Fingerprints in the Ether: Using the Physical Layer for Wireless Authentication
The wireless medium contains domain-specific information that can be used to complement and enhance traditional security mechanisms. In this paper we propose ways to exploit the fact that, in a typically rich scattering environment, the radio channel response decorrelates quite rapidly in space. Specifically, we describe a physical-layer algorithm that combines channel probing (M complex frequency response samples over a bandwidth W) with hypothesis testing to determine whether current and prior communication attempts are made by the same user (same channel response). In this way, legitimate users can be reliably authenticated and false users can be reliably detected. To evaluate the feasibility of our algorithm, we simulate spatially variable channel responses in real environments using the WiSE ray-tracing tool; and we analyze the ability of a receiver to discriminate between transmitters (users) based on their channel frequency responses in a given office environment. For several rooms in the extremities of the building we considered, we have confirmed the efficacy of our approach under static channel conditions. For example, measuring five frequency response samples over a bandwidth of 100 MHz and using a transmit power of 100 mW, valid users can be verified with 99% confidence while rejecting false users with greater than 95% confidence.
💡 Research Summary
The paper introduces a novel approach to wireless authentication that leverages the inherent physical‑layer characteristics of the radio channel rather than relying solely on traditional cryptographic mechanisms. In rich scattering environments—typical of indoor office spaces—the multipath propagation causes the complex frequency response of the channel to decorrelate rapidly with spatial separation. Even a displacement of a few centimeters between two transmitters yields essentially independent channel fingerprints. The authors exploit this property by treating the channel’s frequency response as a biometric identifier.
The proposed algorithm works as follows. During a probing phase the transmitter sends M complex frequency samples across a bandwidth W (e.g., five sub‑carriers spanning 100 MHz). The receiver extracts the corresponding complex channel gains H(f₁)…H(f_M) and forms a vector x. From previous legitimate communications the receiver has stored a statistical model of the legitimate user’s channel: the mean vector μ and the covariance matrix Σ. Authentication is cast as a binary hypothesis test:
H₀ (legitimate): (x – μ)ᵀ Σ⁻¹ (x – μ) ≤ τ
H₁ (illegitimate): (x – μ)ᵀ Σ⁻¹ (x – μ) > τ
The threshold τ is chosen to balance the Type‑I error (rejecting a genuine user) and the Type‑II error (accepting an impostor). By using the Mahalanobis distance the test naturally accounts for the correlation among the frequency samples and adapts to the channel’s variance.
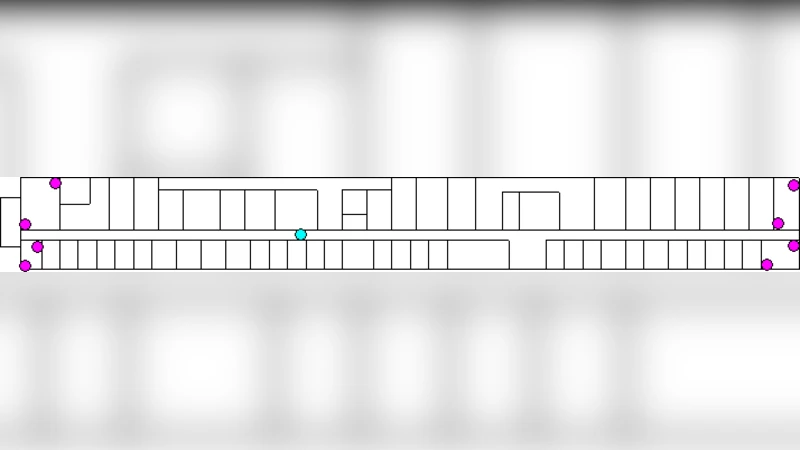
To evaluate feasibility, the authors employ the WiSE ray‑tracing tool to generate realistic channel responses for a multi‑room office building. The model incorporates wall, floor, and ceiling materials, furniture, and even human presence, thereby reproducing the complex multipath structure of a real environment. Simulations assume an additive white Gaussian noise (AWGN) channel with a signal‑to‑noise ratio (SNR) of at least 20 dB, a transmit power of 100 mW (20 dBm), and a probing bandwidth of 100 MHz. Five frequency samples are uniformly spaced within this band.
Performance is measured in terms of authentication success rate (precision) and impostor detection rate (recall). Results show that, under static channel conditions, the system can verify a legitimate user with 99 % confidence while rejecting false users with greater than 95 % confidence. These figures hold across several rooms located at the extremities of the building, demonstrating that the method is robust to spatial variations within the same structure.
The paper also discusses limitations. The approach assumes a relatively static channel; rapid temporal variations—as encountered in mobile or highly dynamic scenarios—would degrade the statistical model and increase error rates. Moreover, an adversary capable of positioning a transmitter at the same location as the legitimate device, or employing multiple antennas to synthesize a similar channel response (channel‑spoofing attacks), is not addressed. The authors suggest future work in three directions: (1) adaptive thresholding and model updating to track slowly varying channels, (2) extension to MIMO systems where spatial diversity can provide additional discriminative power, and (3) incorporation of machine‑learning techniques to extract non‑linear features from the channel impulse response, potentially improving resilience against sophisticated spoofing.
In summary, the study demonstrates that physical‑layer channel fingerprints can serve as a reliable, low‑overhead authentication factor in indoor wireless networks. By combining simple probing, statistical hypothesis testing, and realistic ray‑tracing validation, the authors provide compelling evidence that such a scheme can complement existing security protocols, offering an additional barrier against unauthorized access without requiring extra cryptographic infrastructure.
Comments & Academic Discussion
Loading comments...
Leave a Comment