A Survey of Biometric keystroke Dynamics: Approaches, Security and Challenges
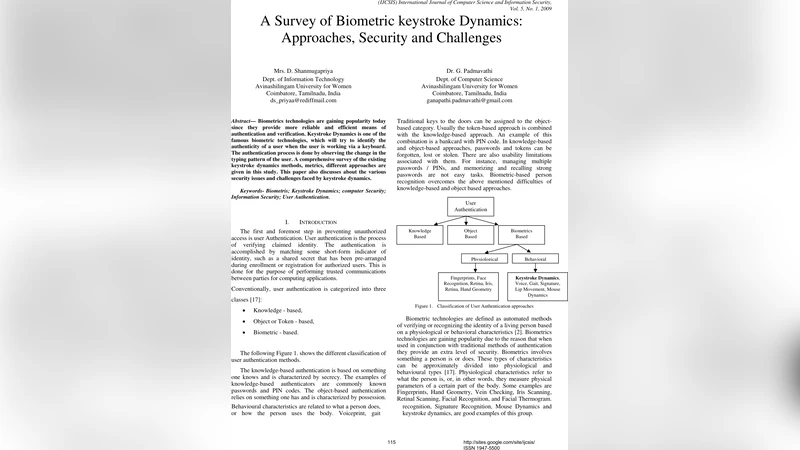
Biometrics technologies are gaining popularity today since they provide more reliable and efficient means of authentication and verification. Keystroke Dynamics is one of the famous biometric technologies, which will try to identify the authenticity of a user when the user is working via a keyboard. The authentication process is done by observing the change in the typing pattern of the user. A comprehensive survey of the existing keystroke dynamics methods, metrics, different approaches are given in this study. This paper also discusses about the various security issues and challenges faced by keystroke dynamics.
💡 Research Summary
The paper provides a comprehensive survey of keystroke dynamics, a behavioral biometric technique that authenticates users based on the timing and rhythm of their typing. It begins by positioning keystroke dynamics within the broader landscape of authentication, highlighting its advantages over traditional password‑based and token‑based methods, especially in terms of cost, user convenience, and resistance to certain replay attacks.
Data acquisition is examined in depth, distinguishing between static (fixed‑text) and dynamic (free‑text) collection protocols. Static protocols, such as typing a predetermined password or phrase, enable controlled experiments and yield high repeatability, but they may not reflect real‑world usage patterns. Dynamic protocols capture natural typing behavior during activities like email composition or chat, offering greater ecological validity at the cost of increased variability. The authors discuss preprocessing steps—including noise filtering, time synchronization, and outlier detection—that are essential for both scenarios.
Feature extraction is a central theme. Traditional time‑domain features (key‑down, key‑up, dwell, flight, and latency) are complemented by frequency‑domain analyses (FFT, wavelet transforms), graph‑based representations of key adjacency, and multimodal signals such as pressure, mouse movement, and touch‑screen force. Recent advances leverage deep learning to bypass manual feature engineering; convolutional‑LSTM hybrids, transformer‑based sequence models, and graph neural networks have been applied to raw timestamp streams. Empirical results on public datasets (e.g., CMU‑Keystroke, LM‑Keystroke) show that these neural approaches reduce Equal Error Rate (EER) by roughly 5–15 % compared with classic classifiers like SVM, k‑NN, or Random Forest.
Classification strategies are categorized into one‑class (user‑specific) and multi‑class (population‑wide) models. One‑class methods—such as One‑Class SVM or auto‑encoder anomaly detectors—excel at rejecting unknown users but can be overly sensitive to legitimate variations in a user’s typing over time. Multi‑class deep models achieve higher overall accuracy in large user bases but require extensive labeled data and incur greater computational overhead. The survey recommends hybrid schemes that combine one‑class anomaly detection with multi‑class verification, together with online adaptation mechanisms that continuously update model parameters as new typing samples arrive.
Security threats are analyzed thoroughly. Replay attacks that simply resend captured timing vectors can be mitigated by challenge‑response mechanisms that require users to type random strings or session‑specific prompts. More sophisticated imitation attacks, powered by generative adversarial networks, aim to synthesize keystroke patterns that mimic a target user; defenses against these include multimodal fusion (e.g., keystroke + facial or voice biometrics), non‑linear random perturbations of the input stream, and uncertainty‑based detection using Bayesian neural networks. Data leakage and model inversion attacks are also discussed, prompting the authors to explore privacy‑preserving techniques such as differential privacy applied during feature extraction and homomorphic encryption for training on encrypted data.
The paper concludes with a forward‑looking discussion of practical deployment challenges. User experience considerations demand low false‑reject rates and seamless enrollment processes; adaptive thresholding and lightweight on‑device inference (e.g., MobileNet‑V2 variants) are suggested to meet latency constraints. Cross‑platform compatibility—spanning laptops, tablets, virtual keyboards, and emerging wearable input devices—requires standardized data formats and APIs. Legal and ethical issues, including consent, data retention policies, and compliance with regulations like GDPR, are highlighted as non‑technical yet critical barriers. Finally, the authors stress the importance of continuous learning frameworks that can accommodate gradual shifts in typing behavior due to fatigue, injury, or changes in hardware.
In summary, the survey underscores that keystroke dynamics holds significant promise as a low‑cost, non‑intrusive biometric, but its widespread adoption hinges on balancing accuracy, security, privacy, and usability. Ongoing research must address adaptive modeling, robust anti‑spoofing measures, and regulatory alignment to realize the full potential of this technology.
Comments & Academic Discussion
Loading comments...
Leave a Comment