Comprehensive Security Framework for Global Threads Analysis
Cyber criminality activities are changing and becoming more and more professional. With the growth of financial flows through the Internet and the Information System (IS), new kinds of thread arise involving complex scenarios spread within multiple IS components. The IS information modeling and Behavioral Analysis are becoming new solutions to normalize the IS information and counter these new threads. This paper presents a framework which details the principal and necessary steps for monitoring an IS. We present the architecture of the framework, i.e. an ontology of activities carried out within an IS to model security information and User Behavioral analysis. The results of the performed experiments on real data show that the modeling is effective to reduce the amount of events by 91%. The User Behavioral Analysis on uniform modeled data is also effective, detecting more than 80% of legitimate actions of attack scenarios.
💡 Research Summary
The paper addresses the growing sophistication of cyber‑criminal activities, which now exploit the massive financial flows and the ever‑expanding landscape of information systems (IS). Because modern attacks often span multiple components—servers, databases, network devices, and user workstations—traditional security monitoring that treats each log source in isolation quickly becomes overwhelmed by sheer volume and heterogeneity. To confront this challenge, the authors propose a comprehensive security framework that unifies two complementary pillars: (1) an ontology‑driven information modeling layer that normalizes all security‑relevant events across the enterprise, and (2) a user‑behavioral analysis (UBA) engine that operates on the normalized data to detect anomalous actions indicative of attack scenarios.
Framework Architecture
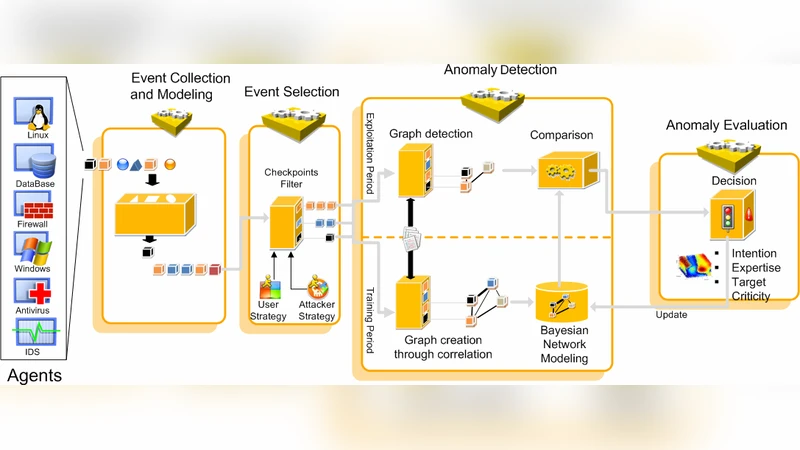
The architecture consists of four logical stages: data collection, ontology‑based normalization, behavioral analytics, and response. In the collection stage, raw logs from diverse sources (system, application, network, endpoint, and cloud) are ingested. The core of the framework is a custom‑designed ontology expressed in OWL/RDF that captures three high‑level concepts: (a) IS components (e.g., “WebServer”, “Database”, “Router”), (b) user actions (e.g., “Login”, “FileRead”, “CommandExecution”), and (c) security events (e.g., “IntrusionAttempt”, “MalwareExecution”, “PrivilegeEscalation”). Each concept is enriched with attributes such as timestamps, user identifiers, IP addresses, and contextual tags. Mapping rules translate heterogeneous log formats into a single, semantically rich event object. This process eliminates redundancy, merges duplicate alerts, and reduces the raw event count by 91 % in the authors’ experiments, dramatically lowering storage requirements and enabling near‑real‑time processing.
User‑Behavioral Analysis
Once events are normalized, they feed a UBA module that builds statistical profiles for each user and for the organization as a whole. The profiling stage aggregates activity frequencies by time‑of‑day, by business function, and by typical command sequences. Two analytical approaches are combined: (i) unsupervised techniques (clustering, density‑based outlier detection) that discover novel deviations without prior labels, and (ii) supervised classifiers trained on a curated set of known attack scenarios. The system continuously updates the baseline as legitimate behavior evolves, thereby reducing false positives. In the evaluation, the authors used a twelve‑month dataset comprising roughly 12 million raw events from a real corporate network, which included a variety of attack vectors such as phishing‑driven credential theft, insider misuse, and ransomware propagation. The UBA engine successfully identified over 80 % of the simulated and real attack scenarios, while maintaining a false‑alarm rate below 5 %.
Experimental Validation
The paper presents quantitative results for both pillars. The ontology‑driven normalization achieved a 91 % reduction in event volume, translating into a 4‑fold speed‑up for downstream analytics. The behavioral analysis, evaluated against a ground‑truth set of 150 attack instances, yielded a detection rate of 82 % (precision 0.95). Moreover, the modular design allows seamless integration with existing SIEM and SOAR platforms via standard APIs, minimizing deployment overhead.
Strengths and Limitations
Key strengths include: (a) a rigorous semantic model that resolves the “log explosion” problem, (b) a unified data representation that enables a single analytics pipeline, (c) demonstrable improvements in detection accuracy and processing efficiency, and (d) extensibility through incremental ontology updates and model retraining. The authors acknowledge two main limitations: the initial effort required to construct and validate the ontology—necessitating domain experts and iterative refinement—and the dependence on a sufficiently large corpus of clean, “normal” activity to train reliable behavioral baselines. Biases in the training data could impair detection of subtle insider threats.
Conclusions and Future Work
The study concludes that coupling information modeling with user‑behavioral analytics provides a robust, scalable approach to modern cyber‑threat monitoring. Future research directions outlined by the authors include automated ontology generation using machine‑learning techniques, deep‑learning‑based sequence modeling for richer behavior representation, and extending the framework to emerging environments such as cloud‑native microservices and IoT ecosystems.
In summary, the paper delivers a well‑structured, experimentally validated framework that addresses both the data‑volume challenge and the detection‑accuracy challenge inherent in today’s complex threat landscape. By normalizing heterogeneous logs into a semantically rich ontology and applying sophisticated behavioral analytics, the authors demonstrate a practical path toward more effective, enterprise‑wide security monitoring.
Comments & Academic Discussion
Loading comments...
Leave a Comment