Multiple Cross-Layer Design Based Complete Architecture for Mobile Adhoc Networks
Different cross layer design for mobile adhoc network focuses on different optimization purpose, different Quality of Service (QoS) metric and the functions like delay, priority handling, security, etc. Existing cross layer designs provide individual…
Authors: R. Venkatachalam, A. Krishnan
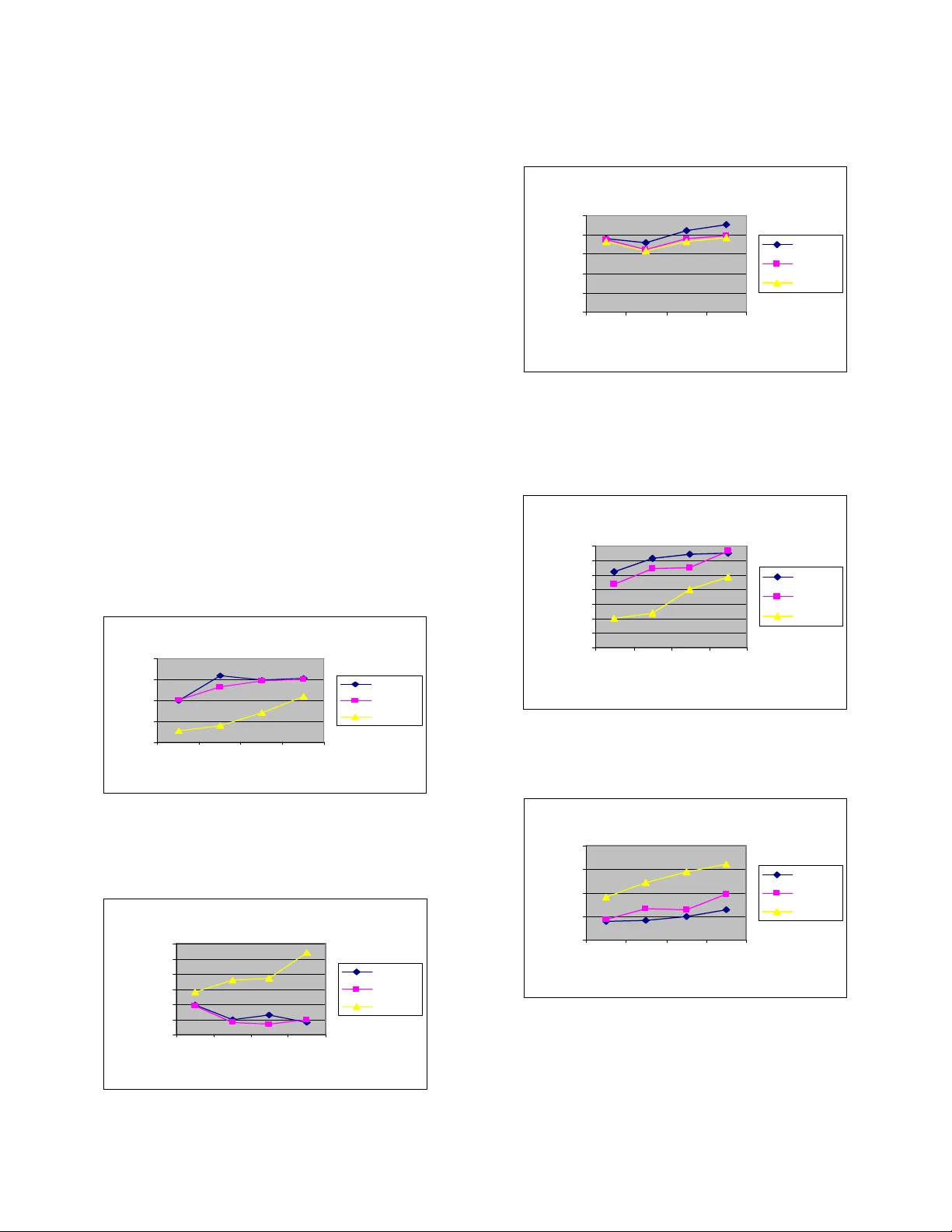
Multi ple Cross-Laye r Design Based Complet e Archit ecture for Mobile Adhoc Networks R.Venkatachalam Research Scho lar K.S.R Colle ge of Technolo gy, T iruchengode-637 215 Namakkal D istrict, Ta milnadu, I ndia Dr.A.Krishnan Dean K.S.R Colle ge of Engineer ing, T iruchengode-637 215 Namakkal D istrict, Ta milnadu, I ndia Abstract — Di fferent cr oss-layer design f or mobile adhoc network focuses on different op ti m ization purpose, different Quality of Service (QoS) metric and t he functions li ke delay, priority handling, security, etc. Existing cross-layer desig ns provide individual solutio n for congestion co ntrol, fault tolerance, power conservation, energy m inimization and flow control and the major draw back is of hig h c ost and overhead. In this pape r, we propose to design multiple cross-layer design based architecture to provide a combined solution for l ink f ailure manage ment, power conservation, congestion control and admission control. B y simulation results, we show that the average end-to-end delay, average energ y consu mp tion and t he pac ket loss ar e considerably reduced w ith the i ncrease i n hi gh thr oughput and good delivery ratio . Keywords: Cross-Layer; MANETs; end-to-end; Packet loss; Delivery ratio; con gestion control I. I NTRODUCTIO N A d-hoc net works a re multi-h op wireless network s where all nodes coop eratively maintain network connect ivity. T hese types o f net works ar e usef ul in situation where te mporary network con nectivity is needed. A mobile ad hoc net work (MANET) [1] is a group of mobile, wireles s nodes which coope ratively and spo ntaneousl y form a ne twork indep endent of any fixed infrastruct ure or c entralized ad ministratio n. Though the major m otivatio n of studying ad hoc networks comes f rom military usage, they w ill also be usef ul in any form of tactica l commun ications s uch as disaster recover y, exploratio ns, la w en forcements, and in various for ms of home and personal area networks. In order to provide communicatio n throug hout the network, t he mobile no des must c oopera te to handle net work functions, s uch a s pa cket routing. Routing is the most ac tive res earch field in mobile ad hoc networkin g. Mi nimizing the nu mber of hops is no lon ger the objective of a routing al gorithm, b ut rather the optimizatio n of multiple parameters such as packet err or r ate o ver t he route, energy co nsumption, net work survivab ility, ro uting overhea d, route setup a nd repa ir speed, p ossibility of e stablishin g parallel ro utes, etc. Man y routing pr otocols for mobile ad- hoc network have a ppeared recently [2] - [9]. A cr itical issue for M ANET s is that the activit y of nod es is po w er-constrai ned. Develop ing routing protocols for MANETs has be en an e xtensive research area during the p ast few years. In particu lar, energy efficien t routing may be the most important design criter ia for MANETs since mobile nodes will b e po w ered b y batteries with limited ca pacity. In o rder to achieve the desire d vertical opti mization goal, the use ful infor mation i s inter -communicated by t he di fferent layers of the network pro tocol stack which is consid ered as cross-layer o r inter-layer netwo rking. The req uirements o f the quality of ser vice may vary with applic ations and hence the network or higher layer s functio n s hould dire ctly rel y o n the information from the lower p hysical and MA C layers. Different la yers c an share l ocally a vailable i nformation by using interla yer interaction. This will si gnificantly improve the performance . There are m any cross-la yer designs for d ifferent op timization p urpose. D ifferent cr oss-layer design focuse s on different opti mization purpos e, different QoS metric, one o r more of t he follo wings: d elay, p riority handlin g, securit y, etc. Obviousl y every s ystem needs more than one cross -layer design to a chieve overall QoS o ptimization . A. Prob lems of th e Existing System A rchitecture o f Cr oss- layer Design s • Only t he lo cal li nk informatio n from it s M AC la yer is used by the congestio n avoidance algorit hm. T he local information is inad equate to replicate the net work situation if the whole ne twork is u nstable. • In general the cro ss-layer designs involve the combinatio n of la yers p hysic al-MAC-net work, M AC- network, Network-T ransport only. But, there is no work made o n complete i ntegration o f MAC-Net work- Transpo rt layers. • The cross-layer d esigns pr ovide individual so lution for congestion contro l, fault tolerance, power conservatio n, energ y minimiz ation and flow contro l. There is no complete and combined solutio n for the above issues. • Expensive a nd High O verhead In this paper, w e p ropose t o de sign multiple cro ss-layer based designs architect ure to pr ovide a co mbined solutio n for (IJCSIS) International Journal of Computer Science and Information Security, Vol. 5, No. 1, 2009 182 http://sites.google.com/site/ijcsis/ ISSN 1947-5500 link failure mana gement, po wer co nservation, con gestion control and admission contro l. The p aper is organized as follo ws. Sec tion 2 p resents the related work done. Section 3 pr esents a detaile d descr iption of our prop osed architecture . Se ction 4 pr esents the si mulation results and co nclusion is given in Sectio n 5. II. R ELATED W ORK Tom Goff et al. [11 ] have investigate d adding pr oactive route selec tion and maintena nce to on-demand ad -hoc ro uting algorithms. Mor e specifical ly, when a path was l ikely to b e broken, a warning has sent to the sourc e i ndicating the likelihood of a disconnectio n. The source was then initiate path discovery early, potentiall y a voiding the d isconnec tion altogether. Hong-Peng W ang a nd Lin Cui [12 ] have d iscussed that the need for a n e fficient routi ng p rotoco l in mobile ad ho c network has widely pr oclaim ed. T heir work has p resented an enhanced AODV p rotoco l, a sche me to make mobile no des more aware of t he local connecti vity to its neighbors in the network. Their scheme has extended the original HELLO message i n AODV but with lo wer o verhead. At the sa me ti me it has pre vented the po tential unidir ectional lin ks i n the network to so me extent. PremaLatha et al. [ 13] have discus sed that in mobile ad hoc wireless networks, multiple mobile statio ns has communicated without the support of a centralized coord ination station for the sc heduling of transmissio ns. Th eir study has deal a co mbination of medium ac cess cont rol proced ure employing d istributed coo rdination function and suitable tr ansport layer mechanism which has improved QoS guarantee in T ransport layer . In their propo sed method , IEEE8 02.11e and Adap tive Incr ease M ultiplicative Decre ase (AIMD) mechanism have b een combined to anal yze t he quality of serv ice in cross la yer. RamaChandra n and Shanmu gaVel [14] have discu ssed tha t in fourth generatio n ( 4G) wireless net works and beyond, it is strongly a nticipated that m obile ad hoc net works a re used to econo mically e xtend their cover age and capacity. In the ir work, they have pr oposed a nd studied three cro ss-layer designs a mong ph ysical, medium acc ess co ntrol and ro uting (network) la yers, u sing Rece ived Sig nal Strength ( RSS) as cross-layer interactio n p arameter for energy conservat ion, unidirectio nal link rejection and reliab le route formation in mobile ad hoc networks. Lijun Chen et al. [15] have considered jointl y opti mal design of cross-layer congestio n control, routing and scheduling for ad hoc wireless net w orks. T hey have first formulated the r ate co nstraint and sc heduling co nstraint u sing multi-co mmodity flow vari ables, and for mulate resour ce allocation in network s with fixed wireless c hannels as a util ity maximization prob lem w ith these constraints. By dual decompositio n, t he reso urce allocation proble m has naturall y decomposed into three s ub prob lems: con gestion cont rol, routing and sc heduling tha t interact through congest ion price. Xinsheng Xia et al. [16] have introduced a method for cross-layer design in mobile ad hoc networks. The y have us ed fuzzy lo gic s ystem (F LS) to co ordinate physical layer, d ata link la yer and ap plicatio n laye r for c ross-layer d esign. G round speed, average dela y and pack ets success ful trans mission rat io are selected as a ntecedents for the FLS. T he outp ut o f F LS has provided adjusting factors for the AMC ( Adaptive Mod ulatio n and Codin g), transmi ssion po wer, retransmis sion ti mes and rate contro l decision. A.n. a l-khwildi, S. k han et al [ 17] pr oposes a novel routing technique called Adaptive Link-Wei ght ( ALW) routing pro tocol. ALW adapti vely selec ts an op timum ro ute on the basis of available bandwidth, low dela y and long r oute lifetime. T he technique adapts a cro ss-layer fra mework wh ere the ALW is i ntegrated with app lication and ph ysical la yer. The proposed design a llows ap plications to co nvey p references to the ALW proto col to override the de fault pa th select ion mechanis m. B. RamaChandran and S. Shanmugavel [18] proposed a simple cross la yer de sign be tween p hysical (P HY) and Medium Access Contro l (MAC) layers for power c onservati on based on trans mission po wer co ntrol. T he Carrier Sense Multiple A ccess w ith Collision Avoid ance (C SMA/CA) mechanis m o f I EEE 802.11 Wireless Local Area Net work (WLAN) standard is integrated with the p ower control algorithm. In t his metho d, the exchange o f RTS/CT S contr ol signals is used to piggyb ack the necessary in formation to enable the trans mitting nod es to discover the r equired minimum a mount o f po wer that is needed to tr ansmit t heir data pa ckets. III. P ROPOSED MCBA D ESIGN A. Overview In this paper, w e p ropose t o design mu ltiple cross-layer based designs architect ure to pr ovide a co mbined solutio n for link failure mana gement, po wer co nservation, con gestion control and admission contro l. 1) Link Failure Ma nagement : Usin g the received signal strength from physical laye r, link quality ca n be predicte d and links wit h low signal s trength will b e discarded from the route sele ction. 2) Power Conservat ion: Using the M AC layer RTS/CT S pac kets excha nge, the minimum r equired po w er can be estimated and accordingly the sender can adj ust its transmittin g power. 3) Congestion Control : From the MAC layer, contention and cha nnel in terference of the nodes c an be estimated and noti fied to the applicatio n la yer. Based on t hese e stimatio ns, at the app lication la yer, the tr ansmission rate ca n be adjusted, to avoid congestion. 4) Admission Contro l : From the phys ical layer, t he bandwidth ca pacity o f t he no des c an be estimated. Using this infor mation, an admission co ntrol mechanis m at the M AC layer, adm its or rejects the flows accord ing to their r equested bandwidth. (IJCSIS) International Journal of Computer Science and Information Security, Vol. 5, No. 1, 2009 183 http://sites.google.com/site/ijcsis/ ISSN 1947-5500 Figure.1 Cross-Lay er Architecture B. Link F ailure Man agement The link q uality ca n be p redicted b y means of t he received signal strengt h from physica l layer and the lin ks with lo w signal stren gth will be d iscarded from the route se lection. The re ceived signal strengt h in cros s layer de signs is calculated at the physical la yer and it ca n be ac cessed at the top layers a s shown in t he figure 1.T he m easured value of received signal stre ngth will be transferred to the M AC layer along with t he signal [ 15]. The p rocedures a t physical la yers have to b e perso nalized. This value in M AC la yer calc ulations is used if required o r to pass the ro uting layers alo ng with the routing contro l p ackets. This value is sto red in the routing/neig hbour tables and it is a lso used in so me of the decision making proc ess. As an interla yer inter action parameter, the re ceived signal strengt h whic h is re lated to the physical layer is passed to the top layers. T he re ceived signal strength improves the p erfor mance of the mo bile ad ho c networks b y adj usting the medium access a nd routing proto cols as per the required cross layer design, The IEEE 802.11 is reliable M AC proto col. Since the received signal strengt h must reach ever y exposed node, it assumes the fixed m aximum transmissio n po wer. Whe n a sending no de transmits RTS packet, it attaches its transmission s po wer. T he r eceiving no de mea sures the sig nal strength rece ived for free–s pace pro pagation model while receiving t he RTS pac ket [15]. R T T R G G d P P 2 ) 4 / ( π λ = (1) Where λ wavelength of carrier, d is distance betwee n sender and rec eiver. T G and R G are unity gai n o f transmittin g a nd receivin g omni directiona l antenn as, respectivel y C. Power Con servation Using the M AC la yer RT S/CTS packets exchange, the minimum required power ca n be esti mated and acc ordingl y the sender can adjust its tra nsmittin g power. The re ceiving node calc ulates the path lo ss experienced as, R P Path − = T P loss (2) The node then c alculate s the mini mum required transmission p ower ) ( min T P as, ) R loss ( * TH min + = path k P T (3) Where TH R is rec eiver thresho ld , the mi nimum require d po w er required for proper signal detec tion. The multiplica tion factor “ k ” is considered to pro vide marginal hike i n minimum required transmissi on power to withsta nd against the effect o f interference o n packet r eception. In our cross-layer desig n, based on the type number at MAC layer the RRE P packet is ac knowledged and fro m PHY layer the r eceived si gnal s trength i nformation is o btained and is passed to routing layer. He nce, the pa th loss exp erienced by the packet is calc ulated by the no des that r eceives AODV’s RREP pac ket and the minimum req uired transmi ssion po wer is computed using the eq uatio ns (2 ) and ( 3).The min T P is stored in the routing tab le with the ne xt hop a gainst the destination. In orde r to get the minimu m req uired transmi ssion po w er in cross-la yer desi gn, the node sending RTS has to refer the ro uting table. It t unes it’s transmit power to this value and also inserts this val ue in R TS as e xtra field so that t he receiving node can tu ne to t his p ower while se nding i ts CT S packet. Subsequen tly b y usi ng the req uired minimum transmit po w er level, the da ta packet from the se nder and ACK pac ket from the recei ver c an also be transmitted. T his scheme clear ly reflects the cr oss-layer intera ction among PHY -MAC – Routing la yers. D. Cong estion Con trol From the M AC layer, conte ntion and channel inter ference of the nodes ca n be e stimated and notified to the applic ation layer. Based on these esti mations, at the ap plication la yer, the transmission ra te can b e adjusted , to avoid congestion. In this network, we consid er IEEE 8 02.11 MAC with the distributed coord ination func tion (DCF). It has the packet sequence as request -to-send (RT S), clear-to-send (CT S), and data, ackno wledge ( ACK). The a mount o f time bet ween the receipt of one pa cket and t he t ransmissio n o f the next i s ca lled a shor t i nter frame space (SIFS). T hen the channel occup ation due to MAC contention will be SIFS CTS RTS occ t t t C 3 + + = (4) Where RTS t and CTS t are the time consumed on RTS and CTS, r espectively and SIFS t is the SIFS p eriod. Then the M AC overhead MAC OH can be r epresented a s acc occ MAC t C OH + = (5) Where acc t is the time taken d ue to access contentio n. The amount o f M AC over head is mai nly d ependent upon the medium access co ntention, and the number o f pa cket (IJCSIS) International Journal of Computer Science and Information Security, Vol. 5, No. 1, 2009 184 http://sites.google.com/site/ijcsis/ ISSN 1947-5500 collisions. That is, MAC OH is stro ngly re lated to the congestion aro und a given node. MAC OH ca n exceed t hreshold value rh T , if co ngestion is incurr ed a nd not contro lled, and it can dra matically decr ease the capacit y of a congested link. The channel resource S ∆ can be ca lculated as, S OH OH T S MAC MAC rh × − = ∆ ) ( (6) Where S is the curre nt traffic lo ad If rh M AC T OH < , then S ∆ will be p ositive and If rh MAC T OH > , then S ∆ will be negati ve. The transmission rate rt is d ynamically adjusted accord ing to the explicit feedback fd . Namel y, fd rt rt + = (7) If S ∆ is positive, the n the trans mission rate rt will be increased as, S rt rt ∆ + = and if S ∆ is ne gative, then the tr ansmission rate rt will b e reduced as, S rt r t ∆ − = Thus the tra ffic r ate is adap tivel y adj usted accord ing to the MAC conte ntion. E. Adm ission Control From the ph ysical layer, the b andwidth capacit y of the nodes can be estimated . U sing this infor mation, a n a dmissi on control m echanism at the MAC layer, ad mits or rejects the flows accord ing to their r equested bandwidth. In t he band width estimation method , the sender ’s current bandwidth usage a s well as the se nder’s one-hop neighbors’ current ba ndwidth usage is cred ited onto the sta ndard “Hello ” message. Each host esti mates its feasible band width based on the infor mation pro vided in t he “Hello” message s and knowledge of the frequency reuse patter n. T his app roach avoids creati ng extra c ontrol messages b y using the “Hello ” messages to d isseminate the b andwidth in formation. Ever y host esti mates its occ upied ba ndwidth by scru tinizing the packets it pro vides into the network. A b and width utilization register recor ds the value at the host and upda tes periodicall y. We modi fy t he “Hello” m essage to include two fields. T he initial field include s host addre ss, consumed band width, timestamp, and the second field includes neighbo rs’ addr esses, consumed b andwidth, ti mesta mp. The ho st receive s a “Hell o” message fro m i ts neighbor s, and concludes whether t his “Hello” i s a restruct ured one by exa mining the message’s timestamp. Once a host knows the band width co nsumption of it s firs t neighbors and its second neighbors, the feasible band width FBW is e stimated as ) / ( WT UBW CHBW FBW − = (8) Where, CHBW - channel bandwidth, UBW - used o r consumed b andwidth, W T - w eight facto r, RBW -required bandwidth, M inBW -Mi nimum B and width, MaxBW - Maximum Ba ndwidth Algorith m Step 1: If RBW FBW < , the source nod e will be rejected, else it further c hecks the required b and width Step 2 : If MinBW RBW < , the flo w can be admitted. Step 3 : If MaxBW RBW > , the flo w is rejected. Step 4 : If MaxBW RBW MinBW < > , a pro bing packet is sent to th e destina tion nod e to obtain the F BW at t he destinatio n. IV. S I MULATION M ODEL AND P ARA METERS We use NS2 to simula te o ur p roposed p rotocol in our simulation, the c hannel capac ity o f mobile hosts is set to t he same val ue: 2 Mbp s. We use the distributed co ordinati on function (DCF) of IEE E 8 02.11 for wireless LANs as the MAC la yer p rotoco l. It has the functionality to notify the network la yer about link b reakage. In our simulation, 5 0 mob ile no des move i n a 150 0 meter x 500 meter rectang ular re gion for 100 seco nds simulatio n ti me. We assume each node moves independently with th e same average speed. All nodes have the same transmissio n ran ge of 250 meters. In o ur simulation, the speed is set as 5m/s. T he simulated tr affic is Co nstant B it Rate (CB R). T he pause time of the mobile node is varied as 0 ,10,20,30 and 40. Our simula tion settin gs and p arameters ar e summariz ed in table I. T ABLE I. S IMULATION S ETT INGS No. of No des 25,50,7 5 and 100 Area Size 1500 X 500 Mac 802.11 Radio Range 250m Simulation T ime 100 sec Traffic Sourc e CBR Packet Size 512 Mobilit y Model Random Wa y Point Speed 5m/s Pause time 10 Receiving P ower 0.395 W Trans mit Power 0.660 W Idle Po wer 0.035 W Initial Ener gy 4.7 J (IJCSIS) International Journal of Computer Science and Information Security, Vol. 5, No. 1, 2009 185 http://sites.google.com/site/ijcsis/ ISSN 1947-5500 A. Performa nce Metrics We compare o ur MCB A pr otocol with t he AOMD V [ 2] and AODV [6] p rotoco ls . We evaluate mainl y the performance accordin g to the following m etrics, b y var ying the number of nodes as 2 5, 50, 75 and 100. Control ove rhead: T he c ontrol overhead is de fined as t he total number o f routi ng contro l pac kets nor malized b y the to tal number of received d ata packets. It occurs while es timating the metrics for Link failure management, P ower Conservati on, Congestion control, Admissio n contro l a nd exc hanging these metrics amon g differe nt layers. Averag e end-to-e nd dela y: The e nd-to-end-delay i s averaged over all survivi ng d ata pa ckets fro m the sources to the destinatio ns. Averag e Pa cket Deliv ery Ratio: I t is t he ratio o f t he number o f packets received succes sfully and the to tal nu mber of packets se nt Throughput : It is t he number o f packet s received successfull y. Drop: I t is the number of p ackets dro pped Averag e Energy: It is the average energy consu mption of all nodes in se nding, recei ving and forward ope rations B. Results Based On Nu mber of No des In this e xperiment, we var y the n umber of nod es as 25 , 50, 75 and 100 N od e s V s D e lay 0 2 4 6 8 25 50 75 100 N od e s D e l a y (s e c ) A OD V A OM D V M C BA Figure 2. Nodes Vs Del a y Figure 2, re presents that the average end-to-e nd delay of the p roposed MCB A proto col is ver y les s when co mpared to AOMDV and AODV pr otocol. N od e s V s Thr o ug hp ut 0 500 1000 1500 2000 2500 3000 25 50 75 100 N od e s T h r o u g h p u t A OD V A OM D V M C B A Figure 3. Nodes Vs Throug h put Figure 3 give s t he throug hput of all the pr otocols when t he number o f node s is incre ased. As we can see from the fig ure, the t hroughput is more i n the case o f MCB A, t han AOMDV and AODV. N od e s V s E ne r g y 0 0.5 1 1.5 2 2.5 25 50 75 100 N od e s E ne r gy A OD V A OM D V M C BA Figure 4. Nodes Vs Energ y Figure 4 shows the r esults of energy co nsumption. From the res ults, w e can see th at M CBA protoco l has less energy than the AOMDV and AODV protocols, since it has the energ y efficient routi ng N od e s V s D r op 0 1000 2000 3000 4000 5000 6000 7000 25 5 0 75 100 N od e s D ro p A OD V A OM D V M C BA Figure 5. Nodes Vs Drop Figure 5 ensures that the packets dropp ed in MCBA are less when co mpared to A ODV and AOMDV. N od e s V s D e lR atio 0 0.2 0.4 0.6 0.8 25 50 75 100 N od e s D e lR a tio A OD V A OM D V M C B A Figure 6. Nodes Vs Del R atio Figure 6 prese nts t he packe t d elivery ra tio of both AODV and AOMDV pr otocols in compari son with MCB A pr otocol. Since t he pa cket dr op is les s and t he thro ughput i s mor e, (IJCSIS) International Journal of Computer Science and Information Security, Vol. 5, No. 1, 2009 186 http://sites.google.com/site/ijcsis/ ISSN 1947-5500 MCBA a chieves good d elivery ratio , c ompared to AOMDV and AODV. V. C ONCLUSION In this paper , we have d esigned multip le cro ss-layer de sign based a rchitecture to provid e a co mbined sol ution for link failure management, power conservatio n, con gestion control and ad mission contro l. The link qual ity can b e predicte d by means of the r eceived signal strength from p hysical la yer a nd the links with lo w si gnal strength will be disca rded fro m the route selectio n. Using t he MAC la yer RTS/CT S pack ets exchange, the min imum requir ed power c an be esti mated and accord ingly the sender can adjust its tra nsmitting po wer. From the MAC layer, contention and chan nel interference of the nodes can be estimated and notified to the a pplication la yer. Based on these est imations, at the applicatio n la yer, t he transmission rate ca n be ad justed, to avoid congestion. Fro m the p hysical la yer, the band width capa city o f the nodes ca n b e estimated. Using this informatio n, a n ad mission c ontr ol mechanis m at t he M AC la yer, a dmits or rejects the flows accord ing to their requested band width. By simulatio n res ults, we have shown that the average end-to-end dela y, average energy c onsumption and the packet loss are consider ably reduced with the increase in hi gh throughput and good delivery ratio . R EFERENCES [1] Douglas S. J. De Cou to,Daniel Aguayo,Benjamin A. and Chamb ers Robert M orris,” Effects of Loss Rate on Ad Hoc Wireless Routing” in Parallel and Distributed Operating Sy st ems Group, MIT Laboratory for Computer Science., 8 March 2002. [2] Mahesh K.Marina and Samir R.Das, “On demand mutip ath distance vector routing in Ad hoc Ne tworks”. [3] Lei Chen and Wendi B. Heinzelman, “QoS-Aware Routing Based on Bandwidth Estimation for Mobile Ad Hoc Networks” on IEEE Journal On Selected Areas I n Communications, VOL . 23, NO. 3 March 2005. [4] S. Mahlknecht, S. A. Ma dani and M. Roetzer, “Energy Aware Dista nce Vector Routing Scheme for Dat a Centric Low Power Wireless Sensor Networks” [5] Jit endra Padhye, Sharad Agarw al, V enkata N. Padmanabhan, Lili Qiu, Ananth Rao, Brian Zill, “Estimation of L i nk I n terference in Static Multi - hop Wireless Ne t works”. [6] Charles E.Perkins and Elizabeth M.Royer, “Ad-hoc On -Demand Distance Vector Routing”. [7] David B. Johnson and David A. Maltz,” Dynamic Source Routing in Ad Hoc Wireless Networks” in a ve rsion of thi s paper will app ear as a chapter in the book M obile Computing, edited by Tomasz Imielinski and Hank Korth,Kl uwer Academic Publishers, 1996. [8] Charles E.Perkins and Pravin Bhagw a t,”Highly Dynamic Destination- Sequenced Distance Vector Rou ting (DSDV ) for Mobile Computers” [9] Vin cent D. Park and M. Sc ott Corson,” A Highly Adaptive Distributed Routing Algo rithm f or Mobile Wireless Ne t works” [10] Jin yang Li,Charles Blake,Douglas S. J. De Couto,Hu Imm Lee a nd Robert Morris,” Capacity of Ad Hoc W i reless Networks” [11] Tom G o ff, Nael B. Abu-Ghazal eh, Dhananjay S. Phatak and Ridvan Kahveciogl u, "Preemptive Routing in Ad Hoc Networks" Journal of Parallel and Distributed Comp uting, Vol . 63,No.2,pp.123-140,2003. [12] Hong-Peng Wang and Lin Cui, "An Enhanced AODV For M obile Ad Hoc Network" in proceedings of International conference on Machine Learning and Cybernatics, Vo l.2, pp.1135-1140,20 0 8. [13] PremaLatha, BalaSubramanie and Venkatesh, "C ross Layer D esign to Improve QoS i n Ad Hoc Networks", Journal of M obile Communication, Vol.2, No.2, pp.52-58, 2 008. [14] Ra maChandran and ShanmugaVel, "Received Signal Strength-based cross-layer designs for Mobile ad hoc networks", IETE T echnical Review, Vol.25, No.4, pp. 192-200, 2009. [15] Lijun Chen, Steven H. Low, M ung Chiang and John C. Doyle , "Cross- layer C ongestion Control, Routin g and S cheduling Design in Ad Hoc Wireless Networks", in proceedings of 25th IEEE I nternational Conference on Computer Communications, pp.1-13, April 2006. [16] Xin sheng Xia, Qingchun Ren and Qilian L i ang, "Cross-Layer Design for Mobile A d Hoc Networks: En ergy , Throughput and Del ay-Aware Approach", in proceedings of IEEE conference on Wireless Communications and Netw orkin g, Vol . 2, pp.770-775, 2006. [17] A.N. Al-khw ildi, S. khan, k.k. loo , H.S. al-Raweshidy,” Adaptive L ink- Weight Routing Protocol using Cross-Layer Communication for MANET”, I SSN: 1109-2742, Issue 11, Vol ume 6, November 2007. [18] B. RamaChandran and S. Shanmuga vel “A Po wer Conservative Cross- Layer Design for Mobile Adhoc Network”, ISSN: 1 812-5638, Information Technology Journ al 4(2) 125-13 1, 2005. A UTHORS P ROFILE R.Venkatachalam received the MCA degree from the Bharathidasan University, Tiruchirappalli, Tamiln adu, I nd ia, in 1995. He is currently a research scholar in K.S.R. C oll ege of Technology , Tiruch engode, Tamilnadu, India. He has passed UGC-NET exam in Computer Science and Applications in June 2006. He has published 7 papers in the national c onfer ence proceedings. His research interests include mobile adhoc networks and mobile communications. He is a life member of t he Computer Society of I n dia (CSI) and Indian Society for Technical Education (I S TE). Dr. A. Kri shnan received the PhD degre e from th e I n dian I n stitute of Technology (IIT) Kanpur, India, in 1979. He is currently Dean, K.S.R. College of Engineering, Tiruchengode, Tamilnadu, India. His research interests in clude control systems and computer networks. He is a senior member of the IEEE, Computer Society of India (CSI) and Indian Society for Technical Education (I S TE). (IJCSIS) International Journal of Computer Science and Information Security, Vol. 5, No. 1, 2009 187 http://sites.google.com/site/ijcsis/ ISSN 1947-5500
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment