Alice Meets Bob: A Comparative Usability Study of Wireless Device Pairing Methods for a "Two-User" Setting
When users want to establish wireless communication between/among their devices, the channel has to be bootstrapped first. To prevent any malicious control of or eavesdropping over the communication, the channel is desired to be authenticated and confidential. The process of setting up a secure communication channel between two previously unassociated devices is referred to as “Secure Device Pairing”. When there is no prior security context, e.g., shared secrets, common key servers or public key certificates, device pairing requires user involvement into the process. The idea usually involves leveraging an auxiliary human-perceptible channel to authenticate the data exchanged over the insecure wireless channel. We observe that the focus of prior research has mostly been limited to pairing scenarios where a single user controls both the devices. In this paper, we consider more general and emerging “two-user” scenarios, where two different users establish pairing between their respective devices. Although a number of pairing methods exists in the literature, only a handful of those are applicable to the two-user setting. We present the first study to identify the methods practical for two-user pairing scenarios, and comparatively evaluate the usability of these methods. Our results identify methods best-suited for users, in terms of efficiency, error-tolerance and of course, usability. Our work sheds light on the applicability and usability of pairing methods for emerging two-user scenarios, a topic largely ignored so far.
💡 Research Summary
The paper “Alice Meets Bob: A Comparative Usability Study of Wireless Device Pairing Methods for a ‘Two‑User’ Setting” addresses a gap in the secure device pairing (SDP) literature: most prior work assumes a single user controls both devices, while many real‑world scenarios involve two distinct users each holding one device. The authors first conduct a comprehensive survey of existing SDP protocols, categorising roughly thirty methods by the auxiliary human‑perceptible channel they employ (visual, auditory, tactile, or physical contact) and by the authentication primitive (numeric comparison, string comparison, QR‑code, beep pattern, vibration pattern, etc.). From this taxonomy they identify seven methods that can realistically be executed when two users must cooperate without sharing physical control of each other’s device.
A user study with 30 participant pairs (60 individuals) was designed to evaluate these seven methods. Each pair performed all methods in a counter‑balanced order while the researchers recorded objective metrics (pairing time, success/failure, type of error – false positive or false negative) and subjective metrics (perceived workload, satisfaction, trust). The experimental environment varied lighting and ambient noise to test robustness, and participants were also asked about their prior familiarity with each other (high vs. low trust condition).
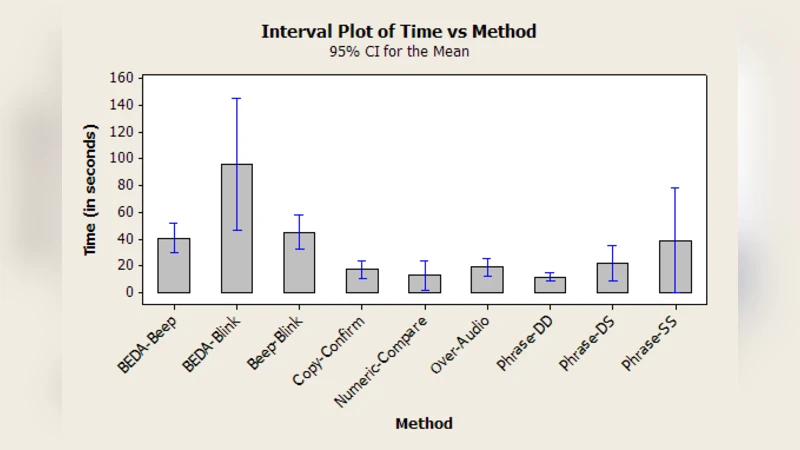
Results show that visual‑based methods—specifically numeric comparison (both devices display the same short number) and QR‑code scanning—outperform all others. They achieved the highest success rates (96 % and 94 % respectively) and the shortest average completion times (≈12 s for numbers, ≈14 s for QR codes). Users rated these methods as the most intuitive and least cognitively demanding. String comparison performed slightly worse (≈18 s, 92 % success) due to the higher effort required to read and match longer alphanumeric sequences.
Auditory methods (beep‑pattern comparison) suffered significantly in noisy environments, with a success rate of only 72 % and higher perceived workload. Tactile vibration‑pattern comparison was the least efficient, taking an average of 22 s and producing a 15 % error rate, reflecting the difficulty of reliably distinguishing vibration sequences without training. Physical‑contact pairing (simultaneous touch or shaking) was the fastest (≈5 s) but required both users to physically handle each other’s device, raising concerns about hygiene, user comfort, and practical feasibility in many contexts. Moreover, its success depended heavily on the trust relationship: participants who knew each other were more willing to accept contact‑based pairing, whereas strangers rejected it.
The study also uncovered that trust level influences method preference. In low‑trust pairings (strangers), visual verification was perceived as the most secure, while in high‑trust pairings (friends or family) participants were more open to contact‑based methods as an additional “human‑in‑the‑loop” assurance.
From these findings the authors distill four design principles for two‑user SDP: (1) favour simple visual cues that users can quickly compare; (2) choose channels that are robust to environmental variations, avoiding reliance on sound or vibration in uncontrolled settings; (3) minimise the need for physical contact to broaden applicability; and (4) incorporate optional trust‑based enhancements (e.g., allowing a contact step when users are acquainted) to balance security and usability.
The paper concludes by outlining future research directions: longitudinal field studies in real IoT deployments, extensions to multi‑user (more than two) scenarios, and the development of semi‑automated auxiliary channels (e.g., automatic camera‑based visual verification or secure acoustic handshakes) that retain usability while strengthening security guarantees.
Overall, this work provides the first empirical evaluation of SDP methods specifically for two‑user contexts, delivering actionable insights for designers of consumer wireless devices, IoT hubs, and collaborative applications where secure, user‑friendly pairing is essential.
Comments & Academic Discussion
Loading comments...
Leave a Comment