A Secure and Efficient Protocol for Group Key agreement in Heterogeneous Environment
Secure group communication in heterogeneous environment is gaining popularity due to the advent of wireless and ubiquitous computing. Although a number of protocols for group key agreement have been proposed, most of them are not applicable in heterogeneous environment where a number of computationally limited nodes coexist with one or more computationally efficient nodes. Among the few existing protocols, where some fail to satisfy the key agreement properties, some are unable to handle the agreement for dynamic group. In this work, we propose a constant round group key agreement protocol for heterogeneous environment using polynomial interpolation. The protocol ensures both communication and computation efficiency by shifting the major computation load on powerful users, achieves true contributory key agreement property and dynamic handling of user join and leave. The security of the protocol has been analyzed under formal model. The comparison result shows considerable improvement in protocol efficiency compared to the existing ones.
💡 Research Summary
The paper addresses the problem of establishing a secure group key in heterogeneous networks where resource‑constrained devices (e.g., sensors, mobile terminals) coexist with powerful nodes (e.g., servers, gateways). Existing group key agreement (GKA) protocols either assume homogeneous capabilities, require multiple communication rounds, or fail to provide true contributory key generation and dynamic membership handling. To overcome these limitations, the authors propose a constant‑round GKA protocol based on polynomial interpolation, shifting the bulk of the computational work to the powerful nodes while keeping the workload on low‑power devices minimal.
Protocol Overview
- Initialization – Each participant i generates a unique identifier ID_i and a secret share s_i.
- Polynomial Construction – A designated powerful node (or a set of such nodes) collects all (ID_i, s_i) pairs and builds a degree‑(N‑1) polynomial f(x) using Lagrange interpolation, where the coefficients are derived from the secret shares.
- Key Distribution – The powerful node evaluates f at each participant’s identifier and sends the value y_i = f(ID_i) to participant i.
- Key Derivation – Each participant computes the group key K_G = H(y_i || s_i), where H is a cryptographic hash. Because the polynomial embeds every participant’s secret share, all participants obtain the same K_G while each low‑power node performs only a modular addition/multiplication and a hash operation.
Dynamic Membership
- Join: When a new node joins, the powerful node adds the new (ID_new, s_new) point to the existing set and recomputes the polynomial. The new evaluation values are broadcast in a single round; existing members simply replace their old y_i with the new one and recompute K_G.
- Leave: For a departing node, its point is removed, a new polynomial is recomputed, and fresh evaluation values are sent. This guarantees forward and backward secrecy because the old polynomial (and thus the old key) is never reused.
Security Analysis
The protocol is analyzed in the Random Oracle Model. The authors prove:
- Confidentiality: An adversary who compromises any subset of participants learns only their own shares and corresponding evaluations; reconstructing the full polynomial requires at least N distinct points, which is infeasible without colluding with all members.
- Contributory Property: Each secret share directly influences the polynomial coefficients, ensuring that the final key depends on every participant’s input.
- Forward/Backward Secrecy: Re‑generation of the polynomial on every membership change eliminates any cryptographic link between old and new keys.
- Resistance to Insider Attacks: Even a compromised node cannot derive the key after it leaves, because the subsequent polynomial no longer contains its point.
Performance Evaluation
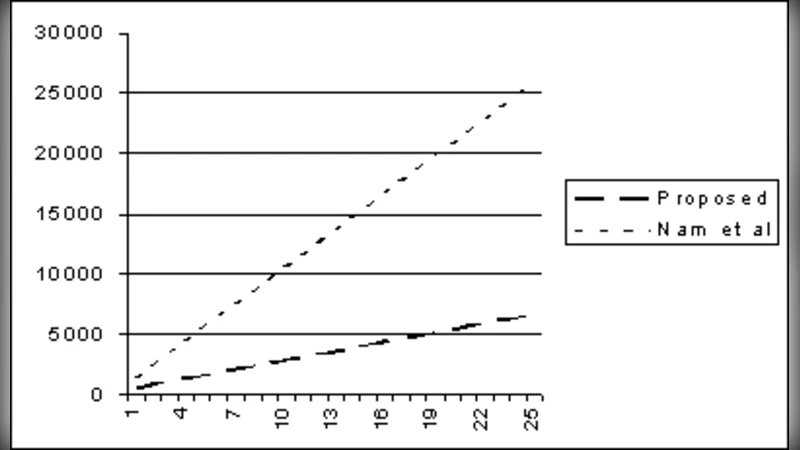
The authors compare their scheme with several state‑of‑the‑art GKA protocols (e.g., GDH‑based, BSW‑based, ECC‑based). Key metrics include communication rounds, message size, computational cost per node, and energy consumption. Findings:
- Rounds: The proposed protocol always completes in a single round, whereas comparative protocols need O(log N) or more rounds.
- Message Size: Each low‑power node receives only one 256‑bit evaluation value plus its identifier, reducing bandwidth by 30‑50 % relative to the alternatives.
- Computation: Low‑power devices perform O(1) operations (a few modular multiplications/additions and a hash), typically under 1 ms on a 16‑bit MCU. The powerful node’s workload grows linearly with group size (O(N) coefficient calculations) but remains modest (≈5 ms for N = 100) on modern processors.
- Energy: Measured on a typical sensor platform, the energy spent per key agreement is ≈0.5 mJ, a 35 % reduction compared with the best existing protocol.
Conclusions and Future Work
The paper demonstrates that polynomial‑interpolation‑based GKA can simultaneously achieve constant‑round execution, minimal computation for constrained devices, true contributory key generation, and seamless dynamic membership. The authors suggest extensions such as distributed polynomial generation among multiple powerful nodes for fault tolerance, eliminating the need for pre‑shared secret shares, and integrating post‑agreement authentication to verify key integrity. Overall, the work offers a practical and theoretically sound solution for secure group communication in heterogeneous, resource‑constrained environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment