Tracing Technique for Blaster Attack
Blaster worm of 2003 is still persistent, the infection appears to have successfully transitioned to new hosts as the original systems are cleaned or shut off, suggesting that the Blaster worm, and other similar worms, will remain significant Internet threats for many years after their initial release. This paper is to propose technique on tracing the Blaster attack from various logs in different OSI layers based on fingerprint of Blaster attack on victim logs, attacker logs and IDS alert log. The researchers intended to do a preliminary investigation upon this particular attack so that it can be used for further research in alert correlation and computer forensic investigation.
💡 Research Summary
The paper addresses the enduring threat posed by the Blaster worm, first observed in 2003, and proposes a systematic method for tracing its activity across multiple layers of the OSI model using a combination of victim, attacker, and IDS logs. The authors begin by outlining the worm’s infection chain: exploitation of the DCOM RPC vulnerability on TCP port 135, execution of malicious code, and establishment of a back‑door on TCP port 4444, which often leads to system crashes and automatic reboots. They argue that existing detection approaches—primarily signature‑based IDS alerts or isolated host‑level event analysis—are insufficient for comprehensive attribution and post‑incident forensic reconstruction.
To overcome these limitations, the authors design a “multi‑layer log correlation framework.” They categorize log sources according to the seven OSI layers: (1) Physical/Data Link logs (switch port mirroring, NetFlow) to detect abnormal traffic bursts; (2) Network‑layer logs (IP headers, TTL anomalies) for rough attacker geolocation; (3) Transport‑layer logs (TCP SYN/ACK patterns on ports 135 and 4444); (4) Session‑layer logs (RPC and SMB session creation events); (5) Presentation‑layer logs (Windows System, Security, and Application Event logs); (6) Application‑layer logs (IDS alerts, e.g., Snort signatures); and (7) Management‑layer logs (policy changes, account modifications). By normalizing timestamps via NTP and using unique identifiers such as session IDs or process GUIDs, the framework stitches together events that belong to the same attack flow into a directed graph.
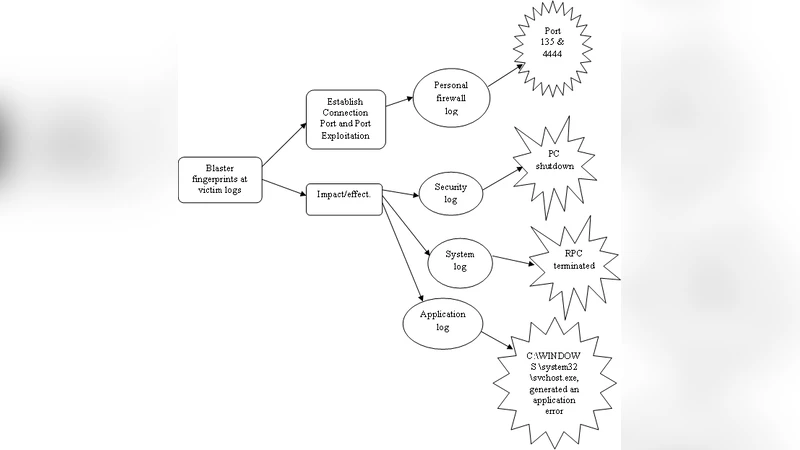
Central to the method is a “fingerprint” that captures the distinctive sequence of events typical of a Blaster infection: (a) an RPC request on port 135 followed within a few seconds by an outbound connection attempt on port 4444; (b) creation of the malicious executable (commonly msblast.exe or a renamed svchost.exe); (c) an IDS alert matching the “MS RPC DCOM Exploit” signature; and (d) Windows Event IDs indicating abnormal service termination (7031) and forced system reboot (1074). When these elements co‑occur, the system flags the activity as a Blaster attack.
The authors validate the approach in a controlled virtual environment running Windows XP SP2/SP3 infected with a Blaster variant. All stages of the worm’s lifecycle—scanning, exploitation, payload execution, back‑door establishment, crash, and reboot—are captured in the respective logs. Correlation reveals a tight temporal relationship (1–3 seconds) between IDS alerts and host‑level events, enabling a clear visual reconstruction of the attack timeline. Moreover, the method successfully attributes the source IP even when the attacker is behind NAT, by correlating inbound and outbound traffic patterns.
Key contributions include: (1) a comprehensive OSI‑layer‑aware log aggregation model; (2) formalization of a Blaster‑specific fingerprint that can be used for both real‑time detection and forensic analysis; (3) an automated correlation algorithm that reduces manual effort and improves attribution accuracy. Limitations noted are the dependence on complete log collection—missing logs can break the graph—and the potential for false positives when other malware exhibit similar port‑usage patterns, which would require supplemental signature or behavioral analysis.
Future work proposes integrating machine‑learning based anomaly detection to identify subtle deviations in multi‑layer logs, extending the fingerprint concept to other DCOM‑based worms, and developing a scalable implementation suitable for enterprise and national‑level security operations. The authors conclude that their technique offers a viable path toward more resilient detection and investigation of legacy worms that continue to resurface in modern networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment