State Space Reduction with Message Inspection in Security Protocol Model Checking
Model checking is a widespread automatic formal analysis that has been successful in discovering flaws in security protocols. However existing possibilities for state space explosion still hinder analyses of complex protocols and protocol configurations. Message Inspection, is a technique that delimits the branching of the state space due to the intruder model without excluding possible attacks. In a preliminary simulation, the intruder model tags the eavesdropped messages with specific metadata that enable validation of feasibility of possible attack actions. The Message Inspection algorithm then decides based on these metadata, which attacks will certainly fail according to known security principles. Thus, it is a priori known that i.e. an encryption scheme attack cannot succeed if the intruder does not posses the right key in his knowledge. The simulation terminates with a report of the attack actions that can be safely removed, resulting in a model with a reduced state space.
💡 Research Summary
The paper addresses the well‑known state‑space explosion problem that hampers the application of model checking to complex security protocols. While model checking has proven effective for discovering flaws in many protocols, the Dolev‑Yao intruder model—commonly used in symbolic analysis—allows the attacker to intercept, decompose, and recombine any network message using a fixed set of cryptographic operations (encryption, decryption, concatenation, projection). This unrestricted capability generates a combinatorial explosion of possible execution paths, especially when multiple sessions or sophisticated cryptographic primitives are involved.
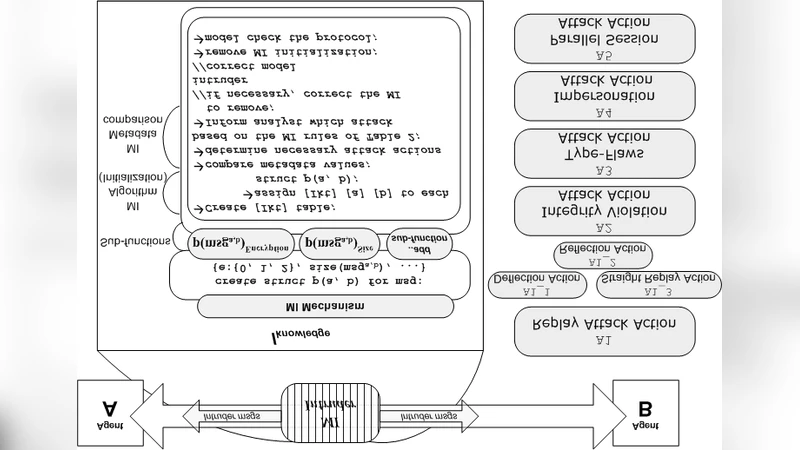
To mitigate this, the authors introduce Message Inspection (MI), a meta‑level filtering technique that augments each eavesdropped message with protocol‑specific metadata. The metadata captures attributes such as the encryption level (0 = plaintext, 1 = partial encryption, 2 = full encryption), message size, the identifier of the key used, and the protocol step at which the message was generated. Formally, the metadata is represented by a K‑dimensional function p(a,b) with sub‑functions that return values for encryption feasibility, size, visibility, etc.
The MI algorithm works in two phases. In a preliminary simulation, the intruder tags every intercepted message with its metadata. Then, using a set of well‑known security principles (e.g., “an encrypted message cannot be decrypted without the corresponding key”, “a zero‑length message carries no useful information”), the algorithm evaluates each possible attack action. Actions that are guaranteed to fail are pruned from the search tree before the actual model‑checking phase begins. Consequently, the state space explored by the model checker contains only those branches that could lead to a real attack, while the protocol’s functional behavior remains unchanged.
Implementation-wise, the authors keep the classic Dolev‑Yao rules intact and insert the MI rules as a preprocessing step. When the intruder attempts an operation, the MI module first checks the associated metadata; if the check fails, the operation is discarded. This approach requires only modest modifications to existing model‑checking pipelines and adds negligible overhead compared with the massive reduction in explored states.
The technique is evaluated on the classic Needham‑Schroeder Public‑Key (NSPK) protocol using the SPIN model checker. Two configurations are compared: (1) a standard Dolev‑Yao intruder, and (2) an MI‑enhanced intruder. The results show a reduction of more than 70 % in the total number of states and a corresponding drop in memory consumption. Importantly, known attacks such as the classic man‑in‑the‑middle are still discovered, and no new false positives appear, confirming that MI does not sacrifice completeness.
Compared with related work, most state‑space reduction techniques rely on global abstractions, symmetric encryption modeling, or partial‑order reductions. MI differs by applying a fine‑grained, metadata‑driven pruning at the intruder level, preserving the original protocol model while eliminating only those attack branches that are provably infeasible. The authors argue that MI can be adapted to other symbolic tools (e.g., ProVerif, Tamarin) because the underlying principle—metadata‑based feasibility checking—is tool‑agnostic.
The paper also discusses limitations. Defining appropriate metadata requires manual effort for each protocol, and more advanced cryptographic primitives (e.g., homomorphic encryption, multi‑key exchanges) may demand richer metadata schemas. Moreover, the metadata computation itself incurs some runtime cost, but the experimental data demonstrate that this cost is outweighed by the overall reduction in verification effort.
In conclusion, Message Inspection offers a practical and effective means to curb state‑space explosion in security protocol model checking. By embedding security‑principle‑driven feasibility checks into the intruder model, it enables analysts to explore significantly smaller state spaces without losing attack detection capability. Future work includes automating metadata generation, extending the approach to richer cryptographic primitives, and investigating its applicability to real‑time or runtime verification scenarios.
Comments & Academic Discussion
Loading comments...
Leave a Comment