-end pack et-sche duling in wireless ad-hoc networks, ” in Proce edings of the fiftee nth annual ACM -SIAM symposium on Discr ete algorith ms . Society for Industrial and Applied Mathematic s Philade lphia, P A, USA, 2004, pp. 1021–1030. [9] T . Moscibrod a and R. W attenhofe r , “Coloring unstructured radio net- works, ” in Proce edings of the seventee nth annual ACM symposium on P aralle lism in algorithms and arc hitect ur es . A CM New Y ork, NY , USA, 2005, pp. 39–48. [10] S. Ramanathan and E. Lloyd, “Scheduling algorithms for m ultihop radio netw orks, ” IEEE/ACM T ransact ions on Networking (TON) , vol. 1, no. 2, pp. 166–177, 1993. [11] G. Sharma, R. Mazumdar , and N. Shroff, “On the comple xity of scheduli ng in wireless network s, ” in MOBICOM 2006. Pr oceedings of the 12th annual international confer ence on Mobile computi ng and networki ng . A CM New Y ork, NY , USA, 2006, pp. 227–2 38. [12] K. Jain, J. Padhye, V . Padmanabhan, and L. Qiu, “Impact of Interfer - ence on Multi -Hop W ireless Netw ork Performance, ” W irele ss Networks , vol. 11, no. 4, pp. 471–487, 2005. [13] J. Gronkvist and J. Di Y uan, “Throughput of optimal spatial reuse TDMA for wireless ad-hoc network s, ” in V ehicul ar T echnol ogy Con- fer ence, 2004. VTC 2004-Spring. 2004 IEEE 59th , vol. 4, 2004. [14] G. Brar , D. Blo ugh, and P . Santi, “Computationa lly ef ficient scheduling with the physical interfere nce model for throughput improv ement in wireless mesh netw orks, ” in MOBICOM 2006. Pr oceedings of the 12th annual internat ional confere nce on Mobile computing and networki ng . A CM New Y ork, NY , USA, 2006 , pp. 2–13. [15] A. Behzad and I. Rubin, “Optimum Integrat ed Link Scheduling and Po wer Control for Multihop Wir eless Netw orks, ” IEEE TRANSACTION S ON VE HICULAR TE CHNOLOGY , vol. 56, no. 1, p. 194, 2007. [16] D. Chafekar , V . Kumar , M. Marathe, S. Parthasar athy , and A. Sriniv asan, “Cross-laye r latenc y minimizati on in wireless networks with SINR con- straints, ” in MOBIHOC 2007. Proce edings of the 8th ACM international symposium on Mobile ad hoc networkin g and computing . A CM Ne w Y ork, NY , USA, 2007, pp. 110–119. [17] T . Moscibroda and R. W attenhofer , “The complex ity of connecti vity in wireless networks, ” in INFOCOM 2006. 25th IEEE International Confer ence on Computer Communicatio ns. P r oceedings , 2006, pp. 1– 13. [18] T . Moscibroda, R. W attenhofer , and A. Zollinger , “T opology control meets SINR: the scheduling comple xity of arbitra ry topologi es, ” in MOBIHOC 2006. Pr oceed ings of the 7th ACM international symposium on Mobile ad hoc networki ng and computing . A CM New Y ork, NY , USA, 2006, pp. 310–321. [19] D. Chafekar , V . Kumar , M. Marathe, S. Parthasar athy , and A. Sriniv asan, “Approximat ion algorithms for computing capaci ty of wireless networks with SINR constraints, ” in IEEE INFOCOM 2008. The 27th Confer ence on Comput er Communicat ions , 2008, pp. 1166–1174. [20] T . Moscibroda, Y . Oswald, and R. W attenh ofer , “How Optimal are W irele ss Scheduling Protocols?” in IEEE INFOCOM 2007. 26th IEEE Internati onal Confer ence on Computer Communicat ions , 2007, pp. 1433–1441. [21] P . Chaporkar , K. Kar, and S. Sarkar , “Throughput guarant ees through maximal scheduling in wireless netw orks, ” in 43rd Annual Allerton Conf . on Communi cation s, Contr ol, and Computing . Cit eseer , 2005. [22] X. Lin and N. Shroff, “The impact of imperfect schedul ing on cross- layer rate control in wirele ss networks, ” in Pr oceedings IEE E INFO- COM 2005. 24th Annual Joint Confer ence of the IEEE Computer and Communicat ions Societi es , vol. 3, 2005. [23] E. Modi ano, D. Shah, and G. Z ussman, “Ma ximizin g throughput in wire- less networks via gossiping, ” in Pr oceedings of the joint internationa l confer ence on Measur ement and modeling of computer systems . A CM Ne w Y ork, NY , USA, 2006, pp. 27–38. [24] Y . Y i, G. de V ecian a, and S. Shakkot tai, “On optimal MA C schedul ing with physical interference , ” in IEEE INFOCOM 2007. 26th IEEE Internati onal Confer ence on Computer Communications , 2007, pp. 294– 302. [25] ——, “MAC Scheduling with Low Overheads by Learning Neighbor - hood Conte ntion Patterns, ” Princet on Unive rsity , T ech. Rep., 2007, T ech. Rep. [26] ——, “Learning content ion patterns and adapt ing to load/ topology change s in a mac scheduling algorithm, ” in 2nd IEEE W orkshop on W ire less Mesh Networks, 2006. W iMesh 2006 , 2006, pp. 23–32 . [27] C. Joo and N. Shrof f, “Performance of random access scheduling schemes in multi-hop wireless netw orks, ” in IEEE INFOCOM 2007. 26th IEE E Internation al Confere nce on Computer Communica tions , 2007, pp. 19–27. [28] C. Scheide ler , A. Richa, and P . Santi, “An O (log n) dominating set protocol for wireless ad-hoc networks under the physical interference model, ” in MOBIHOC 2008. Proc eeding s of the 9th A CM internati onal symposium on Mobile ad hoc networkin g and computing . A CM Ne w Y ork, NY , USA, 2008, pp. 91–100. [29] R. Nelson, L. Kleinroc k, I. Cente r , and N. Y orkto wn Heights, “Spatial TDMA: A Collision-Free Multihop Channel Access Protocol, ” Commu- nicati ons, IEE E T ransact ions on [le gacy , pre-1988] , vol. 33, no. 9, pp. 934–944, 1985. [30] P . Ragha v an and C. T om pson, “Randomized rounding: A techni que for prov ably good algorithms and algorith mic proofs, ” Combinatoric a , vol. 7, no. 4, pp. 365–3 74, 1987.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment