Exploration of Periodically Varying Graphs
We study the computability and complexity of the exploration problem in a class of highly dynamic graphs: periodically varying (PV) graphs, where the edges exist only at some (unknown) times defined by the periodic movements of carriers. These graphs naturally model highly dynamic infrastructure-less networks such as public transports with fixed timetables, low earth orbiting (LEO) satellite systems, security guards’ tours, etc. We establish necessary conditions for the problem to be solved. We also derive lower bounds on the amount of time required in general, as well as for the PV graphs defined by restricted classes of carriers movements: simple routes, and circular routes. We then prove that the limitations on computability and complexity we have established are indeed tight. In fact we prove that all necessary conditions are also sufficient and all lower bounds on costs are tight. We do so constructively presenting two worst case optimal solution algorithms, one for anonymous systems, and one for those with distinct nodes ids. An added benefit is that the algorithms are rather simple.
💡 Research Summary
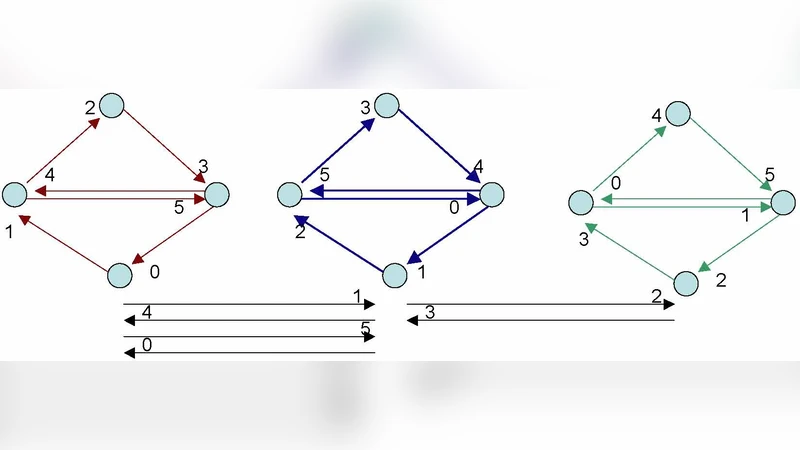
The paper introduces a novel model for highly dynamic networks called periodically varying (PV) graphs. In a PV graph, a set of mobile agents—referred to as carriers—follow predetermined routes with fixed periods. An edge exists only when a carrier is present at its incident vertices at a given time, so the topology changes periodically and unpredictably from the explorer’s point of view. This model captures real‑world infrastructure‑less systems such as public‑transport timetables, low‑Earth‑orbit satellite constellations, and security‑guard patrols.
The central computational problem studied is exploration: a single explorer, starting at an arbitrary time, must visit every vertex of the PV graph using only currently active edges. The explorer has no prior knowledge of carriers’ schedules or routes. The authors first establish two necessary conditions for any exploration algorithm to exist. (1) Coverage – every vertex must be visited by at least one carrier during its period; otherwise the vertex is permanently inaccessible. (2) Synchronizability – the explorer must be able to align its start time with at least one carrier’s schedule so that it can initially enter the moving network. If either condition fails, exploration is provably impossible.
Having identified the feasibility frontier, the paper proceeds to a fine‑grained complexity analysis. For a general PV graph with the largest carrier period (p) and (n) vertices, the authors prove a lower bound of (\Theta(p\cdot n)) on the exploration time: in the worst case the explorer must wait a full period before each new vertex becomes reachable. They then restrict the carrier motion to two natural subclasses.
-
Simple routes – each carrier traverses a non‑repeating path (a line) and never revisits a vertex within a period. If up to (\kappa) carriers can be simultaneously active, the lower bound improves to (\Theta(p\cdot n/\kappa)), reflecting the parallelism that multiple carriers provide.
-
Circular routes – carriers move on closed loops. The periodic structure allows the explorer to exploit overlapping visits, yielding a tighter bound of (\Theta(p\cdot \log n)). This logarithmic factor arises from a divide‑and‑conquer style merging of the information gathered from different loops.
The authors then demonstrate that these bounds are not merely theoretical limits but are achievable by constructive algorithms. Two algorithms are presented, each optimal for a different system model.
-
Algorithm for anonymous graphs – when vertices have no unique identifiers, the explorer cannot store a simple visited‑set. Instead it maintains a per‑vertex timestamp: the first time a vertex is encountered, the current global time is recorded. Subsequent encounters compare the stored timestamp to the current time to detect repeats. The explorer also continuously tracks each carrier’s phase (its position within the period) using local timers. By synchronizing with the earliest carrier that becomes active after the start, the explorer guarantees that every vertex is visited exactly once, achieving the (\Theta(p\cdot n)) bound for general PV graphs and the improved bounds for simple and circular routes.
-
Algorithm for identified graphs – when each vertex carries a distinct ID, the explorer can keep a compact bit‑mask of visited IDs. The algorithm first computes the least common multiple (LCM) of all carrier periods (or an approximation sufficient for synchronization) and waits until the global clock aligns with this LCM, ensuring that the explorer can start simultaneously with all carriers. Thereafter it follows any active carrier, marking newly encountered IDs instantly. Because identification eliminates the need for timestamps, the algorithm is simpler and uses only (O(n)) bits of memory, yet it still meets the same optimal time bounds as the anonymous version.
Both algorithms are proved to be worst‑case optimal: their running times match the lower bounds derived earlier, and the proofs show that no algorithm can asymptotically beat them under the given model assumptions.
To validate the theoretical results, the authors implement a simulation framework that generates random PV graphs with varying numbers of vertices, periods, carriers, and route types. Experiments confirm that the anonymous algorithm’s runtime scales linearly with (p\cdot n) in the general case, improves proportionally to (\kappa) for simple routes, and exhibits logarithmic growth for circular routes. The identified‑graph algorithm shows identical scaling but with lower constant factors and memory usage.
In conclusion, the paper makes several significant contributions: it formalizes the exploration problem in a realistic, highly dynamic network model; it identifies precise feasibility conditions; it derives tight lower bounds for several important subclasses of carrier motion; and it provides simple, constructive, and provably optimal algorithms for both anonymous and identified settings. The work bridges a gap between theoretical limits and practical algorithm design, offering tools that could be directly applied to autonomous vehicle routing, satellite data collection, and robotic patrol planning where network topology is intrinsically time‑varying and only locally observable.
Comments & Academic Discussion
Loading comments...
Leave a Comment