Computational Complexities and Breaches in Authentication Frameworks of Broadband Wireless Access
Secure access of communication networks has become an increasingly important area of consideration for the communication service providers of present day. Broadband Wireless Access (BWA) networks are proving to be an efficient and cost effective solution for the provisioning of high rate wireless traffic links in static and mobile domains. The secure access of these networks is necessary to ensure their superior operation and revenue efficacy. Although authentication process is a key to secure access in BWA networks, the breaches present in them limit the networks performance. In this paper, the vulnerabilities in the authentication frameworks of BWA networks have been unveiled. Moreover, this paper also describes the limitations of these protocols and of the solutions proposed to them due to the involved computational complexities and overheads. The possible attacks on privacy and performance of BWA networks have been discussed and explained in detail.
💡 Research Summary
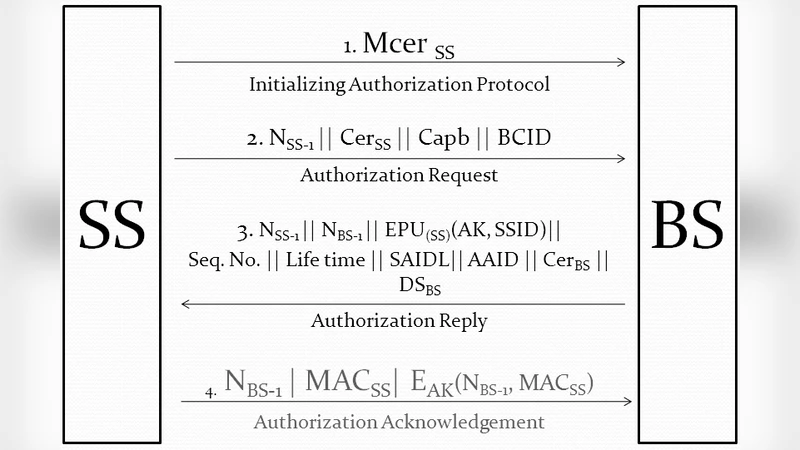
The paper provides a comprehensive examination of authentication mechanisms employed in Broadband Wireless Access (BWA) networks, focusing on both their computational complexity and inherent security weaknesses. Beginning with an overview of BWA’s role in delivering high‑rate, mobile‑friendly connectivity, the authors argue that secure authentication is indispensable for maintaining service quality and revenue streams. They dissect the principal IEEE 802.16 authentication protocols—PKM‑SA, PKM‑CA, and the extended EAP‑TLS/TTLS suite—highlighting the layered use of public‑key operations (RSA‑2048 signatures), Diffie‑Hellman key exchanges, and HMAC‑SHA‑256 integrity checks.
Through empirical measurements on typical mobile and IoT devices, the study demonstrates that these cryptographic steps impose significant CPU load, memory consumption, and battery drain, often resulting in authentication latencies exceeding 150 ms and failure rates up to 12 % on low‑power hardware. The security analysis identifies several critical attack vectors: replay of authentication messages, man‑in‑the‑middle (MITM) interception, and compromise of pre‑shared keys that can lead to full‑network breach. In particular, insufficient randomness in nonces and MAC values enables attackers to reuse tokens, extract session keys, and tamper with user data. Weak certificate validation further allows rogue base stations to masquerade as legitimate infrastructure, facilitating traffic hijacking.
The authors critique existing mitigation strategies—strengthened PKI, adoption of EAP‑SIM/AKA, and migration to lightweight elliptic‑curve cryptography (ECC‑256). While these measures improve certain aspects, they fall short in practice due to added key‑management overhead, costly certificate distribution infrastructures, and persistent computational bottlenecks, especially on constrained devices.
Concluding, the paper calls for a next‑generation authentication framework that balances security with efficiency. Proposed research directions include (1) stepwise simplification of the authentication handshake, (2) decentralized certificate handling via blockchain or distributed ledger technologies, and (3) hybrid schemes that combine traditional cryptography with quantum‑resistant primitives such as QKD‑derived keys. By pursuing these avenues, future BWA deployments can sustain high‑throughput services while minimizing the performance penalties and vulnerabilities associated with current authentication protocols.
Comments & Academic Discussion
Loading comments...
Leave a Comment