BQP and the Polynomial Hierarchy
The relationship between BQP and PH has been an open problem since the earliest days of quantum computing. We present evidence that quantum computers can solve problems outside the entire polynomial hierarchy, by relating this question to topics in c…
Authors: Scott Aaronson
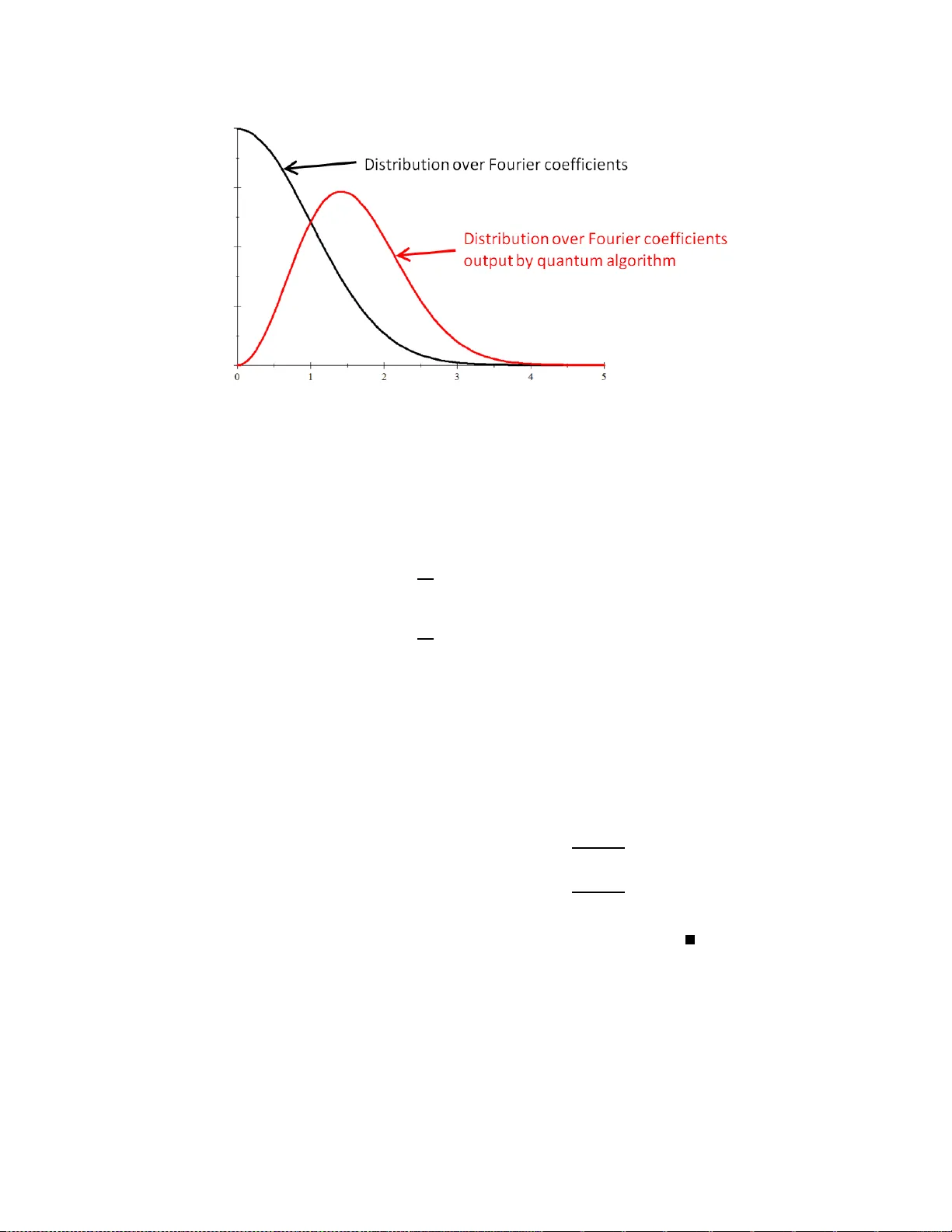
BQP and the P olynomia l Hierarc h y Scott Aaronson ∗ Abstract The relationship b etw een BQP and PH has been an open pr o blem since the earliest days of quantum co mputing. W e pr esent evidence that q uantum computers can solve problems outside the entire po lynomial hierar ch y , b y relating this ques tion to topics in cir cuit complexity , pseudorandomnes s, a nd F ourier a na lysis. First, we show that there exis ts a n oracle relatio n pro blem (i.e., a problem with many v alid outputs) that is solv able in BQP , but not in PH . This also yields a non-orac le rela tion problem that is s olv able in quantum lo garithmic time, but not in AC 0 . Second, we show that a n ora cle de cision pro blem separ ating BQP from PH would follow from the Gener alize d Linial-Nisan Conje ctur e , which we for mulate here a nd which is likely of independent interest. The origina l Linial-Nisa n Conjecture (abo ut pseudora ndomness a gainst constant-depth circ uits) was re c ently prov ed by B rav er man, after b eing op en for tw ent y years. Con ten ts 1 In t ro duction 2 1.1 Motiv ation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 1.2 Our Resu lts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4 1.3 In Defense of Oracles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7 2 Preliminaries 8 2.1 Problems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8 2.2 Complexit y Classes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9 3 Quan tum Algorithms 11 3.1 Quant um Algorithm f or F ourier Fishing . . . . . . . . . . . . . . . . . . . . . . . 11 3.2 Quant um Algorithm f or F ourier Checking . . . . . . . . . . . . . . . . . . . . . . 13 4 The Classical Complexit y of F ourier Fishing 16 4.1 Constan t-Depth Circu it Lo wer Bounds . . . . . . . . . . . . . . . . . . . . . . . . . . 16 4.2 Secretly Biased F ourier Co efficients . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17 4.3 Putting It All T ogether . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20 5 The Classical Complexit y of F ourier Chec king 23 5.1 Almost k -Wise Indep endence . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24 5.2 Oracle S eparation Results . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28 ∗ MIT. Email: aaronson@csail.mit.e du. Supp orted by an NSF CAREER Awa rd, a DARP A YF A grant, MIT CSAIL, and the Keck F ound ation. 1 6 The Generalized Linial-Nisan Conjecture 29 6.1 Lo w-F at P olynomials . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32 7 Discussion 34 8 Op en Problems 36 9 Ac kno wledgmen t s 37 1 In tro duction A central task of qu antum computing theory is to un derstand how BQP —meaning Bounded-Error Quant um Pol ynomial-Time, th e class of all problems feasible for a quan tum compu ter—fits in with classical complexit y classes. In their original 1993 pap er definin g B QP , Bernstein and V azirani [11] sh o wed that BPP ⊆ BQP ⊆ P # P . 1 Informally , this sa ys that quan tum compu ters are at least as fast as classical probab ilistic computers and no more than exp onen tially faster (ind eed, they can b e sim ulated using an oracle for counting). B ernstein and V azirani also ga v e evidence that BPP 6 = BQP , b y exhib iting an oracle p roblem called R ecursive Fourier Sampling th at requires n Ω(log n ) queries on a classical computer bu t only n qu eries on a quantum compu ter. 2 The evidence for the p o wer of qu an tu m computers b ecame dramatically stronger a yea r later, when Shor [33] (b uilding on w ork of Simon [34]) show ed that F actoring and Discrete Logar ithm are in BQP . On the other hand, Bennett et al. [9] ga ve oracle evidence that NP 6⊂ BQP , and while no one r egards su c h eviden ce as decisive , to d a y it seems extremely unlikely that quan tum compu ters can solve NP -complete problems in p olynomial time. A v ast b o dy of researc h, conti n uing to the present , has sought to map out the detailed b oun dary b et ween th ose NP problems that are feasible for quantum compu ters and those that are n ot. Ho wev er, there is a complemen tary question that—despite b eing un iv ers ally r ecognized as one of the “grand c hallenges” of the field—h as had essentia lly zero pr ogress o ver the last sixteen y ears: Is BQP in NP ? Mor e gener al ly, is BQP c ontaine d anywher e in the p olynomial hier ar- chy PH = NP ∪ NP NP ∪ NP NP NP ∪ · · · ? The “default” conjecture is presumab ly B QP 6⊂ PH , since no one kno ws wh at a sim ulation of BQP in PH would lo ok lik e. Before this wo r k, ho wev er, there was no formal evidence for or against that conjecture. Almost all th e problems for wh ic h we h av e quantum algorithms— including F actoring and Discrete Logarithm —are easily seen to b e in NP ∩ coNP . 3 One notable exception is Recur sive F ourier Sampling , the p r oblem that Bernstein and V azirani [11] originally u sed to construct an oracle A relativ e to wh ic h BPP A 6 = BQP A . On e can show, without to o m u c h difficulty , that Recursive Fourier S ampling yiel ds oracles A relativ e to whic h BQP A 6⊂ NP A and ind eed BQP A 6⊂ M A A . Ho wev er, wh ile it is reasonable to conjecture that Recursive Fourier Sampling (as an oracle pr oblem) is n ot in PH , it is op en ev en to sho w that this problem (or any other BQP oracle prob lem) is not in AM ! Recall that AM = NP under 1 The up p er b ound was later impro ved to BQP ⊆ PP by Adleman, DeMarrais, an d Huang [3]. 2 F or more ab out Recursive Fourier Sampling see Aaronson [2]. 3 Here we exclude BQP -complete problems such as approximati ng the Jones p olynomial [5], which, by the very fact of b eing BQP -complete, seem hard to interpret as “evidence” for BQP 6⊂ PH . 2 plausible d erandomization assumptions [26 ]. Thus, until we solv e th e problem of constructing an oracle A su c h that BQP A 6⊂ AM A , w e cannot ev en claim to ha ve oracle evidence (wh ich is itself, of course, a weak form of evidence) that BQP 6⊂ NP . Before going fur ther, we sh ould clarify that there are t w o questions h ere: wh ether BQP ⊆ PH and whether PromiseBQP ⊆ PromisePH . In the unr elativized w orld , it is entirely p ossible that quan tum computers can solv e p romise p roblems outside th e p olynomial hierarc hy , b ut that all languages in BQ P are nev ertheless in PH . Ho wev er, for the sp ecific p u rp ose of constru cting an oracle A suc h that B QP A 6⊂ PH A , th e tw o questions are equiv alen t, b asically b ecause one can alw ays “offload” a p romise in to the constru ction of the oracle A . 4 1.1 Motiv ation There are at least four reasons why the BQP versus PH question is so interesting. A t a basic lev el, it is b oth theoretically and pr actically imp ortan t to und erstand wh at classical r esources are needed to simulate qu an tu m physics. F or example, when a quant um system evo lv es to a giv en state, is there alw ays a short classical pr o of that it do es so? Can one estimate quan tum amplitudes using appro ximate counting (which w ou ld imply B Q P ⊆ BPP NP )? If s omethin g like this w ere tr ue, then w hile the exp onentia l sp eedup of S h or’s f actoring algorithm migh t s tand, quant um computing w ould nev ertheless seem muc h less different fr om classical compu ting than pr eviously though t. Second, if BQP 6⊂ PH , then man y p ossibilities for new quan tum algorithms migh t op en up to us. O n e often hears the complaint that there are to o few quantum algorithms, or that progress on quan tum algorithms h as slo w ed since th e mid-1990s. In our opinion, the real issue here h as nothing to do with quan tum computing, and is simply that th ere are to o few natural NP -inte rmediate problems for whic h there plausib ly c ould b e quantum algorithms! In other words, instead of fo cussing on Graph Isomo rphism and a small num b er of other NP -in termediate problems, it migh t b e fruitful to lo ok for quant um algorithms solving completely different types of problems— problems that are not necessarily ev en in PH . I n this pap er, w e will see a new example of such a quan tum algorithm, wh ich solv es a pr ob lem called F o urier Checking . Third, it is natural to ask whether the P ? = BQP qu estion is related to that other f undamental question of complexit y theory , P ? = NP . More concretely , is it p ossible that qu an tu m computers could provide exp onent ial sp eedups even if P = NP ? If BQP ⊆ PH , then certainly the answer to that question is no (sin ce P = NP = ⇒ P = PH ). Th erefore, if w e w an t evidence that quant um computing could s u rvive a collapse of P and NP , we m ust also seek evidence that BQP 6⊂ PH . F our th , a ma j or c hallenge for quantum compu ting researc h is to get b e tter evidenc e that quantum c omputers c annot solve NP - c omplete pr oblems in p olynomia l time . As an example, could w e sho w that if NP ⊆ BQP , then the p olynomial hierarc hy collapses? A t fi rst glance, this seems like a w ild hop e; certainly w e ha v e no idea at present how to pro v e an ything of the kind. Ho w ever, notice 4 Here is a simple pro of: let Π = (Π YES , Π NO ) b e a promise problem in PromiseBQP A \ PromisePH A , for some oracle A . Then clearly , every PromisePH A mac hine M fa ils to solve Π on infinitely many inp uts x in Π YES ∪ Π NO . This means that we can pro duce an infinite sequence of in p uts x 1 , x 2 , . . . in Π YES ∪ Π NO , whose lengths n 1 , n 2 , . . . are spaced arbitrarily far apart, such that every PromisePH A mac hine M fails to solv e Π on at least one x i . N ow let B b e an oracle that is identical to A , ex cept that for each inp ut length n , it reveals (i) whether n = n i for some i and ( ii) if so, what th e corresp onding x i is. Also, let L b e th e unary language that contains 0 n if and only if (i) n = n i for some i and ( ii) x i ∈ Π YES . Then L is in BQP B but not PH B . 3 that if BQP ⊆ AM , then the desired implication w ould follo w immediately! F or in that case, NP ⊆ B QP = ⇒ coNP ⊆ BQP = ⇒ coNP ⊆ AM = ⇒ PH = Σ P 2 where the last implication wa s sho wn by Boppana, H ˚ astad, and Zac hos [12]. S imilar remarks apply to the questions of whether NP ⊆ BQP wo uld imply PH ⊆ B QP , and whether the folklore result NP BPP ⊆ BPP NP has the qu an tum analogue NP BQP ⊆ BQP NP . In eac h of these cases, we fi nd that understand ing some other issue in quan tum complexit y theory requires first coming to grips with whether BQP is con tained in some lev el of the p olynomial hierarc h y . 1.2 Our R esults This pap er presents the fi rst formal evidence for the p ossibilit y th at BQP 6⊂ PH . P erhaps more imp ortantl y , it p laces th e r elativized BQP v ersu s PH question at the fr on tier of (classical) circuit lo wer b ound s. The heart of the pr oblem, w e will find, is to extend Bra v erman ’s sp ectacular recent pro of [13] of the L inial-Nisan Conjecture, in w ays that w ould reve al a great d eal of information ab out small-depth circuits indep endent of the implications for quantum compu ting. W e hav e tw o main contributions. First, w e ac hiev e an oracle separation b et ween BQP and PH for the case of r elation pr oblems . A relation problem is simply a p r oblem wh ere the desir ed output is an n -bit string (rather than a single b it), and any string from some non emp t y set S is acceptable. Relation problems arise often in th eoretical compu ter science; one well- kno wn example is findin g a Nash equilibrium (shown to b e PP AD -complete by Dask alakis et al. [15]). Within quantum computing, there is considerable p receden t f or studying relation problems as a wa r m up to the harder case of decision problems. F or example, in 2004 Bar-Y ossef, Ja yram, and K er en idis [6] ga ve a relation pr ob lem with qu an tu m on e-wa y comm un ication complexit y O (log n ) and randomized one-w ay communicatio n complexity Ω ( √ n ). It took s everal m ore y ears f or Ga vinsky et al. [20] to ac hiev e the same separation for decision problems, and the pro of wa s m uc h more complicate d. The same phen omenon has arisen m an y times in qu an tu m comm u nication complexit y [17, 18, 19, 21, 22], though to our kno wledge, this is the first time it has arisen in quant um query complexit y . F ormally , our r esult is as f ollo ws: Theorem 1 Ther e exists an or acle A r elative to which FBQP A 6⊂ FBPP PH A , wher e FBQP and FBPP ar e the r elation v ersions of BQP and BPP r esp e ctively. 5 Underlying Th eorem 1 is a new lo wer b ound against AC 0 circuits (constan t-depth circuits com- p osed of AND, OR, an d NOT gates). The close connection b etw een AC 0 and the p olynomial hierarc hy that we exp loit is n ot new. In the early 198 0s, F ur s t-Saxe-Sipser [16] and Y ao [39] no- ticed that, if w e ha v e a PH mac hine M that computes (sa y) the P ar ity of a 2 n -bit oracle string, then b y simply rein terpreting th e existen tial qu an tifiers of M as OR gates and the universal quan- tifiers as AND gates, w e obtain an AC 0 circuit of size 2 poly ( n ) solving the same problem. It follo ws that, if we can p ro v e a 2 ω (p olylog n ) lo wer b ound on the size of A C 0 circuits computing P arity , w e 5 Confusingly , the F stands for “function”; we are simply follow ing the stand ard naming con ven tion for classes of relation problems ( FP , FNP , etc). 4 can construct an oracle A relativ e to whic h ⊕ P A 6⊂ PH A . The idea is the s ame for constructing an A relativ e to w hic h C A 6⊂ PH A , wher e C is an y complexit y class. Indeed, the relation b et w een PH and A C 0 is so direct that w e get the follo wing as a more-or-less immediate coun terpart to Theorem 1: Theorem 2 In the unr elativize d world (with no or acle), ther e exists a r elation pr oblem solvable in quantum lo garithmic time but not i n nonuniform AC 0 . The relation pr ob lem that w e us e to separate B Q P fr om PH , an d BQLOGT IM E from A C 0 , is called F ou rier Fishing . The pr oblem can b e informally stated as follo ws. W e are giv en oracle access to n Bo olean fu nctions f 1 , . . . , f n : { 0 , 1 } n → {− 1 , 1 } , whic h we think of as c h osen uniformly at r andom. The task is to output n strings, z 1 , . . . , z n ∈ { 0 , 1 } n , su c h that the corresp ond ing squared F ourier co efficien ts b f 1 ( z 1 ) 2 , . . . , b f n ( z n ) 2 are “often m u c h larger than a verage .” Notice that if f i is a random Bo olean f u nction, th en eac h of its F ourier coefficients b f i ( z ) follo ws a n or- mal distribu tion—meanin g that with o v erwh elming prob ab ility , a constant f raction of the F ourier co efficien ts will b e a constant factor larger than th e mean. F urthermore, it is s traigh tforward to create a qu an tum algorithm that samples eac h z w ith probabilit y prop ortional to b f i ( z ) 2 , so that larger F ourier co efficients are more likel y to b e s ampled than smaller ones. On the other hand, computing any sp e cific b f i ( z ) is easily seen to b e equiv alen t to su mming 2 n bits. By we ll-kno wn low er b ounds on the size of AC 0 circuits computing the Majority f unction (see H ˚ astad [36] f or example), it follo ws that, for any fixed z , computing b f i ( z ) cannot b e in PH as an oracle problem. Unfortunately , th is do es not directly imply any separation b et w een BQP and PH , s in ce the quant um algorithm do es not compute b f i ( z ) either: it ju st samples a z with probabilit y prop ortional to b f i ( z ) 2 . Ho w eve r, we will sho w that, if there exists a BPP PH mac hine M that eve n appr oximately sim ulates the b eha vior of the quant um algorithm, then one can solv e Majority by m eans of a nondeterministic reduction—whic h us es appro ximate coun ting to estimate Pr [ M outpu ts z ], and adds a constan t n um b er of la yers to the AC 0 circuit. T h e central difficulty is that, if M knew the sp ecific z for whic h we w ere in terested in estimating b f i ( z ), then it could c ho ose adversarially never to outp u t that z . T o solve this, w e w ill sho w that we can “smuggl e” a Majority instance into th e estimation of a r andom F ourier coefficient b f i ( z ), in suc h a w a y that it is inform ation-theoretically imp ossible for M to d etermine which z we care ab out. Our second con trib ution is to define and stud y a new blac k-b o x decision problem, called F o urier Check ing . Informally , in this p roblem we are giv en oracle access to two Bo olean functions f , g : { 0 , 1 } n → {− 1 , 1 } , and are promised that either (i) f and g are b oth u niformly random, or (ii) f is un iformly random, while g is extremely well correlated with f ’s F ourier transform o v er Z n 2 (whic h we call “forr elated”). The problem is to decide wh ether (i) or (ii) is the case. It is n ot hard to show that F ourier Checking is in BQP : basically , on e can prepare a u niform sup erp osition ov er all x ∈ { 0 , 1 } n , then query f , apply a quant um F our ier transform, qu ery g , and c heck whether one has reco vered s omething close to the u niform sup erp osition. On the other hand, b eing forr elated seems like an extremely “global” p rop erty of f and g : one that would not b e apparent f r om querying any small n um b er of f ( x ) and g ( y ) v alues, regardless of the outcomes 5 of those qu eries. And th u s, one migh t conjecture that Fourier Che cking (as an oracle problem) is not in PH . In this pap er, we addu ce str on g evidence for that conjecture. Sp ecifically , w e sho w that for ev ery k ≤ 2 n/ 4 , the forrelated distribution o ver h f , g i pairs is O k 2 / 2 n/ 2 -almost k -wise indep e ndent . By this we mean that, if one h ad 1 / 2 prior probability th at f and g w ere un iformly rand om, an d 1 / 2 prior probability that f and g w ere forrelated, then ev en conditioned on an y k v alues of f and g , the p osterior probabilit y that f and g were forrelated wo uld still b e 1 2 ± O k 2 2 n/ 2 . W e conjecture th at this almost k -wise in dep en dence prop erty is enough, by itself, to imply that an oracle problem is not in PH . W e call this the Gener alize d Li ni al-N isan Conje ctur e . Without the ± O k 2 / 2 n/ 2 error term, our conjecture would b e equiv alen t 6 to a famous con- jecture in circuit complexit y made by Linial an d Nisan [28] in 1990. Their conjecture stated that p olylo garithmic indep endenc e fo ols A C 0 : in other words, eve ry probabilit y distribution o ver N -bit strings that is unif orm on ev er y small sub set of bits, is indistingu ish able from the truly u niform distribution b y AC 0 circuits. When we b egan in v estigating th is topic a y ear ago, ev en the original Linial-Nisan Conjecture w as still op en. Sin ce then, Bra verman [13] (bu ilding on earlier w ork b y Bazzi [7] and Razb oro v [30]) has given a b eautiful p ro of of that conjecture. In other words, to construct an oracle r elativ e to whic h BQP 6⊂ PH , it now s u ffices to generalize Bra v erman’s Theorem from k -wise indep enden t distr ibutions to almost k -wise indep en d en t ones. W e b eliev e that this is b y far the m ost promisin g approac h to the BQ P v ersu s PH p roblem. Alas, generalizing Bra verman’s pro of is muc h harder than one migh t ha ve hop ed. T o pro ve th e original L in ial-Nisan Conjecture, Bra verman sh o wed that eve ry A C 0 function f : { 0 , 1 } n → { 0 , 1 } can b e w ell-approximat ed, in the L 1 -norm, by low-de gr e e sandwiching p olynomials : real p olynomials p ℓ , p u : R n → R , of degree O ( p olylog n ), su c h th at p ℓ ( x ) ≤ f ( x ) ≤ p u ( x ) for all x ∈ { 0 , 1 } n . Since p ℓ and p u trivially ha v e the same exp ectation on an y k -wise ind ep end en t distrib ution that they ha ve on the uniform distribu tion, one can sho w that f m ust ha ve almost the same exp ectation as w ell. T o generalize Brav erman’s result from k -wise indep endence to almost k -w ise ind ep end ence, w e will sho w that it suffices to construct lo w-degree sandwic h p olynomials that satisfy a certain additional condition. This n ew condition (whic h w e call “lo w-fat”) basically sa ys that p ℓ and p u m u st b e r epresent able as linear com b in ations of terms (that is, pro ducts of x i ’s and (1 − x i )’s), in suc h a w ay that the sum of the absolute v alues of the co efficien ts is b ound ed—thereby prev en ting “massiv e cancellations” b et ween p ositive and negativ e terms. Un fortunately , while we kn o w t wo tec hniqu es for appro ximating A C 0 functions by lo w-degree p olynomials—that of Linial-Mansour- Nisan [27] and th at of Razb oro v [29] and S molensky [35]—neither tec hnique pro v id es anyt hing like the control o ve r co efficien ts that we need. T o construct low-fa t sandwic hing p olynomials, it seems necessary to r epro ve the LMN and Razb oro v-S molensky theorems in a more “conserv ativ e,” less “profligate” w a y . And such an adv ance seems lik ely to lead to breakthroughs in circuit complexit y and computational learning theory having nothing to do with quantum compu ting. Let us m en tion t wo further applications of F ourier Chec king : (1) I f the Generalized L in ial-Nisan C onjecture holds, then just like with F o urier Fishing , w e can “scale do wn by an exp onentia l,” to obtain a promise prob lem that is in B QLOGTIME but not in AC 0 . 6 Up to unimp ortant v ariations in the parameters 6 (2) Without an y assumptions, we can p ro ve the new results that there exist oracles relativ e to whic h BQP 6⊂ BPP path and BQP 6⊂ S ZK . W e can also r epro ve all previous oracle separations b et w een BQP and classical complexit y classes in a un ified fashion. T o summarize our conclusions: Theorem 3 Assuming the Gener alize d Linial-N isan Conje ctur e, ther e exists an or acle A r elative to which BQP A 6⊂ PH A , and ther e also exists a pr omise pr oblem in BQLOGTIME \ AC 0 . Unc ondi- tional ly, ther e exists an or acle A r elative to which BQP A 6⊂ BPP A path and BQP A 6⊂ SZK A . As a candidate p roblem, Fourier Checking has at least five adv an tages o ver the Re cursive F o urier Sampl ing problem of Bernstein and V azirani [11]. Firs t, it is m uc h simp ler to defin e and reason ab out. Second, F our ier Checking has the almost k -wise indep end ence prop ert y , which is not shared by Re cursive F ourier Sampl ing , and whic h immed iately connects the former to general questions ab out pseu d orandomness against constan t-depth circuits. Third, F ou rier Checking can yield exp onential separations b et ween qu an tu m and classical mo dels, rather than just qu asip olynomial ones. F ourth, one can h op e to u se Fourier Checking to giv e an oracle relativ e to whic h BQP is not in PH [ n c ] (or PH w ith n c alternations) for any fixed c ; by contrast, Recursive F ourier Sampl ing is in PH [lo g n ]. Fin ally , it is at least conceiv able that the quan tum algorithm for Fourier Checking is g o o d for something. W e lea ve the challe nge of find ing an explicit compu tational problem that “instant iates” F ourier Chec king , in the same wa y that F actoring and Discrete Logarithm instan tiated Shor’s p erio d-find ing pr oblem. 1.3 In Defense of Oracles This pap er is concerned w ith fin ding oracles relativ e to whic h B QP outp erforms classical complexit y classes. As such, it is op en to the usual ob jections: “But don’t oracle results m islead us ab out the ‘real’ world? What ab out n on-relativizing r esults lik e IP = PSP A CE [32]?” In our view, it is most helpful to think of oracle separations, n ot as stran ge metamathematica l claims, b u t as lower b ounds in a c oncr ete c omputationa l mo del that is natur al and wel l-motivate d in its own right. The mo d el in qu estion is query c omplexity , wh ere the resour ce to b e minimized is the n um b er of accesses to a very long input string. When someone giv es an oracle A r elativ e to whic h C A 6⊂ D A , what they really mean is simp ly that they ha ve foun d a problem th at C mac hines can solv e using sup erp olynomially few er queries than D mac hines. In other words, C has has “cleared the first p ossible obstacle”—the query complexit y obstacle—to having capabilities b ey ond those of D . O f cours e, it could b e (and sometimes is) that C ⊆ D for other reasons, but if we do n ot even ha ve a query complexit y lo w er b ound, then p r o ving one is in some s ense the ob vious place to start. Oracle separations hav e play ed a role in many of the cen tr al dev elopments of b oth classical and quan tum complexity theory . As mentio ned earlier, p ro vin g query complexit y lo we r b oun ds for PH mac h in es is essentiall y equ iv alen t to pro ving size lo wer b ounds for AC 0 circuits—and indeed, the pioneering AC 0 lo wer b ounds of the early 1980s w er e explicitly motiv ated by the goal of pro v- ing oracle separations for PH . 7 Within qu an tum computing, oracle results hav e p la ye d an ev en more decisiv e role: the first evidence for the p ow er of qu an tu m computers came fr om the oracle 7 Y ao’s p ap er [39] w as entitled “S ep arating the p olynomial-time hierarc hy by oracles”; the F u rst-Saxe-Sipser pap er [16] was entitled “P arity , circuits, and th e p olyn omial time h ierarch y .” 7 separations of Bernstein-V azirani [11] an d Simon [34], and Sh or’s algorithm [33] cont ains an oracle algorithm (for th e Period-Finding pr oblem) at its core. Ha ving said all that, if for some reason one still feels a verse to the language of oracles, then (as menti oned b efore) one is free to scale ev erything do wn by an exp onentia l, and to reint erpret a relativized separation b et wee n BQP and PH as an un relativized separation b et we en BQLOGTIM E and AC 0 . 2 Preliminaries It will b e con v enient to consider Bo olean functions of the f orm f : { 0 , 1 } n → {− 1 , 1 } . Th roughout this pap er, w e let N = 2 n ; w e will often view the truth table of a Bo olean fun ction as an “input” of size N . Giv en a Bo olean function f : { 0 , 1 } n → {− 1 , 1 } , the F ourier trans form of f is defi ned as b f ( z ) := 1 √ N X x ∈{ 0 , 1 } n ( − 1) x · z f ( x ) . Recall Pa rsev al’s identit y: X x ∈{ 0 , 1 } n f ( x ) 2 = X z ∈{ 0 , 1 } n b f ( z ) 2 = N . 2.1 Pr oblems W e fi r st define the F our ier Fishing problem, in b oth “distrib utional” and “promise” v ersions. In the distrib utional ve rsion, w e are giv en oracle access to n Bo olean f unctions f 1 , . . . , f n : { 0 , 1 } n → {− 1 , 1 } , which are c hosen uniformly and ind ep endently at random. The task is to output n str ings, z 1 , . . . , z n ∈ { 0 , 1 } n , at least 75% of w hic h satisfy b f i ( z i ) ≥ 1 and at least 25% of whic h satisfy b f i ( z i ) ≥ 2. (Note that these thresholds are not arb itrary , but we re carefully chosen to pro duce a separation b et ween the quantum and classical mo dels!) W e n o w w ant a version of Fourier Fishing that r emo ve s the n eed to assume the f i ’s are uniformly random, replacing it with a worst-c ase p romise on the f i ’s. Call an n -tuple h f 1 , . . . , f n i of Bo olean fu nctions go o d if n X i =1 X z i : | b f i ( z i ) | ≥ 1 b f i ( z i ) 2 ≥ 0 . 8 N n, n X i =1 X z i : | b f i ( z i ) | ≥ 2 b f i ( z i ) 2 ≥ 0 . 26 N n. (W e will show in Lemma 8 that the v ast m a jorit y of h f 1 , . . . , f n i are go o d .) In Promise Fourier Fishing , w e are giv en oracle access to Boolean f u nctions f 1 , . . . , f n : { 0 , 1 } n → { − 1 , 1 } , whic h are promised to b e go o d. Th e task, again, is to output s tr ings z 1 , . . . , z n ∈ { 0 , 1 } n , at least 75% of whic h satisfy b f i ( z i ) ≥ 1 and at least 25% of whic h satisfy b f i ( z i ) ≥ 2. Next w e d efi ne a decision problem called Fourier Checking . Here w e are giv en oracle access to t wo Bo olean functions f , g : { 0 , 1 } n → {− 1 , 1 } . W e are pr omised that either 8 (i) h f , g i was drawn fr om the u niform distr ibution U , which s ets ev ery f ( x ) and g ( y ) b y a fair, indep en den t coin toss. (ii) h f , g i w as dra w n fr om the “forrelated” distribution F , whic h is d efined as follo ws. First c ho ose a r andom real vec tor v = ( v x ) x ∈{ 0 , 1 } n ∈ R N , b y dra w ing eac h entry in dep end en tly from a Gaussian distribu tion with mean 0 and v ariance 1. Then set f ( x ) := sgn ( v x ) and g ( x ) := sgn ( b v x ) for all x . Here sgn ( α ) := 1 if α ≥ 0 − 1 if α < 0 and b v is the F ourier transform of v ov er Z n 2 : b v y := 1 √ N X x ∈{ 0 , 1 } n ( − 1) x · y v x . In other words, f and g individual ly are still uniform ly random, b ut they are no longer indep en den t: no w g is now extremely well correlated with the F our ier transform of f (hence “forrelated”). The problem is to accept if h f , g i was dr a wn fr om F , and to reject if h f , g i was d r a wn from U . Note that, since F and U o v erlap sligh tly , we can only hop e to succeed with o verwhelming pr obabilit y o ve r the c h oice of h f , g i , n ot for ev ery h f , g i p air. W e can also define a pr omise-pr oblem v ers ion of Fourier Che cking . In Pr omise F ou rier Checking , we are promised that th e quan tit y p ( f , g ) := 1 N 3 X x,y ∈{ 0 , 1 } n f ( x ) ( − 1) x · y g ( y ) 2 is either at least 0 . 05 or at most 0 . 01. The problem is to accept in the former case and r eject in the latter case. 2.2 Complexity Classes See the Complexit y Zo o 8 for the defi n itions of standard complexit y classes, s u c h as BQP , AM , and PH . When we write C PH (i.e., a complexit y class C with an oracle for th e p olynomial hierarch y), w e mean ∪ k ≥ 1 C Σ P k . W e will consider n ot only d ecision problems, but also r elation pr oblems (also called function pr oblems ). In a relation problem, the output is n ot a single bit but a p oly ( n )-bit string y . There could b e many v alid y ’s for a giv en instance, and the algorithm’s task is to output an y one of them. The defin itions of FP and FNP (the relation versions of P and NP ) are s tandard. W e n o w d efine FBPP and F BQP , the relation v ersions of BPP and BQP . Definition 4 FBPP is the class of r elations R ⊆ { 0 , 1 } ∗ × { 0 , 1 } ∗ for which ther e exists a pr ob a- bilistic p olynom ial-time algorithm A that, given any input x ∈ { 0 , 1 } n , pr o duc es an output y such that Pr [( x, y ) ∈ R ] = 1 − o (1) , 8 www.complexit yzo o.com 9 wher e the pr ob ability is over A ’s internal r andomness. (In p articular, this implies that for every x , ther e exists at le ast one y such that ( x, y ) ∈ R .) F BQP is define d the same way, exc ept that A is a quantum algorithm r ather than a classic al one. An imp ortant p oin t ab out FBPP and FBQP is that, as far as w e kn o w, these classes d o not admit amplification. In other words, the v alue of an algorithm’s success probabilit y might actually matter, not ju st the fact that the pr obabilit y is b ound ed ab o ve 1 / 2. T his is why w e adopt the con ven tion that an algorithm “succeeds” if it outp u ts ( x, y ) ∈ R with probabilit y 1 − o (1). In practice, we will giv e oracle p roblems for whic h the FB QP algorithm succeeds with probability 1 − 1 / exp ( n ), w hile any FB PP PH algorithm succeeds w ith probabilit y at most (sa y) 0 . 99. Ho w far the constant in this separation can b e impr o ved is an op en problem. Another imp ortan t p oin t is that, w hile BPP PH = P PH (whic h follo ws f rom B PP ⊆ Σ P 2 ), th e class FBPP PH is strictly larger than FP PH . T o see this, consider the relation R = { (0 n , y ) : K ( y ) ≥ n } , where w e are giv en n , and aske d to outp ut any string of Kolmogoro v complexit y at least n . Clearly this p roblem is in FBPP : just output a random 2 n -b it string. On the other h and, j ust as ob viously the problem is not in FP PH . This is why w e need to constru ct an oracle A su c h that FBQP A 6⊂ FBPP PH A : b ecause constructing an oracle A su c h th at FBQP A 6⊂ FP PH A is trivial and not ev en related to quantum computing. W e n o w d iscuss some “lo w-lev el” complexit y classes. A C 0 is the class of prob lems solv able by a nonuniform family of AND/OR/NOT circu its, with depth O (1), size p oly ( n ), and u n b ound ed fanin. When we sa y “ A C 0 circuit,” w e mean a constan t-depth circuit of AND/OR/NOT gates, n ot necessarily of p olynomial size. An y suc h circuit can b e made into a formula (i.e., a circuit of fanout 1) with only a p olynomial increase in size. T he circuit has depth d if it consists of d alternating la ye rs of AND and OR gates (without loss of generalit y , th e NOT gate s can all b e push ed to the b ottom, and w e do n ot coun t them to w ard s the depth). F or examp le, a DNF (Disjunctiv e Normal F orm) formula is just an AC 0 circuit of depth 2. W e will also b e in terested in qu an tu m lo garithmic time, which can b e defined naturally as follo ws: Definition 5 BQLOGTIME is the class of languages L ⊆ { 0 , 1 } ∗ that ar e de cidable, with b ounde d pr ob ability of err or, by a LOG TIME -uniform family of qu antum cir cuits { C n } n such that e ach C n has O (log n ) gates, and c an include gates that make r andom-ac c ess queries to the input string x = x 1 . . . x n (i.e., that map | i i | z i to | i i | z ⊕ x i i f or every i ∈ [ n ] ). One other complexit y class th at arises in this pap er, w h ic h is less well kn own than it should b e, is BPP path . Lo osely sp eaking, BPP path can b e defined as the class of pr oblems th at are solv able in pr obabilistic p olynomial time, giv en the ability to “p ostselect” (that is, discard all runs of the computation that do n ot pro duce a desired resu lt, even if suc h run s are the o verwhelming ma j orit y). F ormally: Definition 6 BPP path is the class of languages L ⊆ { 0 , 1 } ∗ for which ther e exists a BPP machine M , which c an either “suc c e e d” or “fail” and c onditione d on suc c e e ding either “ ac c e pt” or “r eje ct,” such that for al l inputs x : 10 (i) P r [ M ( x ) suc c e e ds ] > 0 . (ii) x ∈ L = ⇒ Pr [ M ( x ) ac c epts | M ( x ) suc c e e ds ] ≥ 2 3 . (iii) x / ∈ L = ⇒ P r [ M ( x ) ac c epts | M ( x ) suc c e e ds ] ≤ 1 3 . BPP path w as defined b y Han, Hemaspaandra, and Th ierauf [25], who also sho wed that MA ⊆ BPP path and P NP || ⊆ BPP path ⊆ BPP NP || . Usin g F ourier Checking , we will construct an oracle A r elativ e to wh ic h BQP A 6⊂ BPP A path . This result might not sound amazing, but (i) it is new, (ii) it do es not follo w fr om the “standard” quan tu m algo rithms, suc h as those of Simon [34] and Shor [33], and (iii) it sup ersedes almost all pr evious oracle results placing BQP outside classical complexit y classes. 9 As another illustration of the v ersatilit y of Fourier Che cking , we u se it to giv e an A such that BQ P A 6⊂ SZ K A , where SZK is Statistical Zero Kno w ledge. The opp osite direction—an A su ch th at SZK A 6⊂ BQP A —w as sho wn by Aaronson [1] in 2002 . 3 Quan tum Algorithms In this section, w e sho w that F ourier Fishing and F ourier Checking b oth admit simp le quan tum algorithms. 3.1 Quan tum Algorit hm for F ourier Fishing Here is a quantum algorithm, FF-A LG , that solv es F our ier Fishing with o v erw helming probability in O n 2 time and n qu an tum queries (one to eac h f i ). F or i := 1 to n , first p repare the state 1 √ N X x ∈{ 0 , 1 } n f i ( x ) | x i , then apply Hadamard gates to all n qub its, then measur e in th e compu tational basis and output the result as z i . In tuitiv ely , FF-ALG samples the F ourier coefficient s of eac h f i under a distribu tion that is sk ewed to wa rds larger co efficients; the algorithm’s b eha vior is illustrated pictorially in Figure 1. W e now giv e a formal analysis. Recall the d efinition of a “go o d” tuple h f 1 , . . . , f n i from Section 2.1. Assuming h f 1 , . . . , f n i is goo d, it is easy to analyze FF-ALG ’s success p robabilit y . Lemma 7 A ssuming h f 1 , . . . , f n i i s go o d, FF-ALG suc c e e ds with pr ob ability 1 − 1 / exp ( n ) . Pro of. Let h z 1 , . . . , z n i b e the algorithm’s output. F or eac h i , let X i b e the ev ent that b f i ( z i ) ≥ 1 and let Y i b e the ev en t that b f i ( z i ) ≥ 2. Also let p i := Pr [ X i ] and q i := Pr [ Y i ], where the 9 The one exception is t h e result of Green and Pruim [24] that there exists an A relativ e to which BQP A 6⊂ P NP A , but that can also b e easily reprodu ced using Fourier Checking . 11 Figure 1: T he F our ier co efficien ts of a rand om Bo olean function follo w a Gaussian distribu tion, with mean 0 and v ariance 1. Ho w ever, larger F ourier co efficients are more likel y to b e obs er ved b y the quantum algorithm. probabilit y is o v er FF -ALG ’s in ternal (quantum) r an d omness. Then clearly p i = 1 N X z i : | b f i ( z i ) | ≥ 1 b f i ( z i ) 2 , q i = 1 N X z i : | b f i ( z i ) | ≥ 2 b f i ( z i ) 2 . So by assu mption, p 1 + · · · + p n ≥ 0 . 8 n, q 1 + · · · + q n ≥ 0 . 26 n. By a Chern off/Hoeffdin g b ound, it follo ws that Pr [ X 1 + · · · + X n ≥ 0 . 75 n ] > 1 − 1 exp ( n ) , Pr [ Y 1 + · · · + Y n ≥ 0 . 25 n ] > 1 − 1 exp ( n ) . Hence FF-ALG su cceeds with 1 − 1 / exp ( n ) p robabilit y by the union b oun d. W e also hav e the follo wing: Lemma 8 h f 1 , . . . , f n i is go o d with pr ob ability 1 − 1 / e xp ( n ) , if the f i ’s ar e chosen uniformly at r andom. 12 Pro of. Ch o ose f : { 0 , 1 } n → {− 1 , 1 } u n iformly at random. Then for eac h z , the F ourier co efficien t b f ( z ) follo ws a n ormal distribution, w ith mean 0 and v ariance 1. S o in the limit of large N , E f X z : | b f ( z ) | ≥ 1 b f ( z ) 2 = X z ∈{ 0 , 1 } n Pr h b f ( z ) ≥ 1 i E h b f ( z ) 2 | b f ( z ) ≥ 1 i ≈ 2 N √ 2 π Z ∞ 1 e − x 2 / 2 x 2 dx ≈ 0 . 801 N . Lik ewise, E f X z : | b f ( z ) | ≥ 2 b f ( z ) 2 ≈ 2 N √ 2 π Z ∞ 2 e − x 2 / 2 x 2 dx ≈ 0 . 261 N . Since the f i ’s are chose n in dep end en tly of one another, it follo ws by a C hernoff b oun d that n X i =1 X z i : | b f i ( z i ) | ≥ 1 b f i ( z i ) 2 ≥ 0 . 8 N n, n X i =1 X z i : | b f i ( z i ) | ≥ 2 b f i ( z i ) 2 ≥ 0 . 26 N n with probability 1 − 1 / exp ( n ) ov er the c hoice of h f 1 , . . . , f n i . Com b ining Lemmas 7 and 8, we fin d that FF-ALG succeeds with probabilit y 1 − 1 / exp ( n ), w here the pr obabilit y is o ver b oth h f 1 , . . . , f n i and FF-A LG ’s in tern al randomn ess. 3.2 Quan tum Algorit hm for F ourier Checking W e no w tur n to F ourier Chec king , the p roblem of d eciding whether tw o Bo olean f u nctions f , g are indep enden t or forrelated. Here is a quan tum algorithm, FC- ALG , th at solve s Fourier Check- ing w ith constan t error pr obabilit y usin g O (1) queries. First pr ep are a uniform su p erp osition o ver all x ∈ { 0 , 1 } n . Then qu ery f in sup erp osition, to create the state 1 √ N X x ∈{ 0 , 1 } n f ( x ) | x i Then apply Hadamard gates to all n qubits, to create the state 1 N X x,y ∈{ 0 , 1 } n f ( x ) ( − 1) x · y | y i . Then query g in sup erp osition, to create the state 1 N X x,y ∈{ 0 , 1 } n f ( x ) ( − 1) x · y g ( y ) | y i . 13 Then apply Hadamard gates to all n qubits again, to create the state 1 N 3 / 2 X x,y ,z ∈{ 0 , 1 } n f ( x ) ( − 1) x · y g ( y ) ( − 1) y · z | z i . Finally , measur e in the computational basis, and “accept” if and only if the outcome | 0 i ⊗ n is observ ed . If needed, rep eat the whole algorithm O (1) times to b o ost the su ccess probabilit y . It is clear th at the p robabilit y of observing | 0 i ⊗ n (in a single run of FC-A LG ) equals p ( f , g ) := 1 N 3 X x,y ∈{ 0 , 1 } n f ( x ) ( − 1) x · y g ( y ) 2 . Recall that Promise F ourier Checking wa s the pr oblem of deciding whether p ( f , g ) ≥ 0 . 05 or p ( f , g ) ≤ 0 . 01, promised that one of these is the case. Thus, we immediately get a quan tum algorithm to solv e Promise Fourier Check ing , with constan t error pr ob ab ility , u sing O (1) queries to f and g . F or the d istributional v ersion of Fourier Checking , w e also need the follo wing theorem. Theorem 9 If h f , g i i s dr awn fr om the uniform distribution U , then E U [ p ( f , g )] = 1 N . If h f , g i is dr awn f r om the forr elate d distribution F , then E F [ p ( f , g )] > 0 . 07 . Pro of. Th e first part follo ws immediately by sym m etry (i.e., the fact that all N = 2 n measuremen t outcomes of the quant um algorithm are equally lik ely). F or the second p art, let v ∈ R N b e the vect or of indep endent Gaussians used to generate f and g , let w = v / k v k 2 b e v scaled to hav e un it norm, and let H b e the n -qubit Hadamard matrix. Also let flat ( w ) b e the unit ve ctor whose x th en try is sgn ( w x ) / √ N = f ( x ) / √ N , and let flat ( H w ) b e the un it vect or whose x th en try is sgn ( b v x ) / √ N = g ( x ) / √ N . Then p ( f , g ) equ als flat ( w ) T H flat ( H w ) 2 , or the squ ared inner pro du ct b et ween the v ectors flat ( w ) and H flat ( H w ) . Not e th at w T · H H w = w T w = 1. So the whole problem is to understand the “discretization err or” incurred in rep lacing w T b y flat ( w ) T and H H w b y H flat ( H w ) . By the tr iangle inequalit y , the angle b et w een flat ( w ) and H flat ( H w ) is at most the angle b et wee n fl at ( w ) and w , plu s the angle b et we en w and H flat ( H w ). In other words: arccos flat ( w ) T H flat ( H w ) ≤ arccos flat ( w ) T w + arccos w T H flat ( H w ) . 14 No w, flat ( w ) T w = X x ∈{ 0 , 1 } n w x · 1 √ N | w x | w x = 1 √ N X x ∈{ 0 , 1 } n | w x | = P x ∈{ 0 , 1 } n | v x | √ N k v k 2 . Recall that eac h v x is an indep en d en t real Gaussian with m ean 0 and v ariance 1, meanin g that eac h | v x | is an ind ep end ent nonnegativ e random v ariable w ith exp ectation p 2 /π . So b y standard tail b ounds, for all constan ts ε > 0 we ha ve Pr v X x ∈{ 0 , 1 } n | v x | ≤ r 2 π − ε ! N ≤ 1 exp ( N ) , Pr h k v k 2 2 ≥ (1 + ε ) N i ≤ 1 exp ( N ) . So by th e union b ound, Pr v " flat ( w ) T w ≤ r 2 π − ε # ≤ 1 exp ( N ) . Since H is u nitary , the same analysis applies to w T H fl at ( H w ). Therefore, for all constants ε > 0, with 1 − 1 / exp ( N ) probabilit y we hav e arccos flat ( w ) T w ≤ arccos r 2 π ! + ε, arccos w T H fl at ( H w ) ≤ arccos r 2 π ! + ε. So setting ε = 0 . 0001 , arccos flat ( w ) T H flat ( H w ) ≤ arccos flat ( w ) T w + arccos w T H flat ( H w ) ≤ 2 arccos r 2 π ! + 2 ε ≤ 1 . 3 Therefore, with 1 − 1 / exp ( N ) probabilit y o ver h f , g i d ra w n from F , flat ( w ) T H flat ( H w ) ≥ cos 1 . 3 , in which case p ( f , g ) ≥ (cos 1 . 3) 2 ≈ 0 . 072. Com b ining Theorem 9 with Mark o v’s inequalit y , we immediately get the follo wing: 15 Corollary 10 Pr h f ,g i∼U [ p ( f , g ) ≥ 0 . 01] ≤ 100 N , Pr h f ,g i∼ D [ p ( f , g ) ≥ 0 . 05] ≥ 1 50 . 4 The Classical Complexit y of F ourier Fishing In S ection 3.1, we ga ve a qu an tum algorithm for F ourier F ishing that made only one query to eac h f i . By con trast, it is not h ard to sho w that an y classical algorithm for F o urier Fishing requires exp onent ially man y qu eries to the f i ’s. In th is section, we pro v e a muc h stronger result: that F ou rier Fishing is n ot in FBPP PH . Th is r esult do es not rely on any u nprov ed conjectures. 4.1 Constant-Depth Circuit Low er Bounds Our starting p oint will b e the follo wing AC 0 lo wer b ound , wh ic h can b e found in th e b o ok of H ˚ astad [36] for example. Theorem 11 ([36]) Any depth- d cir c uit that ac c epts al l n -bit strings of H amming weight n/ 2 + 1 , and r eje cts al l strings of Hamming weight n/ 2 , has size exp Ω n 1 / ( d − 1) . W e no w giv e a corollary of T h eorem 11, whic h (though simple) seems to b e new, and migh t b e of indep end en t in terest. Consider the follo wing problem, wh ic h we call ε -Bias Detect ion . W e are giv en a string y = y 1 . . . y m ∈ { 0 , 1 } m , and are promised that eac h bit y i is 1 with in dep en d en t probabilit y p . The task is to decide wh ether p = 1 / 2 or p = 1 / 2 + ε . Corollary 12 L et U [ ε ] b e the distribution over { 0 , 1 } m wher e e ach bit is 1 with indep endent pr ob- ability 1 / 2 + ε . Then any depth- d cir cu i t C such that Pr U [ ε ] [ C ] − Pr U [0] [ C ] = Ω (1) has size exp Ω 1 /ε 1 / ( d +2) . Pro of. Supp ose such a distinguishin g circuit C exists, with dep th d and size S , for some ε > 0 (the parameter m is actually irrelev ant). Let n = 1 /ε , and assume f or s im p licit y th at n is an in teger. Using C , w e will constru ct a new circuit C ′ with depth d ′ = d + 3 and s ize S ′ = O ( n S ) + p oly ( n ), whic h accepts all strings x ∈ { 0 , 1 } n of Hammin g w eigh t n/ 2 + 1, and rejects all strings of Hamming w eight n/ 2. By Theorem 11, th is will imp ly that the original circuit C must h a ve h ad size S = 1 n exp Ω n 1 / ( d ′ − 1) − p oly ( n ) = exp Ω 1 /ε 1 / ( d +2) . So fix an inpu t x ∈ { 0 , 1 } n , and su pp ose w e c ho ose m bits x i 1 , . . . , x i m from x , with eac h index i j c hosen u niformly at rand om w ith replacemen t. C all the r esulting m -bit strin g y . O bserve that if 16 x had Hamming weigh t n/ 2, then y will b e d istributed according to U [0], w hile if x had Hamming w eight n/ 2 + 1, then y will b e distributed according to U [ ε ]. So by assump tion, Pr [ C ( y ) | | x | = n/ 2] = α, Pr [ C ( y ) | | x | = n/ 2 + 1] = α + δ for some constants α and δ 6 = 0 (w e can assume δ > 0 without loss of generalit y). No w sup p ose w e rep eat the ab o ve exp eriment T = k n times, for some constant k = k ( α, δ ) . That is, we create T strings y 1 , . . . , y T b y c ho osing random bits of x , so that eac h y i is distributed indep en den tly according to either U [0] or U [ ε ]. W e then apply C to eac h y i . Let Z = C ( y 1 ) + · · · + C ( y T ) b e the num b er of C inv o cations that accept. Th en b y a Cher n off b ound , if | x | = n / 2 then Pr Z > αT + δ 3 T < exp ( − n ) , while if | x | = n/ 2 + 1 then Pr Z < αT + 2 δ 3 T < exp ( − n ) . By taking k large enough, we can mak e b oth of th ese pr obabilities less th an 2 − n . By the union b oun d , this implies that there m ust exist a w ay to choose y 1 , . . . , y T so that | x | = n 2 = ⇒ Z ≤ αT + δ 3 T , | x | = n 2 + 1 = ⇒ Z ≥ αT + 2 δ 3 T for every x with | x | ∈ { n/ 2 , n/ 2 + 1 } simulta neously . In forming the circuit C ′ , w e simply h ardwire that c h oice. The last step is to decide whether Z ≤ αT + δ 3 T or Z ≥ αT + 2 δ 3 T . This can b e don e using an A C 0 circuit f or the Appro xima te Majo rity problem (see Viola [37] for example), wh ich has depth 3 and size p oly ( T ). The end result is a circuit C ′ to distinguish | x | = n/ 2 from | x | = n/ 2 + 1, whic h has depth d + 3 and size T S + p oly ( T ) = O ( nS ) + p oly ( n ). 4.2 Secretly Biased F ourier Co efficien ts In this s ection, we pro v e tw o lemmas indicating that one can slightly bias one of the F our ier co efficien ts of a random Bo olean function f : { 0 , 1 } n → {− 1 , 1 } , and ye t still ha ve f b e information- theoreticall y ind istinguishable f rom a random Bo olean fu nction (so that, in particular, an adv ersary has no wa y of kno wing which F ourier co efficien t was biased). Th ese lemmas will pla y a key role in our reduction fr om ε -Bias Detection to Fourier Fishing . Fix a strin g s ∈ { 0 , 1 } n . Let A [ s ] b e the probability distribution o ver functions f : { 0 , 1 } n → {− 1 , 1 } where eac h f ( x ) is 1 with indep enden t p r obabilit y 1 2 + ( − 1) s · x 1 2 √ N , and let B [ s ] b e the distribution where eac h f ( x ) is 1 with ind ep endent p robabilit y 1 2 − ( − 1) s · x 1 2 √ N . Then let D [ s ] = 1 2 ( A [ s ] + B [ s ]) (that is, an equal mixture of A [ s ] and B [ s ]). 17 Lemma 13 Supp ose Alic e cho oses s ∈ { 0 , 1 } n uniformly at r andom, then dr aws f ac c or ding to D [ s ] . She ke eps s se cr et, but se nds the truth table of f to Bob. A f ter examining f , Bob outputs a string z such that b f ( z ) ≥ β . Then Pr [ s = z ] ≥ e β + e − β 2 √ eN . wher e the pr ob ability is over al l runs of the pr oto c ol. Pro of. By Y ao’s principle, w e can assume without loss of generalit y that Bob’s strategy is deter- ministic. F or eac h z , let F [ z ] b e the set of all f ’s that cause Bob to output z . Then the first step is to low er-b oun d Pr D [ z ] [ f ], for some fixed z and f ∈ F [ z ] . Let N f [ z ] b e the num b er of inp uts x ∈ { 0 , 1 } n suc h that f ( x ) = ( − 1) z · x . It is not hard to see that N f [ z ] = N 2 + √ N b f ( z ) 2 . So Pr D [ z ] [ f ] = 1 2 Pr A [ z ] [ f ] + Pr B [ z ] [ f ] = 1 2 Y x ∈{ 0 , 1 } n 1 2 + ( − 1) z · x f ( x ) 2 √ N + Y x ∈{ 0 , 1 } n 1 2 − ( − 1) z · x f ( x ) 2 √ N = 1 2 N +1 1 + 1 √ N N f [ z ] 1 − 1 √ N N − N f [ z ] + 1 − 1 √ N N f [ z ] 1 + 1 √ N N − N f [ z ] ! = 1 2 N +1 1 + 1 / √ N ( √ N b f ( z )+ N ) / 2 1 − 1 / √ N ( √ N b f ( z ) − N ) / 2 + 1 − 1 / √ N ( √ N b f ( z )+ N ) / 2 1 + 1 / √ N ( √ N b f ( z ) − N ) / 2 = 1 2 N +1 1 − 1 N N/ 2 1 + 1 / √ N 1 − 1 / √ N ! √ N b f ( z ) / 2 + 1 − 1 / √ N 1 + 1 / √ N ! √ N b f ( z ) / 2 = 1 2 √ e 2 N e b f ( z ) + e − b f ( z ) ≥ e β + e − β 2 √ e 2 N . Here the second-to-last line tak es the limit as N → ∞ , while the last line follo w s from the as- sumption b f ( z ) ≥ β , together w ith the fact that e y + e − y increases monotonically a w ay from y = 0. 18 Summing o ver all z and f , Pr [ s = z ] = X z ∈{ 0 , 1 } n X f ∈F [ z ] Pr [ f ] · Pr [ s = z | f ] = X z ∈{ 0 , 1 } n X f ∈F [ z ] Pr [ f ] · Pr [ f | s = z ] Pr [ s = z ] Pr [ f ] = 1 N X z ∈{ 0 , 1 } n X f ∈F [ z ] Pr D [ z ] [ f ] ≥ e β + e − β 2 √ eN . No w let D = E s [ D [ s ]] (that is, an equal mixture of all the D [ s ]’s). W e claim that D is extremely close in v ariation distance to U , the uniform distribution o ver all Boolean functions f : { 0 , 1 } n → {− 1 , 1 } . Lemma 14 kD − U k ≤ e − 1 2 √ 2 eN . Pro of. By a calculation from Lemm a 13, for all f and s w e ha ve Pr D [ s ] [ f ] = 1 2 √ e 2 N e b f ( s ) + e − b f ( s ) in the limit of large N . Hence Pr D [ f ] = E s Pr D [ s ] [ f ] = 1 2 √ eN 2 N X s ∈{ 0 , 1 } n e b f ( s ) + e − b f ( s ) . Clearly E f [Pr D [ f ]] = 1 / 2 N . Our goal is to u pp er-b ound the v ariance V ar f [Pr D [ f ]], wh ic h mea- sures the d istance from D to the un if orm d istribution. In the limit of large N , we h av e E f Pr D [ f ] 2 = 1 4 eN 2 2 2 N X s E f e b f ( s ) + e − b f ( s ) 2 + X s 6 = t E f h e b f ( s ) + e − b f ( s ) e b f ( t ) + e − b f ( t ) i = 1 4 eN 2 2 2 N P s 1 √ 2 π R ∞ −∞ e − x 2 / 2 ( e x + e − x ) 2 dx + P s 6 = t h 1 √ 2 π R ∞ −∞ e − x 2 / 2 ( e x + e − x ) dx i 2 = 1 4 eN 2 2 2 N 2 e 2 + 2 N + 4 eN ( N − 1) = 1 2 2 N 1 + ( e − 1) 2 2 eN ! . Hence V ar f Pr D [ f ] = E f Pr D [ f ] 2 − E f Pr D [ f ] 2 = ( e − 1) 2 2 eN 2 2 N . 19 So by C auc hy-Sc hw arz, E f Pr D [ f ] − Pr U [ f ] ≤ s V ar f Pr D [ f ] = e − 1 √ 2 eN · 1 2 N and kD − U k ≤ e − 1 2 √ 2 eN . An immediate corollary of Lemm a 14 is that, if a F o urier Fishing algorithm succeeds with probabilit y p on h f 1 , . . . , f n i drawn fr om U n , then it also succeeds with probabilit y at least p − kD n − U n k ≥ p − ( e − 1) n 2 √ 2 eN on h f 1 , . . . , f n i drawn fr om D n . 4.3 Put ting It All T ogether Using the results of S ections 4.1 and 4.2, w e are no w ready to pro ve a low er b ound on the constant - depth circuit complexit y of F ou rier Fishing . Theorem 15 Any depth- d cir cuit that solves the Fourier Fishing pr oblem, with pr ob ability at le ast 0 . 99 over f 1 , . . . , f n chosen uniformly at r andom, has size exp Ω N 1 / (2 d +8) . Pro of. Let C b e a circuit of dep th d and size s . Let G b e the set of all h f 1 , . . . , f n i on whic h C suc c e e ds : that is, for wh ic h it outpu ts z 1 , . . . , z n , at least 75% of which satisfy b f i ( z i ) ≥ 1 and at least 25% of whic h satisfy b f i ( z i ) ≥ 2. S u pp ose Pr U n [ h f 1 , . . . , f n i ∈ G ] ≥ 0 . 99 . Then by L emm a 14, we also ha ve Pr D n [ h f 1 , . . . , f n i ∈ G ] ≥ 0 . 99 − ( e − 1) n 2 √ 2 eN ≥ 0 . 98 for sufficientl y large n . Using the ab ov e fact, w e w ill con vert C into a n ew circuit C ′ that solv es the ε -Bias Dete ction problem of Corollary 12, with ε := 1 2 √ N . This C ′ will ha v e depth d ′ = d + 2 and size S ′ = O ( N S ). By Corollary 12 , this will imp ly that C itself must h a ve had size S = exp Ω 1 /ε 1 / ( d ′ +2) = exp Ω N 1 / (2 d +8) . Let M = N 2 n , and let R = r 1 . . . r M ∈ { 0 , 1 } M b e a string of b its where eac h r j is 1 with indep en den t probabilit y p . W e wan t to decide whether p = 1 / 2 or p = 1 / 2 + ε —t hat is, wh ether R 20 w as dr a wn from U [0] or U [ ε ]. W e can do this as follo ws. First, choose str in gs s 1 , . . . , s n ∈ { 0 , 1 } n , bits b 1 , . . . , b n ∈ { 0 , 1 } , and an inte ger k ∈ [ n ] uniformly at random. Next, defin e Bo olean functions f 1 , . . . , f n : { 0 , 1 } n → {− 1 , 1 } u sing the fir s t N n bits of R , like so: f i ( x ) := ( − 1) r ( i − 1) N + x + s i · x + b i . Finally , feed h f 1 , . . . , f n i as inpu t to C , and consider z k , the k th output of C (discarding the other n − 1 outputs). W e are in terested in Pr [ z k = s k ], wh ere the p robabilit y is o ver R , s 1 , . . . , s n , b 1 , . . . , b n , and k . If p = 1 / 2, notice that f 1 , . . . , f n are in dep end en t and un iformly r andom r egardless of s 1 , . . . , s n . So C gets no in formation ab out s k , and Pr [ z k = s k ] = 1 / N . On the other hand , if p = 1 / 2 + ε , then eac h f i is drawn indep enden tly f rom the distribution D [ s ] stu died in Lemm a 13. So b y the Lemma, for ev ery i ∈ [ n ], if b f i ( z i ) ≥ β then Pr f i [ z i = s i ] ≥ e β + e − β 2 √ eN . So assuming C succeeds (that is, h f 1 , . . . , f n i ∈ G ), w e ha v e Pr f 1 ,...,f n ,k [ z k = s k ] ≥ 1 4 e 2 + e − 2 2 √ eN + 1 2 e 1 + e − 1 2 √ eN ≥ 1 . 038 N . So for a r andom h f 1 , . . . , f n i dra wn according to D n , Pr f 1 ,...,f n ,k [ z k = s k ] ≥ 0 . 98 1 . 038 N ≥ 1 . 017 N . Notice that this is b ounded ab o ve 1 / N by a multiplicativ e constan t. No w let us rep eat the ab o v e exp erimen t N times. That is, for all j := 1 to N , w e generate Bo olean functions f j 1 , . . . , f j n : { 0 , 1 } n → {− 1 , 1 } b y the same pr ob ab ilistic p ro cedure as b efore, but eac h time using a new N n -bit substrin g of R j of R , as well as new s , b , and k v alues (denoted s j 1 , . . . , s j n , b j 1 , . . . , b j n , and k j ). W e then app ly C to eac h n -tuple h f j 1 , . . . , f j n i . Let z j b e the k th j string that C outpu ts when run on h f j 1 , . . . , f j n i . Then by the ab ov e, for eac h j ∈ [ N ] we h a ve p = 1 2 = ⇒ Pr z j = s j k j = 1 N , p = 1 2 + ε = ⇒ Pr z j = s j k j ≥ 1 . 017 N . F u r thermore, these probabilities are indep endent across the differen t j ’s. So let E b e the eve n t that there exists a j ∈ [ N ] suc h that z j = s j k j . Th en if p = 1 / 2 we h a ve Pr [ E ] = 1 − 1 − 1 N N ≈ 1 − 1 e ≤ 0 . 633 , while if p = 1 / 2 + ε we ha ve Pr [ E ] ≥ 1 − 1 − 1 . 017 N N ≥ 0 . 638 . 21 It should now b e clear h o w to create the circuit C ′ , whic h distinguishes R ∈ { 0 , 1 } M dra wn from U [0] f r om R dr a wn from U [ ε ] with constant b ias. F or eac h j ∈ [ N ], generate an n -tuple of Bo olean functions h f j 1 , . . . , f j n i fr om R and apply C to it; then chec k whether there exists a j ∈ [ N ] such that z j = s j k j . This chec king step can b e d on e by a d epth-2 circuit of size O ( N n ). Therefore, C ′ will ha v e depth d ′ = d + 2 and size s ′ = O ( N s ). A tec hn icalit y is that our c h oices of the s j i ’s, b j i ’s, and k j ’s were made randomly . Ho we v er, by Y ao’s principle, there clearly exist s j i ’s, b j i ’s, and k j ’s suc h that Pr U [ ε ] C ′ ( R ) − Pr U [0] C ′ ( R ) ≥ 0 . 638 − 0 . 633 = 0 . 005 . So in forming C ′ , we s imply hardw ire those c h oices. Com b ining Theorem 15 with standard diagonalization tricks, we can n o w prov e an oracle sep- aration (in f act, a r andom oracle separation) b etw een the complexit y classes FBQP and FBPP PH . Theorem 16 FBQP A 6⊂ FBPP PH A with pr ob ability 1 for a r andom or acle A . Pro of. W e inte rpret the oracle A as enco ding n random Bo olean functions f n 1 , . . . , f nn : { 0 , 1 } n → {− 1 , 1 } for eac h p ositiv e in teger n . Let R b e the r elational problem wh ere we are giv en 0 n as input, and suc c e e d if and only if w e output strin gs z 1 , . . . , z n ∈ { 0 , 1 } n , at least 3 / 4 of which satisfy b f ni ( z i ) ≥ 1 and at least 1 / 4 of wh ic h satisfy b f ni ( z i ) ≥ 2. Then by Lemmas 7 and 8, there exists an FBQP A mac hine M suc h that for all n , Pr [ M ( 0 n ) succeeds] ≥ 1 − 1 exp ( n ) , where the p robabilit y is o ver b oth A and the quant um randomness. Hence Pr [ M (0 n ) su cceeds] ≥ 1 − 1 / exp ( n ) on all but fi nitely many n , with probab ility 1 ov er A . Since we can simply hard wire the answers on the n ’s for whic h M fails, it f ollo ws that R ∈ FB QP A with probability 1 o ver A . On the other hand, let M b e an FBPP PH A mac hine. Then b y the standard con v ersion b et wee n PH and A C 0 , for ev er y n there exists a prob ab ilistic A C 0 circuit C M ,n , of size 2 poly ( n ) = 2 polyl og( N ) , that tak es A as inp ut and simulates M (0 n ). By Y ao’s principle, we can assume without loss of generalit y that C M ,n is deterministic, since the oracle A is already random. Then b y Th eorem 15, Pr A [ C M ,n succeeds] < 0 . 99 for all sufficien tly large n . By the indep end en ce of the f ni ’s, this is true even if w e condition on C M , 1 , . . . , C M ,n − 1 succeeding. S o as in the stand ard rand om oracle argument of Bennett and Gill [10], for eve ry fi xed M we h av e Pr A [ C M , 1 , C M , 2 , C M , 3 , . . . succeed] = 0 . So by th e union b ound, Pr A [ ∃ M : C M , 1 , C M , 2 , C M , 3 , . . . succeed] = 0 as wel l. It follo ws that FBQP A 6⊂ FBPP PH A with probability 1 o ver A . If we “scale do wn by an exp onen tial,” then w e can eliminate the need for the oracle A , and get a relation pr oblem that is solv ab le in quantum lo garithmic time b ut not in AC 0 . 22 Theorem 17 Ther e exists a r elation pr oblem solvable in BQLOGTIME but not in AC 0 . Pro of. In our relation p roblem R , the inpu t (of size M = 2 n n ) will enco d e the tru th tables of n Bo olean functions, f 1 , . . . , f n : { 0 , 1 } n → {− 1 , 1 } , which are promised to b e “go o d ” as d efi ned in Section 2.1. T he task is to solv e Promise Fourier Fish ing on h f 1 , . . . , f n i . By Lemma 7, there exists a quant um algorithm that runs in O ( n ) = O (log M ) time, making random accesses to the truth tables of f 1 , . . . , f n , that solv es R with probabilit y 1 − 1 / exp ( n ) = 1 − 1 / M Ω(1) . On the other hand, supp ose R is in AC 0 . Then we get a nonuniform circuit family { C n } n , of depth O (1) and size p oly ( M ) = 2 O ( n ) , that solv es Fourier Fish ing on all tuples h f 1 , . . . , f n i that are goo d. Recall th at by Lemma 8, a 1 − 1 / exp ( n ) fraction of h f 1 , . . . , f n i ’s are go o d. Therefore { C n } n actually solv es Fourier Fishing with probabilit y 1 − 1 / e xp ( n ) on h f 1 , . . . , f n i c hosen uniformly at random. But this con tradicts Th eorem 15. Hence R ∈ FBQLOGTIM E \ F AC 0 (where FBQLOG TIME and F AC 0 are the relatio n v ersions of BQLOGTIME and AC 0 resp ectiv ely). 5 The Classical Complexit y of F ourier Chec k ing Section 4 settled the relativized BQP v ersu s PH question, if w e are w illing to talk ab out relation problems. Ultimatel y , though, w e also care ab out decision problems. So in this section we consider the Fourier Check ing pr oblem, of deciding w hether tw o Bo olean fun ctions f , g are ind ep end en t or f orr elated. In Section 3.2, we sa w that Fourier Checking has quantum query complexit y O (1). What is its classical qu ery complexit y? 10 It is not hard to giv e a classica l algorithm that solv es F ou rier Checking using O √ N = O 2 n/ 2 queries. The algorithm is as follo ws: for some K = Θ √ N , first choose sets X = { x 1 , . . . , x K } and Y = { y 1 , . . . , y K } of n -bit strings u n iformly at random. Th en qu ery f ( x i ) and g ( y i ) for all i ∈ [ K ]. Finally , compu te Z := K X i,j =1 f ( x i ) ( − 1) x i · y j g ( y j ) , accept if | Z | is greater than some cutoff cK , and reject otherwise. F or suitable K and c , one can sho w that th is algorithm accepts a forrelated h f , g i pair with probabilit y at least 2 / 3, and accepts a rand om h f , g i pair with prob ab ility at least 1 / 3. W e omit the details of the analysis, as they are tedious and not needed elsewhere in the pap er. In the next section, we will sho w that Fourier Checking has a prop ert y called almost k -wise indep endenc e , whic h imm ediately implies a lo wer b ound of Ω 4 √ N = Ω 2 n/ 4 on its classical query complexit y (as w ell as exp onential lo w er b ounds on its MA , BPP path , and SZ K qu ery complexities). Indeed, we conjecture that almost k -wise in d ep end ence is enough to im p ly that Fourier Chec king is not in PH . W e discu ss the status of that conjecture in Section 6. 10 So long as we consider t h e distributional versio n of Fourier Checking , the deterministic and randomized q uery complexities are the same (by Y ao’s principle). 23 5.1 Almost k -Wise Indep endence Let Z = z 1 . . . z M ∈ {− 1 , 1 } M b e a string. Then a liter al is a term of the form 1 ± z i 2 , and a k - term is a pro d uct of k literals (eac h in v olving a different z i ), wh ic h is 1 if the literals all tak e on prescrib ed v alues and 0 otherwise. Let U b e the un iform d istribution o ve r {− 1 , 1 } M . The follo w ing defin ition will pla y a ma jor role in this w ork. Definition 18 A distribution D over {− 1 , 1 } M is ε -almost k - wise indep endent if for every k -term C , 1 − ε ≤ Pr D [ C ] Pr U [ C ] ≤ 1 + ε. (Note that Pr U [ C ] is just 2 − k .) No w let M = 2 n +1 = 2 N , and let F b e the forrelated distribution o v er pairs of Bo olean functions f , g : { 0 , 1 } n → {− 1 , 1 } . That is, w e samp le h f , g i ∈ F by fi rst choosing a v ector v = ( v x ) x ∈{− 1 , 1 } n ∈ R N of indep endent N (0 , 1) Gaussians, then setting f ( x ) := sgn ( v x ) for all x and g ( y ) := sgn ( b v y ) for all y . Theorem 19 F or al l k ≤ 4 √ N , the forr elate d distribution F is O k 2 / √ N -almost k -wise inde- p endent. Pro of. As a fir st step, we will pro v e an analogous statemen t for the real-v alued fu nctions F ( x ) := v x and G ( y ) := b v y ; then we will generalize to the discrete versions f ( x ) and g ( y ). Let U ′ b e the probabilit y m easur e o ve r h F , G i that corresp onds to case (i) of F our ier Checking : that is, w e c ho ose eac h F ( x ) and G ( y ) in dep end en tly from the Gaussian measure N ( 0 , 1). Let F ′ b e th e probabilit y measure o v er h F , G i that corresp onds to case (ii) of F ourier Check ing : that is, w e c ho ose eac h F ( x ) indep endent ly from N (0 , 1) , then set G ( y ) := b F ( y ) where b F ( y ) = 1 √ N X x ∈{ 0 , 1 } n ( − 1) x · y F ( x ) is the F ourier transform of F . Observ e that s in ce th e F ourier transform is unitary , G has the same marginal distribu tion as F un d er F ′ : namely , a p ro du ct of indep enden t N (0 , 1) Gaussians. Fix inputs x 1 , . . . , x K ∈ { 0 , 1 } n of F and y 1 , . . . , y L ∈ { 0 , 1 } n of G , for some K, L ≤ N 1 / 4 . Then giv en constan ts a 1 , . . . , a K , b 1 , . . . , b L ∈ R , let S b e the set of all h F , G i that satisfy the K + L equations F ( x i ) = a i for all 1 ≤ i ≤ K , (1) G ( y j ) = b j for all 1 ≤ j ≤ L . Clearly S is a (2 N − K − L )-dimensional affine sub space of R 2 N . The me asur e of S , u nder s ome probabilit y measure µ on R 2 N , is defi ned in the usu al w ay as µ ( S ) := Z h F ,G i∈ S µ ( F, G ) d h F , G i . 24 No w let ∆ S := a 2 1 + · · · + a 2 K + b 2 1 + · · · + b 2 L b e the squ ared distance b et w een S and the origin (that is, the minimum s quared 2-norm of an y p oint in S ). Then by the sph erical sym metry of the Gaussian measure, it is not hard to see that S has measure U ′ ( S ) = e − ∆ S / 2 √ 2 π K + L under U ′ . Ou r k ey claim is th at 1 − O ( K + L ) ∆ S √ N ≤ F ′ ( S ) U ′ ( S ) ≤ 1 + O ( K + L ) ∆ S √ N . T o prov e th is claim: r ecall that the p robabilit y measure o ve r F ind uced b y F ′ is just a sph erical Gaussian G on R N , and that G = b F uniqu ely determines F and vice v ersa. So consider the ( N − K − L )-dimensional affine subspace T of R N defined by the K + L equations F ( x i ) = a i for all 1 ≤ i ≤ K , b F ( y j ) = b j for all 1 ≤ j ≤ L . Then F ′ ( S ) = G ( T ): that is, to compute how m u c h measure F ′ assigns to S , it suffices to compute ho w m u c h measure G assigns to T . W e ha ve G ( T ) = e − ∆ T / 2 √ 2 π K + L , where ∆ T is the squared E uclidean distance b etw een T and the origin. Thus, our pr oblem redu ces to minimizing ∆ F := X x ∈{ 0 , 1 } n F ( x ) 2 o ve r all F ∈ T . By a standard fact ab out quadratic optimizati on, th e min imal F ∈ T will ha v e the form F ( x ) = α 1 E 1 ( x ) + · · · + α K E K ( x ) + β 1 χ 1 ( x ) + · · · + β L χ L ( x ) where E i ( x ) := 1 if x = x i 0 otherwise is an in d icator function, and χ j ( x ) := ( − 1) x · y j √ N is the y th j F our ier c haracter ev aluated at x . F urtherm ore, the co efficien ts { α i } i ∈ [ K ] , { β j } j ∈ [ L ] can 25 b e obtained by solving the linear system 1 0 0 ± 1 / √ N · · · ± 1 / √ N 0 . . . 0 . . . . . . . . . 0 0 1 ± 1 / √ N · · · ± 1 / √ N ± 1 / √ N · · · ± 1 / √ N 1 0 0 . . . . . . . . . 0 . . . 0 ± 1 / √ N · · · ± 1 / √ N 0 0 1 | {z } A α 1 . . . α K β 1 . . . β L | {z } u = a 1 . . . a K b 1 . . . b L | {z } w Here A is simply a m atrix of co v ariances: the top left blo ck records the inner pro d uct b et w een eac h E i and E j (and h ence is a K × K iden tity matrix), the b ottom righ t blo c k records th e inn er pro du ct b et w een eac h χ i and χ j (and hence is an L × L iden tity matrix), and the r emaining tw o blo c k s of size K × L r ecord the inner pr o duct b etw een eac h E i and χ j . Th us, to get the v ector of co efficien ts u ∈ R K + L , we simply need to calculat e A − 1 w . Define B := I − A . Then by T a ylor series expansion, A − 1 = ( I − B ) − 1 = I + B + B 2 + B 3 + · · · Notice th at ev ery en tr y of B is at m ost 1 / √ N in absolute v alue. This means that, for all p ositiv e in tegers t , eve ry entry of B t is at most ( K + L ) t − 1 N t/ 2 in abs olute v alue. Since K + L ≪ √ N , th is in turn means that ev ery entry of I − A − 1 has absolute v alue O 1 / √ N . So A − 1 is exp on entially close to the iden tity matrix. Hence, when we compute the vec tor u = A − 1 w , we fi n d that α i = a i + ε i for all 1 ≤ i ≤ K , β j = b j + δ j for all 1 ≤ j ≤ L , for some small error terms ε i and δ j . Sp ecifically , eac h ε i and δ j is the inner p ro du ct of w , a ( K + L )-dimensional v ector of length √ ∆ S , with a vec tor every entry of which h as absolute v alue O 1 / √ N . By Cauc hy-Sc hw arz, th is implies th at | ε i | , | δ j | = O p ( K + L ) ∆ S √ N ! 26 for all i, j . So ∆ T = min F ∈ T X x ∈{ 0 , 1 } n F ( x ) 2 = K X i =1 α 2 i + L X j =1 β 2 j + 2 K X i =1 L X j =1 α i β j √ N = K X i =1 ( a i + ε i ) 2 + L X j =1 ( b j + δ j ) 2 + 2 K X i =1 L X j =1 ( a i + ε i ) ( b j + δ j ) √ N = ∆ S ± O ( K + L ) ∆ S √ N + ( K + L ) 2 ∆ S N + ( K + L ) 3 ∆ S N 3 / 2 ! = ∆ S 1 ± O K + L √ N , where the fourth line m ade r ep eated use of Cauc hy-Sc hw arz, and the fifth line used the fact that K + L ≪ √ N . Hence F ′ ( S ) U ′ ( S ) = e − ∆ T / 2 / √ 2 π K + L e − ∆ S / 2 / √ 2 π K + L = exp ∆ S − ∆ T 2 = exp ± O ( K + L ) ∆ S √ N = 1 ± O ( K + L ) ∆ S √ N whic h pro v es the claim. T o prov e the theorem, we no w need to generalize to the discrete fu n ctions f and g . Here w e are giv en a term C that is a conjun ction of K + L in equalities: K of th e form F ( x i ) ≤ 0 or F ( x i ) ≥ 0, and L of the form G ( y j ) ≤ 0 or G ( y j ) ≥ 0. If we fix x 1 , . . . , x K and y 1 , . . . , y L , w e can think of C as just a con vex region of R K + L . T hen giv en an affine subsp ace S as defined by equation (1), we will (abusin g notation) write S ∈ C if the vec tor ( α 1 , . . . , α K , β 1 , . . . , β L ) is in C : that is, if S is compatible with the K + L in equ alities that define C . W e need to sho w that the ratio 27 Pr F [ C ] / Pr U [ C ] is close to 1. W e can do so u sing the previous r esult, as follo ws: Pr F [ C ] Pr U [ C ] = R S ∈ C F ′ ( S ) dS R S ∈ C U ′ ( S ) dS = R S ∈ C U ′ ( S ) h 1 ± O ( K + L )∆ S √ N i dS R S ∈ C U ′ ( S ) dS = R S ∈ C h e − ∆ S / 2 / √ 2 π K + L i h 1 ± O ( K + L )∆ S √ N i dS R S ∈ C h e − ∆ S / 2 / √ 2 π K + L i dS = (1 / 2) K + L ± O R S ∈ C h e − ∆ S / 2 / √ 2 π K + L i ( K + L )∆ S √ N dS (1 / 2) K + L = 1 ± 2 K + L ( K + L ) √ N O Z S ∈ C e − ∆ S / 2 √ 2 π K + L ∆ S dS ! = 1 ± K + L √ N O Z S e − ∆ S / 2 √ 2 π K + L ∆ S dS ! = 1 ± O ( K + L ) 2 √ N ! . Setting k := K + L , this completes the pro of. 5.2 Oracle Separation Results The follo wing lemma shows th at any almost k -wise ind ep end en t distribu tion is ind istinguishable from the un iform distribu tion by BPP path or SZK machines. Lemma 20 Supp ose a pr ob ability distribution D over or acle strings is 1 /t ( n ) -almost p oly ( n ) -wise indep endent, for some sup erp olynomial function t . Then no B PP path machine or SZ K pr oto c ol c an distinguish D fr om the uniform distribution U with non-ne gligi b le bias. Pro of. Let M b e a BPP path mac hine, and let p D b e the pr obabilit y that M accepts an oracle string dra wn from distr ibution D . Then p D can b e written as a D /s D , where s D is the fraction of M ’s computation paths that are p ostselected, and a D is the fraction of M ’s paths that are b oth p ostselected and acce pting. Since eac h computation p ath can examine at m ost p oly ( n ) b its and D is 1 /t ( n )-almost p oly ( n )-wise indep en den t, w e ha ve 1 − 1 t ( n ) ≤ a D a U ≤ 1 + 1 t ( n ) and 1 − 1 t ( n ) ≤ s D s U ≤ 1 + 1 t ( n ) . Hence 1 − 1 t ( n ) 2 ≤ a D /s D a U /s U ≤ 1 + 1 t ( n ) 2 . No w let P b e an S ZK proto col. Then b y a resu lt of Sahai and V adh an [31], there exist p olynomial-time samplable distrib u tions A and A ′ suc h that if P accepts, th en k A − A ′ k ≤ 1 / 3, 28 while if P rejects, then k A − A ′ k ≥ 2 / 3. But sin ce eac h computation path can examine at most p oly ( n ) oracle bits and D is 1 /t ( n )-almost p oly ( n )-wise indep end en t, we hav e k A D − A U k ≤ 1 /t ( n ) and k A ′ D − A ′ U k ≤ 1 /t ( n ), where the sub script denotes the distrib u tion from w hic h the oracle string w as drawn. Hence A D − A ′ D − A U − A ′ U ≤ k A D − A U k + A ′ D − A ′ U ≤ 2 t ( n ) and no SZ K proto col exists. W e n o w combine Lemma 20 and T heorem 19 w ith standard diagonalization tric ks, to obtain an oracle relativ e to w h ic h BQP 6⊂ B PP path and BQP 6⊂ S ZK . Theorem 21 Ther e exists an or acle A r elative to which BQP A 6⊂ BPP A path and BQP A 6⊂ SZK A . Pro of. The oracle A will enco de th e truth tables of Bo olean fun ctions f 1 , f 2 , . . . and g 1 , g 2 , . . . , where f n , g n : { 0 , 1 } n → {− 1 , 1 } are on n v ariables eac h. F or eac h n , with 1 / 2 probabilit y we dra w h f n , g n i from the u niform d istribution U , and with 1 / 2 probability w e dra w h f n , g n i from the forrelated d istribution F . Let L b e the un ary language consisting of all 0 n for which h f n , g n i was dra wn from F . By Theorem 9, there exists a BQP A mac hine M that decides L on all bu t finitely many v alues of n , with probabilit y 1 o ver A . Since w e can simply hard wire the v alues of n on which M fails, it follo ws that L ∈ BQP A with probability 1 o ver A . On th e other hand, we sho w ed in Theorem 19 that F is O p ( n ) 2 / 2 n/ 2 -almost p ( n )-wise indep en den t for all p olynomials p . Hence, by Lemma 20, no BPP path mac hine can d istinguish F from U with non-negligible b ias. Let E n ( M ) b e the even t that the BPP A path mac hine M correctly decides wh ether 0 n ∈ L . Then Pr A [ E n ( M )] ≤ 1 2 + o (1) , and moreov er this is tr ue eve n conditioning on E 1 ( M ) , . . . , E n − 1 ( M ). So as in the standard random oracle argument of Bennett and Gill [10], for ev ery fixed M we h a ve Pr A [ E 1 ( M ) ∧ E 2 ( M ) ∧ · · · ] = 0 . So by th e union b ound, Pr A [ ∃ M : E 1 ( M ) ∧ E 2 ( M ) ∧ · · · ] = 0 as well. It follo ws that BQP A 6⊂ BPP A path with p robabilit y 1 ov er A . By exactly the s ame argumen t, w e also get BQP A 6⊂ SZK A with probability 1 o ver A . Since BPP ⊆ MA ⊆ B PP path , T heorem 21 su p ers edes the pr evious results that there exist oracles A relativ e to w hic h BPP A 6 = BQP A [11] and B QP A 6⊂ MA A [38]. 6 The Generalized Linial-Nisan Conjecture In 1990, Linial and Nisan [28] f amously conjectured that “p olylogarithmic indep endence fo ols A C 0 ”—or lo osely sp eaking, that eve ry probability distrib ution D o v er n -bit str ings that is un iform on all s mall subsets of b its, is indistinguishable from the un iform distribu tion by p olynomial-size, 29 constan t-depth circuits. W e n ow state a v arian t of the Linial-Nisan Conjecture, not with the b est p ossible parameters but with weak er, easier-to-understand p arameters that suffice for our applica- tion. Conjecture 22 (Linial-Nisan Conjecture) L et D b e an n Ω(1) -wise indep endent distribution over { 0 , 1 } n , and let f : { 0 , 1 } n → { 0 , 1 } b e c ompute d by an A C 0 cir cuit of size 2 n o (1) and depth O (1) . Then Pr x ∼D [ f ( x )] − Pr x ∼U [ f ( x )] = o (1) . After sev ente en years of almost n o pr ogress, in 2007 Bazzi [7] fin ally p ro ved Conj ecture 22 for the sp ecial case of d epth-2 circuits (also called DNF formulas). Ba zzi’s pro of w as ab out 50 p ages, but it w as dr amatically s implified a y ear later, wh en Razb orov [30] disco v ered a 3-page pro of. Then in 2009, Bra v erman [13] ga ve a breakthrou gh pro of of the f ull Linial-Nisan Conjecture. Theorem 23 (Bra verman’s T he orem [13]) L et f : { 0 , 1 } n → { 0 , 1 } b e c ompute d by an AC 0 cir cuit of size S and depth d , and let D b e a log S ε 7 d 2 -wise indep e ndent distribution over { 0 , 1 } n . Then for al l sufficie ntly lar ge S , Pr x ∼D [ f ( x )] − Pr x ∼U [ f ( x )] ≤ ε. W e conjecture a mo dest-seeming extension of Bra v erman’s Th eorem, wh ic h sa ys (inf orm ally) that almost k -wise in dep end en t distr ib utions fo ol AC 0 as wel l. Conjecture 24 (Generalized Linial-Nisan or GLN Conjecture) L et D b e a 1 /n Ω(1) -almost n Ω(1) -wise i ndep endent distribution over { 0 , 1 } n , and let f : { 0 , 1 } n → { 0 , 1 } b e c ompute d by an A C 0 cir cuit of size 2 n o (1) and depth O (1) . Then Pr x ∼D [ f ( x )] − Pr x ∼U [ f ( x )] = o (1) . By the usual corresp ondence b et wee n A C 0 and PH , the GLN Conjecture immediately implies the follo w in g counte rpart of Lemma 20. Supp ose a pr ob ability distribution D over or acle strings is 1 /t ( n ) -almost p oly ( n ) -wise indep endent, for some sup erp olynomial function t . Then no PH machine c an distin- guish D fr om the uniform distribution U with non-ne gligible bias. And thus w e get the follo w ing imp lication: Theorem 25 Assuming the GLN Conje ctur e, ther e e xi sts an or acle A r e lative to which BQP A 6⊂ PH A . Pro of. Th e pro of is th e same as th at of Theorem 21; the only difference is that the GLN Conjecture no w pla ys the r ole of Lemma 20. Lik ewise: 30 Theorem 26 Assuming the GLN Conje ctur e for the sp e c ial c ase of depth- 2 cir cuits (i.e. , DN F formulas), ther e exists an or acle A r elative to which B QP A 6⊂ AM A . Pro of. Just like in Th eorem 21, defin e an oracle A and an asso ciated language L using the F ourier Checking p roblem. Then L ∈ BQP A , with p r obabilit y 1 o v er the choic es made in constructing A . On the other hand, supp ose L ∈ A M A with pr obabilit y 1 o v er A . T hen we claim that F ou rier Checking can also b e solv ed by a family of DNF formulas { ϕ n } n ≥ 1 of size 2 poly ( n ) : Pr h f ,g i∼F [ ϕ n ( f , g ) ] − Pr h f ,g i∼U [ ϕ n ( f , g ) ] = Ω (1) . But since F is O k 2 / 2 n/ 2 -almost k -wise indep en d en t (b y Theorem 19), suc h a family ϕ n w ould violate the d epth-2 case of the GLN Conj ecture. W e now pro ve the claim. F or simplicit y , fix an input length n , and let A refer to a single instance h f , g i of F ou rier Che cking . 11 Let P b e an AM proto col that su ccessfully distinguish es the forrelated distribution F ov er h f , g i p airs from the un iform distribution U . W e can assume without loss of generalit y that P is public- c oin [23]. In other words, Arth u r fi rst sends a rand om c hallenge r ∈ { 0 , 1 } poly ( n ) to Merlin, then Merlin r esp ond s with a witness w ∈ { 0 , 1 } poly ( n ) , then Arth ur runs a deterministic p olynomial-time ve rification pro cedure V A ( r , w ) to decide whether to accept. By th e assump tion that P succeeds, Pr A ∼D ,r ∃ w : V A ( r , w ) − Pr A ∼D ,r ∃ w : V A ( r , w ) = Ω (1) . So by Y ao’s pr inciple, there exists a fixe d c hallenge r ∗ suc h that Pr A ∼D ∃ w : V A ( r ∗ , w ) − Pr A ∼D ∃ w : V A ( r ∗ , w ) = Ω (1) . No w let Q A,w b e the set of all quer ies that V A ( r ∗ , w ) mak es to A , and let C A,w ( A ′ ) b e a term (i.e., a conjun ction of 1’s and 0’s) that r eturns T R UE if and only if A ′ agrees with A on all queries in Q A,w . T hen we can assume without loss of generalit y that C w := C A,w dep end s only on w , not on A —since Merlin can simp ly tel l Arth u r what queries V is going to mak e and what their outcomes will b e, and Arthur can r eject if Merlin is lying. Let W b e th e set of all w itnesses w suc h that Arth ur accepts if C w ( A ) returns TR UE. Consider the DNF formula ϕ ( A ) := _ w ∈ W C w ( A ) , whic h expresses that there exists a w causing V A ( r ∗ , w ) to acce pt. Then ϕ con tains at m ost 2 poly ( n ) terms with p oly ( n ) literals eac h, and Pr A ∼D [ ϕ ( A )] − Pr A ∼D [ ϕ ( A )] = Ω (1) . 11 It is straigh tforwa rd to generalize to th e case where Art hur can query oth er instances, b esides the one he is trying to solve. 31 As a side note, it is conceiv able that one could pro v e Pr x ∼D [ ϕ ( x )] − Pr x ∼U [ ϕ ( x )] = o (1 ) for ev ery almost k -wise in dep end en t distrib u tion D and sm all CNF form ula ϕ , w ithout getting the same resu lt for DNF form ulas (or vice v ersa). How ev er, since BQP is closed un der complemen t, ev en suc h an asymmetric result would imply an oracle A relativ e to wh ic h B QP A 6⊂ AM A . If the GLN Conjecture holds, then we can also “scale down by an exp onential, ” to obtain an unr elativize d decision problem that is solv able in quan tu m logarithmic time but not in A C 0 . Theorem 27 Assuming the GLN Conje ctur e, ther e exists a pr omise pr oblem in BQLOGTIME that is not in AC 0 . Pro of. In our pr omise p roblem Π = (Π YES , Π NO ), the inpu ts (of size M = 2 n +1 ) will enco de pairs of Bo olean fu nctions f , g : { 0 , 1 } n → {− 1 , 1 } , su c h that p ( f , g ) := 1 N 3 X x,y ∈{ 0 , 1 } n f ( x ) ( − 1) x · y g ( y ) 2 is either at least 0 . 05 or at most 0 . 01. The problem is to accept in the former case and r eject in the latter case. Using the algorithm FC-ALG from Section 3.2, it is immediate that Π ∈ BQLOGTIME . On the other hand, supp ose Π ∈ A C 0 . Then w e get a nonuniform circuit family { C n } n , of depth O (1) and size p oly ( M ) = 2 O ( n ) , that solv es F o urier Checking on all pairs h f , g i suc h that (i) p ( f , g ) ≤ 0 . 01 or (ii) p ( f , g ) ≥ 0 . 05. By Corollary 10 , the class (i) includes the o ve rwhelming ma jorit y of h f , g i ’s d ra wn f rom the u niform distribu tion U , while the class (ii) in clud es a constant fraction of h f , g i ’s drawn fr om the forr elated distribution F . Therefore, w e actually obtain an AC 0 circuit family that distinguishes U from F w ith constan t bias. But this con tradicts Theorem 19 together with th e GLN Conjecture. 6.1 Low-F at Polynomials Giv en that the GLN Conj ecture would ha v e su c h remark able imp lications f or quantum complexit y theory , the question arises of how w e can go ab out p ro vin g it. As w e are indebted to Louay Bazzi for p ointing out to u s, the GLN Con j ecture is e qu ivalent to th e follo wing conjecture, ab out appro ximating AC 0 functions by low-deg ree p olynomials. Conjecture 28 (Lo w- F at Sandwich Conjecture) F or every function f : { 0 , 1 } n → { 0 , 1 } c om- putable by an AC 0 cir cuit, ther e exist p olynomials p ℓ , p u : R n → R of de gr e e k = n o (1) that satisfy the fol lowing thr e e c onditions. (i) Sa ndwiching: p ℓ ( x ) ≤ f ( x ) ≤ p u ( x ) for al l x ∈ { 0 , 1 } n . (ii) L 1 -Appr oximation: E x ∼U [ p u ( x ) − p ℓ ( x )] = o (1) . (iii) L ow-F at: p ℓ ( x ) and p u ( x ) c an b e written as line ar c ombinations of terms, p ℓ ( x ) = P C α C C ( x ) and p u ( x ) = P C β C C ( x ) r esp e ctively, such that P C | α C | 2 −| C | = n o (1) and P C | β C | 2 −| C | = n o (1) . (Her e a term is a pr o duct of liter als of the form x i and 1 − x i .) 32 If we tak e out condition (iii), then Conjecture 28 b ecomes equiv alen t to the original Linial-Nisan Conjecture (see Bazzi [7] for a pro of ). And indeed, all progress so far on “Linial-Nisan problems” has crucially relied on this connection with p olynomials. Bazzi [7] and Razb oro v [30] p r o ved the depth-2 case of the LN Conjecture by constr u cting lo w-degree, appr oximati ng, sandwic hing p olynomials for ev ery DNF, while Brav erman [13] pr ov ed the full LN Conjecture b y constructing suc h p olynomials for every AC 0 circuit. 12 Giv en this history , p ro vin g Conjecture 28 wo uld seem lik e the “ob vious” app roac h to pr o ving the GLN Conjecture. Belo w w e pro ve one direction of the equiv alence: that to p ro ve the GLN Conjecture, it su ffices to constru ct lo w-fat sandwiching p olynomials for every AC 0 circuit. The other direction—that the GLN Conjecture imp lies Conjecture 28, and hence, there is no loss of generalit y in wo rking with p olynomials instead of p robabilit y distribu tions—follo ws from a linear p rogramming du alit y calculatio n that w e omit. Theorem 29 The L ow-F at Sandwich Conje ctur e implies the GLN Conje ctur e. Pro of. Giv en an AC 0 function f , let p ℓ , p u b e the lo w-fat sandwiching p olynomials of degree k that are guarantee d b y Conjecture 28. Also, let D b e an ε -almost k -wise indep endent distribution o ve r { 0 , 1 } n , for some ε = 1 /n Ω(1) . Th en Pr x ∼D [ f ( x )] − Pr x ∼U [ f ( x )] ≤ E D [ p u ] − E U [ p ℓ ] = X C β C E D [ C ] − E U [ p ℓ ] ≤ X C β C + | β C | ε 2 | C | − E U [ p ℓ ] = E U [ p u − p ℓ ] + ε X C | β C | 2 | C | = o (1) + n o (1) n Ω(1) = o (1) . Lik ewise, Pr x ∼U [ f ( x )] − Pr x ∼D [ f ( x )] ≤ E U [ p u ] − E D [ p ℓ ] = E U [ p u ] − X C α C E D [ C ] ≤ E U [ p u ] − X C α C − | α C | ε 2 | C | = E U [ p u − p ℓ ] + ε X C | α C | 2 | C | = o (1) . 12 Strictly sp eaking, Bra verma n constru ct ed approximating p olynomials with slightly different (though still suffi- cien t) prop erties. W e kn o w from Bazzi [7] t h at it must b e p ossible to get sandwic hing p olynomials as w ell. 33 7 Discussion W e no w tak e a step bac k, and use our r esults to add r ess s ome conceptual questions ab out the relativized BQP versus PH question, the GLN Conj ecture, and what m akes them so difficu lt. The first question is an ob vious one. Complexit y theorists ha ve kno wn for d ecades how to pro v e constant-depth circuit lo w er b ounds, and how to use those lo wer b ounds to giv e oracles A relativ e to wh ic h (for example) PP A 6⊂ PH A and ⊕ P A 6⊂ PH A . So why s h ould it b e so m uc h harder to giv e an A relativ e to whic h BQP A 6⊂ PH A ? What mak es this AC 0 lo wer b ound different from other AC 0 lo wer b ound s? The answer seems to b e that, while we ha ve p o werful tec hniqu es for pro ving th at a function f is not in A C 0 , al l of those te chniques, in one way or another, involve ar gu ing that f is not appr oximate d by a low-de gr e e p olynomial. T he Razb orov-Smolensky technique [29, 35] argues this explicitly , while even the random r estriction tec hn ique [16, 39, 36] argues it “implicitly ,” as shown b y Lin ial, Mansou r , and Nisan [27]. And this is a problem, if f is also computed b y an efficient quan tum algorithm. F or Beals et al. [8] pr ov ed the follo wing in 1998: Lemma 30 ([8]) Su pp ose a quantum algorithm Q makes T queries to a Bo ole an input X ∈ { 0 , 1 } N . Then Q ’s ac c eptanc e pr ob ability is a r e al multiline ar p olynomial p ( X ) , of de gr e e at most 2 T . In other words, if a fu nction f is in BQP , then for that ve ry reason, f has a lo w -degree appro x- imating p olynomial! As an example, we already sa w th at the follo win g p olynomial p , of degree 4, successfully distinguish es the forrelated d istribution F from the uniform distribu tion U : p ( f , g ) := 1 N 3 X x,y ∈{ 0 , 1 } n f ( x ) ( − 1) x · y g ( y ) 2 . (2) Therefore, w e cannot hop e to prov e a low er b ound for F ou rier Checking , by an y argument th at w ould also imply that suc h a p cannot exist. This br ings us to a second question. If (i) ev ery kno wn tec h n ique for proving f / ∈ A C 0 in volv es sh o win g th at f is not appro ximated by a lo w -d egree p olynomial, but (ii) ev ery function f with lo w quan tu m query complexit y is appro ximated by a lo w-degree p oly- nomial, do es that mean there is no h op e of s olving the relativized BQP v ersus PH problem u sing p olynomial- based tec hn iques? W e b eliev e the answe r is n o. Th e essen tial p oint here is that an AC 0 function can b e appro xi- mated by d ifferen t kinds of lo w -degree p olynomials. F or example, Linial, Mansour, and Nisan [27] sho wed that, if f : { 0 , 1 } n → { 0 , 1 } is in AC 0 , then there exists a real p olynomial p : R n → R , of degree p olylog n , s u c h that E x ∈{ 0 , 1 } n h ( p ( x ) − f ( x ) ) 2 i = o (1) . 34 By comparison, Razb oro v [29] and Smolensky [35] show ed th at if f ∈ AC 0 , then there exists a p olynomial p : F n → F o v er any field F (fin ite or infi n ite), of degree p olylog N , suc h that Pr x ∈{ 0 , 1 } n [ p ( x ) 6 = f ( x )] = o (1) . F u r thermore, to sh o w that f / ∈ AC 0 , it suffices to sho w that f is not appro x im ated by a low- degree p olynomial in any one of these sens es. F or example, even though the P ar ity function has degree 1 o ve r the fi nite field F 2 , Razb orov and Smolensky sh o wed that ov er other fields (such as F 3 ), an y degree- o ( √ n ) p olynomial disagrees with P arity on a large fraction of inputs—and that is enough to imply that P arity / ∈ AC 0 . In other w ords, we simply need to fi nd a typ e of p olynomial appr o ximation th at w orks for A C 0 circuits, bu t do es not w ork for the Fourier Checking problem. If true, Conjecture 28 (the Lo w-F at Sandw ich Conj ecture) pro vides exactly suc h a type of appro ximation. But this raises another question: what is the s ignificance of the “lo w-fat” requiremen t in Con- jecture 28? Wh y , of all things, do we wa n t our app ro ximating p olynomial p to b e expressible as a linear com bination of terms, p ( x ) = P C α C C ( x ), such that P C | α C | 2 −| C | = n o (1) ? The answer take s u s to the heart of wh at an oracle separation b etw een BQP and PH wo uld ha ve to accomplish. Notice that, although the p olynomial p from equation (2) solve d the Fourier Checking problem, it did so only by c anc el ling massive numb ers of p ositive and ne gative terms, then r epresen ting the ans w er by the tiny residue left o ver. Not coinciden tally , th is sort of cancella - tion is a cen tral feature of quan tum algorithms. By con trast, Th eorem 29 essentiall y sa ys that, if a p olynomial p do es not in volv e su c h massive cancellations, but is instead m ore “conserv ativ e” an d “reasonable” (lik e the p olynomials that arise fr om classical decision trees), then p cannot distin- guish almost k -wise ind ep end en t distributions from the uniform distribution, and therefore cannot solv e F ou rier Checking . If Conjecture 28 h olds, then ev ery small-depth circuit can b e appr o x- imated, not just b y an y lo w-degree p olynomial, but b y a “conserv ativ e,” “reasonable” lo w-degree p olynomial—one with a b ound on the coefficients that prev en ts massiv e cancellatio ns. Th is w ould pro v e th at F o urier Checking h as no small constant-depth circuits, and h ence that there exists an oracle separating BQP from PH . This brin gs us to the fourth and fi nal question: ho w might one pro v e Conjecture 28? In particular, is it p ossible that s ome tr ivial mo dification of Brav erman’s pr o of [13] would giv e lo w-fat sandwic hing p olynomials, thereb y establishing the GLN Conjecture? While we cannot rule this out, w e b eliev e that the answ er is no. F or examining Bra v erman’s pro of, we find th at it com b in es tw o kinds of p olynomial appr o ximations of A C 0 circuits: that of Linial-Mansour-Nisan [27], and that of Razb oro v [29] and Smolensky [35 ]. Un f ortunately , neither LMN nor R azb or ov-Smolensky gives anything like the c ontr ol over the appr oximating p olynomial’s c o efficie nts that Conje ctur e 28 demands. LMN simply tak es the F our ier transform of an AC 0 function and deletes th e h igh-order coefficients; w hile R azb oro v-Smolensky appro x im ates eac h OR gate b y a pr o duct of r andomly-c h osen linear fun ctions. Both tec hniqu es pr o duce approxima ting p olynomials with a huge num b er of monomials, and n o r easonable b ound on their coefficients. While it is conceiv able that those p olynomials satisfy the lo w-fat condition an ywa y—b ecause of some non-obvio us representat ion as a linear com bination of terms—certainly neither LMN nor Razb oro v-S molensky giv es any id ea what that representat ion w ould lo ok like. T h us, w e susp ect that, to get the d esired con trol o ver the co efficien ts, one will n eed more “constructiv e” p r o ofs of b oth the LMN and R azb oro v-Smolensky theorems. Suc h pro ofs w ould lik ely b e of great inte rest to circuit complexit y and computational learnin g theory for indep endent reasons. 35 8 Op en Problems First, of cours e, prov e the GLN Conjecture, or pro ve the existence of an oracle A relativ e to w hic h BQP A 6⊂ PH A b y some other means. A natural first s tep w ould b e to p ro ve th e GLN Conjecture for the sp ecial case of DNFs: as shown in Theorem 26, this would imply an oracle A relativ e to whic h BQP A 6⊂ AM A . W e ha ve offered a $200 pr ize for the PH case and a $100 pr ize for th e AM case. 13 Second, it would b e of in terest to pro v e the GLN Conj ecture for classes of f unctions w eak er than (or incomparable with) DNFs: for example, monotone DNFs, read-once formulas, and read- k -times form ulas. Third, can we giv e an example of a Bo olean f unction f : { 0 , 1 } n → { − 1 , 1 } that is w ell- appro ximated b y a lo w-degree p olynomial, but not by a lo w-degree lo w-fat p olynomial? Here is a more concrete version of the chall enge: let k f − p k := E x ∈{ 0 , 1 } n h ( f ( x ) − p ( x )) 2 i . Then find a Boolean fun ction f f or whic h (i) there exists a degree- n o (1) p olynomial p : R n → R such th at k f − p k = o (1), but (ii) there do es not exist a degree- n o (1) p olynomial q : R n → R suc h that k f − q k = o (1) and q can b e written as a linear com bination of terms, q ( x ) = P C α C C ( x ), with P C | α C | 2 −| C | = n o (1) . F our th , can w e give an oracle relativ e to wh ic h BQP 6⊂ IP ? What ab ou t an oracle relativ e to whic h BQP 6 = IP BQP , where IP BQP is the class of problems that admit an in teractiv e proto col with a BPP verifier and a BQP pro ver? 14 Fifth, what other implications do es the GLN Conjecture ha ve? If we assu me it, can w e ad d ress other longstanding op en questions in quantum complexit y th eory , s uc h as those d iscussed in Section 1.1? F or example, can we giv e an oracle relativ e to whic h NP ⊆ BQP but PH 6⊂ BQP , or an oracle relativ e to w h ic h NP ⊆ BQP and PH is infi nite? Sixth, ho w m u ch can we sa y ab out th e BQ P ve rsus PH question in the u nrelativized w orld? As one concrete c hallenge, can we find a non trivial w ay to “realize ” the F ou rier Checking oracle (in other words, an explicit compu tational problem th at is solv able using Fourier Chec king )? Sev enth, ho w far can th e gap b et wee n the s uccess probabilities of FBQP and FBPP PH algorithms b e impro ved? T heorem 15 ga v e a r elation f or wh ic h a quantum algorithm su cceeds with probabilit y 1 − c − n , whereas an y FBPP PH algorithm succeeds with probabilit y at most 0 . 99. By c h anging the success criterion for Fourier Fishing —basically , b y requirin g the classical algorithm to output z 1 , . . . , z n suc h that b f 1 ( z 1 ) 2 , . . . , b f n ( z n ) 2 are distr ibuted “almost exactly as they w ould b e in the quan tum algorithm”—one can improv e the 0 . 99 to 1 / 2 + ε for any ε > 0. How ev er, impr o ving the constan t further might require a direct pro du ct th eorem f or A C 0 circuits solving F our ier Fishing . 13 See http://scottaaronson.com/ blog/?p=381 14 If w e let the verifier transmit un entangle d q ubits to the prov er, then the resulting class IP | θ i BQP actually equals BQP , as recently sho wn by Broadb ent, Fitzsimons, and Kashefi [14] (see also Aharono v, Ben-Or, and Eban [4]). It is not known wheth er this IP | θ i BQP = BQP result relativizes; we conjecture that it do es not. 36 9 Ac kno wledgmen ts I thank Lou ay Bazzi for r eform u lating the GLN Conjecture as the Lo w-F at Sand wic h Conjecture; and Andy Druck er, Lance F ortno w, and Sash a Razb oro v for helpfu l discussions. References [1] S. Aaronson. Quan tum lo w er b ound for the collision prob lem. In Pr o c. ACM STOC , pages 635–6 42, 2002. quant- ph/0111102 . [2] S. Aaronson. Q u an tum lo we r b ound f or recursive Fourier samp ling. Quantum Informatio n and Computatio n , 3(2):165 –174, 2003. EC CC TR02-072, quant-ph/020 9060. [3] L. Ad leman, J. DeMarrais, and M.-D. Huang. Quan tum compu tabilit y . SIAM J . Comput. , 26(5): 1524– 1540, 1997. [4] D. Aharono v, M. Ben-Or, and E. Eban. I n teractiv e pro ofs for quan tum co mputations. arXiv:0810 .5375, 2008. [5] D. Aharono v, V. Jones, and Z. Land au . A p olynomial quantum algorithm for appr o ximating the Jones p olynomial. In Pr o c. ACM STOC , pages 427–436 , 2006. quan t-ph /05110 96. [6] Z. Bar-Y ossef, T. S . Ja yram, and I. Kerenidis. Exp onential separation of quantum and classical one-w ay comm unication complexit y . SIAM J. Comput. , 38(1): 366–3 84, 2008. C onference v ersion in ACM STOC 2004. ECCC TR04-036. [7] L. Bazzi. P olylogarithmic indep endence can fo ol DNF form ulas. In P r o c. IEE E FOCS , pages 63–73 , 2007. [8] R. Beals, H. Buhrman, R. Cleve, M. Mosca, an d R. de W olf. Quantum lo wer b ound s b y p olynomials. J . ACM , 48(4):778– 797, 2001. Earlier version in IEEE FOCS 1998, pp. 352-361. quan t-ph/98020 49. [9] C. Bennett, E. Bernstein, G. Brassard, and U. V azirani. Strengths and wea knesses of q u an tum computing. SIAM J. Comput. , 26(5) :1510– 1523, 1997 . quan t-ph/97010 01. [10] C. H. Bennett an d J. Gill. Relativ e to a random oracle A, P A 6 = N P A 6 = coN P A with probabilit y 1. SIAM J . Comput. , 10(1):9 6–113 , 1981. [11] E. Bernstein and U. V azirani. Quan tu m complexit y theory . SIAM J. Comput. , 26(5):141 1– 1473, 1997. First app eared in ACM STOC 1993. [12] R. B. Boppana, J. H ˚ astad, and S. Zac hos. Do es co-NP ha ve sh ort inte ractiv e pro ofs? Inform. Pr o c. L e tt. , 25:127– 132, 1987. [13] M. Brav erman. Poly-lo garithmic indep endence fo ols AC 0 circuits. In Pr o c. IEE E Confer enc e on Computationa l Complexity , pages 3–8, 2009. ECCC TR09-011. [14] A. Broadb en t, J. Fitz simons, and E. Kashefi . Univ ersal blind quan tum computation. arXiv:0807 .4154, 2008. 37 [15] C. Dask alakis, P . W. Goldb erg, and C. H. P apadimitriou. The complexit y of computing a Nash equilibrium. Commun. ACM , 52(2):8 9–97, 2009. Earlier ve rsion in Pro ceedings of S TOC’2006. [16] M. F urst, J. B. Saxe, and M. Sipser. P arit y , circu its, and the p olynomial time hierarc h y . M ath. Systems The ory , 17:13–27, 1984. [17] D. Ga vinsky . Classical inte raction cannot replace a quan tum message. In Pr o c. ACM STOC , pages 95–102, 2008. quan t-ph /0703215. [18] D. Ga vinsky . On the role of shared en tanglemen t. Quantum Information and Computation , 8(1-2) :82–95 , 2008 . quan t-ph /06040 52. [19] D. Ga vinsky . Pr edictiv e q u an tum learning. arXiv:0812.342 9, 2009. [20] D. Ga vinsky , J. Kemp e, I. Kerenidis, R. Raz, and R. de W olf. Exp onent ial sep aration f or one-w ay quan tum comm u nication complexit y , with applications to cryp tograph y . SIAM J. Comput. , 38(5):169 5–170 8, 2008. Earlier v ersion in ST OC’2007. quan t-ph/06112 09. [21] D. Ga vinsky , J. Kemp e, O . Regev, and R. d e W olf. Bounded-error quant um s tate iden tification and exp onen tial separations in communicatio n complexit y . In P r o c. ACM STO C , pages 594– 603, 2006. quant- ph/0511013 . [22] D. Ga vinsky and P . Pudl´ ak. E xp onential separation of quant um and classical n on -interact iv e m u lti-part y communicatio n complexit y . In Pr o c. IEEE Confer enc e on Computationa l Com- plexity , pages 332–339, 2008. arXiv:0708 .0859. [23] S. Goldw asser and M. S ipser. Priv ate coins v ersu s pu blic coins in in teractiv e p ro of systems. In R andomness and Computation , vo lu me 5 of A dvanc es in Computing R ese ar ch . JAI Press, 1989. [24] F. Green and R. Pruim . Relativize d separation of E QP from P N P . Inform. Pr o c. L ett. , 80(5): 257–2 60, 2001. [25] Y. Han, L. Hemaspaandra, and T. Thierauf. Threshold computation and cryptographic secu- rit y . SIAM J . Comput. , 26(1):59–7 8, 1997. [26] A. Kliv ans and D. v an Melk eb eek. Graph nonisomorphism has sub exp onential size pro ofs unless the p olynomial-time hierarc h y collapses. SIAM J. Comput. , 31:150 1–152 6, 2002. E arlier v ersion in ACM STOC 1999. [27] N. Linial, Y. Mansour, and N. Nisan. Constant depth circuits, Fourier transform, and learn- abilit y . J . ACM , 40(3):607–6 20, 1993. [28] N. Linial and N. Nisan. Appr oximate inclusion-exclusion. Combinatoric a , 10(4):3 49–36 5, 1990. Earlier version in STOC ’90. [29] A. A. Razb oro v. Lo w er b ounds f or the size of circuits of b ounded depth with basis { & , ⊕} . Mathematicheskie Zametki , 41(4): 598–6 07, 1987. English translation in Math. Notes. A c ad. Sci. USSR 41(4 ):333– 338, 1987. 38 [30] A. A. Razb oro v. A simple pro of of Bazzi’s theorem. A CM T r ans. on Computation The ory , 1(1), 2009. ECCC TR08-081 . [31] A. Sahai and S . V adh an. A complete pr omise pr oblem for statistical zero-kno w ledge. J. ACM , 50(2): 196–2 49, 2003. ECCC TR00-084. Earlier v ers ion in IEEE F OC S 1997. [32] A. S h amir. I P =PSP A C E. J. ACM , 39(4) :869–8 77, 1992 . [33] P . W. Sh or. P olynomial-time algorithms for p rime factorization and discrete logarithms on a quan tum computer. SIAM J. Comput. , 26(5):14 84–15 09, 1997. Earlier ve rsion in IEEE F OCS 1994. quant -ph/950802 7. [34] D. Simon. On the p ow er of quant um computation. In Pr o c . IEEE F O CS , p ages 116–123 , 1994. [35] R. Smolensky . Algebraic metho ds in the th eory of lo w er b ound s for Bo olean circuit complexit y . In Pr o c. ACM STOC , pages 77–82, 1987. [36] J. H ˚ astad. Computational Limitations f or Smal l Depth Cir cuits . MIT Press, 1987 . [37] E. Viola. On appro ximate ma jority and probabilistic time. In P r o c. IEE E Confer enc e on Computation al Complexity , pages 155–168, 2007. Journal version to app ear in C omputational Complexit y . [38] J. W atrous. Succinct quan tum pro ofs for prop erties of finite groups. In P r o c. IEE E FOCS , pages 537–546 , 2000. cs.CC/0009002. [39] A. C-C. Y ao. Separating th e p olynomial-time hierarc hy by oracles (preliminary v ersion). In Pr o c. IEEE FOCS , pages 1–10 , 1985. 39
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment