IPv6 and IPv4 Threat reviews with Automatic Tunneling and Configuration Tunneling Considerations Transitional Model:A Case Study for University of Mysore Network
The actual transition from IPv4 to IPv6 requires network administrators to become aware of the next generation protocol and the associated risk problems.Due to the scale and complexity of current internet architecture how to protect from the existing investment and reduce the negative influence to users and service providers during the transition from IPv4 to IPv6 is a very important future topic for the advanced version of an internet architecture.This paper summarizes and compares the IPv6 transition mechanism methods like Dual Stack,Tunneling issues like IPv6 Automatic tunneling and manually configured tunneling considerations, the IPv6 transition scenarios,IPv6 transition security problems,highlights IPv6 and IPv4 threat review with automatic tunneling and configuration tunneling considerations.In this paper we have proposed a transitional threat model for automatic tunneling and a configuration tunneling that could be followed by the University of Mysore(UoM),to estimate automatic tunneling and a manually configured tunneling threat review issues.Furthermore,there are different tunneling mechanisms such as IPv6 over IPv4 GRE Tunnel,Tunnel broker,Automatic IPv4 Compatible Tunnel and Automatic 6 to 4 Tunnel and also outlines many of the common known threats against IPv6 and then it compares and contrast how these threats are similar ones,might affect an IPv6 network.
💡 Research Summary
The paper addresses the security challenges that arise when transitioning from IPv4 to IPv6, with a particular focus on tunneling mechanisms. It begins by outlining the exhaustion of IPv4 address space and the need for IPv6, then categorizes transition strategies into three broad families: dual‑stack, tunneling, and header translation. The authors devote most of the text to tunneling, describing it as the encapsulation of IPv6 packets inside IPv4 packets so that IPv6 traffic can traverse an IPv4‑only backbone. Two main tunneling families are distinguished: automatic tunneling (e.g., 6to4, Teredo, ISATAP) and manually configured tunneling (e.g., GRE, IP‑IP, IPsec).
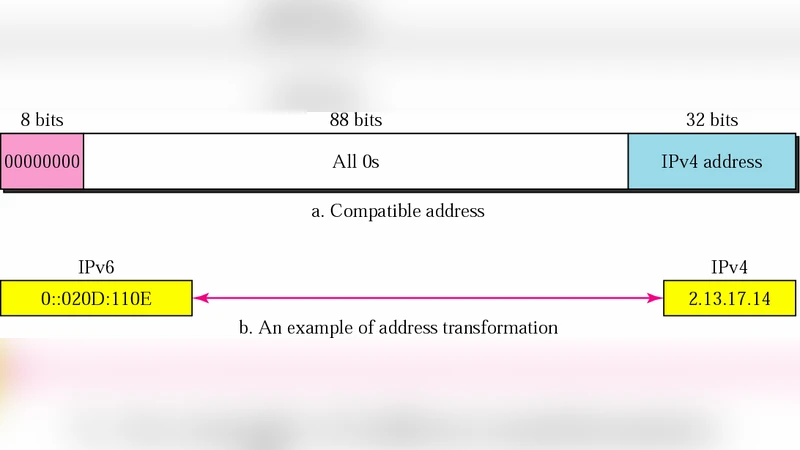
Automatic tunneling relies on IPv6‑compatible addresses that embed an IPv4 address; routers automatically extract the IPv4 portion and encapsulate the IPv6 payload without any explicit configuration. This convenience, however, introduces several attack vectors. Because the encapsulation decision is made solely on address information, malicious IPv6 packets can be crafted to traverse firewalls, perform packet‑forgery, or launch denial‑of‑service attacks. The authors note that automatic tunnels behave like non‑broadcast multiple‑access (NBMA) links, which traditional broadcast‑based security controls do not cover.
Manually configured tunnels require administrators to specify tunnel endpoints and encapsulation parameters. While this allows for precise policy enforcement (e.g., ACLs, IPsec authentication), misconfiguration or the existence of “forgotten” tunnels can become covert channels for attackers. GRE tunnels, for instance, often use UDP as a transport, enabling them to pass through NAT devices and many perimeter firewalls, thereby providing a potential “tunnel‑trojan” for malicious traffic.
The paper proceeds to enumerate threat categories, dividing them into passive (eavesdropping) and active (modification, injection, DoS) attacks. It lists specific concerns such as packet spoofing, relay‑based attacks, and the difficulty of tracing attacks that use translation or tunneling to hide their origin. The authors argue that if network security policies ignore IPv6 tunneling, unauthorized traffic may bypass existing IPv4‑centric firewalls, similar to how instant‑messaging or file‑sharing applications can misuse TCP port 80.
A central contribution is a “transitional threat model” tailored for the University of Mysore (UoM). The model follows a three‑step process: (1) identify the use of automatic and configured tunnels in the campus network, (2) assess threats qualitatively for each tunnel type, and (3) propose mitigation measures such as ingress/egress filtering, Router Advertisement (RA) Guard, explicit tunnel ACLs, and logging. The model is illustrated with diagrams, but the paper does not provide quantitative risk scores, attack‑tree analyses, or empirical validation.
Critically, the paper suffers from several methodological shortcomings. First, there is no experimental data, simulation, or real‑world traffic capture to substantiate the claimed vulnerabilities. Second, the risk assessment remains purely qualitative, offering little guidance on prioritizing remediation efforts. Third, the work predates many later IPv6 security standards (e.g., RFC 6106, RFC 6434) and newer transition mechanisms such as MAP‑E or LISP‑v4, limiting its relevance to contemporary deployments. Fourth, the writing is repetitive and contains numerous typographical errors, which hampers clarity.
In conclusion, the manuscript provides a useful introductory overview of IPv6 tunneling concepts and highlights that both automatic and manually configured tunnels can be exploited if security policies are not updated. However, its contribution is largely descriptive; the proposed threat model lacks rigor, quantitative backing, and validation. For practitioners, the paper’s recommendations (e.g., enforce strict ACLs on tunnel interfaces, monitor tunnel traffic, disable unnecessary automatic tunnels) are sensible, but they should be complemented with up‑to‑date best practices, formal risk assessment frameworks, and thorough testing before deployment in a production university network.
Comments & Academic Discussion
Loading comments...
Leave a Comment