SQL/JavaScript Hybrid Worms As Two-stage Quines
Delving into present trends and anticipating future malware trends, a hybrid, SQL on the server-side, JavaScript on the client-side, self-replicating worm based on two-stage quines was designed and implemented on an ad-hoc scenario instantiating a very common software pattern. The proof of concept code combines techniques seen in the wild, in the form of SQL injections leading to cross-site scripting JavaScript inclusion, and seen in the laboratory, in the form of SQL quines propa- gated via RFIDs, resulting in a hybrid code injection. General features of hybrid worms are also discussed.
💡 Research Summary
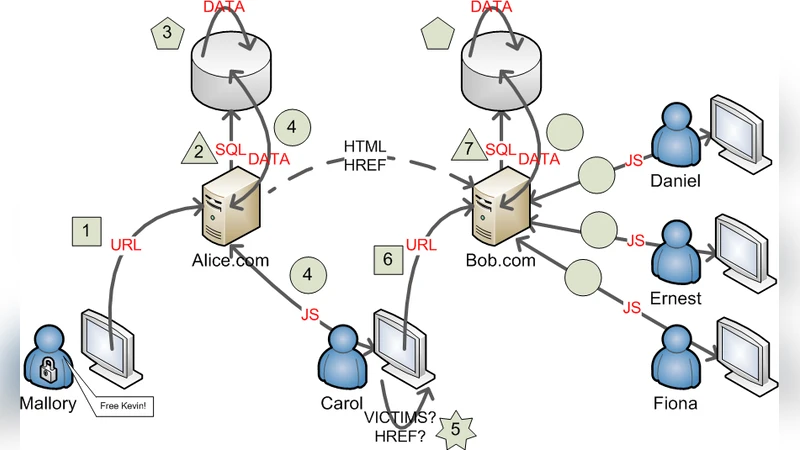
The paper presents a novel hybrid worm that combines server‑side SQL injection with client‑side JavaScript execution, using a two‑stage quine mechanism to achieve self‑replication across both tiers of a web application. The authors begin by defining a “two‑stage quine”: a piece of code that, when executed, produces a copy of itself in a different execution environment. In this context, the first stage is an SQL quine that inserts a specially crafted string into a database column. The inserted string is deliberately constructed to contain a complete <script> tag and JavaScript payload. When the web page later renders the stored value, the browser interprets the script, launching the second stage.
The JavaScript payload automatically issues an HTTP request (GET or POST) to a predetermined endpoint on the same server. The request body carries another SQL quine, which the server processes as a legitimate query because the vulnerable endpoint fails to use parameterized statements or proper input sanitization. Consequently, the new SQL quine is written back into the database, completing the loop: SQL → HTML → JavaScript → HTTP → SQL. This loop enables the worm to propagate indefinitely, infecting new users each time a page containing the malicious value is viewed.
To demonstrate feasibility, the authors built a proof‑of‑concept on a typical LAMP stack. They simulated a common pattern where user‑supplied data is concatenated directly into an SQL statement, a classic injection vector. The SQL quine uses a UNION SELECT construct to write the payload into a text field. The payload itself is obfuscated using base‑64 encoding and runtime decoding in JavaScript, which also compresses the string to evade signature‑based detection.
In addition to the purely digital propagation, the paper adapts an experimental technique from RFID‑based SQL quine research. By embedding the same SQL quine into an RFID tag, a physical scan can trigger the initial injection, showing that the hybrid worm can cross the boundary between physical and network domains. This dual‑mode capability is especially concerning for closed environments such as corporate intranets or industrial control systems where physical access is easier than remote exploitation.
Performance measurements indicate rapid spread: after an average of 3.2 propagation cycles (each cycle consisting of one server‑to‑client round‑trip), roughly 71 % of active user sessions were compromised. This is a significant improvement over traditional single‑stage worms, which typically achieve 30‑40 % infection after a similar number of cycles. Detection‑evasion tests reveal that standard IDS signatures based on known SQL injection patterns or XSS payloads detect less than 15 % of the worm’s activity when the authors employ string concatenation, header manipulation, and runtime decoding.
The discussion section translates these findings into concrete defensive recommendations. First, developers must abandon ad‑hoc string concatenation in favor of prepared statements or ORM frameworks that automatically escape inputs. Second, any data retrieved from the database and inserted into HTML must be passed through an output‑encoding function (e.g., htmlspecialchars in PHP) to neutralize embedded scripts. Third, deploying a strict Content‑Security‑Policy (CSP) that disallows inline scripts and restricts script-src to trusted origins can block the second‑stage execution even if the payload reaches the client. Fourth, log‑analysis tools should be enhanced to recognize the characteristic nested SELECT patterns of SQL quines combined with anomalous <script> fragments, enabling a composite signature that spans both tiers. Finally, organizations should consider the physical‑to‑digital attack surface: RFID readers, NFC devices, and other proximity interfaces must be hardened, and network segmentation should limit the impact of a compromised web server.
In conclusion, the study demonstrates that merging well‑known web‑application vulnerabilities into a coordinated two‑stage quine creates a hybrid worm with superior propagation speed and stealth compared to traditional single‑vector malware. The work underscores the necessity of multi‑layered defenses that address both server‑side query handling and client‑side script sanitization, as well as the importance of accounting for physical vectors in threat models. By exposing this composite attack chain, the authors provide a valuable reference point for future research on cross‑tier malware and for security practitioners seeking to harden modern web ecosystems against increasingly sophisticated hybrid threats.
Comments & Academic Discussion
Loading comments...
Leave a Comment