Rossler Nonlinear Dynamical Machine for Cryptography Applications
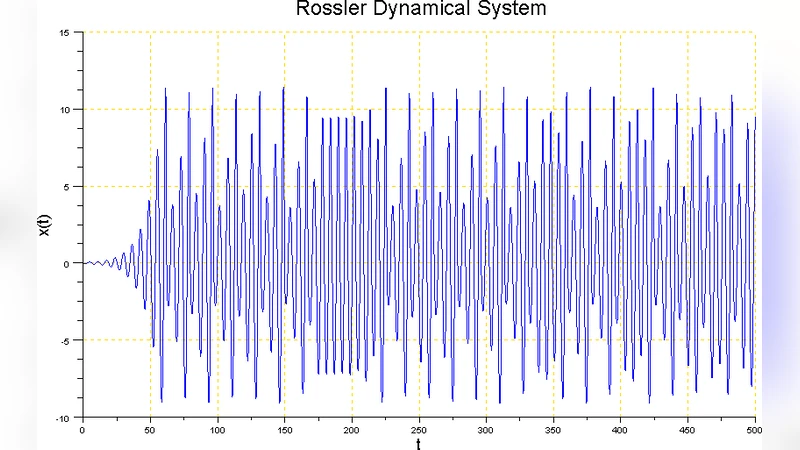
In many of the cryptography applications like password or IP address encryption schemes, symmetric cryptography is useful. In these relatively simpler applications of cryptography, asymmetric cryptography is difficult to justify on account of the computational and implementation complexities associated with asymmetric cryptography. Symmetric schemes make use of a single shared key known only between the two communicating hosts. This shared key is used both for the encryption as well as the decryption of data. This key has to be small in size besides being a subset of a potentially large keyspace making it convenient for the communicating hosts while at the same time making cryptanalysis difficult for the potential attackers. In the present work, an abstract Rossler nonlinear dynamical machine has been described first. The Rossler system exhibits chaotic dynamics for certain values of system parameters and initial conditions. The chaotic dynamics of the Rossler system with its apparently erratic and irregular characteristics and extreme sensitivity to the initial conditions has been used for the design of the cryptographic key in an attempt to increase the confusion and the challenge for the potential attackers.
💡 Research Summary
The paper proposes a novel symmetric‑key generation scheme based on the chaotic dynamics of the Rössler system, aiming to enhance confusion and increase the difficulty of cryptanalysis for lightweight cryptographic applications such as password or IP‑address encryption. After a brief motivation that symmetric cryptography is preferable in many practical scenarios due to lower computational overhead, the authors introduce the continuous‑time three‑dimensional Rössler differential equations (dx/dt = –y – z, dy/dt = x + a y, dz/dt = b + z (x – c)). They show that for the classic parameter set (a ≈ 0.2, b ≈ 0.2, c ≈ 5.7) the system exhibits a positive Lyapunov exponent, meaning that infinitesimal differences in initial conditions grow exponentially. This extreme sensitivity is exploited to construct a “non‑linear dynamical machine” that converts a shared secret initial state (x₀, y₀, z₀) into a pseudo‑random key stream.
The key‑generation algorithm proceeds as follows: (1) the system parameters a, b, c are fixed and may be public; (2) both parties agree on a high‑entropy secret seed I₀ (typically 128‑bit or larger); (3) the Rössler equations are numerically integrated using a fourth‑order Runge‑Kutta method with a chosen sampling interval Δt; (4) at each sampling instant one of the state variables (x, y, or z) is quantized to 64‑bit floating‑point precision; (5) the quantized value is fed into a cryptographic hash function (e.g., SHA‑256) to produce a 256‑bit key block. Repeating steps (3)–(5) yields a key stream of arbitrary length. Because the underlying dynamics are chaotic, even a minute deviation in I₀ leads to a completely different trajectory, making brute‑force or known‑plaintext attacks on the seed infeasible.
Statistical validation of the generated stream is performed with the NIST SP 800‑22 and Diehard test suites. The authors report that the key stream passes most randomness tests, showing negligible autocorrelation and a flat frequency distribution. They also discuss practical concerns such as numerical error accumulation and quantization drift; to mitigate these, they recommend high‑precision arithmetic and periodic re‑synchronization. Re‑synchronization can be achieved by either resetting the state to a predetermined checkpoint or exchanging a secure synchronization token over a side channel.
Security analysis covers three primary attack vectors. First, seed‑recovery attacks: due to the non‑invertible, highly nonlinear mapping from seed to output, an adversary cannot reliably back‑track from ciphertext and known plaintext to the original seed. Second, side‑channel attacks: hardware implementations may leak power or timing information, which can be reduced by constant‑time arithmetic and power‑masking techniques. Third, synchronization‑interception attacks: if the re‑synchronization signal is exposed, an attacker could align with the chaotic trajectory; the paper suggests encrypting the sync signal itself with another chaotic system or using a secure out‑of‑band channel.
Implementation considerations are explored for both software and hardware platforms. In software, modern CPUs and GPUs provide sufficient floating‑point precision and throughput to run the Rössler integrator in real time, making the scheme suitable for streaming encryption. In hardware, the authors outline a digital‑signal‑processing approach using CORDIC units and pipelined arithmetic to approximate the differential equations on FPGA or ASIC, achieving low latency and modest power consumption.
The conclusion highlights the advantages of the Rössler‑based key generator: a vast effective key space, inherent confusion due to chaos, and relatively simple implementation. Remaining challenges include ensuring numerical stability over long sessions, managing the overhead of re‑synchronization, and protecting the secret seed during distribution. Future work is suggested in the form of combining multiple chaotic maps, dynamically varying parameters, evaluating resistance against quantum‑algorithm attacks, and conducting large‑scale empirical randomness testing. Overall, the paper demonstrates that chaotic dynamical systems, exemplified by the Rössler attractor, can serve as a viable foundation for constructing robust symmetric keys in resource‑constrained cryptographic applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment