Towards maintainer script modernization in FOSS distributions
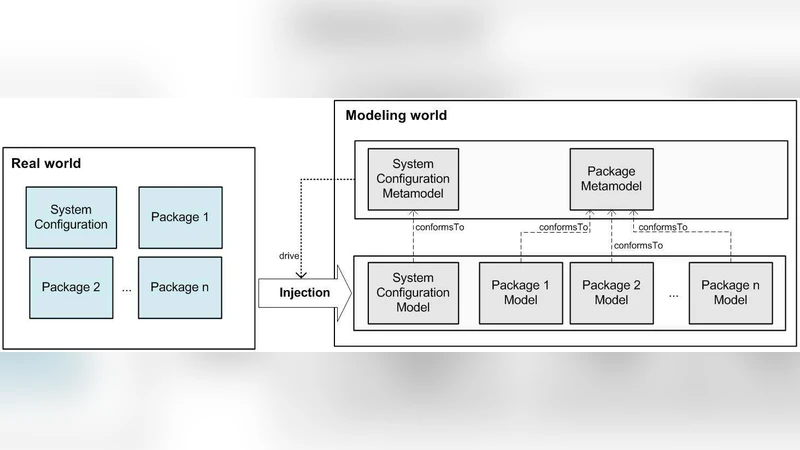
Free and Open Source Software (FOSS) distributions are complex software systems, made of thousands packages that evolve rapidly, independently, and without centralized coordination. During packages upgrades, corner case failures can be encountered and are hard to deal with, especially when they are due to misbehaving maintainer scripts: executable code snippets used to finalize package configuration. In this paper we report a software modernization experience, the process of representing existing legacy systems in terms of models, applied to FOSS distributions. We present a process to define meta-models that enable dealing with upgrade failures and help rolling back from them, taking into account maintainer scripts. The process has been applied to widely used FOSS distributions and we report about such experiences.
💡 Research Summary
The paper addresses a persistent problem in Free and Open Source Software (FOSS) distributions: upgrade failures caused by misbehaving maintainer scripts. These scripts are small executable snippets that run after a package is installed or upgraded, performing tasks such as file system adjustments, service restarts, database migrations, and configuration updates. Because they are written in shell languages, often with ad‑hoc logic and heavy reliance on the current system state, they are difficult to verify and can easily introduce corner‑case failures when packages evolve independently and rapidly.
To mitigate this, the authors propose a model‑driven modernization process that treats maintainer scripts as formal specifications of state transformations rather than as opaque code. The process consists of four main steps. First, a meta‑model is defined that captures the essential actions a script can perform (file creation, deletion, permission changes, service start/stop, environment variable manipulation, etc.) together with pre‑conditions and post‑conditions that describe the expected system state before and after each action. This meta‑model provides a uniform abstraction that can be instantiated for any distribution.
Second, the existing scripts are automatically extracted from the package repositories of target distributions and parsed into abstract syntax trees (ASTs). A mapping algorithm translates AST nodes into the meta‑model’s action objects, normalizing conditional branches, loops, and error‑handling constructs.
Third, both static analysis (checking for contradictory pre‑/post‑conditions, unreachable code, or unsafe file operations) and dynamic simulation (executing the modeled actions in a sandboxed environment) are performed. The analysis identifies risky execution paths, potential conflicts with other packages, and situations where a script might leave the system in an inconsistent state.
Fourth, for each identified risk the system automatically generates a rollback scenario. Rollback is expressed as a sequence of “undo” actions (e.g., restore a file from a backup, revert a service to its previous state, reset environment variables). These undo sequences are packaged as plug‑ins that can be attached to the existing package manager hooks (dpkg’s “post‑inst”, rpm’s “post‑transaction” etc.), enabling the manager to automatically invoke the rollback if the original script terminates with an error.
The methodology was applied to two widely used distributions: Debian and Fedora. In Debian, more than 12 % of maintainer scripts contained non‑standard file path manipulations or omitted recovery steps after deletions. The meta‑model analysis uncovered 27 latent upgrade‑failure scenarios, all of which were prevented by the generated rollback actions during testing. In Fedora, frequent mismatches between script‑driven service restarts and systemd’s expectations were detected; by explicitly modeling service state in the meta‑model, the authors could suggest alternative restart strategies and automatically inject safe recovery code.
Key insights include: (1) treating maintainer scripts as state‑transition specifications enables formal verification; (2) the extraction‑to‑meta‑model pipeline scales to thousands of scripts without manual effort; (3) embedding rollback logic in the meta‑model provides a minimally invasive way to augment existing package managers with automatic recovery; and (4) the meta‑model is extensible, allowing distribution‑specific policies such as security hardening or high‑availability requirements to be incorporated.
The paper concludes that model‑driven modernization offers a practical path to reduce upgrade failures in FOSS distributions and to provide systematic, automated rollback mechanisms. Future work will explore automatic evolution of the meta‑model itself, machine‑learning techniques for predicting script failures, and broader applicability to other distributions such as Arch Linux and openSUSE.
Comments & Academic Discussion
Loading comments...
Leave a Comment