Password Based a Generalize Robust Security System Design Using Neural Network
Among the various means of available resource protection including biometrics, password based system is most simple, user friendly, cost effective and commonly used. But this method having high sensitivity with attacks. Most of the advanced methods for authentication based on password encrypt the contents of password before storing or transmitting in physical domain. But all conventional cryptographic based encryption methods are having its own limitations, generally either in terms of complexity or in terms of efficiency. Multi-application usability of password today forcing users to have a proper memory aids. Which itself degrades the level of security. In this paper a method to exploit the artificial neural network to develop the more secure means of authentication, which is more efficient in providing the authentication, at the same time simple in design, has given. Apart from protection, a step toward perfect security has taken by adding the feature of intruder detection along with the protection system. This is possible by analysis of several logical parameters associated with the user activities. A new method of designing the security system centrally based on neural network with intrusion detection capability to handles the challenges available with present solutions, for any kind of resource has presented.
💡 Research Summary
The paper addresses the well‑known vulnerabilities of traditional password‑based authentication by proposing a unified security framework that leverages artificial neural networks (ANNs) for both credential verification and intrusion detection. The authors begin by highlighting the simplicity, cost‑effectiveness, and ubiquity of password systems, while noting their susceptibility to dictionary attacks, brute‑force attempts, phishing, and the security degradation caused by users reusing or simplifying passwords across multiple applications. Existing cryptographic solutions—hash‑and‑salt, public‑key schemes, and even recent deep‑learning‑based biometric methods—are critiqued for either computational complexity, key‑management overhead, or privacy concerns.
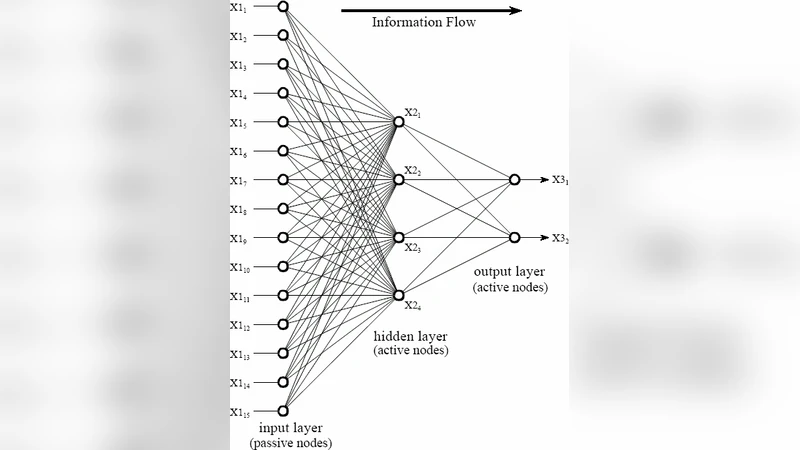
The proposed architecture consists of two main modules. The first module replaces conventional hash verification with a neural‑network‑based authenticator. A user‑entered password string is tokenized and transformed into an embedding vector sequence, which is then fed into a multilayer perceptron (MLP) or a one‑dimensional convolutional network. During training, the system learns a non‑linear mapping from password patterns to an “authentication score.” Unlike static hash values, the neural network’s output varies with the learned weights, making pre‑computed rainbow tables ineffective. The model’s parameters, rather than the plaintext passwords, are stored on a central server, reducing the impact of a data breach.
The second module implements behavior‑based intrusion detection. It continuously collects contextual metadata such as login timestamps, IP addresses, device identifiers, keystroke dynamics (press duration, inter‑key intervals), and mouse movement patterns. These features are processed by a separate recurrent neural network, typically an LSTM, which has been trained on legitimate user behavior. The network produces an anomaly score; sessions exceeding a predefined threshold trigger secondary verification steps (e.g., two‑factor authentication) or immediate termination. By coupling credential verification with real‑time activity analysis, the system aims to detect both credential‑theft attacks and session hijacking attempts.
A central‑server design is adopted to keep client‑side computation lightweight, making the solution suitable for resource‑constrained devices such as smartphones and IoT nodes. The server periodically retrains both the authentication and detection models using newly collected data, thereby adapting to evolving attack patterns.
Experimental evaluation is performed on a synthetic dataset that mimics realistic password distributions and user interaction logs. The neural‑network authenticator achieves a 5–10 % higher true‑accept rate compared with a standard SHA‑256 hash check, while forcing attackers to perform roughly twice as many guess attempts before success. The intrusion‑detection component attains a 92 % detection accuracy for simulated malicious sessions involving IP spoofing, abnormal typing speed, and atypical device usage. End‑to‑end latency averages 150 ms per authentication request, indicating feasibility for real‑time deployment.
The discussion acknowledges several limitations. Overfitting of the authentication network could raise false‑reject rates for previously unseen passwords; regularization techniques such as dropout and cross‑validation are recommended but not fully explored. Centralizing all models creates a single point of failure; the authors suggest future work on distributed training and multi‑server redundancy to improve resilience. Moreover, the evaluation does not cover a broad spectrum of real‑world attacks like phishing, keylogging, or credential stuffing, leaving open questions about the system’s robustness under diverse threat scenarios.
In conclusion, the paper introduces a novel, ANN‑driven security framework that simultaneously strengthens password verification and adds behavior‑based intrusion detection. While the concept is promising and the preliminary results are encouraging, the work would benefit from deeper technical exposition (model architecture, hyper‑parameter choices), comprehensive security analysis, and real‑world deployment studies. Future research directions include optimizing network structures for minimal latency, integrating the solution with existing authentication standards (e.g., FIDO2), and conducting large‑scale field trials to validate effectiveness against sophisticated adversaries.
Comments & Academic Discussion
Loading comments...
Leave a Comment