A Proposed Algorithm to improve security & Efficiency of SSL-TLS servers using Batch RSA decryption
Today, Internet becomes the essential part of our lives. Over 90 percent of the ecommerce is developed on the Internet. A security algorithm became very necessary for producer client transactions assurance and the financial applications safety. The rsa algorithm applicability derives from algorithm properties like confidentiality, safe authentication, data safety and integrity on the internet. Thus, this kind of networks can have a more easy utilization by practical accessing from short, medium, even long distance and from different public places. Rsa encryption in the client side is relatively cheap, whereas, the corresponding decryption in the server side is expensive because its private exponent is much larger. Thus ssl tls servers become swamped to perform public key decryption operations when the simultaneous requests increase quickly .The batch rsa method is useful for such highly loaded web server .In our proposed algorithm by reducing the response time and clients tolerable waiting time an improvement in performance of ssl tls servers can be done. The proposed algorithm should provide the reasonable response time and optimizes server performance significantly. At Encryption side, to withstand many attacks like brute force attack, subtle attack etc. we also adapted a parameter generation method, which sieve all the parameters strictly, and filter out every insecure parameter.
💡 Research Summary
The paper addresses a well‑known performance imbalance in SSL/TLS handshakes: RSA encryption on the client side is cheap, while RSA decryption on the server side is computationally heavy because the private exponent d is much larger than the public exponent e. When many clients connect simultaneously, the server becomes a bottleneck. To mitigate this, the authors propose a combined batch‑RSA and mini‑batching scheme together with an optimal batch‑size scheduling algorithm.
First, the algorithm determines a maximum batch size based on the arrival rate λ and the client‑tolerable waiting time Tₜ using the formula maxbatchsize = ⌊0.4 λ Tₜ + 1⌋. It then iterates over possible batch sizes b (2 ≤ b ≤ maxbatchsize) and computes the expected mean response time T_b. If T_b < b/λ, that b is selected as the optimal batch size; otherwise the system falls back to conventional RSA decryption.
Having fixed b, the server creates b queues, each associated with a distinct public exponent eᵢ. Client requests are assigned to queues in a round‑robin fashion. When every queue contains at least one request, a full batch decryption is performed. To avoid excessive waiting when some queues are empty, the scheme introduces “mini‑batching”: if the head request of any queue exceeds a pre‑defined maximum timer (derived from Tₜ), the server immediately processes a mini‑batch consisting of the non‑empty queues. This dynamic approach reduces both the mean response time and the client‑perceived latency, especially under bursty traffic conditions.
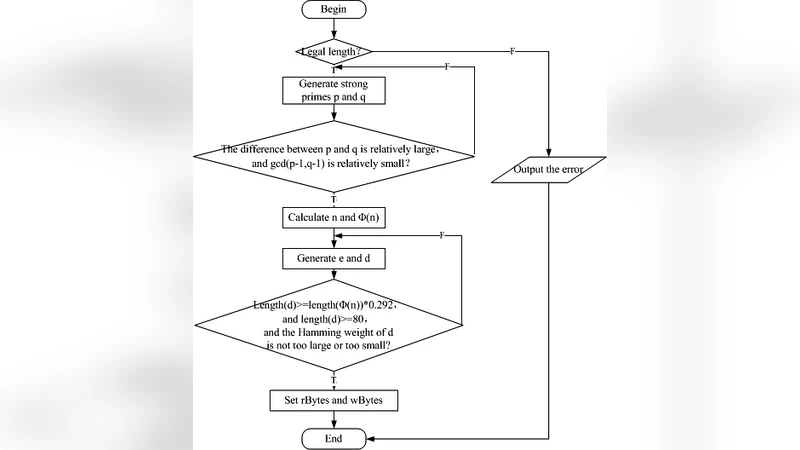
On the security side, the authors augment RSA parameter generation. They require strong primes p and q, enforce a large difference between p and q to resist square attacks, keep gcd(p‑1, q‑1) small to avoid iteration attacks, and ensure the private exponent d has a bit‑length at least 0.292·log₂ n (thereby resisting Wiener and Boneh‑Durfee attacks). The Hamming weight of d is also constrained to make exhaustive or combinatorial attacks infeasible.
The paper presents theoretical analyses: a graph comparing mean response time of the proposed batch scheme against a non‑batch baseline, a table showing how increasing the modulus size n affects the lengths of all RSA components, and a discussion of known attacks (brute‑force, factorization, small‑prime multiplication, square, iteration, low‑exponent attacks). The authors claim that their combined batch‑mini‑batch algorithm can significantly improve server throughput while the hardened parameter generation protects against a wide range of cryptanalytic attacks.
In the conclusion, the authors summarize their contributions—optimal batch scheduling, integration of mini‑batching, and a secure parameter generation method—and state that future work will involve implementing the scheme on a real SSL/TLS server to obtain empirical performance measurements. While the theoretical benefits are compelling, the paper lacks experimental validation, and the assumption of multiple distinct public exponents per request may not align with typical TLS deployments where a server uses a single key pair. Consequently, practical adoption would require further engineering and performance testing.
Comments & Academic Discussion
Loading comments...
Leave a Comment