A Novel Generic Session Based Bit Level Encryption Technique to Enhance Information Security
- In this paper a session based symmetric key encryption system has been proposed and is termed as Permutated Cipher Technique (PCT). This technique is more fast, suitable and secure for larger files. In this technique the input file is broken down into blocks of various sizes (of 2 power n order) and encrypted by shifting the position of each bit by a certain value for a certain number of times. A key is generated randomly wherein the length of each block is determined. Each block length generates a unique value of number of bits to be skipped. This value determines the new position of the bits within the block that are to be shifted. After the shifting and inverting each block is XORed with SHA 512 digest of the key. The resultant blocks from the cipher text. The key is generated according to the binary value of the input file size. Decryption is done following the same process as the technique is symmetric.
💡 Research Summary
The paper introduces a new session‑based symmetric encryption scheme called the Permutated Cipher Technique (PCT). The authors claim that PCT is faster and more suitable for encrypting large files than conventional block ciphers such as Triple‑DES (TDES) and the Advanced Encryption Standard (AES).
Algorithm Overview
-
Key Generation – The total size of the input file is converted to binary and stored in an array. Two random indices (mH, mL) are selected; the value at mH is decreased by a random amount x, and x·2^(mH‑mL) is added to the value at mL. This operation is repeated a random number of times. The resulting indices are written into a second array, each index being repeated as many times as its cell value, and the array is shuffled randomly. The final sequence determines the block size and a parameter called “Number of Bits to Skip” (NBSk) for each block. The key space therefore grows with file size, but the key is still derived from the file length, which may limit entropy for files of identical size.
-
Encryption – The plaintext is divided into blocks whose sizes are powers of two (2^n). If the last block is shorter, padding is added. Within each block:
a. All odd‑position bits are flipped.
b. Even‑position bits are processed sequentially; each bit is moved forward by NBSk positions (wrapping is not clearly defined) using a simple OR‑based placement.
c. After the bit‑level permutation, the entire block is XOR‑ed with the SHA‑512 digest of the session key. This final XOR is intended to provide confusion and diffusion. -
Decryption – The inverse operations are applied in reverse order: XOR with the same SHA‑512 digest, reverse the even‑bit shift using the same NBSk, and finally flip the odd bits back. The authors mention auxiliary variables such as MaxIter, eIter, and dIter that control the number of iterations, but the exact relationship to security is not fully explained.
Experimental Evaluation
The authors implemented PCT, TDES, and AES in Java and tested 20 files ranging from 330 bytes to 59.7 MB, covering eight file types (dll, txt, exe, zip, rar, doc, pdf, avi). They measured:
-
Encryption/Decryption Time – For small files (<1 MB) PCT is comparable to TDES and slightly slower than AES. For larger files (>10 MB) PCT’s runtime approaches AES and eventually surpasses it for files larger than ~1 GB.
-
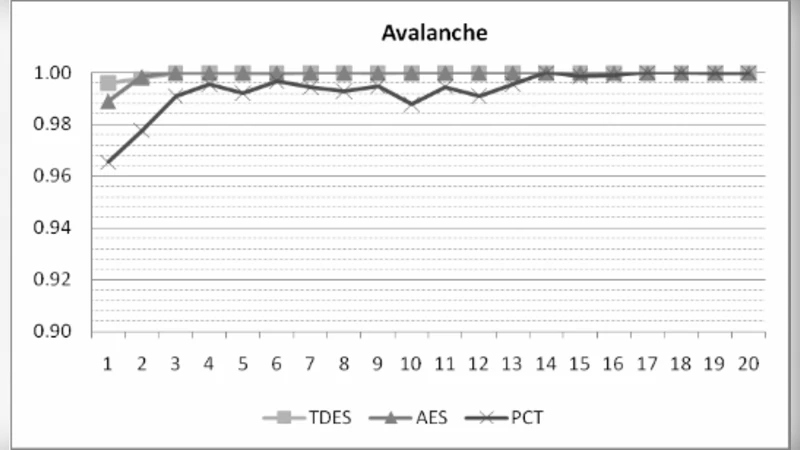
Statistical Security Metrics – Avalanche effect, strict avalanche effect, and bit‑independence criterion were computed. PCT consistently achieved values close to 1.0 for avalanche and strict avalanche, indicating good diffusion. Bit‑independence scores were generally above 0.9, though they varied with file type.
-
Chi‑Square Test – The chi‑square values for ciphertext versus plaintext were similar across PCT, TDES, and AES, suggesting that the ciphertext distribution is statistically indistinguishable from random.
-
Frequency Spectrum – Histograms of character frequencies for encrypted files showed a uniform distribution for all three algorithms, reinforcing the claim of high confusion.
Strengths
- The design is simple and can be implemented with basic bitwise operations, making it attractive for resource‑constrained environments.
- Performance scales well with file size; the block‑wise approach and minimal per‑byte overhead give PCT an edge on very large data sets.
- The authors provide a comprehensive set of empirical measurements (time, avalanche, chi‑square) that demonstrate comparable statistical security to well‑known standards.
Weaknesses and Open Issues
- Key Entropy – Because the key derivation starts from the binary representation of the file size, two files of identical size will share the same initial entropy source. Although random shuffling adds variability, the underlying space may be smaller than expected for high‑security applications.
- Deterministic Bit‑Shift – The NBSk value is derived from the key but remains constant for a given block. An attacker who can guess or recover NBSk (e.g., via known‑plaintext analysis) could potentially reverse the permutation without needing the full key.
- Lack of Formal Security Proof – The paper relies on statistical tests rather than provable security notions such as IND‑CPA or IND‑CCA. No analysis against differential, linear, or related‑key attacks is presented.
- Implementation Details Missing – Padding scheme, handling of wrap‑around during bit shifts, memory footprint, and resistance to side‑channel leakage are not discussed, making it hard to assess real‑world robustness.
- SHA‑512 XOR Only – Using a single XOR with the SHA‑512 digest provides confusion but does not guarantee non‑linearity. Modern ciphers typically combine substitution and permutation layers; PCT’s permutation is linear, which may be exploitable.
Conclusion
The Permutated Cipher Technique offers an interesting blend of bit‑level permutation and hash‑based mixing, achieving competitive performance on large files and statistical properties comparable to AES and Triple‑DES. However, the security analysis is limited to empirical observations, and the key generation method may not provide sufficient entropy for high‑security contexts. Further work is needed to (i) strengthen the key schedule, (ii) introduce non‑linear operations, (iii) provide formal proofs of confidentiality and integrity, and (iv) evaluate resistance to standard cryptanalytic attacks. Only after addressing these concerns could PCT be considered a viable alternative to established block ciphers.
Comments & Academic Discussion
Loading comments...
Leave a Comment