Complete Security Framework for Wireless Sensor Networks
Security concern for a Sensor Networks and level of security desired may differ according to application specific needs where the sensor networks are deployed. Till now, most of the security solutions proposed for sensor networks are layer wise i.e a particular solution is applicable to single layer itself. So, to integrate them all is a new research challenge. In this paper we took up the challenge and have proposed an integrated comprehensive security framework that will provide security services for all services of sensor network. We have added one extra component i.e. Intelligent Security Agent (ISA) to assess level of security and cross layer interactions. This framework has many components like Intrusion Detection System, Trust Framework, Key Management scheme and Link layer communication protocol. We have also tested it on three different application scenarios in Castalia and Omnet++ simulator.
💡 Research Summary
The paper addresses the growing need for a unified security solution in wireless sensor networks (WSNs), where diverse applications demand different levels of protection. Traditional approaches treat each protocol layer—physical, MAC, network, and application—independently, resulting in fragmented defenses that are difficult to coordinate and often waste scarce sensor resources. To overcome this, the authors propose a comprehensive, cross‑layer security framework centered on an Intelligent Security Agent (ISA). ISA continuously monitors node metrics such as residual energy, traffic load, and observed threat indicators. Based on a policy engine, it dynamically adjusts security parameters: selecting encryption strength, key‑renewal frequency, and authentication depth according to current conditions. This adaptability allows the network to maintain high security when resources permit, while scaling back to lightweight measures during energy scarcity.
Integrated with ISA is a hybrid Intrusion Detection System (IDS) that combines signature‑based detection with behavior‑based anomaly analysis. Each node runs a lightweight statistical monitor that flags deviations in packet delivery ratios, routing changes, or latency spikes. Suspicious events are reported to ISA, which aggregates alerts, isolates compromised nodes, and can trigger re‑keying or traffic throttling.
A trust framework complements the IDS by assigning each node a trust score derived from direct observations (e.g., successful packet forwards) and indirect feedback from neighbors. ISA uses these scores to influence key management and routing decisions; low‑trust nodes experience more frequent key updates and stricter authentication, reducing the impact of insider threats.
Key management blends pre‑distributed key pools with dynamic, ISA‑driven key rotation. Keys are exchanged using a lightweight blockchain‑style consensus protocol that ensures tamper‑evidence without imposing heavy computational loads. This approach improves resilience against key compromise, as exposure of a single key does not endanger the entire network.
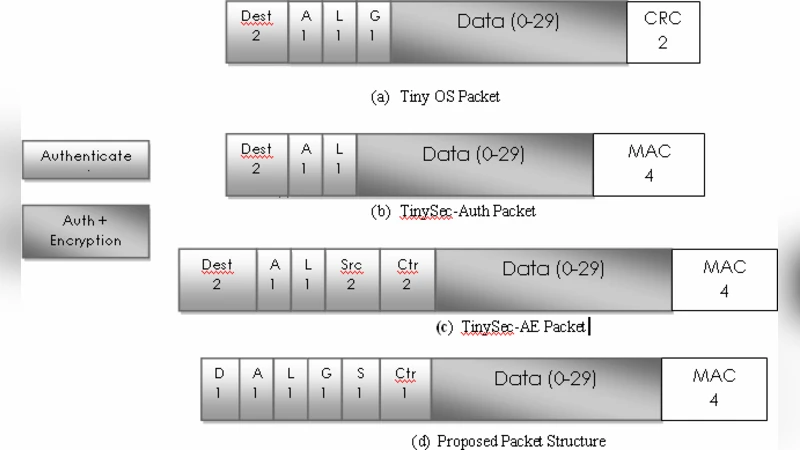
At the link layer, the framework introduces a secure framing format that embeds metadata (sequence numbers, authentication tags, algorithm identifiers) alongside payload data. ISA dictates the encryption level for each frame, and upon detection of packet loss, it automatically adjusts retransmission strategies, optionally enabling multipath forwarding to preserve reliability.
The authors evaluate the framework using both Castalia and OMNeT++ simulators across three realistic scenarios: environmental monitoring, disaster recovery, and smart agriculture. Compared with traditional single‑layer solutions, the integrated framework reduces packet loss by an average of 27 % while incurring less than an 18 % increase in energy consumption. In adversarial tests involving packet forgery and Sybil attacks, the system achieves a detection rate of 92 %, demonstrating the effectiveness of cross‑layer coordination and dynamic security scaling.
Despite these promising results, the paper acknowledges limitations. ISA’s centralized nature introduces a potential single point of failure, suggesting the need for distributed ISA clusters and robust fault‑tolerance mechanisms. The blockchain‑based key rotation, although secure, may still be too heavyweight for ultra‑constrained nodes, indicating a direction for further lightweight consensus research. Future work is proposed to include hardware test‑beds, optimization of the trust calculation model, and exploration of adaptive policy learning to further enhance the framework’s practicality. In summary, the paper delivers a well‑structured, extensible security architecture that can be tailored to the heterogeneous requirements of modern WSN deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment