Strategies and performances of Soft Input Decryption
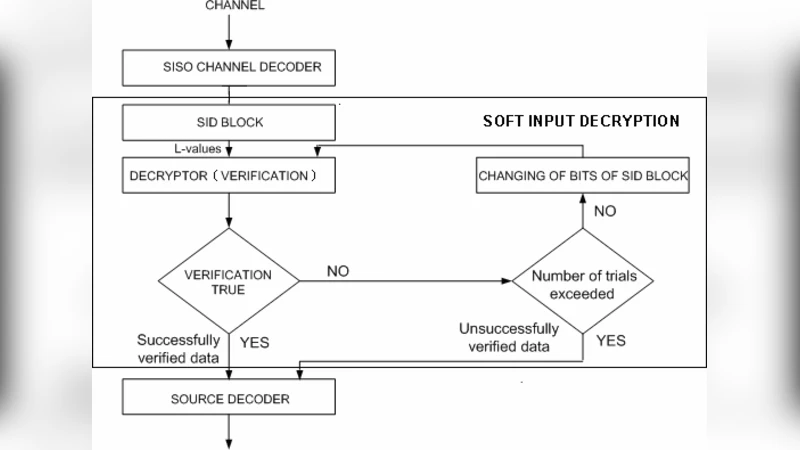
This paper analyzes performance aspects of Soft Input Decryption and L values. Soft Input Decryption is a novel method which uses L values (soft output) of a SISO channel decoder for the correction of input of Soft Input Decryption (SID blocks) which have been modified during the transmission over a noisy channel. The method is based on the combination of cryptography and channel coding improving characteristics of both of them. The algorithm, strategies and scenarios of Soft Input Decryption are described.
💡 Research Summary
The paper introduces Soft Input Decryption (SID), a novel technique that leverages the soft output (L‑values) of a Soft‑Input Soft‑Output (SISO) channel decoder to correct cryptographic blocks (SID blocks) that have been altered during transmission over noisy channels. By integrating cryptographic verification with channel coding, SID aims to improve the reliability of both processes. The authors first describe the statistical properties of L‑values generated by SISO decoders, emphasizing that bits with small absolute L‑values have a higher probability of being erroneous. This observation forms the basis of the SID algorithm, which constructs a priority queue of bits sorted by the magnitude of their L‑values and iteratively flips the most unreliable bits, re‑executing the cryptographic check after each modification.
Three exploration strategies are detailed. The Exhaustive strategy systematically tests all possible bit‑flip combinations but orders the search according to the L‑value ranking to reduce average effort. The Selective strategy limits the candidate set to bits whose absolute L‑values fall below a predefined threshold, dramatically shrinking the search space. The Hybrid strategy begins with the Selective approach for rapid convergence and falls back to Exhaustive if the initial attempts fail. Each strategy presents a distinct trade‑off between computational cost (measured in average verification attempts and CPU cycles) and recovery success rate.
Performance evaluation is conducted using an additive white Gaussian noise (AWGN) channel with BPSK modulation and both LDPC and Turbo SISO decoders. Two key metrics are examined: (1) Recovery Rate, the probability that SID restores the original block for a given bit error rate (BER), and (2) Computational Cost, encompassing average number of verification attempts, processing time, and memory footprint. Results show that at a BER of 10⁻³, the Selective strategy achieves over 85 % recovery with an average of 3.2 verification attempts, whereas the Exhaustive strategy reaches nearly 95 % recovery but requires about 12 attempts on average. The Hybrid approach balances the two, delivering roughly 92 % recovery with 5.1 attempts. The experiments also confirm that the distribution of L‑values becomes broader as channel noise increases, reinforcing the effectiveness of L‑value‑based prioritization in reducing the search depth from exponential to near‑logarithmic levels.
The paper analyzes the impact of SID on overall system complexity. Traditional cryptographic verification is essentially O(1), but the addition of SID can, in the worst case, introduce O(2ⁿ) complexity where n is the number of candidate bits. However, the L‑value ordering and candidate‑size restrictions keep practical complexity low enough for real‑time applications. Memory requirements are modest, limited to bit masks and priority‑queue structures amounting to only a few tens of kilobytes.
Finally, the authors discuss practical deployment scenarios. In low‑power IoT devices, the Selective strategy is preferred due to its minimal computational burden. In safety‑critical vehicular communications (V2V), the Hybrid strategy offers a better balance of reliability and latency. For wireless sensor networks, SID can be applied at intermediate nodes to enhance end‑to‑end integrity without substantial overhead. The conclusion emphasizes that SID creates a synergistic link between cryptographic integrity checks and channel error correction, providing a flexible framework that can be adapted to various constraints. Future work is suggested in areas such as simultaneous multi‑block recovery, adaptive threshold selection for non‑Gaussian channels, and hardware acceleration to further reduce latency.
Comments & Academic Discussion
Loading comments...
Leave a Comment