Sonet Network Design Problems
This paper presents a new method and a constraint-based objective function to solve two problems related to the design of optical telecommunication networks, namely the Synchronous Optical Network Ring Assignment Problem (SRAP) and the Intra-ring Syn…
Authors: ** - Marie Pelleau (Université de Nantes) – marie.pelleau@univ-nantes.fr - Pascal Van Hentenryck (Brown University) – pvh@cs.brown.edu - Charlotte Truchet (Université de Nantes) – Charlotte.Truchet@univ-nantes.fr **
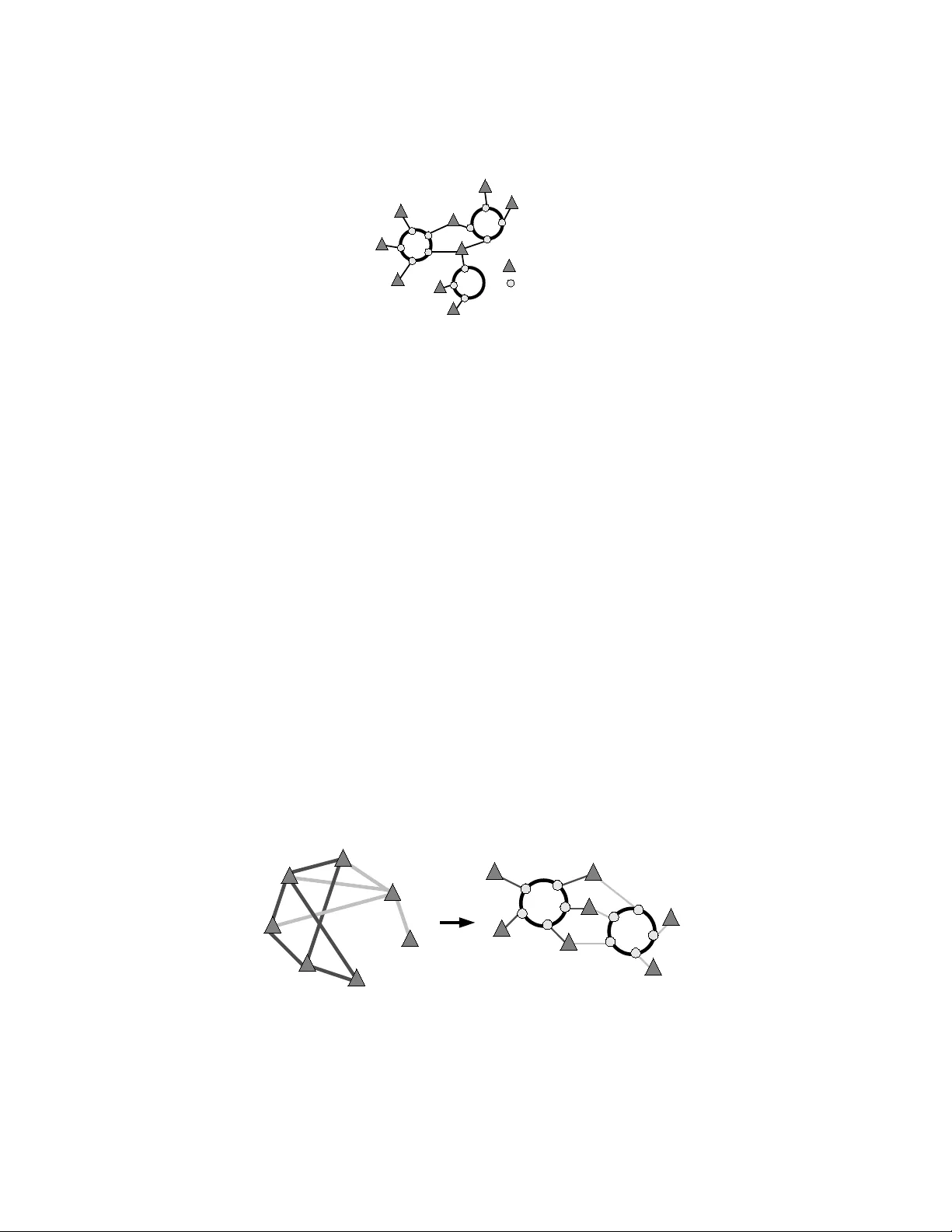
Y . Deville and C. Solnon (Eds): Sixth International W orkshop on Local Search T echniques in Constraint Satisfaction (LSCS’09). EPTCS 5, 2009, pp. 81–95, doi:10.4204/EPTCS.5.7 c M. Pelleau & P . V an Hentenryck & C. T ruchet Sonet Network Design Pr oblems Marie Pelleau † , ‡ Pascal V an Hentenryck ‡ Charlotte T ruchet † marie.pelleau@univ-nantes.fr pvh@cs.brown.edu Charlotte.Truchet@univ-nantes.fr † Univ ersit ´ e de Nantes ‡ Brown Uni versity D ´ epartement informatique Computer Science 2 rue de la Houssini ` ere 115 W aterman Street 44322 Nantes cedex 3 Providence, RI 02912 France USA This paper presents a new method and a constraint-based objective function to solve two problems related to the design of optical telecommunication networks, namely the Synchronous Optical Net- work Ring Assignment Problem (SRAP) and the Intra-ring Synchronous Optical Network Design Problem (IDP). These network topology problems can be represented as a graph partitioning with capacity constraints as shown in previous works. W e present here a new objective function and a new local search algorithm to solve these problems. Experiments conducted in C O M E T allow us to compare our method to previous ones and sho w that we obtain better results. 1 Intr oduction This paper presents a new algorithm and an objectiv e function to solv e two real-world combinatorial optimization problems from the field of network design. These two problems, the Synchronous Optical Network Ring Assignment Problem (SRAP) and the Intra-ring Synchronous Optical Network Design Problem (IDP), ha ve been shown N P -hard and hav e already been solved by combinatorial optimization techniques. This work extends the seminal ideas introduced by R. Aringhieri and M. Dell’Amico in 2005 in [2]. This paper is organized as follows. In the sequel of this section we introduce the two problems we have worked on, and the local search techniques which have been used to solve them. W e will also introduce the models in a constrained optimization format for the two problems. W e then present the pre vious works on SRAP and IDP in section 2. Section 3 describes the ke y ingredients necessary to implement the local search algorithms. Finally , the results are shown in Section 4. 1.1 Optical networks topologies During the last few years the number of internet based application users has exponentially increased, and so has the demand for bandwidth. T o enable fast transmission of large quantities of data, the fiber optic technology in telecommunication is the current solution. The Synchronous Optical NET work (SONET) in North America and Synchronous Digital Hierarchy (SDH) in Europe and Japan are the standard designs for fiber optics networks. They hav e a ring-based topology , in other words, the y are a collection of rings. 82 Sonet Network Design Problems Rings Each customer is connected to one or more rings, and can send, recei ve and relay messages using an add-drop-multiplex er (ADM). There are two bidirectional links connecting each customer to his neighboring customers on the ring. In a bidirectional ring the traffic between two nodes can be sent clockwise or counterclockwise. This topology allo ws an enhanced survi vability of the network, specifically if a failure occurs on a link, the traffic originally transmitted on this link will be sent on the survi ving part of the ring. The volume traf fic on any ring is limited by the link capacity , called B . The cost of this kind of network is defined by the cost of the dif ferent components used in it. There are different ways to represent a network. In this paper , we consider two network topologies described by R. Aringhieri and M. Dell’Amico in 2005 in [2]. In both topologies the goal is to minimize the cost of the network while guaranteeing that the customers’ demands, in term of bandwidth, are satisfied. The model associated to these topologies are based on graphs. Giv en an undirected graph G = ( V , E ) , V = { 1 , . . . , n } , the set of nodes represent the customers and E , the set of edges, stand for the customers’ traf fic demands. A communication between two customers u and v corresponds to the weighted edge ( u , v ) in the graph, where the weight d uv is the fixed traffic demand. Note that d uv = d vu , and that d uu = 0. 1.1.1 First topology (SRAP) In the first topology , each customer is connected to exactly one ring. All of these local rings are con- nected with a device called digital cross connector (DXC) to a special ring, called the federal ring . The traf fic between two rings is transmitted over this special ring. Lik e the other rings, the federal ring is limited by the capacity B . Because DXCs are so much more expensi ve than ADMs we want to have the smallest possible number of them. As there is a one-to-one relationship between the ring and the DXC, minimizing the number of rings is equiv alent to minimizing the number of DXCs. The problem associated to this topology is called SONET Ring Assignment Pr oblem (SRAP) with capacity constraint . Figure 1 sho ws an example of this topology . Federal Ring ADM D XC Customer Figure 1: A SONET network with DXC. Model This topology is modeled by a decomposition of the set of nodes V into a partition, each subset of the partition representing a particular ring. Assigning a node to a subset of the partition in the model is then equi valent to assigning a customer to a ring. Formally , let V 1 , V 2 , . . . , V k be a partitioning of V in k subsets. Each customer in the subset V i is assigned to the i -th local ring. As each customer is connected with an ADM to one and only one ring, and each local ring is connected to the federal ring with a DXC, there are exactly | V | AMD and k DXC used in the corresponding SRAP network. M. Pelleau & P . V an Hentenryck & C. T ruchet 83 Hence, minimizing the number of rings is equi valent to minimizing k subject to the following con- straints: ∑ u ∈ V i ∑ v ∈ V , v 6 = u d uv ≤ B , ∀ i = 1 , . . . , k (1) k − 1 ∑ i = 1 k ∑ j = i + 1 ∑ u ∈ V i ∑ v ∈ V j d uv ≤ B (2) Constraint (1) imposes that the total traffic routed on each ring does not exceed the capacity B . In other words, for a gi ven ring i , it forces the total traf fic demands of all the customers connected to this ring, to be lo wer or equal to the bandwidth. Constraint (2) forces the load of federal ring to be less than or equal to B . T o do so, it computes the sum of the traffic demands between all the pairs of customers connected to dif ferent rings. Figure 2 illustrates the relation between the node partitioning model and the first topology SRAP . W e can see that, because the nodes 1, 3, 5 and 6 are in the same partition, they are connected to the same ring. Similarly , the nodes 2, 4 and 7 are on the same ring. 2 1 4 3 5 6 7 1 2 4 3 5 6 7 Figure 2: Relation between the node partitioning and the network topology . For this problem we can easily compute a lo wer bound k l b introduced in [6]. In fact, we want to kno w the minimum number of partitions needed to route all the traffic. Reasonning on the total traffic amount, if we sum all the traffic demands of the graph and divide it by the bandwidth B , we tri vially obtain a minmum for the number of rings, that is, a lower bound of the number of partitions. Moreover , we cannot hav e fractional part of partition, that is why we take the upper round of this fraction. k l b = n − 1 ∑ u = 1 n ∑ v = u + 1 d uv B 1.1.2 Second topology (IDP) In the second topology , customers can be connected to more than one ring. If two customers want to communicate, they have to be connected to the same ring. In this case, the DXC are no longer needed and neither is the federal ring. Howe ver there are more ADM used than in the first topology . In this case, the most expensi ve component is the ADM although its price has significantly dropped ov er the past few 84 Sonet Network Design Problems years. It is important, in this topology , to hav e the smallest numbers of ADMs. This problem is called Intra-ring Sync hr onous Optical Network Design Pr oblem (IDP). The figure 3 illustrates this topology . ADM Customer Figure 3: A SONET network without DXC. Model Contrarily to the SRAP problem, there is no need to assign each customer to a particular ring because customers can be connected to se veral rings. Here the model is based on a partition of the edges of the graph, where a subset of the partition corresponds to a ring. Formally , let E 1 , E 2 , . . . , E k be a partitioning of E in k subsets and N od es ( E i ) be the set of endpoint nodes of the edges in E i . Each subset of the partition corresponds to a ring, in other w ords, each customer in N od es ( E i ) is linked to the i -th ring. In the corresponding IDP network, there are k ∑ i = 1 | N od es ( E i ) | ADM and no DXC. Hence, minimizing the number of ADMs is equi valent to minimizing k ∑ i = 1 | N od es ( E i ) | subject to, ∑ ( u , v ) ∈ E i d uv ≤ B , ∀ i = 1 , . . . , k (3) Constraint (3) imposes that the traf fic in each ring does not exceed the capacity B . Figure 4 sho ws the relation between the edge partitioning and the second topology . If all the edges of a node are in the same partition, this node will only be connected to a ring. W e can see, for example, the node 4 has all its edges in the same partition, because of that, the node 4 is connected to only one ring. On the opposite, the edges of the node 2 are in two dif ferent partitions, so it is connected to two rings. 1 2 4 3 5 6 7 7 4 1 2 3 5 6 Figure 4: Relation between the edge partitioning and the network topology . M. Pelleau & P . V an Hentenryck & C. T ruchet 85 The SRAP problem can be seen as a node partitioning problem, whereas IDP , as an edge partition- ing problem for the graph described abov e, subject to capacity constraints. These graph partitioning problems hav e been introduced in [6] and [7]. Both of these problems are N P -hard (see O. Goldschmidt, A. Laugier and E. Olinick in 2003, [6], and O. Goldschmidt, D. Hochbaum, A. Levin and E. Olinick in 2003, [7] for details). The principal constraint, the load constraint, is similar to a capacity constraint, yet different: a capacity constraint holds on the variables in the sum, while the load constraint holds on the variables below the sum. The question is ho w to choose the d uv (which are data) that count for the load. 1.2 Brief introduction of Local Search In order to ef ficiently and quickly solve these two combinatorial optimization problems, we decided to use Local Search instead of an exact algorithm. Indeed, it permits to search in a efficiently way among all the candidate solutions, by performing steps from a solution to another . Principles Local search is a metaheuristic based on iterativ e improvement of an objectiv e function. It has been proved very efficient on many combinatorial optimization problems like the Maximum Clique Problem (L. Cavique, C. Rego and I. Themido in 2001 in [9]), or the Graph Coloring Problem (J.P . Hansen and J.K. Hao in 2002 in [10]). It can be used on problems which formulated either as mere op- timization problems, or as constrained optimization problems where the goal is to optimize an objective function while respecting some constraints. Local search algorithms perform local moves in the space of candidate solutions, called the search space, trying to improve the objectiv e function, until a solution deemed optimal is found or a time bound is reached. Defining the neighborhood graph and the method to explore it are tw o of the key ingredients of local search algorithms. The approach for solving combinatorial optimization problems with local search is very different from the systematic tree search of constraint and integer programming. Local search belongs to the fam- ily of metaheuristic algorithms, which are incomplete by nature and cannot prove optimality . Howe ver on many problems, it will isolate a optimal or high-quality solution in a very short time: local search sacrifices optimality guarantees to performance. In our case, we can compute the lower bound to either prov e that the obtained solution is optimum, or estimate its optimality , hence local search is well suited. Basic algorithm A local search algorithm starts from a candidate solution and then iterati vely mov es to a neighboring solution. This is only possible if a neighborhood relation is defined on the search space. T ypically , for e very candidate solution, we define a subset of the search space to be the neighborhood. Mov es are performed from neighbors to neighbors, hence the name local search. The basic principle is to choose among the neighbors the one with the best value for the objecti ve function. The problem is then that the algorithm will be stuck in local optima. Metaheuristics, such as T ab u Search, are added to av oid this. In T ab u Search, the last t visited configurations are left out of the search ( t being a parameter of the algorithm): this ensures that the algorithm can escape local optima, at least at order t . A pseudo-code is gi ven on figure 1. T ermination of local search can be based on a time bound. Another common choice is to terminate when the best solution found by the algorithm has not been improved in a gi ven number of iterations. Lo- cal search algorithms are typically incomplete algorithms, as the search may stop e ven if the best solution found by the algorithm is not optimal. This can happen e ven if termination is due to the impossibility of improving the solution, as the optimal solution can lie f ar from the neighborhood of the solutions crossed by the algorithms. 86 Sonet Network Design Problems Choose or construct an initial solution S 0 ; S ← S 0 ; /* S is the current solution */ S ∗ ← S 0 ; /* S ∗ is the best solution so far */ bes t Val ue ← ob jVal ue ( S 0 ) ; /* bestV al ue is the evaluation of S ∗ */ T ← / 0 ; /* T is the Tabu list */ while T erminaison criterion not satisfied do N ( S ) ← all the neighboring solutions of S ; /* Neighborhood exploration */ S ← a solution in N ( S ) minimizing the objecti ve ; if ob j Val ue ( S ) < bestV al ue then /* The solution found is better than S ∗ */ S ∗ ← S ; bes t Val ue ← ob jVal ue ( S ) ; end Record tabu for the current mo ve in T (delete oldest entry if necessary) ; end Algorithm 1 : T ab u Search 1.3 C O M E T C O M E T is an object-oriented language created by Pascal V an Hentenryck and Laurent Michel. It has a constraint-based architecture that makes it easy to use when implementing local search algorithms, and more important, constraint-based local search algorithms (see [1] for details). Moreov er , it has a rich modeling language, including in v ariants, and a rich constraint language fea- turing numerical, logical and combinatorial constraints. Constraints and objectiv e functions are dif feren- tiable objects maintaining the properties used to direct the graph exploration. The constraints maintain their violations and the objectives their e valuation. One of its most important particularity , is that differ - entiable objects can be queried to determine incrementally the impact of local mov es on their properties. As we can see on the constraint (1), the sum are on datas ( d uv ) and are determined by the v ariables ( u ∈ V i , v ∈ V , v 6 = u ). W e will rely on C O M E T ’ s built-in in variants to define a constraint to represent the load. 2 Related work These two problems ha ve been well studied. It has been prov en that they are both N P -hard ([6], [7]). 2.1 Greedy algorithms for SRAP In [6] the SRAP problem is considered. They propose three greedy algorithms with different heuristics, the edge-based , the cut-based and the node-based . The first two algorithms start by assigning each node to a different ring. At each iteration they reduce the number of rings by merging two rings V i and V j if V i ∪ V j is a feasible ring for the capacity constraint. In the edge-based heuristic, the two rings with the maximum weight edge are merged. While in the cut-based heuristic, the two rings with the maximum total weight of the edges with one endpoint in each of them, are merged. Algorithm 2 sho ws the pseudo code for the edge-based heuristic. Gi ven a v alue k , the node-based heuristic, starts by randomly assigning a node to each of the k rings. At each iteration it first chooses the ring V i with the largest unused capacity , then the unassigned node M. Pelleau & P . V an Hentenryck & C. T ruchet 87 F ← E ; /* Initialize the set of edges that have not been used yet */ ∀ v ∈ V r ing ( v ) ← v ; /* Assign each node to a different ring */ while F 6 = / 0 do /* There is still some edges that have not been used */ Choose a maximum capacity edge ( u , v ) ∈ F ; i ← r ing ( u ) , j ← r ing ( v ) ; if V i ∪ V j is a feasible ring then /* Merging the rings gives a feasible ring */ ∀ v ∈ V j r ing ( v ) ← i ; F ← F \{ ( x , y ) | ring ( x ) = i , r ing ( y ) = j } ; else F ← F \{ ( u , v ) } ; end end Algorithm 2 : Edge-Based Heuristic u with the largest traffic with the nodes in V i . Finally it adds u to the ring V i disregarding the capacity constraint. The pseudo-code for this heuristic is shown on algorithm 3. The node-based heuristic is run ten times. At each run, if a feasible solution is found, the corresponding v alue for k is kept and the ne xt run takes k − 1 as an input. The idea behind this is to try and improv e the objecti ve at each run. U ← V ; /* Initialize the set of nodes that have not been used yet */ f or i = 1 to k do /* Assign k random nodes to the k partitions */ Choose u ∈ U , V i ← u , U ← U \{ u } end while U 6 = / 0 do /* There are some unused nodes */ Choose a minimum capacity ring V i Choose u ∈ U to maximize ∑ { v ∈ V i } d uv r ing ( u ) ← V i , U ← U \{ u } ; /* Assign u to V i */ end Algorithm 3 : Node-Based Heuristic T o test these heuristics, the authors have randomly generated 160 instances 1 . The edge-based, and the cut-based are run first. If they have found a feasible solution and obtained a value for k , the node-based is then run with the smallest value obtained for k as input. If they ha ve not, the node-based heuristic has for input a random v alue from the range [ k l b , | V | ] where k l b is the lower bound , described pre viously . 2.2 MIP and Branch and Cut f or IDP A special case of the IDP problem where all the edges hav e the same weight, is studied in [7]. This special case is called the K-Edge-P artitioning problem. Giv en a simple undirected graph G = ( V , E ) and a value k < | E | , we want to find a partitioning of E , { E 1 , E 2 , . . . E l } such that ∀ i ∈ { 1 , . . . , l } , | E i | ≤ k . The authors present two linear -time-approximation algorithms with fixed performance guarantee. 1 These instances are av ailable at www.seas.smu.edu/ ~ olinick/srap/GRAPHS.tar. 88 Sonet Network Design Problems Y . Lee, H. Sherali, J. Han and S. Kim in 2000 ([8]), have studied the IDP problem with an additional constraint such that for each ring i , | N od es ( E i ) | ≤ R . The authors present a mixed-integer programming model for the problem, and dev elop a branch-and-cut algorithm. They also introduce a heuristic to generate an initial feasible solution, and another one to improv e the initial solution. T o initialize a ring, the heuristic first, adds the node u with the maximum graph degree, with respect to unassigned edges, and then adds to the partition the edge [ u , v ] such that the graph degree of v is maximum. It iterativ ely increases the partition by choosing a node such that the total traffic does not exceed the limit B . A set of 40 instances is generated to test these heuristics and the branch-and-cut. 2.3 Local Search for SRAP and IDP More recently , in [2], these two problems have been studied. The authors hav e dev eloped different metaheuristic algorithms, all based on the T ab u Search. The metaheuristics are the Basic T abu Sear ch (BTS), two versions of the P ath Relinking (PR1, PR2), the eXploring T abu Sear ch (XTS), the Scatter Sear ch (SS), and the Diversification by Multiple Neighborhoods (DMN). These local search algorithms are detailed further . Pre viously , we saw that with local search it is necessary to define a neighborhood to choose the next solution. The authors of [2] use the same for all of their metaheuristics. It tries to assign an item x from a partition, P 1 , to another partition, P 2 . The authors also consider the neighborhood obtained by swapping two items, x and y , from two different partitions, P 1 and P 2 . But instead of trying all the pairs of items, it will only try to swap the two items if the resulting solution of the assignment of x to the partition P 2 is unfeasible. In order to compute a starting solution for the IDP problem, the authors describe four different heuristics. The first heuristic introduced in [2] ordered the edges by decreasing weight, at each iteration it tries to assign the edge with the biggest weight which is not already assigned, to the ring with the smallest residual capacity regarding to capacity constraint. If no assignment is possible, the current edge is assigned to a new ring. The second one, sorts the edges by increasing weight, and tries to assign the current edge to the current ring if the capacity constraint is respected, otherwise the ring is no longer considered and a ne w ring is initialized with the current edge. The two other methods described in [2] are based on the idea that to save ADMs a good solution should hav e very dense rings. They are both greedy and rely on a clique algorithm. In graph theory , a clique in an undirected graph G = ( V , E ) is a subset of the verte x set C ⊆ V , such that for ev ery two vertices in C , there exists an edge connecting the two. Finding a clique is not that easy , a way to do it is to use an ”Union-Find” strategie, F ind two clique A and B such that each node in A is adjacent to each node in B then merge the two cliques ( Union ). The associated heuristic starts by considering each node to be a clique of size one, and to merge two cliques into a larger clique until there are no more possible merges. In the third method, Clique-BF , it iterati vely selects a clique of unassigned edges with the total traffic less or equal to B . Then assigns it to the ring that minimizes the residual capacity and, if possible, preserves the feasibility . If both of them are impossible it places it to a ne w ring. Algorithm 4 sho ws the pseudo code associated to this heuristic. The last algorithm, Cycle-BF , is like the previous method, but instead of looking for a clique at each iteration it try to find a cycle with as man y cords as possible. They also introduce four objecti ve functions, one of which depends on the current and the next status of the search. Let z 0 be the basic objecti ve function counting the number of rings of a solution for SRAP , and the total number of ADMs for IDP , and let BN be the highest load of a ring in the current solution. M. Pelleau & P . V an Hentenryck & C. T ruchet 89 U ← E ; r ← 0 ; while U 6 = / 0 do Heuristicaly find a clique C ⊂ U such that weight ( C ) ≤ B ; /* Search a ring such that the weight of the ring plus the weight of the clique does not exceed B and is the biggest possible */ j ← min { B − weight ( E i ) − weight ( C ) : i ∈ { 1 , . . . , k } , B − weight ( E i ) − weight ( C ) ≥ 0 } ; if j = null then r + + ; j ← r ; end E j ← E j ∪ C ; U ← U \ C ; end Algorithm 4 : Clique-BF z 1 = z 0 + max { 0 , BN − B } , z 2 = z 1 + α · RingLoad ( r ) if the last mov e has created a new ring r , 0 otherwise z 3 = z 0 · B + BN z 4 = z 4 a = z 0 · B + BN (= z 3 ) (a): from feasible to feasible z 4 b = ( z 0 + 1 ) BN (b): from feasible to unfeasible z 4 c = z 0 B (c): from unfeasible to feasible z 4 d = β z 0 BN (d): from unfeasible to unfeasible with α ≥ 1 and β ≥ 2, two fixed parameters, and where RingLoad ( r ) is the load of the ring r . The first function z 1 minimizes the basic function z 0 . As BN > B , it also penalizes the unfeasible solutions, by taking into account only one ring, the one with the highest overload. In addition to the penalty for the unfeasible solutions, z 2 penalizes the mov es that increase the number of rings. Function z 3 encourages solutions with small z 0 , while among all the solutions with the same v alue of z 0 , it prefers the ones in which the rings have the same loads. The last objectiv e function z 4 is an adapting technique that modifies the ev aluation according to the status of the search. It is a variable objective function having dif ferent expressions for dif ferent transitions from the current status to the next one. 3 Our work In this section we present the dif ferent tools needed to implement the Constraints Based Local Search algorithms for SRAP and IDP . First we introduce the starting solution, then the neighborhoods and the objecti ve functions. Finally we present the different local search algorithms. 3.1 Starting solution Most of the times, local search starts from an random initial solution. Howe ver we hav e tested other possibilities and two other options pro ved to be more ef ficient. 90 Sonet Network Design Problems The best initializing method assigned all the items, nodes for SRAP or edges for IDP , to the same partition. This solution is certainly unfeasible as all the traf fic is on only one ring. This biases the search to wards solutions with a minimum value for the cost and a very bad value for the capacity constraints’ violations. Astonishingly this is the one that gav e us the best results on large instances. W e had good confidence in another one which first computes the lower bound k l b (described in section 2) and randomly assigns all the items to e xactly k l b partitions. The idea was to let the Local Search reduce the number of violations. This starting solution was good on small instances and not so good on lar ge ones. It w as the same with a random solution, which corresponds, for these problems, to a solution where all the items are randomly assigned to a partition. 3.2 Neighborhoods In a generic partitioning problem there are usually two basic neighborhoods. From a given solution, we can move an object from a subset to another subset or swap two objects assigned to two different subsets. For SRAP a neighboring solution is produced by mo ving a node from a ring to another (including a new one) or by swapping two nodes assigned to two different rings. The same kind of neighborhood can be used for IDP: moving an edge from a ring to another or sw apping two edges. In some cases it is more efficient to restrain the neighborhood to the feasible space. W e hav e tested dif ferent variants of the basic neighborhood applying this idea, by choosing the worst partition (wrt. the capacity constraint) and ev en by assigning it to the partition with the lowest load. Anyway it appears to be less efficient than the basic one. As will be seen later it seems that on these problems it is necessary to keep the search as broad as possible. 3.3 Objective function W e hav e compared the four objectiv e functions described in [2] (see Section 2) to a new one we hav e defined: z 5 . z 5 = z 0 + ∑ p ∈ part it ions viol at ions ( p ) where part it ions are all the rings (in the case of the SRAP problem the federal ring is also included), viol at ions ( p ) = ca pacit y ( p ) − B if the load of p exceed B 0 otherwise. This objectiv e function minimizes the basic function z 0 and penalizes the unfeasible solutions, but contrarily to the previous objectives, this penalty is based on all the constraints. W e consider that ev ery constraint is violated by a certain amount (its current load minus B ). By summing all the violations of the current solution, we obtain the total violation for all the constraints, and we can precisely say ho w far we are from a feasible one. If the current solution is feasible, ∑ p ∈ part it ions viol at ions ( p ) = 0. This objecti ve has also the nice property that it is merely local, depending only on the current solution and not on the other moves. Notice that a feasible solution with 4 rings will be preferred to an unfeasible solution with 3 rings, as z 0 is much smaller than the load of a ring. M. Pelleau & P . V an Hentenryck & C. T ruchet 91 3.4 Local Search W e have proposed a new algorithm called DMN2 which proved to be ef ficient on both problems. It is a variant of the Div ersification by Multiple Neighborhood (DMN) proposed in [2]. DMN is based on T ab u Search, and adds a mechanism to perform di versification when the search is going round and round without improving the objectiv e (ev enthough it is not a local minimum). This replaces the classical random restart steps. W e refine this particular mechanism by proposing sev eral ways of escaping such areas. More precisely , on our problems, after a series of consecutiv e non improving iterations, the DMN algorithm empties a partition by moving all its items to another partition, disregarding the capacity constraint and locally minimizing the objectiv e function. There is a particular case for our function z 5 , because it integrates the capacity constraints. In this case, the ” z 5 ” version of DMN we have implemented mov es the items to another partition minimizing z 5 . The results in [2] show a general trend on SRAP and IDP: the more div ersification is performed, the better are the results. Following this idea, we propose dif ferent ways of perfoming the DMN step, which gi ves our algorithm DMN2. In DMN2, when the search needs to be di versified, it random ly chooses among three di versification methods ( d 1 , d 2 , d 3 ). The first method, d 1 , is the di versification used in DMN. The second one, d 2 , generates a random solution, in the same way as a classic random restart. Finally , d 3 randomly chooses a number m in the range [1, k ], where k is the number of rings, and applies m random moves. In the end, our general algorithm starts with a solution where all the items are in the same partition. Then it applies one of the local search algorithms described before. If the solution returned by the local search is feasible but with the objectiv e value greater than the lo wer bound k l b , it empties one partition by randomly assigning all its items to another . Then run once again the local search until it founds a solution with the objecti ve v alue equals to k l b or until the time limit is exceeded. 4 Results The objectiv e functions and the metaheuristics, respectiv ely described in Section 3.3 and Section 3.4, hav e been coded in C O M E T and tested on Intel based, dual-core, dual processor, Dell Poweredge 1855 blade server , running under Linux. The instances used are from the litterature. 4.1 Benchmark T o test the algorithms, we used two sets of instances. The first one has been introduced in [6]. They hav e generated 80 geometric instances, based on the fact that customers tend to communicate more with their close neighbors, and 80 random instances. These subsets hav e both 40 low-demand instances, with a ring capacity B = 155 Mbs, and 40 high-demand instances, where B = 622 Mbs. The traffic demand between two customers, u and v , is determined by a discrete uniform random variable corresponding to the number of T1 lines required for the anticipated volume of traffic between u and v . A T1 line has an approximate capacity of 1.5 Mbs. The number of T1 lines is randomly picked in the interval [ 3 , 7 ] , for lo w-demand cases, while it is selected from the range [ 11 , 17 ] , for the high-demand cases. The generated graphs have | V | ∈ { 15 , 25 , 30 , 50 } . In the 160 instances, generated by O. Goldschmidt, A. Laugier and E. Olinick in 2003, 42 ha ve been proven to be unfeasible by R. Aringhieri and M. Dell’Amico using CPLEX 8.0 (see [2]). 92 Sonet Network Design Problems Construct the initial solution S 0 ; S ← S 0 ; /* S is the current solution */ S ∗ ← S 0 ; /* S ∗ is the best solution so far */ bes t Val ue ← ob jVal ue ( S 0 ) ; /* bestV al ue is the evaluation of S ∗ */ T ← / 0 ; /* T is the Tabu list */ nonI m provingS t e p ← 0 ; /* nonI m pro vingSt e p is the number of consecutive non improving iterations */ while bestV al ue > l ower bound and we still have time do N ( S ) ← all the neighboring solution of S ; S ← the solution in N ( S ) minimizing the objecti ve ; if ob jVal ue ( S ) < bestV al ue then /* The solution found is better than S ∗ */ S ∗ ← S ; bes t Val ue ← ob jVal ue ( S ) ; nonI m provingS t e p ← 0 ; else /* The iteration did not improve S ∗ */ nonI m provingS t e p + + ; end Record tabu for the current mo ve in T (delete oldest entry if necessary) ; if nonI m pro vingSt e p = maxN onI m provingS t e p then /* Stuck in a non improving area: time for diversification */ nonI m provingS t e p ← 0 ; /* Uniformly chooses the diversification to apply */ d ← U ni f or mRand om ( 1 , 3 ) ; switch The value of d do case 1 /* Empties a partition */ Randomly choose a partition p ; f oreach item i on the partition p do Choose the partition p 0 such that the assignment of i to p 0 minimizes the objecti ve function and p 0 6 = p ; Assign i to the partition p 0 ; end case 2 /* Random Restarts */ f oreach item i do Randomly choose a partition p ; Assign i to the partition p ; end case 3 /* Applies m random moves */ m ← U ni f ormRand om ( 1 , numberO f Rings ) ; Apply m mov es ; end end end end Algorithm 5 : DMN2 M. Pelleau & P . V an Hentenryck & C. T ruchet 93 The second set of instances has been presented in [8]. They hav e generated 40 instances with a ring capacity B = 48 × T1 lines and the number of T1 lines required for the traf fic between two customers has been chosen in the interv al [ 1 , 30 ] . The considered graphs hav e | V | ∈ { 15 , 20 , 25 } and | E | = { 30 , 35 } . Most of the instances in this set are unfeasible. Note that all the instances can be feasible for the IDP problem, we always could assign each demand to a dif ferent partition. 4.2 Computational Results W e now describe the results obtained for SRAP and IDP on the above two benchmark sets, by the algorithms Basic T ab u Search (BTS), Path Relinking (PR1, PR2), eXploring T abu Search (XTS), Scatter Search (SS), Div ersification by Multiple Neighborhoods (DMN, DMN2) (see Section 3.4 for details). For each algorithm we consider the five objectiv e functions of Section 3.3, b ut for the SS we use the three functions described in Section 3.4. W e ga ve a time limit of 5 minutes to each run of an algorithm. Howe ver we observed that the average time to find the best solution is less than 1 minute. Obviously , the algorithm terminates if the current best solution found is equal to the lower bound k l b . In case the lower bound is not reached, we define as a high-quality solution a solution for which the ev aluation of the objecti ve is equal to k l b + 1. Remind that objecti ve functions z 2 and z 3 cannot be applied with the Scatter Search. Min BTS P R 1 PR2 XTS SS DMN DMN2 0 20 40 60 80 100 120 140 160 180 200 Number of instances fo r which the Local Search found the optimal solution The Local Search associat e with the objective function z5 Figure 5: Results for IDP . The figure 5 only sho ws for each algorithm the number of optimal solutions found with the objecti ve function z 5 . With the other objectiv es, the number of optimal solutions found is zero, that is why we did not show them on the diagram. Howe ver the other objectiv es found good solutions. Our conclusion is that maybe the other functions do not enough discriminate the different solutions. For this problem, 94 Sonet Network Design Problems we can see that the eXploring T ab u Search does not give good results. This can be due to a too early ”backtracking”. After a fixed number of consecutiv e non improving iterations the search goes back in a pre vious configuration and applies the second best mov e. In the case of the IDP problem, it could take much more iterations to improve the value of the objectiv e function than for the SRAP problem. Indeed, the value of the objective function depends on the number of partitions in which a customer belongs, while an iteration moves only one edge ; and to reduce its value by only one it could need to move se veral edges. z 5 z1 z 2 z3 z 4 z 5 z 1 z 2 z3 z 4 z 5 z1 z2 z3 z 4 z 5 z 1 z 2 z3 z 4 z 5 z1 z2 z 3 z4 z 5 z1 z 2 z3 z 4 z5 z 1 z2 z3 z 4 0 20 40 60 80 100 120 140 160 180 200 BTS P R 1 PR2 XTS SS DMN DMN2 Number of i nstances for which the Local Sear ch found at least a f easible solution F easible Lowe r bound + 1 O ptimal All the Local Search associ at e wi t h the different objectiv e functions Figure 6: Results for SRAP . Figure 6 shows for each algorithm and each objective function, the number of instances for which the search has found an optimal solution, i.e. a solution with k l b partitions (in dark gray on the diagram) ; the number of those for which the best feasible solution found has k l b + 1 partitions (in gray) ; and, in light gray , the number of instances for which it has found a feasible solution with more than k l b + 1 partitions. From the objectiv e functions perspecti ve, we can see that z 4 , supposed to be the most improving one, is not that good in the C O M E T implementation. Howe ver the one we add, z 5 , is always better than the other ones. Against all odds, the Basic T abu Search on all the objectiv e functions, is as good as the other search algorithms. Still on the local search algorithms, we can see that the second v ersion of the Diversification by Multiple Neighborhoods, is much better than the first one with the objecti ves z 3 and z 4 . For the details of our results see the report [11]. M. Pelleau & P . V an Hentenryck & C. T ruchet 95 5 Conclusion The purpose of this work was to reproduce with C O M E T the results obtained, for the SONET Design Problems, by R. Aringhieri and M. DellAmico in 2005 in ANSI C (see [2] for details). W e hav e implemented in C O M E T the algorithms and the objectiv e functions described in this paper . W e found rele vant to add a variant of one of their local search algorithm and a new objectiv e function. Unfortunately , we cannot e xactly compare our results to theirs because the set of 230 instances the y ha ve generated is not av ailable. Howe ver , for the IDP problem, we obtained better results for 15 instances over the 160 compared, and similar results for the other instances. Unfortunately we did not found their results for the SRAP problem. Still for the problem SRAP , compare to the results obtained by O. Goldschmidt, A. Laugier and E. Olinick in 2003, [6] we obtained better results, we have more instances for wich the algorithm reach the lo wer bound and less unfeasible instances. It would be interesting to ha ve all the instances and the results to fully compare our results. In the end we can exhibit two main observations. Firstly , for these two problems, the more an algorithm uses di versification the better it is. Actually , we hav e tried different intensification methods for the local search algorithms but none of them improv ed the results, worst, they ga ve us pretty bad results. Secondly , based on our results, we can say that our objectiv e function implemented in C O M E T finds more good solutions than the other ones. It is a constraint-based objectiv e function taking into account the violation of ev ery constraint. Hence it has the asset of being both more generic and precise than the dedicated functions, with better results. Refer ences [1] V an Hentenryck, Pascal and Michel, Laurent (2005): Constraint-Based Local Sear ch . The MIT Press [2] Aringhieri, Roberto, Dell’Amico, Mauro (2005): Comparing Metaheuristic Algorithms for Sonet Network Design Pr oblems . Journal of Heuristics 11, pp. 35–57 [3] Dell’Amico, Mauro, T rubian, Marco (1998): Solution of Lar ge W eighted Equicut Pr oblems . European J. Oper . Res 106(2/3), pp. 500–521 [4] Glov er , Fred, Laguna, Manuel (1997): T abu Sear ch . Boston. Kluwer Academic Publishers [5] Glov er , Fred (1997): A T emplate for Scatter Searc h and P ath Relinking . Lecture Notes in Computer Science 1363, pp. 13–54 [6] Goldschmidt, Oli vier , Laugier , Alexandre, Olinick, Eli V . (2003): SONET/SDH Ring Assignment with Capac- ity Constraints . Discrete Appl. Math. 129, pp. 99–128 [7] Goldschmidt, Olivier , Hochbaum, Dorit S., Levin, Asaf, Olinick, Eli V . (2003): The Sonet Edge-P artition Pr oblem . Networks 41, pp. 3–23 [8] Lee, Y oungho, Sherali, Hanif D., Han, Junghee, Kim, Seong-in (2000): A Branch-and-Cut Algorithm for Solving an Intraring Sync hr onous Optical Network Design Pr oblem . Networks 35, pp. 223–232 [9] Ca vique, Lus, Rego, Csar , Themido, Isabel (2001): A Scatter Searc h Algorithm for the Maximum Clique Pr oblem . Essays and Surveys in Metaheuristics Kluwer pp. 227-244 [10] Hamiez, Jean-Philippe, Hao, Jin-Kao (2002): Scatter Searc h for Graph Coloring . Lecture Notes In Computer Science 2310, pp. 195–213 [11] Pelleau, Marie (2009): Sonet Network Design Pr oblem .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment