Cooperative Jamming for Wireless Physical Layer Security
Cooperative jamming is an approach that has been recently proposed for improving physical layer based security for wireless networks in the presence of an eavesdropper. While the source transmits its message to its destination, a relay node transmits…
Authors: Lun Dong, Zhu Han, Athina P. Petropulu
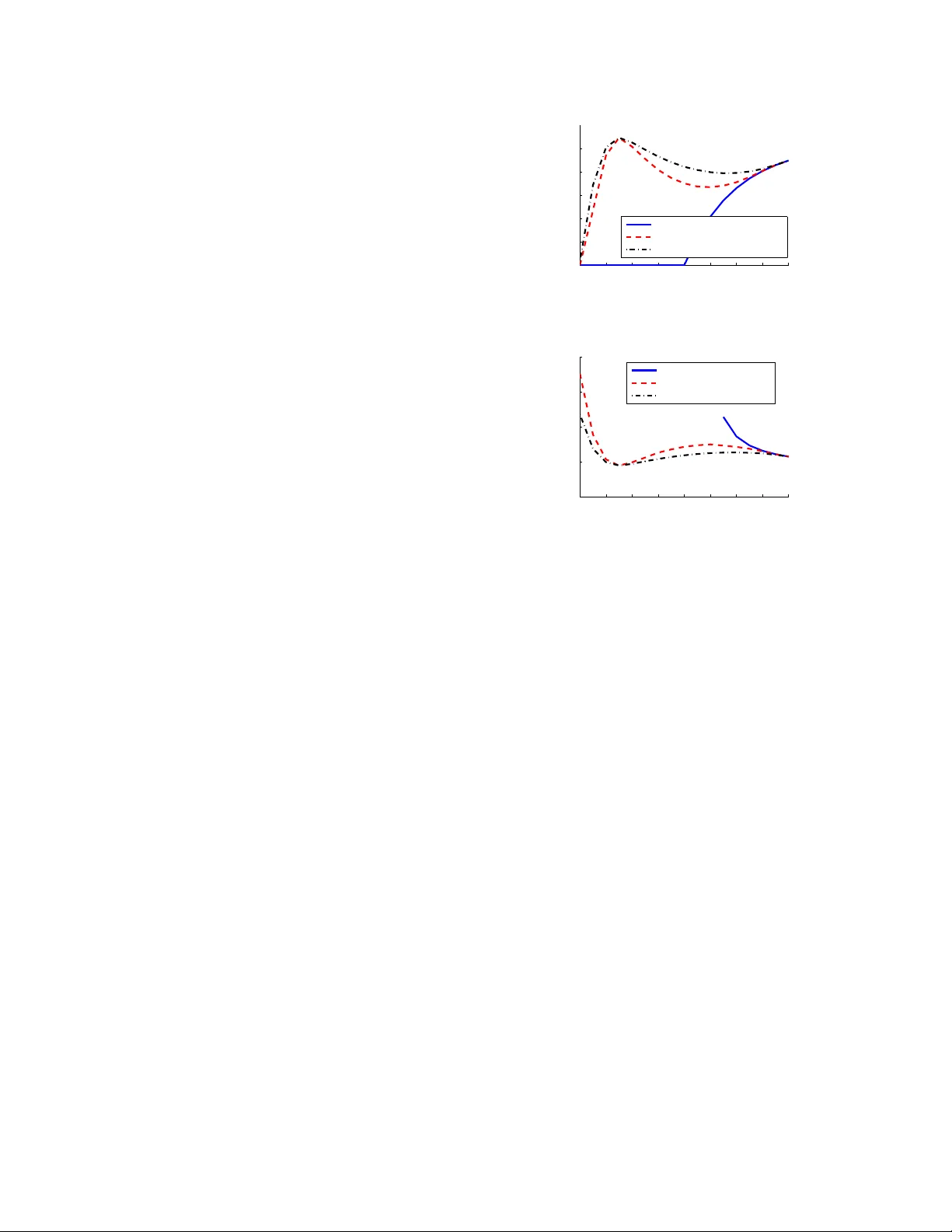
COOPERA TIVE J AMMING FOR WIRELESS PHYSICAL LA YER SECURITY Lun Dong † , Zhu Han ‡ , Athina P . P etr opulu † and H. V incent P oor ∗ † Electrical & Computer Engineering Department, Drex el University ‡ Electrical & Computer Engineering Department, Univ ersity of Houston ∗ School of Engineering and Applied Science, Princeton Univ ersity ABSTRA CT Cooperative jamming is an ap proach that has be en recently propo sed for im proving ph ysical layer based secu rity for wire- less n etworks in the presence of an ea vesdr opper . While the source transmits its m essage to its destination, a r elay node transmits a jamming signal to create interf erence at the eav es- dropp er . In this p aper, a scen ario in which the relay is equipped with mu ltiple antenn as is con sidered. A n ovel system d esign is p roposed fo r de termining the antenn a weights and trans- mit power of so urce and relay , so that the system secrecy rate is maximized subject to a total transmit po wer constraint, or , the transmit power is minimized su bject to a secre cy rate constraint. Since the op timal solu tions to these p roblems are difficult to obtain, subop timal clo sed-form solutions are pro- posed that introduc e an add itional constraint, i.e. , the co m- plete nulling of jamming signal at the destination. Index T erms — physical layer security , secrecy rate, co - operation , coo perative jamming 1. INTR O DUCTION Security is an important issue in wireless networks du e to the open wireless me dium. Security against an ea vesdropper is typically achieved v ia cryp tograph ic algorithm s that are im- plemented at higher network layers [1]. Physical (PHY) layer based secur ity , a line of work tha t has attracted co nsiderable recent attention in this context, exploits th e physical ch arac- teristics of the wireless chann el to transmit messages securely (see [2] for a revie w of recen t developments in this area). The idea was pioneer ed b y W yner , who in troduced the wiretap channel and established the po ssibility of creating per fectly secure commun ication links with out r elying on priv ate (se- cret) keys [3]. W y ner showed that whe n an eavesdropper’ s channel is a degrad ed version of the main chan nel, the source and destination can exchange pe rfectly secure messages at a non-ze ro rate, while th e eavesdropper can lear n almo st n oth- ing about the messages from its ob servations. The maximal rate of perf ectly secret transmission from th e source to its in- tended de stination is nam ed the secrecy rate . Ho wever , the This research wa s suppor ted by the N ationa l Science Founda tion under Grants CNS-06-256 37, CCF-07-28208, CNS-0831371 and CNS-0910461. feasibility of traditional P HY layer security ap proaches based on single antenna systems is hamper ed by chan nel conditions: absent feedback, if the channel between source and destina- tion is worse than the channel between source and eav esd rop- per, the secrecy rate is typically zero. Some re cent work has b een prop osed to overcom e this limitation by taking advantage o f user coop eration [4]-[ 9]. For conventional wireless n etworks withou t secrecy constraints (i.e., without eavesdropper), the mo st commo n strategy f or user coop eration is cooperative relaying , e.g., the well-known decode- and-fo rward and amplify-and-f orward schemes. Co- operative relaying with secrecy constraints was discussed in [4]-[6]. Cooperative jamming is anoth er approach to imple- ment user coo peration for wireless networks with secrecy con- straints [7]-[9]. In coop erativ e jamming, a relay transmits a jam ming signal at the same tim e wh en the sourc e trans- mits the message sign al, with th e purpo se of jamming the eav e sdropper . Existing work s on cooper ativ e jamming have focused primar ily on the c ase of on e single-antenn a r elay , and on the analysis of secrecy rate and the capacity-achieving strategy . In this paper, we consider a different system model and different d esign objectives for implementin g cooperative jam- ming. W e con sider a scenario in which a sour ce comm uni- cates with a d estination in the p resence of one eavesdropper . The commu nication is aid ed b y a relay th at is equipped with multiple an tennas tha t p rovide more d egrees of freed om for the relay c hannel. Our goal is to assign weig hts to th e an- tenna elements in an optimum fashion, and also allocate the power of source and relay in an op timum fashion. The weight and power design problem is formu lated as the following opti- mization problem: (1) maximize achiev ab le s ecrecy rate sub- ject to a total transmit power constraint; or (2) minim ize the total transmit power subject to a secrecy rate constraint. W e assume that global ch annel state info rmation (CSI) is av ail- able for system design. As the o ptimum design is in gen - eral difficult, we consider a subo ptimal weigh t d esign, i. e., to co mpletely null out th e jam ming sign al at the destinatio n. From the simulation results, c ooperative jamming could sig- nificantly improve the system perfor mance especially when the eav esd ropper is close to the relay . 2. SYSTEM MODEL AND PROBL EM FORMULA TION W e consider a wireless network mod el co nsisting of one source, one tru sted relay 1 , one d estination, and one eavesdropper . The source, destinatio n an d eavesdropper are each eq uipped with a single omn i-directiona l an tenna each , while the relay h as N > 1 omn i-direction al an tennas 2 . All ch annels are as- sumed to undergo flat fading. W e denote by h S D the sou rce- destination ch annel, by h S E the sou rce-eavesdropper cha n- nel, by h S R the source-relay channel ( N × 1 column v ec tor), by h RD the rela y-destination chan nel ( N × 1 colum n vector), and by h RE the r elay-eavesdropper chann el ( N × 1 c olumn vector). A narrowband message signal s is to be transmitted from the source to the destination . Th e power of the m essage signal s is normalized to u nity , i. e, E {| s | 2 } = 1 . Th e total power budget for transmitting the message signal to its des- tination is P . Thermal noise at any node is assumed to be zero-mea n white com plex Gaussian with variance σ 2 . 2.1. Co operative jamming In cooper ati ve jamming, while the source transmits, the relay transmit a jammin g signal that is indep endent of th e so urce message. The goal is to in terfere with the eavesdropper’ s received signal. M ore specifically , the so urce tran smits the message signal √ P s s , wh ere P s is the tr ansmit power o f the source; at the same time , the relay transmits a weighted ver- sion of a com mon jamm ing signal z , i.e., w z , where w is the weigh t vector a pplied o n the N antennas. The tran s- mit power budget fo r tran smitting the jamm ing signal is thus P j = P − P s . The received signal at the destinatio n equals y d = p P s h S D s + w † h RD z + n d , (1) where n d represents white comp lex Gau ssian noise at the des- tination and ( · ) † represents th e Hermitian transpose. The re- ceiv e d signal at the eavesdropper equa ls y e = p P s h S E s + w † h RE z + n e , (2) where n e represents white co mplex Gaussian noise at the eav es- dropp er . 2.2. P roblem f ormulat ion In the pr esence o f an eavesdropper, secr ecy rate is the figu re of merit to repre sent the maximal secr ecy information r ate o ne can transmit from a sou rce to its destination. Recall that th e secrecy rate is R s = ma x { 0 , R d − R e } wher e R d is the rate from the sou rce to the destina tion and R e is the ra te from the source to t he eavesdropper [3]. W e consider the practica l case 1 W e still adopt the name “re lay”, though it is not used for relayi ng here. 2 This can also be understo od as m ultipl e relays with one antenna each. in wh ich th e system can be designed so that the secrecy rate is positive. In that case, the secr ecy r ate can b e simplified to R s = R d − R e . From (1) and (2), the secrecy rate is given by R s = log 2 1 + P s | h S D | 2 | w † h RD | 2 + σ 2 − log 2 1 + P s | h S E | 2 | w † h RE | 2 + σ 2 . (3) In the subseq uent section we d etermine the relay we ights w and the power P s based on the objectives: (i) max imize secrecy rate subject to a tran smit power constraint P 0 , or, (ii) minimize the transmit power subject to a secr ecy rate con - straint R 0 s . W e assume that global CSI is a vailable for system design (a comm on assumption in the PHY security literature), ev en the eavesdropper’ s chan nel ar e known. I nforma tion o n the ea vesdropper ’ s channel can be obtained in cases where the eav e sdropper is active in the network an d the ir transmissions can be m onitored . This is ap plicable particularly in networks combinin g multicast and un icast transmission s, in which ter- minals play dual roles as le g itimate receivers fo r some signals and ea vesdr oppers for others. 3. SYSTEM DESIGN In this section we address system design that maximiz es the secrecy rate subject to a total transmit power constraint P 0 or minimize the total transmit power subject to a secrecy rate constraint R 0 s . There are two aspects in system design : o ne is to determine the o ptimal tr ansmit power allocated to the source and to relay ; anoth er is to design th e o ptimal relay weights. In the following, we first fix P s to ob tain the weigh ts for secrecy rate maximization or p ower minimiza tion, and then find the optimal value of P s . 3.1. Secrecy rate maximizatio n From ( 3), it can be seen that the secrecy rate is a pro duct of two correlated g eneralized eigenvector problems and is in general difficult to handle. T o simplify the analysis, in t he fol- lowing we consider a sub optimal design. W e add o ne more constraint to c ompletely n ull o ut the jammin g sign al at the destination, i.e., w † h RD = 0 . Then, the pr oblem of secrecy rate maximization can be formulated as arg max w | w † h RE | 2 (4) s . t . w † h RD = 0 k w k 2 ≤ P j where k · k d enotes the vector 2-n orm. It is easy to show that the inequ ality constraint (i.e., k w k 2 ≤ P j ) in (4 ) is equiv alent to the equality constraint k w k 2 = P j by contrad iction. The Lagrang ian of (4 ) is L ( w † , λ, η ) = (2 h † RE w ) h RE + λ h RD + 2 η w (5) where λ and η are Lagran ge multip liers. As h † RE w is a scalar , by setting the Lagrang ian to ze ro, we can s ee that w is a linear combinatio n of h RD and h RE , represented as w = a h RD + b h RE . (6) Substituting w into the two equality con straints in (4), we can solve a and b . Notice that the values of a and b are not uniqu e: it is straightforward to see that, if w ∗ is the solution of (4), after rotating an arbitrary ph ase, e j θ w ∗ is still the solution of ( 4). A possible selectio n is a = − p P j µ h † RD h RE and b = p P j µ k h RD k 2 where µ = h k h RD k 4 k h RE k 2 − k h RD k 2 | h † RD h RE | 2 i − 1 / 2 . (7) Next, we find th e optimal value of P s . Noticing that the above design ed weight vector w is pr oportio nal to √ P s , le t us denote w by w = √ P s v whe re v = ( − µ h † RD h RE ) h RD + ( µ k h RD k 2 ) h RE . (8) Substituting it in to the expression o f R s , the secrecy r ate can be expressed as a f unction of P s : R s ( P s ) = log 2 e 0 + e 1 P s + e 2 P 2 s f 0 + f 1 P s (9) where e i and f i are co efficients independen t of P s and given by e 0 = σ 2 ( σ 2 + P 0 | v † h RE | 2 ) , (10) e 1 = ( | h S D | 2 P 0 − σ 2 ) | v † h RE | 2 + | h S D | 2 σ 2 , (11) e 2 = −| h S D | 2 | v † h RE | 2 , (12) f 0 = σ 2 ( σ 2 + P 0 | v † h RE | 2 ) , (13) f 1 = σ 2 ( | h S E | 2 − | v † h RE | 2 ) . (14) T akin g the der i vative o f 2 R s ( P s ) and setting to zero, the optimal value of P s is the solution of the quadr atic equ ation e 2 f 1 ( P s ) 2 + 2 e 2 f 0 P s + ( e 1 f 0 − e 0 f 1 ) = 0 . (15) In case no solution exists within (0 , P 0 ] , it holds that P s = P 0 (i.e., the case of direct transmission without jamming). 3.2. T ransmit power minimization W e again co nsider to c ompletely null o ut the jam ming signa l at the destinatio n. For a fixed P s , the pr oblem of secrecy rate maximization can be formulated as arg min w k w k 2 (16) s . t . w † h RD = 0 | w † h RE | 2 ≥ ρ where ρ = P s | h RE | 2 2 − R 0 s (1+ P s | h RD | 2 /σ 2 ) − 1 − σ 2 . By using th e La- grange multiplier method ( similarly as in Section 3. 1), it can be shown that w is a linear combin ation of h RD and h RE , represented as w = a h RD + b h RE . A p ossible selectio n is a = − µ h † RD h RE and b = µ || h RD || 2 where µ = s ρ k h RD k 2 k h RE k 2 − | h † RD h RE | 2 . (17) Let us denote w = √ ρ v wh ere v = − h † RD h RE h RD + k h RD k 2 h RE k h RD k 2 k h RE k 2 − | h † RD h RE | 2 . (18) Then, the total transmit power can be represented as P s + k w k 2 = e 0 + e 1 P s + e 2 P 2 s f 0 + f 1 P s (19) where e 0 = − (2 − R 0 s − 1) σ 2 k v k 2 , (20) e 1 = 2 − R 0 s − 1 + ( | h S E | 2 − 2 − R 0 s | h S D | 2 ) k v k 2 , (21) e 2 = 2 − R 0 s | h S D | 2 /σ 2 , (22) f 0 = 2 − R 0 s − 1 , (23) f 1 = 2 − R 0 s | h S D | 2 /σ 2 . (24) Then, the o ptimal v alu e of P s is obtained by solving the qu adratic equation which is of the same form as (15). 4. SIMULA TIONS For convenience, we consider a simple one-d imension sys- tem model, as illu strated in Fig. 1, in which th e source , re- lay , destination and eavesdropper are p laced along a lin e. T o highligh t the effects of distances, channels are modeled by a simple line-of-sight channel model including the path loss (path loss exponent is 3 . 5 ) an d a ran dom phase (u niform ly distributed). The sourc e-destination distance is fixed at 50 m, and the so urce-relay distance is fixed at 25 m (i.e., the relay is located at the midd le point of sou rce and destina tion). T he noise power σ 2 is − 100 dBm. source destination eavesdropper relay Fig. 1 . Simulation model. The position o f the eavesdropper is v aried so that the source- eav e sdropper distance varies from 10 m to 90 m. Fig. 2 shows the secrecy r ate versus th e sou rce-eavesdropper dis- tance fo r a transmit power constraint P 0 ≤ − 40 dBm. For direct transmission without the relay’ s help, the secrecy rate is positive only if the source-eavesdropper distance is larger than the so urce-destina tion distance. Also, the secrecy rate of direct transmission incr eases with the incr ease of source- eav e sdropper distance, as the rate at the eavesdropper R j de- creases. For co operative jamming , the c loser the ea vesdrop - per is located to the relay , the higher th e secrecy rate is. This is because whe n relay an d eavesdropper are close, even a small amount of power allocated to th e relay can create eno ugh in- terference at the ea vesdro pper, a nd a large amo unt of power can b e u sed for the source to transmit the message signal. When the eavesdropper moves aw ay from the relay an d closer to the sou rce, the secrecy rate decrea ses, since more jam - ming power is needed for creating larger interferen ce and less power is av ailable for the source to transmit message signa l. When th e eavesdropper moves away from both the re lay an d source, it is interesting to see th at the secrecy ra te at first de- creases, then increases, and eventually beco mes eq ual to the secrecy rate of direct transmission . Th is is b ecause when the eav e sdropper is very far fr om th e relay and the sou rce, we should spe nd mo st o f the po wer o n transmitting th e message signal. In that situation it is not worth spending a large am ount of power on the jamming signal, since the recei ved p ower of the message signal at th e eavesdropper is always small (r e- gardless of jam ming) d ue to th e large path loss. Also, as ex- pected, increasing the numb er of antennas of the relay N can always imp rove the secrecy rate. Fig. 3 shows the total transmit power versus the source- eav e sdropper distance fo r a secrecy r ate c onstraint R 0 s ≥ 1 b/s/Hz. For the curve co rrespon ding to direct tr ansmission, we only sh ow the feasible region in which the r equired se- crecy rate can b e satisfied. The curves for coo perative jam - ming exhibits similar characteristics to Fig. 2, therefore a de- tailed discussion is omitted. 5. CONCLUSIONS In this paper , we hav e addr essed practica l system d esign prob- lems for the coo perative jamming protoco l fo r secure wireless commun ications in the presence of a r elay w ith mu ltiple an - tennas. For coop erative jamm ing, while the the source trans- mits its message signal, th e relay tr ansmits a jammin g signal to create interferen ce at the eavesdropper . T he mu ltiple an- tennas at the relay can pr ovide d egrees of freedom for the relay channel and thus eliminate the effects of jamming sig- nals at the destination. Th e objectives o f our system desig n are the secrecy ra te maximization subject to a total power constraint and the transmit power minimization sub ject to a secrecy rate constraint. Simulatio n re sults show that cooper- ativ e jammin g could significantly improve the system p erfor- mance especially when the eav e sdropper is close to the relay . Future work includes the investigations of p erform ance degra- dation and system design in the pr esence of imperfect channel estimates. 10 20 30 40 50 60 70 80 90 0 0.2 0.4 0.6 0.8 1 Source−eavesdropper distance (m) Secrecy capacity (b/s/Hz) direct transmission cooperative jamming with N=3 cooperative jamming with N=6 Fig. 2 . Secrecy rate versus source-eavesdropper distance. 10 20 30 40 50 60 70 80 90 −45 −40 −35 −30 −25 Source−eavesdropper distance (m) Transmit power (dBm) direct transmission cooperative jamming, N=3 cooperative jamming, N=6 Fig. 3 . T ransmit power v e rsus source-eav esdroppe r distance. 6. REFERENCES [1] N. Sklavos and X. Zhang (Ed.), W ir eless Security and Cryptogr aphy: Specific ations and I mplement ations . CRC Press, Boca Raton, FL, 2007. [2] Y . Liang, H. V . Poor , and S. Shamai, Information Theoreti c Security . No w Publishers: Dordrecht, The Netherlan ds, 2009. [3] A. D. W yner , “The wire-tap channel, ” Bell System T ec hnical J ournal , vol. 54, no . 8, pp. 1355-1387, 1975. [4] L . Dong, Z. Han, A. Petropulu and H. V . Poor , “Secure wireless com- municati ons via cooperat ion, ” in Pr oc. 46th Annual Allerto n C onf. Com- mun., Contr ol, and Computing , Monticello, IL , Sept . 2008. [5] L . Dong, Z. Han, A. Petropulu, and H. V . Poor , “ Amplify-an d-forwa rd based cooperatio n for secure wireless communications, ” in Proc. IEEE Int’l Conf . Acoust. Speec h Signal P r oc. , T aipei , T aiwa n, Apr . 2009. [6] V . Aggarw al, L . Sankar , A. R. Calderbank, and H. V . Poor , “ Secrec y capac ity of a class of orthogona l relay ea vesdropper channels, ” Eurasip J ournal on W irele ss Communications and Networking , submitte d in Dec. 2008. [Online ]. A vai lable : http://arxi v .org/abs/ 0812.2275 [7] R. Negi and S. Goelm, “Secret communicat ion using artificia l noise, ” in P r oc. IE EE V ehicu lar T ec h. Conf , v ol. 3, Dallas TX, pp. 1906-19 10, Sept. 2005. [8] E . T e kin and A. Y ener , “The general Gaussian multip le access and two- way wire-tap channels: Achie vable rates and cooper ati ve jamming, ” IEEE T rans. Inf . Theory , vol. 54, no. 6, pp. 2735-2751, Jun. 2008. [9] L . Lai and H. El Gamal , “The relay-ea vesdroppe r channe l: Cooperation for secrec y , ” IEEE Tr ans. Inf. Theory , vol. 54, no. 9, pp. 4005 - 4019, Sept. 2008.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment