Deterministic Formulization of SNR for Wireless Multiuser DS-CDMA Networks
Wireless Multiuser receivers suffer from their relatively higher computational complexity that prevents widespread use of this technique. In addition, one of the main characteristics of multi-channel communications that can severely degrade the perfo…
Authors: ** - **Syed S. Rizvi** – Computer Science, Engineering Department, University of Bridgeport
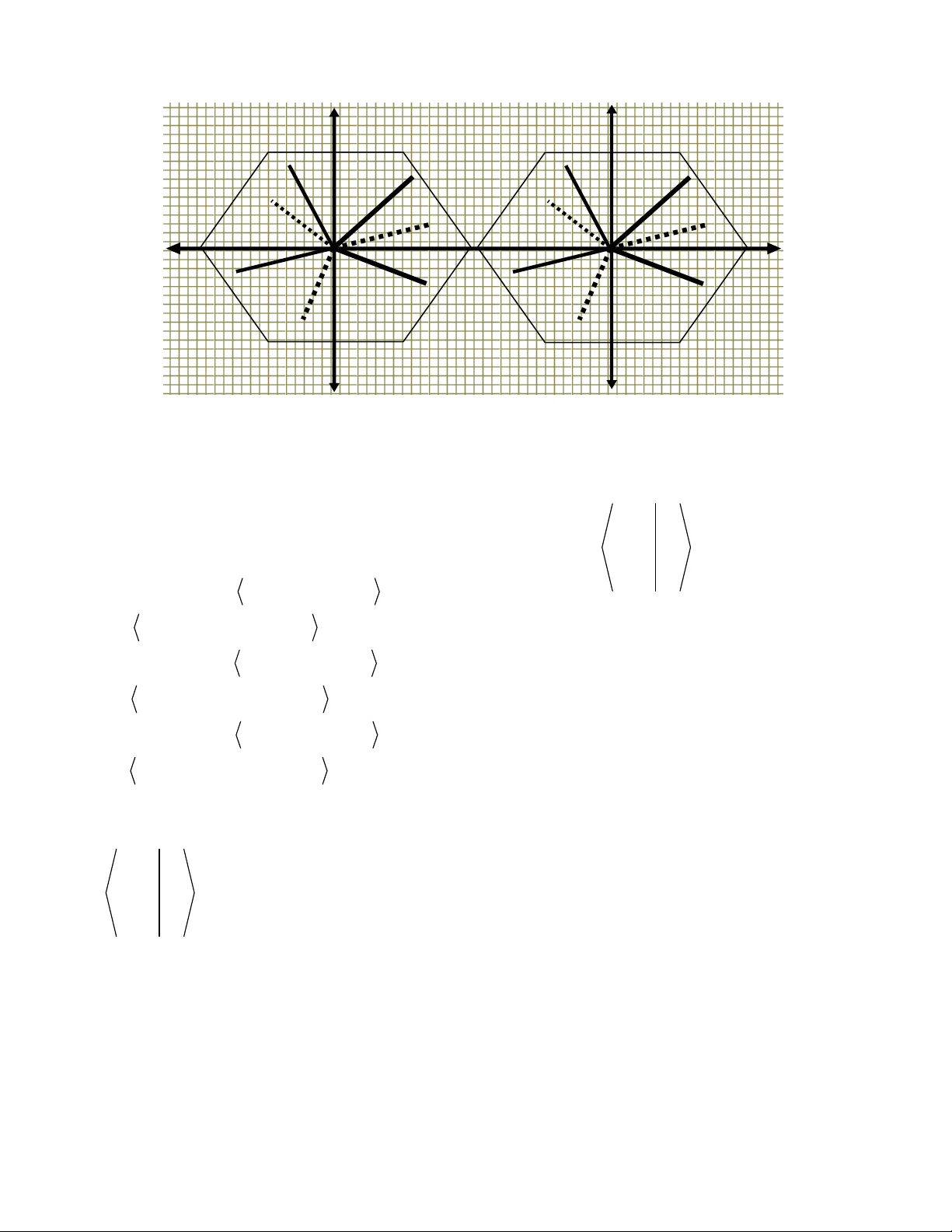
Abstract — Wirel ess Multi user receivers suffer from their relati vely higher com putational complexity that prevents widespread use of t his techni que. In addition, one of the main characteri sti cs o f multi-channel com munications that can severely degrade the perfo rmance is the inconsistent an d low values of SNR that result in high BER and poo r channel capacity. It has been shown that t he comp utational complexity of a multiuser receiver can be reduced by using t he transformation matrix (TM) algo rithm [4]. In this paper, we prov ide quantif icat ion of SNR based on the co mputational com plexity of TM algorithm. We show that the reducti on of com plexity results high and consistent values of SNR that can consequently be used to achieve a desirable BER perform ance. In additi on, our simulation resul ts suggest t hat the high and consistent values of SNR can be achieved f or a desirabl e BER performan ce. The perf orm ance measure ado pted i n thi s paper is the c on sist ent values of SNR. Keywords—Com putati onal com plexi ty, DS-CD MA, wireles s m ultiuser rece ivers , s ignal to noise rati o I. I NTRO DUCTION From th e design stan dpoint, fo r a given m odulation an d th e co ding sc heme there is a one to one co rr espo ndence be tw ee n th e bit err or rat e (BER) a n d the sign al-t o -n oise ra tio (SNR ). From th e use r stan dpoint, SNR is n ot th e fav o rit e criteri on fo r th e perfo rma n ce ev aluati on of di gita l co mmun ication lin ks, bec ause th e user m easures th e quali ty of a sy ste m by th e n um be r of err ors i n th e r ece ive d b its a n d prefe rs to avo id th e techn ical detail of modulati on o r co ding. H ow ev er , using rece ive d SNR ra th er th an B ER w ill allow us to r elate our per fo rman ce cr iter ia to t h e requir ed t r an smit ted pow e r, which is ve ry importan t fo r battery -o perated w ireless operati ons. U sing SN R r ath er th an B E R h as two advan tages. Fir st, SNR is th e criter ion used for acc es sing bo th digi tal an d anal og modulation techn iques. Sec o nd, SNR is dir ec tly rela ted to the tr an smit ted pow er , w hi ch i s an import an t design pa r ameter. A sign ificant a mount of ef f o rt s h ave be e n m ade in order to a chieve h igh values of SNR [3, 5]. Ho w e ve r, none o f th ese methods relate th e co mplexity of multi user r ece ive rs fo r ach ieving h igh SNR values. On th e o th er h a n d, t h e T M algorit h m is a lo w co mplexity , but sy n chr onous tr an smission techn ique th at is able t o r educe t h e n um be r o f co mputati ons perfo rms b y a m ulti user r ece ive r fo r sign a l detec tion [4]. T h e TM a lgorit h m th er ef o re pr ov i des f ast multi user sign al detec tion w hich can be furt h er used to achi ev e h igh SNR values. T h e contr ibution of t h is research w o rk is th e qua n tification o f SNR using th e T M al gorith m propos ed by Rizvi et. [4]. At h i gh SNR v alues, t h e err or ra te fo r mult i ch an n el can be r educe d as we ll th e capacity o f th e chan n el can be w ell appr oximated. Multiuser r ece ive rs can be catego r i zed in th e f o llow ing two fo rms: optima l ma ximum l ikelih oo d sequence estimati o n (ML SE) r ec eiv ers a nd sub o ptima l li n ear a n d nonl in ear r ece ive rs. No n-li n ear multi user r ece ive r in vo lve s th e estimati on an d reco nstr uction o f MAI [6] see n by eac h user w it h the ob j ec tive of can celing it f r om t he r eceiv e d signa l. Th e two w ell kn ow n i mplement ati ons of t h is mechan ism are SIC an d PIC. In i n terference cancellati on, MAI i s first estimated a n d t h en subtra cted from th e receiv e d sign al [1, 7]. On t he oth er han d, l in ear multi user receiv e r s apply a lin ear tr an sfo r m ati on to an ob servation ve c tor, which serve s as so ft decisio n fo r th e tran smi tted data. Rec ently , Ott os so n a n d Agr ell [2] propo se d a n ew ML receiv e r t h at use s t he n eigh bo r desce nt (ND) algori th m. Th ey i mplement ed a l in ear itera tive appr oach usin g the ND algorit h m t o locate t h e r egion w her e th e actual ob se rvations be lo ng. Th e li near it y of th eir iter ati ve appr oach in creases noise c ompo nent s at t h e rece iving end. Due to t h e enh an cement in th e n oise compo nen ts, th e SNR an d BER of ND a lgorit hm is m ore a ff e cted by the M AI. Tab le 1, reported f r om [8], h igh li gh ts th e a ssumed kn ow ledge fo r th e co mputati onal co mplexity of a CDMA base d mul tiuser receiv e r . Ta ble I show s th a t diff erent r ec eiv ers distin gui sh th emselv e s with r espe ct to th e r equir ement of t he desired know ledge as well as th e i mplement ati on co mplexity . V erdu [1] pr opo se d t h e optimum mul tiuser detecto r fo r asy n ch r onous sy stems. Th e co mplexity o f multiuser Sye d S. R iz v i and Kh ale d M. Ell e ithy Computer Science and En gin eerin g Departm ent U ni ve rsity of Bridgepo rt Bridgepo rt , CT 06601 {sriz vi, elleith y }@b ri dgepo rt. edu A asia R iasat Departm ent of Co mputer Science Insti tute of Business Managemen t Kara chi, Paki stan 78100 aasia. r iasat @iob m.edu.pk Deter ministi c For muliz ation of SNR for Wireless Multiuser DS-CDMA Networks (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 25 receiv e r gr ow s exponent iall y i n an o rder o f O (2) K , wher e K is t he num be r of active users. Re ce nt ly , [2] pr opo se d a ML receiv e r t ha t uses t h e n eighbo ri n g decent (ND) al gorith m w ith an itera tive a ppr oac h to lo cate th e regions. The lin ear ity of th e iter ative appr oac h in creases n oise co mpo nen ts at th e r ec eiv in g e nd. The TM a lgorit h m [4] ob serves th e coo r di n ates of t h e co nstella tion diagr am to determin e th e location of t he tr an sfo rma tion poin ts. Sin ce most of the dec isions ar e corr ec t, th e TM a lgorit h m can reduce the n umbe r o f co mputations by usin g t h e tr an sfo rmat ion ma tr ices o nly on those co o rdin a tes w hich ar e most likely to lead to an i n co rr ect dec ision. II. P ROPOSED T RA NSFORMA TION M ATRIX A LGORITH M We co nsider a sy n ch r onous DS-CDMA sy stem as a lin ear time i n varia nt (LTI) chan n el. In a LTI chan n el, th e probab ility of var iat ions in th e i nt erference par am eters, such as th e timi ng of all users, a mplit ude varia tion, ph ase shift, an d frequency sh ift, is extremely l ow . Th is pr ope rt y makes it po ssib le t o r educe the o v eral l co mputati onal co mplexity a t th e rece iving end. Our TM techn ique ut ili zes th e co mplex pr ope rt ies of t h e existin g in verse ma tr ix algorit h ms to c onstr uct th e tr an sfo rma tion matr i ce s an d t o determin e th e l oc ation o f t h e TPs th at m ay oc cur i n a n y co o rdin a te of t h e constellat ion di agr am. T he i ndi vidual T Ps can be used to determi ne t h e a ve rage computationa l co mplexity . Th e sy stem may consist of K users. Use r k can tr an smi t a signa l at an y given time w ith th e pow er of W k . With th e binar y pha se s hi ft ke y i n g (BP SK) mo dulation tec h ni que, th e tr an smit ted bits be long t o either +1 or -1, (i.e., { 1 } k b ∈ ± ). Th e cross co rr elat ion can be r educ ed by neglectin g th e vari able delay spreads, since t h ese dela y s a r e rela tively small as co mpar ed to th e sy mbo l tran smission time. In order to detect sign als from a ny user, th e demo dulated output of t h e l ow pass filter is multi plied by a uni que sign atur e w ave f o rm a ssigned by a pseudo r an dom num be r genera tor. It should be n oted th at w e extract th e signa l usin g t h e ma tch filter fo llow e d by a Vit erbi algorit h m. Th e optimum multi user receiv e r exists an d permi ts t o r elax th e constr ain ts of ch oo sing th e spreadin g seque nces w ith goo d co rr elat ion pr ope rt ies at a cos t of in creased receiv e r co mplexity . A. Descript ion of Transformation Matrix Al gorithm Acc o rdin g t o ori gin al Verdu’s al gorith m , th e outputs of th e mat ched filter 1 ( ) y m and 2 ( ) y m can be co nsidered a s a singl e o utput ( ) y m . In order t o mi n imi ze th e n oise co mpo nen ts an d to m axim ize th e r ece ive d demodulated bits, w e can tr an sfo rm th e output o f the mat ched f ilter , an d th is tr an sfo rmat ion c an be e xpresse d as fo l low s: ( ) y m Tb η = + w her e T repr ese nt s th e TM, { 1 } k b ∈ ± a n d η repr ese nt s th e n oise co mponents. In additi on, if the v ec tors are regar ded as po int s in K- dimen sio n al space , t h en t h e v ec tors co nsti tute a co nstellat ion di agr am th a t h a s K total point s. Th e co nstellat ion di agr am can be m ath emati cally expresse d as: { } b X = Τ w her e { } 1 , 1 b ∈ − + an d X r epr ese nt s th e c o llective co mputati onal c o mplexity of a m ulti user receiv e r . Th e pr ece din g equation is f unda ment al to t h e pr opo se d algorit h m. Ac co rdin g to th e detectio n r ule, t h e co nstellat ion diagr am can be par tit ioned in to 2 K lin es (w her e th e total pos sib le l in es in t he co nstell ation diagra m can be repr ese nt ed as ſ ) th at can only in t ersec t each o th er at th e fo l low ing points: X = {Tb} b ∈ {-1, 1} K \ ſ . Fig. 1 sh ow s t h e co nstella tion diagr a m th at co nsists of th r ee diffe rent vec to rs (lin es) with t he o ri gin al vec tor ‘ X ’ th at r epresents t h e co llectiv e co mplexity of t h e r ece ive r. Q , R , and S r epr ese nt ve cto rs or TP with in t he cov e ra ge ar ea of a cellular netwo rk (see Fig. 1). In addit ion, Q ¬ , R ¬ , an d S ¬ repr ese nt th e co mputat ional co mplexity o f eac h in dividual TP. In order to co mpute th e co llec tive co mputa tional co mplexity of th e optimum rece ive r, it i s ess entia l to determin e th e complexity of each i n dividual T P. TABLE I. C OMPL EXI TY R EQUI REMENTS O F D ETECTIO N A L GORI THMS F OR DS - CDMA S YST EMS Rece iver s Signatu re of Desire d User Signatu re of Interfer ence Timin g of Desire d User Timin g of Interfer ers Relative Am plitu de Trainin g Sequence Conve ntional and Rak e YES NO YES NO YES NO Linear ZF YES YES YES YES N O NO Linear MM SE YES YES YES YES Y ES NO SIC an d PIC YES YES YES YES Y ES NO Trained A da ptive MM SE NO NO YES NO NO YES Blind Ad ap tive M M SE YES NO YES NO NO NO (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 26 Th e co mputat ional complexity of each in dividual TP is repr ese nt ed by X ¬ o f th e T P w hich is e qual to th e co llective co mplexity o f Q ¬ , R ¬ , a n d S ¬ . In order t o derive th e v alue of th e origin al vec tor X , w e n eed to perfo rm th e fo llow ing derivations. We consider th e o ri gin al v ec tor w ith r espe c t to each tr a n smitted sy mbo l or bit. i j K i j K X Q Xi XQ XR XS i XQ i XR i XS i ¬ ¬ ¬ ¬ ¬ ¬ = = + + = + + i j K i j K X R Xj XQ XR X S j XQ j XR j X S j ¬ ¬ ¬ ¬ ¬ ¬ = = + + = + + i j K i j K X S Xk XQ XR XS k XQ k XR k XS k ¬ ¬ ¬ ¬ ¬ ¬ = = + + = + + Th e fo llow ing equation can be derived from t h e abov e sy stem: ( ) ( ) ( ) ( ) ( ) ( ) ( ) ( ) ( ) X Q i i i j i k i XQ X R j i j j j k j XR i k j k k k XS X S k ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ = (1) Equati on (1) r epresents t h e fo llow in g: QRS with th e un it ve c tors , , and i j k , an d , , a n d X Q X R X S ¬ ¬ ¬ w ith t h e in ve rse of th e un it vec tors and , , i j k ¬ ¬ ¬ . Th e sec o nd mat r ix on t h e r igh t h an d side o f (1) r epr ese nt s b , w her e as t h e first matr i x on t h e righ t ha n d side o f (1) repr ese nt s th e actual TM. T h e T M from th e glob al refe ren ce po i n ts to a parti cular lo cal r ef e ren ce point can now be derived f rom (1): / L G X Q i XQ X R j T X R XS X S k ¬ ¬ ¬ ¬ ¬ ¬ = (2) Equati on (2) can also be w ri tten as: / L G ii j i ki T ij jj kj ik jk kk ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ ¬ = (3) In (3), th e dot pr oducts of th e un i t ve cto rs of t h e two refe ren ce po in ts ar e in fact th e sam e as the un it vec tor of th e inverse TM of (2). We need to compute t he l oc ations of th e actual TP des cribed in (2) an d (3). Le t th e un it ve cto rs fo r th e local r ef erence po in t be: [ ] [ ] [ ] 11 12 13 21 2 2 2 3 31 32 33 , , , , , , i T i T j T k j T i T j T k k T i T j T k ¬ ¬ ¬ = = = (4) Since, ( ) i i j k i ¬ ¬ + + = , where ( ) 1 i j k + + = . T h e same ar gument i s tr ue for t he rest o f t h e un it ve cto rs. Th erefo re, (4) can be rew rit ten as: [ ] [ ] [ ] 11 12 13 21 22 2 3 31 32 33 , , , , , , i T T T j T T T k T T T ¬ ¬ ¬ = = = (5) X S Q R ¬ R S ¬ Q ¬ X S Q R ¬ R S ¬ Q ¬ Fig ure 1. A c on s te llati on d iagram c o ns is ti ng o f th re e dif fe ren t v e ct ors (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 27 By substitutin g th e values o f and , , i j k ¬ ¬ ¬ from (5) in t o (3), we o b tain 11 11 12 13 11 12 13 21 21 22 23 2 1 2 2 23 31 31 32 33 31 32 3 3 / , , , , , , 12 13 , , , , , , 22 23 , , , , , , 32 33 L G i T i T j T k j T i T j T k k T i T j T k i T i T j T k j T i T j T k k T i T j T k i T i T j T k j T i T j T k k T i T j T k T = 11 12 13 21 22 2 3 31 3 2 33 / , , , , , , L G T T T T T T T T T T = (6) Sub stituti n g T L / G from (6) in to (2), y ields 11 12 13 21 22 23 31 32 33 X Q T T T XQ X R T T T X R X S T T T X S ¬ ¬ ¬ = (7) Equati on (7) co rr espo nds to t h e fo llo w in g sta nda r d equation tha t use d fo r computin g th e computationa l co mplexity at t h e r ec eiv ing end: X = Tb where { } b 1 , 1 k ∈ − + . If th e tar get o f one tr an sfo rma tion ( ) : U Q R → is th e same as th e so urce o f o ther tran sfo rma tion ( ) : T R S → , then w e can co mb in e tw o o r m ore tran sfo rm ations an d form th e fo l low ing co mposition: TU: Q S, TU( Q) =T[U( Q) ] . Th is co mpo sition can be used t o deri ve t he co llec tive co mputati onal co m plexity at th e r ece iv in g en d usin g (7). Since w e a ssumed tha t th e tr a nsmi tted sign als ar e modulated usin g BPSK w h ich can a t mo st use 1 bit out of two bits (i. e., { 1 } b k ∈ ± ), co nsider th e fo l low ing set o f TP to appr oximate th e number of demo dulated r ece ive d bits th at need to search out by decisio n algori th m: ( ) ( 0 ) ( 1) 0 0 ( ) ( 1) (1 ) ( 0 ) ( 1) 0 ( 1) 0 ( 1) ( 0 ) 0 ( ) 0 ( 1) ( 0 ) ( ) y m Tb Tb m y m Tb Tb Tb m Tb Tb m k Tb Tb y K η η η = − + − + + + … … (8) Equati on (8) is deri ve d usin g our funda ment al equati on of TM (i. e., y T b η = + ). Our appr oach is to a ssume term s ( ) m η an d ( ) m k η + in (7) n ot equal to zer o. Th is co ndit ion is fulfilled by peri odic all y in serti n g a n onzero- energy bit in th e in fo r m ati on b it seque nce. Th erefo r e, th e in terference due to th e cross-c o rr elati on of th e a ctual sy mbo ls w i th th e past and futur e sy mb o ls in th e asy n ch r onous chan n els can be acc o un ted. U sing (7), a simple m atr i x a dditi on o f th e r ece ive d demo dulated bits can be used t o appr oximat e t h e num be r o f most corr elated TP. The en tir e pr oc edure fo r co m putin g th e num be r of de modulated b its th at n eed t o be search ed out by th e decisio n a lgorit hm can be used to appr oximate th e num be r o f most co rr elat ed signa ls fo r an y given set o f TP. Th is is b ec ause we n ee d to check wheth er or not th e TP a r e clo se st to eith er (+ 1, +1) or (-1, -1). Th e decisio n r egio ns or th e co ordi n ates w here th e TP lie fo r (+1, +1) an d (-1, -1) ar e simpl y th e co rr espo ndin g t r an sfo r m ati on mat ri ces th at store t h e patter n s of th eir oc curr ences . If the T P do not exist in t he r egion o f eith er (+1, +1) o r (-1, -1), th en i t is just a matt er of checking wheth er t h e T P ar e clos es t t o (+1, -1) o r to (-1, + 1). Th e m in imum se ar ch perfo r m ed by th e decisio n algorit h m i s co nducted if th e TP e xist with in th e in co r rect region. S in ce the min i mum se ar ch sav e s co mputat ion by one degree, th e decisio n a lgorith m h a s to se ar ch at least 4 k demo dulated bits. T hi s i mpli es th at th e total n umbe r of demo dulated b its t h at n eed t o be search ed out by th e dec ision al gorith m can n ot exce e d by 5 K - 4 K . T h us, t h e total num be r of mo st co r r elat ed pa ir s ha s an upper b o und of 5 K - 4 K . Since most of th e decisio ns a r e co rr ect, we can r educ e th e num be r of co mputat ions by usin g t h e t r an sf ormat ion matr i ce s onl y on th ose coo rdin at es th at ar e most likely t o lead t o an in corr ec t dec ision. Th us, t hi s greatl y r educe s t h e unn eces sary pr oce ssing r equired to ma ke a decisio n a bo ut th e corr ect r egion. T h us, th e n umber of receiv ed demo dulated b its t h at n eed to be sear ched out can be appr oximated as 5 K - 4 K . Th e co m putat ional co mplexity o f a n y multi user r ece ive r can be quan ti fie d by its tim e co mplexity per bit [6]. T h e co llec tive co mputati onal co mplexity of the propo se d algorit h m is achi ev e d afte r per fo rmin g th e TM sum. T h is impli es th at b o th qua nt iti es T a n d b from our fundamen tal equation can be co m puted together an d th e genera tion of all th e v alues of th e demo dulat ed r ece ive d b its b can be done th r ough the sum o f th e actual TM T th at appr oximately takes О (5/4) k operati ons with a n a sy m ptotic co nsta n t. U sing th e New ton appr oximati on method given in MATLA B , w e can dir ectly co me to an appr oximati on o f О (5/4) k . Th e co mputati onal co mplexity of t h e pr opo sed algorit h m is n ot poly n omial in the n umber of users, i n stead th e n um be r of operati ons requir ed to m axim ize th e demo dulati on o f th e tr a n smitt ed bits an d t o choo se a n optimal value of b i s О (5/4) k , an d th er ef o re th e time co mplexity per bit i s О (5/4) k . (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 28 III. P ROPOS ED Q U A NTIFICA TION O F S IGNA L - T O -N OISE R A T ION (SNR ) In t h is sec tion, we derive an expression to pr ov ide quan tification of SNR fo r th e sign al s r ece ive d a t th e DS- CDMA multi user r ec eiv er. Th e r educ ed complexity of th e TM algorit h m pr ov ides faste r detec tion r ate. T h e faster detec tion r a te r esults h igh a n d co n sistent values of SNR. Once w e determ in e th e values of SNR , we can r elat e th em to th e BER perfo rma n ce an d th e cha nn el capacity appr oximation fo r a wireless multiuser r ece iv er. MAI causes t he SNR degra dati on r esultin g i n a degraded SNR perfo rm an ce f or a pa r ticular value of E b /N o . We present th at due t o th e reduced co mplexity , t h e SNR perfo rma n ce of th e T M al gorith m wo uld r emain co nsisten t in term s o f t h e des ir ed values ev en fo r a lar ge value o f K . Th is co n sistency i n SNR per fo rma nce y ields an optimal BER perfo rma n ce . A. Sy stem Model and Key Assumptions Our f unda ment al assumption i s th at t he sy stem i s li n ear time in vari an t (LTI) which l eads us to th e f act t h at th e tr an smit ted sign als expe ri ence n o deep fades. Due to th e lin ear ity an d tim e in varia n t pr operties of th e sy stem, we can ign ore th e ph ase shi ft, an d dee p fade s. In other w ords, t h e ov er all SNR of th e r ece ive d sign als h a s a slow co nve r gence ra te co mpar ed to th e co nvergence ra te of th e BER . B. Proposed Form ulizati on for SNR Consider t h e follo w ing assumpti ons fo r a n AWGN chan n el: (a) ℵ represent s the c omputational complexi ty t hat belongs t o a certain cov erage area . (b) SNR (w e represent SNR by γ ) is uniformly distributed among all the acti ve user’s signals with respect to c omputational comple xit y . (c) A c ertain cel lular c overage area has K users. Base d on th ese abo v e a ssumptions, we can give th e fo l low ing h y poth esis: { } 1 2 3 , , , ........... ......, i K ℵ ℵ ℵ ℵ ℵ ∈ (9) w her e 1, 2, 3, ........... ......... K ℵ ℵ ℵ ℵ in dicat es th e in di cates th e co mputati onal co mplexity -do main an d { } 1 2 3 , , , ................, i K h h h h h ∈ (10) w her e 1 2 3 , , , ................ , K h h h h in dicates th e user- domain. Complexity -domain can b e co nsider ed as a simpl e dat a structur e fo r stori n g th e pat tern s of oc curr ences of all active users. Us er-Domain is t h e n um be r of active users pr esent in th e ce r tain co v erage a rea of a ce llula r n etw ork. Th e co llec tive c omputationa l complexity can be expresse d as: 1 1 , 2, ....., K i i where i K = ℵ = ℵ = ∑ (11) Sin ce each user h as th h par t of th e co mputat ional co mplexity suc h as: 1 1 2 2 , , ......, K K h h h ℵ ℵ ℵ ∈ ∈ ∈ . Th is impl ies tha t each acti v e user in a certa in a rea o f a ce llula r netw o rk has an ave ra ge of K ℵ c o mputati onal co mplexity . Since SN R is un ifo r mly distr ibuted am ong al l th e use r’s sign a ls at th e rece iving en d, each user expe ri ences an average of K γ SNR . Th er ef o re, th is ar gument l eads us to: ( ) ( ) 1 1 1 1 K C C C γ γ − − − ℵ = − ℵ = − ℵ (12) w her e C in (12) r epresents th e n orm ali zat ion fac tor, K ℵ is th e inverse of th e co mputati onal complexity , an d γ ℵ repr ese nt s t he SNR with respec t to a ve rage co mputat ional co mplexity . Equati on (12) can be i n terpr eted t ha t th e in ve rse of co mputati onal complexity equals to th e diff e ren ce betw e en th e in verse-normal iza tion facto r a n d th e pr oduct of th e in ve rse-norm ali zati on factor a n d SNR w ith respec t t o th e co llec tive co mputationa l co mplexity . Th e m ain ob je c tive of (12) is t o m ake sur e th at we should get maxi mum positive values of SNR fo r most of th e values o f K. C. P roof for γ ℵ If th e pr evio us assumptions ar e valid fo r an AWGN chan n el, th e fo l low ing appr oximati on must be true fo r b o th th e co mplexity an d t he user domain s: approximation K C K γ ℵ → + (13) We pr esent o ur hy po th esis th a t t h e diff erence betw e en th e ave ra ge computati o n al c o mplexity an d th e ave ra ge SNR should equal to t h e n orm aliz ati on facto r. Th e mai n ob jectiv e of (13) i s to get maxim um pos iti v e values of SNR fo r mos t of t h e values o f K . Equati on (5) can a lso b e w ri tten as: ( ) ( ) K K C γ ℵ − = (14) Base d on (14), we can w ri te th e fo llow i n g equation: (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 29 ( ) 1 K C γ = − ℵ ℵ (15) Sin ce th e r igh t h an d side of (15) r epresents t he i n ve rse of th e ave r age co mputat ional co mplexity with th e norm ali zat ion facto r , t h e n um be r of r equired operati ons can not be l ess th an z ero. It should be n ote d th at th e r igh t h an d side of (15) a lway s gives us a po sitive value of SNR fo r a ny value of K which is greater th an 10. Equa tion (15) can also be rewritt en a s: ( ) [ ] 1 1 K C γ − ℵ = − ℵ (16) Us in g th e complexity a nd t he user domain, w e can m ake an a r gument t h at th e in verse of an ave r age SNR sh ould be at least gr eater than zero. Th is a r gument gua r an tees th at th e sy stem does n ot w o rk w ith a non positive value of SNR . In other w o rds, th e in verse of th e average SNR should equal to t h e di ff e ren ce of th e n ormal iza tion f actor an d th e in ve rse o f t h e average computati o n al complexity . Rec all (12): ( ) ( ) 1 K C CK γ γ − ℵ = ℵ − ℵ = ℵ − (17) Equa tion (17) r epresents SNR by deter min in g th e diff e ren ce be twe e n th e pow er of th e tr an smi tted sign al from th e co mputati onal co m plexity -do main an d the n umbe r of users f rom th e user-domain . Equa tion (17) can also be used to compute t he values of SNR i n an ideal sit uati on only if MAI does not aff ec t th e r ece ive d sign al s by K-1 users. H o w ev er , in a pr actical DS -CDMA sy s tem, t h is assumpti on doe s not exist. Th erefo re, w e should co nsider t ha t th e variat ions in t h e n etw o rk l oad fo r an AWGN ch an n el in tr oduc es th e pr ese nce of varia n ce (w e r epr ese nt varian ce by 2 Φ ) th a t r epr ese nts MAI. Th e sele ctio n of varian ce is e nti r ely depe ndent o n th e netwo rk l oad. Th e vari an ce is a li n ear function of th e active users ( K ) a n d it should in crease a s w e incr ease th e value of K . In o rder to compute the values o f S NR , w e need to chan ge th e li n ear quant ity in to decib e ls (dB) b y mul tiplying it to th e base-10 logari th mi c function as w ell a s with th e varian ce. Th is leads us t o th e follo w ing expr essio n fo r SNR : ( ) 2 10 10 log CK γ = Φ ℵ − (18) We use th e values o f v ar ian ce in our sim ulat ion th at repr ese nt s MAI w ith r espec t to K . IV. E X PE RIME NTAL V ER IFICA T ION A ND S IMU LATION R E SU L TS F ig. 2 show s th e l o gical di agr am of a cellular sy stem t h at uses sy n ch r onous DS-CDMA sy stem. We assume th a t all th e use rs among th e c ellular area communi cate usin g AWG N chan n els th r ough one or more base stations. Be c ause o f AWGN multi ple cha n n els, th e sy mbo l dur a tion of th e tr a n smitt ed sign al is much l ar ger th an t h e de lay spread which avo id i n ter-sy mb ol in terference. Th erefo re th e uplin k (fr o m user to BS ) model is base d on sy nch ronous DS CDMA sy stem with mul tipl e pa th ch an n els an d th e presence of AWGN with zero mean a n d a var y i n g a mount of varia n ce . Th e choice of v ar ian ce depe nds on t h e n umbe r of active users pr ese nt in th e cov e ra ge ar ea of a ce llula r n etw ork. Furth er more, we a ssume th at th e t r an smission pow e r o f each use r i s t igh tly co ntr olled (which i s a usual th in g fo r w ir eles s applicati ons) by the centr al entit y o f a cov er age ar ea such a s a ce ntr a l b ase sta tion (B S) or an acc ess point (AP). Th is im plies t h at t h e centr al ent ity (BS/AP) of a co v erage ar ea receiv e s unifo rm -pow er -signa ls an d th ey rema in sam e th r oughout th e total communi cation t ime. It ha s be en show n th at th e SNR degradat ion depe nds o n th e n umber of users, K , [4]. An i n crease in K w ould degrade th e perfo r man ce be cause i t w ould in cr ease t h e cross co rr elation betw e en th e r ece ive d sign als from al l the users (i. e., K-1 users). Math emat ically , w e can express th is as: K ∝ MA I ∝ hi gh B ER ∝ 1/SNR . T h is sh ow s th at a sligh t in crease in K w o uld degrade t h e SNR per fo rma n ce th at conseque ntl y in creases th e BER . H o w ev er , a l ar ge in crease in value o f K fo r ces MAI to r each i ts peak value th at lim its th e dive rgen ce o f SNR fo r t h e TM al gorith m. Th r ee dif f erent ty pes of detec tion al gorith m s a r e in ve stigated, which ar e th e ori gin al ML al gorith m, r educe d ND a lgorit h m, an d the pr opo sed TM algorit h m [4]. T h e fo l low ing is th e descripti on of t h e pa r ameters th a t we use fo r tw o diff erent sce na r ios: (i) li ghtly -loaded netw ork where K star ts f rom 2 t o 50 a n d (ii ) heav ily-l oaded netw ork where K star ts from 2 to 100. LTI sy nch r onous DS-CDMA ov er an AWGN chan n el with small vari ati on in 2 Φ ar e used. In order to compare t h e SNR perfo rma n ce of th e propos ed algorit h m w ith th e o ther multi user dete ction algorit h ms, w e use a same constan t value w i th th eir asy m ptotic c omputationa l co mplexities th at do es n ot ma ke an exceptio n fo r an y one of th e in ves tigat ed al gorith ms. In our simul ati on fo r b o th scenar ios, we use one (i. e., 1 C = ) as a n orma liz ation fac tor th a t r emai ns sam e fo r all t h e in ve stigated al gorith m s. Th e choic e of a small value of 2 Φ is ent ir ely base d on th e load of th e co v e ra ge ar ea ( K ) a n d it is sele cte d th r ough a ra n dom pr oc e ss fo r a ce rta in r an ge o f use rs. For a ligh t ly loaded netwo rk, we e xpec t th at th e value of v ari an ce ( 2 Φ ) (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 30 may v ary from 0.6 to 0. 9 an d fo r a h eav ily -loade d n etw o rk; th e value of var ian ce may vary from 0.1 to 1. Since th e propos ed algori th m detects tr a nsmi tted sign als by usin g co mplex pr ope rt ies of i nverse ma tr ix al gorith m th at ob serves th e coo r di n ates of t h e co nstella tion diagr am to determin e t h e loc ation of th e co r r espo ndi n g tr an sfo rmat ion points, it is more li kely th at t h e value of vari an ce is extremely small fo r bo t h li gh tly -loade d as w e ll as h eav ily - loaded n etwo r ks. Fur th erm ore, al l sign a ls tr a n smit at t he same bit r ate an d al l sign als r ece ive w ith th e same pow er (i.e., perfec t pow e r co nt r ol). For ligh tl y -l oade d n etwo rk, (2 55) w hen co mpar e t o a l igh tl y -l oade d n etw o rk. Th is is be c ause t h e co mputati onal co m plexity fo r a h eavily -l oade d case is much greater th an th e co mputat ional co mplexity fo r a ligh t ly -lo aded case t h at force s bo th ML an d ND algorit h ms to mi n imiz e th e facto r of divergence an d h en ce maxim ize t h e f actor of co nvergence. Sin ce w e assume th at th e selec tion of varian ce is ra ndom w ith in t h e spe cif ied ra n ge, it r emain s sta ble after a certai n value of K th at li mits th e dive rgen ce o f SNR . Another i mportan t point th a t can be o b serve d from Fig. 8 is t h at th e gr aph fo r th e pr opo sed a lgorit h m co nverges to appr oximately 45 dB after 100 users an d only a sligh t in crease i n th e value o f SNR can be expec ted fo r v ery l ar ge values of K . Thi s is a lso essentia l f or a chieving an acce ptable performan ce, sin ce cr os sing th e th r eshold value of SNR migh t degr ade th e ov erall sy stem perfo rm an ce. In other w ords, a fte r a certa in value o f K, th e MAI r eaches t o its peak value th at li mit s th e divergence of th e SNR cur ve fo r th e pr opo se d algori th m. V. C ONC LU SI ON In t h is pape r, w e prese nt ed th e quan tification o f SNR base d on th e T M a lgorith m . We h ave sh ow n th at t h e reduction i n t he computationa l co mplexity of a mul tiuser receiv e r can be used to achi ev e h igh an d consistent v alues of SNR . Th e simul ati on results sugges t th at due t o a low co mplexity do mai n, th e S NR pe rforman ce of th e T M algorit h m is more un ifo rm a n d smoo t h er ov er th e o th er w ell know n a lgorith m s. For th e f utur e wo rk, it w ill be in terestin g t o i mplement th e pr opo s ed appr oach f o r asy n ch r onous sy stems to achiev e de sira ble B E R perfo rma n ce an d appr oximat e t h e capacity of a multi chan n el. R E FE RENCE S [ 1] S. V e rdu, Multi use r De te c tio n. Cam br idg e U ni ve rs ity P re ss , 198 8. [2] T. Ottos s on and E. Agre ll , “ML opti mal CDMA Multi use r Rec ei ve r,” Ele c tron ic s Le tt ers , Vo l. 31, Is sue - 18, pp . 1544 -1555, A ugus t 1995. [3] N. Jindal, “High SNR analy si s of MIMO bro adc as t chan ne ls ,” P roce ed ings of intern ation al sy mpo sium o n informa tion theo ry , V ol. 4, n o. 9, p p. 2310 – 2314, Sep t. 2005 [4] Sye d S. Riz vi , Kh aled M. El lei th y, and A as ia Rias at, “T rans fo rm atio n Matri x Alg orit hm for Red ucin g the Com putati on al Com p le xit y of Multi use r Rec e ive rs fo r DS- CDMA Wirel es s Sys te m s ,” Wireless T eleco mmu nica tion Symp osiu m (W T S 2 00 7) , Pom o na, Calif orn ia, A pril 26-28 2007. [5] A. Loz an o, M. An to ni a, and S. Ve rd ú, “ High - SN R Pow er Off set in Multi ante n na Com m uni cati on ,” IEEE T rans on informa tion the ory , V ol. 51, No , 12, p p. 4134- 4151, Dec 2005. [6] Z. T ian, H. Ge, and L. Sch arf , “ Low -co m pl ex ity m ultius e r de te c tio n and re d uce d- ra nk W ie ne r fil te rs fo r ultra-w id e ban d multip le a cc e s s, ” IEEE Int ern atio nal Con f e ren c e on Ac o ust ics , Spe e ch , and Sign al Pro ce s s in g, V ol . 3, pp . 621-624, 2005. [7] E. Del, R. Fantac c i, S. M oro s i, S. Marapo di, “A low -co m pl ex ity mult iuse r de te ct or fo r asyn c hro no us CDMA QP SK adaptiv e a nte n na 2 12 22 32 42 5 2 62 72 82 92 102 5 10 15 20 25 30 35 40 45 50 U S E R S S N R ML ND P rop o s ed Fig ure 8. A p pro xi mate v alue of SNR (d B) v e rs us num be r o f us er s (K =102, he avi ly- loade d ne tw o rk) w ith a ran do m am oun t o f v arianc e f or a s yn c hro n ous sy s te m in an A WGN ch ann e l. 2 1 2 22 3 2 42 52 62 7 2 5 10 15 20 25 30 35 40 U S E R S S N R ML N D Prop osed Fig ure 7. A p pro xi mate v alue of SNR (d B) v e rs us num be r o f us er s (K =72) w ith a rand om amo unt of v arian ce f or a s yn c hro no us DS- CDMA s ys te m in a Gauss ian c han ne l. (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 33 array s ys te m s ,” Wire le ss Netw o rks , Kl uwe r Ac ade m ic P ubli sh e rs . Man ufac ture d in The Nethe rlan ds , Vol . 9, Iss ue 4, pp. 373-378, July 2003 . [8] C. Pie ro, Multiuser De tection in CDMA Mobile Termina ls . A rtec h H ous e, In c. , 2002. Syed S. Rizvi is a Ph.D. stude nt of Com p uter Scie n ce and Eng ine e rin g at U niv e rs ity of Brid ge p ort . He re ce iv ed a B.S . in Com pute r Engi ne e ring from Sir Sy ed Uni ve rs ity of Eng ine e rin g and Tech n olo g y and an M. S. in Com p uter Eng in e eri ng fro m Old Dom in io n U niv e rs ity in 2 001 and 20 05, resp e ct ive ly . In the pas t, he has don e res e arch on bioi nf o rm atic s pro je c ts wh e re h e in ve s ti gate d th e us e o f Lin ux base d clust er se arc h en gin e s f or f ind in g the de si red prote in s in input and outp uts seq uen c es f rom multi pl e datab ase s . Fo r last thre e year, his res e arch f oc use d prim arily on the mod e lin g a nd sim ulatio n of wid e ra ng e paralle l/ dis tr ibute d s y s tem s an d the w eb bas ed t raini ng ap pl ic ation s . Sye d Riz vi is th e au tho r o f 68 sc ho larly pub lic atio ns in vario us areas . His curre nt res e arc h f oc use s on the de s ig n, im p le me n tatio n and c om p aris on s o f alg orit hm s in the areas o f mult iuse r com m unic atio ns , m ultip ath sig nals dete c tio n, multi- acc e ss inte rf ere n ce e st im atio n, co m putatio n al co m ple x ity and co m bin ato rial op tim iz atio n of m ultiuse r rec e iv ers , pee r- to-p e er netw orking , net w ork se c urity , an d rec o nf igurable c op ro ce s s or and FP GA b ase d arc hit ec ture s . AA SIA RIASA T is an As s o ci ate P rof e s s or of Com pute r Sc ie nc e at Co llag e of Busine s s Manag em ent (CBM ) si nc e May 2006. S h e rec e ive d a n M.S. C. in Com p uter Scie nc e fro m the Un iv er si ty of Sin dh , and an M.S in Com p uter Scie nc e f rom Old Domi nio n Un iv er si ty in 2005 . Fo r last on e year, she is wo rking as one o f the act ive m em b er s o f the w ire le ss and mo b ile co m mun ic atio ns (WMC) lab res e arc h group of Un ive rs ity o f Brid ge p ort , Brid g ep o rt CT. In WMC res e arc h group , she is main ly res p on s ibl e for sim ulatio n des ig n for all the res e arc h w ork. A as ia Rias at is the author or co- a utho r o f mo re than 40 sc h ol arly publ icat ion s in vario us areas . Her res earc h int ere s ts inc lude mo d el ing and sim ulatio n, we b - bas e d vis ualiz atio n, virt ual realit y, data co m pre s s io n, and alg ori th ms o p tim iz atio n. KHALED ELLEITHY rece iv e d the B .Sc . deg re e in com pute r sc ie nc e and autom atic co nt rol fro m Al ex and ria U niv e rs ity in 19 83, the MS Degre e in co m pute r netw o rks fro m the sam e univ ers ity in 1986, a nd the MS and Ph .D. de gre e s in com p uter sc ien c e fro m The Ce nte r fo r Ad van ce d Comp ute r Stud ie s at th e Un ive rs ity of Lo uisi ana at Laf aye tte in 198 8 and 1990, res p e cti ve ly . Fro m 1 983 to 1986, he w as w ith the Com pute r Sc ie n ce Departm e nt , A lex and ria Uni ve rs ity , Eg yp t, a s a le cture r. F rom Se p tem ber 1990 to May 199 5 he w o rked as an as s is tant pro f e ss o r at th e Dep artm e nt of Comp ute r Eng in ee rin g , Kin g Fahd Un ive rs it y of Pe tro le um an d Mi ne rals , Dh ahran , Saudi A rabi a. Fro m May 1995 to Dec e m be r 2000, h e has worke d as an As s oc iate Prof e s so r in the sam e de part me n t. In January 2000 , Dr. Elle it hy has join e d th e Dep artm en t of Com p uter Sc ie n ce an d Eng in e eri ng in U n iv ers ity (IJCSIS) International Journal of Computer Science and Information Security Vol. 3, No. 1, 2009 34
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment