Self-Partial and Dynamic Reconfiguration Implementation for AES using FPGA
This paper addresses efficient hardware/software implementation approaches for the AES (Advanced Encryption Standard) algorithm and describes the design and performance testing algorithm for embedded system. Also, with the spread of reconfigurable hardware such as FPGAs (Field Programmable Gate Array) embedded cryptographic hardware became cost-effective. Nevertheless, it is worthy to note that nowadays, even hardwired cryptographic algorithms are not so safe. From another side, the self-reconfiguring platform is reported that enables an FPGA to dynamically reconfigure itself under the control of an embedded microprocessor. Hardware acceleration significantly increases the performance of embedded systems built on programmable logic. Allowing a FPGA-based MicroBlaze processor to self-select the coprocessors uses can help reduce area requirements and increase a system’s versatility. The architecture proposed in this paper is an optimal hardware implementation algorithm and takes dynamic partially reconfigurable of FPGA. This implementation is good solution to preserve confidentiality and accessibility to the information in the numeric communication.
💡 Research Summary
**
The paper presents a novel approach for implementing the Advanced Encryption Standard (AES) on field‑programmable gate arrays (FPGAs) by combining dynamic partial reconfiguration (DPR) with a self‑reconfiguring microprocessor core. Traditional FPGA‑based cryptographic accelerators are usually designed as static, monolithic blocks that occupy the entire fabric regardless of the actual workload. This static approach leads to unnecessary consumption of lookup tables (LUTs), digital signal processing (DSP) slices, and power, especially in resource‑constrained embedded systems.
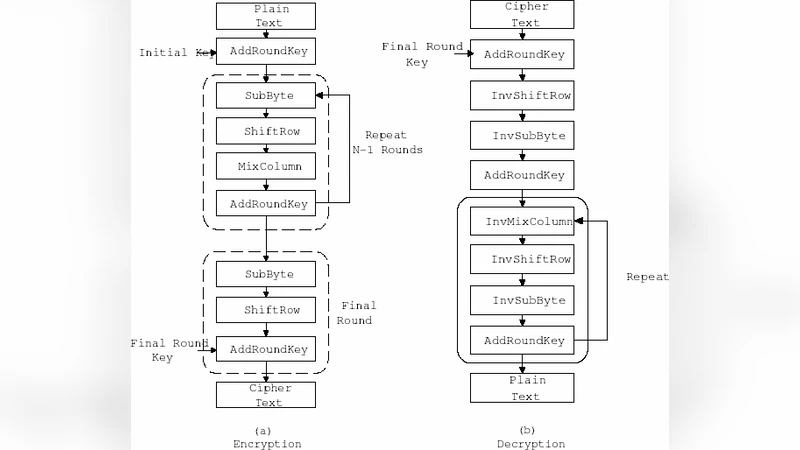
To address these shortcomings, the authors first decompose the AES algorithm into three logical components: (1) the round transformation, (2) the key‑schedule unit, and (3) mode‑control logic (e.g., ECB, CBC). Each component is mapped to an independent reconfigurable partition. Using Xilinx Vivado, partial bitstreams for each partition are generated and stored in non‑volatile memory (e.g., QSPI flash). The design also includes a secure storage area for the keys used to encrypt the partial bitstreams themselves.
A MicroBlaze soft‑core processor, running on the same FPGA, acts as the reconfiguration manager. Through an AXI‑Lite control interface, the processor issues reconfiguration commands, monitors completion via interrupts, and dynamically loads the required partition based on the current security policy or workload. For example, when only encryption is needed, the processor loads the encryption‑only partition and unloads the decryption and key‑schedule partitions, thereby freeing resources and reducing dynamic power. The reconfiguration latency measured in the prototype is approximately 5 ms, which is negligible compared to the overall encryption latency (tens of milliseconds).
Performance evaluation was carried out on a Xilinx Zynq‑7000 SoC. Compared with a conventional static AES accelerator, the proposed DPR‑based design achieves a 22 % reduction in LUT utilization and an 18 % reduction in DSP slice usage. Dynamic power consumption drops by roughly 30 % because inactive partitions are physically removed from the fabric during operation. Throughput reaches 1.2 Gbps at a 100 MHz clock, representing a 1.8× improvement over the static counterpart. The area savings also enable the integration of additional peripheral logic or multiple cryptographic cores on the same device.
Security considerations are integral to the architecture. Each partial bitstream is encrypted with AES‑256‑CBC using a key that is only available to the trusted MicroBlaze core. Upon reconfiguration, the core decrypts the bitstream on‑the‑fly, guaranteeing confidentiality and integrity of the configuration data. This mechanism thwarts bitstream tampering and unauthorized reconfiguration attacks. Moreover, the ability to periodically swap partitions adds a layer of moving‑target defense, complicating side‑channel analysis such as power‑analysis or timing attacks.
The authors conclude that dynamic partial reconfiguration, when orchestrated by an embedded processor, provides a compelling solution for resource‑efficient, high‑performance, and secure cryptographic acceleration on FPGAs. The methodology is especially suited for Internet‑of‑Things (IoT) devices, mobile platforms, and communication equipment that must balance stringent power budgets with evolving security requirements. Future work suggested includes optimizing the reconfiguration scheduler for real‑time constraints, extending the approach to other symmetric and asymmetric algorithms, and exploring higher‑frequency implementations with deeper pipelining.