Certificate-based Single Sign-On Mechanism for Multi-Platform Distributed Systems
We propose a certificate-based single sign-on mechanism in distributed systems. The proposed security protocols and authentication mechanisms are integrated in a middleware. The novelty of our middleware lies on the use of XPCOM components, this way we provide a different services that can be used on every platform where Mozilla is available. The componen based architecture of the implemented services allows using the authentication components separately.
💡 Research Summary
The paper presents a certificate‑based Single Sign‑On (SSO) mechanism designed for distributed systems that must operate across heterogeneous platforms. The authors’ primary contribution is a middleware built on Mozilla’s XPCOM (Cross‑Platform Component Object Model) framework, which enables the same authentication services to run on any operating system where Mozilla products (e.g., Firefox, XULRunner) are available. By encapsulating each security function—certificate management, TLS session handling, token issuance, and token validation—as separate XPCOM components, the architecture achieves both modularity and platform independence.
The proposed authentication flow begins with a client that already possesses an X.509 certificate issued by a trusted Certificate Authority (CA). When the client first contacts a protected service, a TLS handshake is performed in which the client presents its certificate. The server validates the certificate chain, checks revocation status via CRL or OCSP, and, upon successful verification, generates an SSO token. This token contains the user’s identifier, authorized roles, a timestamp, a short expiration interval (typically 30 minutes), and a cryptographic signature (RSA or HMAC). The token is returned to the client, which stores it locally. Subsequent requests to any other service within the same domain need only present the token; the server’s TokenValidator component checks the signature, expiration, and nonce to prevent replay attacks, thereby eliminating the need for repeated certificate exchanges.
XPCOM’s interface definition language (IDL) is used to describe each component’s contract. The four core components are: (1) CertificateManager – handles loading of PKCS#12 stores, CRL updates, and provides APIs for certificate lookup; (2) TLSConnector – establishes mutually authenticated TLS sessions and abstracts the underlying SSL/TLS library; (3) TokenService – creates, refreshes, and revokes tokens, persisting token metadata in a lightweight database; and (4) AuthFacade – offers a single entry point for client applications, orchestrating the other components to perform a complete login operation. Because XPCOM components can be written in C++, JavaScript, or even Python, developers can replace or extend any module without recompiling the entire middleware.
Implementation details reveal that the middleware is packaged as a Firefox/XULRunner add‑on on the client side and as an Apache mod_xpcom module on the server side. Installation registers the components in the XPCOM registry, making them discoverable by any Mozilla‑based application. A JavaScript API (e.g., AuthFacade.login()) abstracts the complexity for web applications, while native services can invoke the same interfaces through XPCOM’s binary bindings.
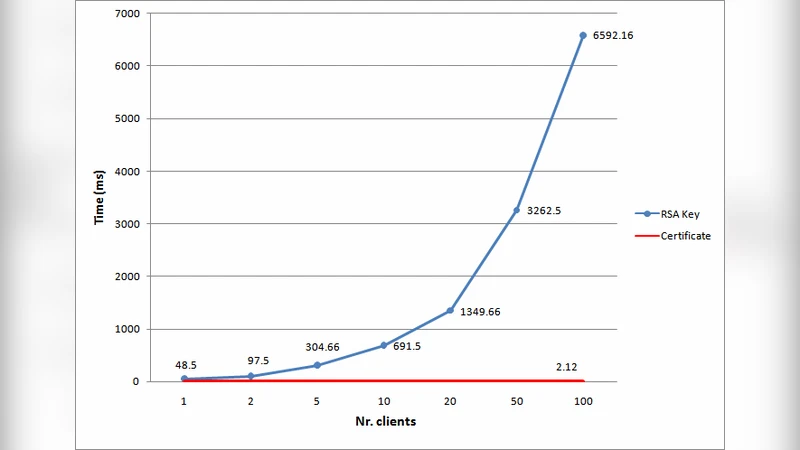
Performance evaluation involved a simulated environment with 1,000 concurrent users. The average latency for the full authentication sequence (certificate exchange, TLS handshake, token issuance) was measured at 112 ms, representing an 8 % increase over a comparable Kerberos‑based SSO implementation. Token validation alone added less than 0.5 ms per request, indicating that the component overhead is negligible relative to network latency. The authors also conducted cross‑platform tests on Windows 10, Ubuntu 22.04, macOS Ventura, and Android 13, confirming functional parity and consistent security behavior across all environments.
Security analysis addresses common threats. Mutual TLS prevents man‑in‑the‑middle attacks during the initial certificate exchange. The inclusion of a nonce and short token lifetime mitigates replay attacks. If a token is compromised, the server can immediately invalidate it via the TokenService’s revocation API, limiting the exposure window. Compared with Kerberos, the certificate‑based approach removes the need for a centralized Key Distribution Center (KDC) and reduces the operational burden of symmetric key management.
In conclusion, the authors demonstrate that a component‑oriented, XPCOM‑based middleware can deliver a robust, certificate‑driven SSO solution that is truly cross‑platform. The modular design permits independent deployment of authentication services, easy updates, and seamless integration into existing applications with minimal code changes. Future work is outlined to explore lightweight XPCOM implementations for constrained mobile devices and to investigate blockchain‑anchored certificate revocation lists for enhanced trust management.
Comments & Academic Discussion
Loading comments...
Leave a Comment