A Survey of Attacks, Security Mechanisms and Challenges in Wireless Sensor Networks
Wireless Sensor networks (WSN) is an emerging technology and have great potential to be employed in critical situations like battlefields and commercial applications such as building, traffic surveillance, habitat monitoring and smart homes and many more scenarios. One of the major challenges wireless sensor networks face today is security. While the deployment of sensor nodes in an unattended environment makes the networks vulnerable to a variety of potential attacks, the inherent power and memory limitations of sensor nodes makes conventional security solutions unfeasible. The sensing technology combined with processing power and wireless communication makes it profitable for being exploited in great quantity in future. The wireless communication technology also acquires various types of security threats. This paper discusses a wide variety of attacks in WSN and their classification mechanisms and different securities available to handle them including the challenges faced.
💡 Research Summary
The surveyed paper provides a comprehensive overview of security issues in Wireless Sensor Networks (WSNs), focusing on the taxonomy of attacks, the spectrum of defensive mechanisms, and the open research challenges that arise from the intrinsic constraints of sensor nodes. The authors begin by highlighting the broad applicability of WSNs—from battlefield surveillance to smart homes and environmental monitoring—and immediately point out that the unattended deployment of low‑power, memory‑limited nodes makes conventional security solutions impractical.
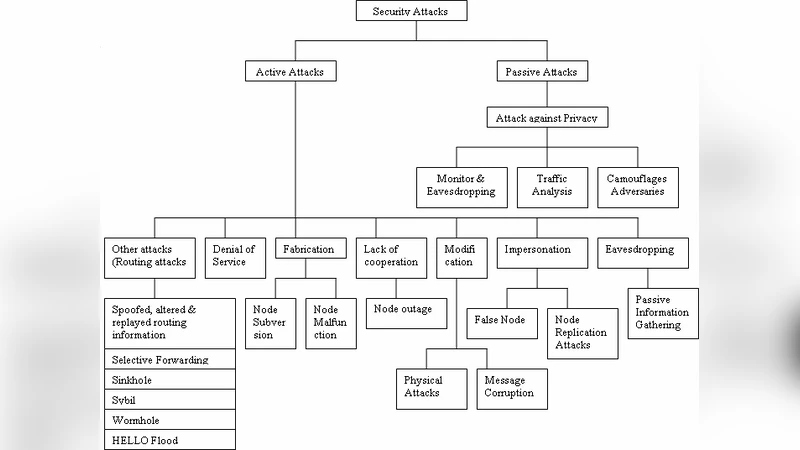
The attack classification is organized into four layers: physical, data‑link, network, and application. Physical‑layer threats include node capture, tampering, and destruction; once a node is captured, any stored cryptographic material can be extracted, compromising the entire network’s trust base. At the data‑link layer, eavesdropping, replay, and denial‑of‑service (DoS) attacks are prevalent, with particular emphasis on the manipulation of MAC‑layer protocols to inject forged routing information or to desynchronize time‑synchronization services. Network‑layer attacks encompass packet spoofing, black‑hole, gray‑hole, and wormhole attacks, as well as more sophisticated replication and distributed denial‑of‑service campaigns that disrupt routing paths and exhaust node energy. Application‑layer threats target data integrity, privacy, and service availability, often through large‑scale data flooding or malicious data alteration.
In response to these threats, the paper surveys a range of security mechanisms that have been adapted for the constrained WSN environment. Lightweight symmetric encryption algorithms such as AES‑128, RC5, and Skipjack are discussed, noting their low computational overhead but also their dependence on robust key management. Public‑key solutions based on Elliptic Curve Cryptography (ECC) are presented as viable alternatives because they achieve comparable security with shorter key lengths, thereby reducing energy consumption. The authors review key management schemes—including pre‑distribution, dynamic key renewal, and protocol‑specific approaches like LEAP, SPINS, and TinySec—highlighting how they aim to limit the impact of node capture while preserving scalability. Authentication techniques covered include Message Authentication Codes (MACs), one‑time passwords, and emerging blockchain‑inspired trust propagation models designed to prevent message forgery and node impersonation. Intrusion detection systems (IDS) tailored for WSNs are also examined; these systems monitor anomalous traffic patterns, routing inconsistencies, and abnormal power usage to flag potential attacks in real time. Additional defensive strategies such as trust‑based routing, multipath forwarding, and hash‑chain integrity checks are described as complementary layers of protection.
Despite the breadth of existing solutions, the paper identifies several persistent challenges. First, the trade‑off between security strength and energy consumption remains a central obstacle; even lightweight cryptographic primitives can significantly shorten node lifetimes if not carefully tuned. Second, many key management architectures rely on centralized authorities, creating single points of failure that are unacceptable in large‑scale, dynamic deployments. Third, the lack of adaptive security policies that can respond to topology changes, node additions, or failures hampers long‑term resilience. Fourth, the impending advent of quantum computing raises concerns about the longevity of current ECC‑based schemes, prompting a call for research into post‑quantum, resource‑efficient algorithms. Finally, the authors note a gap between simulation‑based evaluations and real‑world deployments; extensive field testing is needed to validate the practicality of proposed mechanisms under realistic environmental conditions.
In conclusion, the survey emphasizes that effective WSN security must integrate energy‑aware cryptography, distributed and self‑healing key management, adaptive trust models, and lightweight intrusion detection into a cohesive framework. Future work should focus on harmonizing these components to produce scalable, low‑maintenance solutions capable of providing real‑time protection in heterogeneous, large‑scale sensor networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment