A Modeling Framework for Generating Security Protocol Specifications
We propose a modeling framework for generating security protocol specifications. The generated protocol specifications rely on the use of a sequential and a semantical component. The first component defines protocol properties such as preconditions, effects, message sequences and it is developed as a WSDL-S specification. The second component defines the semantic aspects corresponding to the messages included in the first component by the use of ontological constructions and it is developed as an OWL-based specification. Our approach was validated on 13 protocols from which we mention: the ISO9798 protocol, the CCITTX.509 data transfer protocol and the Kerberos symmetric key protocol.
💡 Research Summary
The paper introduces a comprehensive modeling framework designed to automate the generation of security protocol specifications. Recognizing that traditional protocol descriptions—typically textual RFCs or standards—require manual interpretation and coding, the authors propose a two‑layered approach that separates procedural flow from semantic meaning, thereby enabling machine‑readable, reusable, and extensible specifications.
The first layer is a procedural component expressed in WSDL‑S (Web Services Description Language – Semantics). It captures the protocol’s preconditions, effects, and message sequences as service operations, enriched with semantic annotations. By leveraging WSDL‑S, the framework remains compatible with existing web‑service infrastructures while providing a formal description of each step’s required state and resulting state changes. This layer makes it possible to automatically generate or simulate the ordered exchange of messages, verify state transitions, and drive code generation tools.
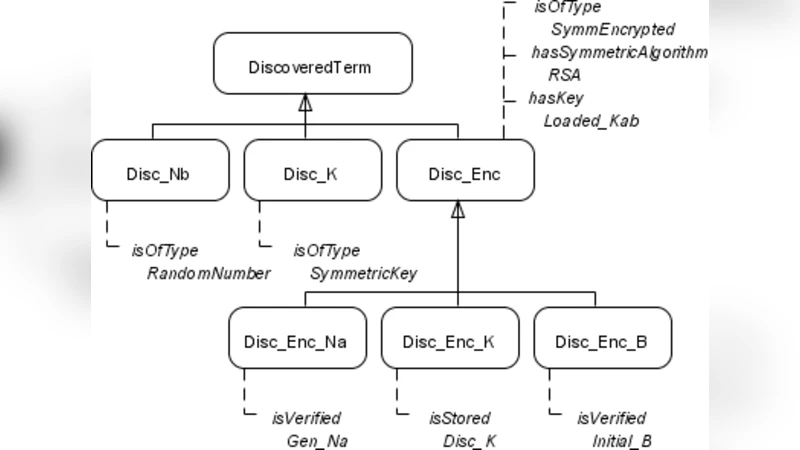
The second layer is a semantic component built on OWL (Web Ontology Language). Here, all security‑relevant concepts—cryptographic algorithms, key types, tickets, timestamps, etc.—are modeled as classes and properties within an ontology. Each message defined in the WSDL‑S file is linked, via a “semantics” annotation, to the corresponding OWL individual or class URI. This linkage supplies a machine‑interpretable meaning for every payload element, allowing automated reasoning about confidentiality, integrity, and authentication properties. Because the ontology is hierarchical and reusable, new protocols can inherit existing concepts, reducing design effort and ensuring semantic consistency.
The integration process works as follows: a WSDL‑S document defines the service interface and the ordered steps; each operation’s semantic annotation points to an OWL entity that describes the message’s content and security attributes. At runtime, parsers for both WSDL‑S and OWL load the specifications, resolve the links, and construct a complete, executable model of the protocol. This model can feed automatic code generators, simulators, or formal verification tools, effectively bridging the gap between high‑level design and concrete implementation.
To validate the approach, the authors applied the framework to thirteen well‑known security protocols, including ISO‑9798 (symmetric‑key authentication), the X.509 data‑transfer protocol, and the Kerberos ticket‑granting protocol. For each case, they authored a WSDL‑S file describing the message flow and a corresponding OWL ontology capturing cryptographic primitives, keys, and tickets. The generated specifications were shown to be functionally equivalent to the original protocols, and the OWL‑based semantics facilitated additional analyses such as type checking, vulnerability detection, and compliance verification. Moreover, reusing the same ontology across multiple protocols demonstrated a significant reduction in specification effort.
Key contributions of the paper are:
- A clear separation of procedural and semantic aspects of security protocols, leading to higher modularity and reuse.
- The use of widely adopted standards (WSDL‑S and OWL), ensuring compatibility with existing tooling and service ecosystems.
- Demonstration that ontology‑driven semantics can be directly leveraged for automated verification and formal reasoning.
- Empirical validation on a diverse set of protocols, confirming both functional correctness and practical benefits.
Future work suggested includes extending the ontology to cover policy‑based access control, integrating formal proof assistants for rigorous security guarantees, and enabling adaptive protocols that can modify their behavior at runtime based on contextual information. The authors also envision applying the automatically generated specifications to real‑time monitoring and intrusion detection systems, thereby providing a proactive, specification‑driven defense layer at the protocol level.
Comments & Academic Discussion
Loading comments...
Leave a Comment