Ftklipse - Design and Implementation of an Extendable Computer Forensics Environment: Software Requirements Specification Document
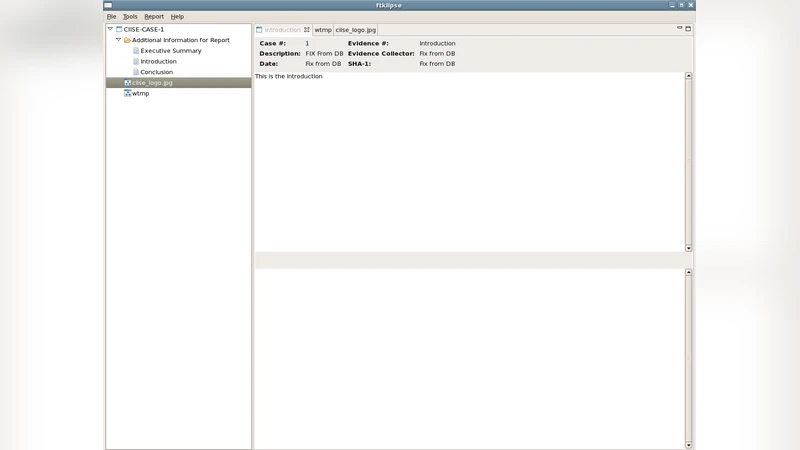
The purpose behind this article is to describe the features of Ftklipse, an extendable platform for computer forensics. This document designed to provide a detailed specification for the developers of Ftklipse. Ftklipse is a thick-client solution for forensics investigation. It is designed to collect and preserve evidence, to analyze it and to report on it. It supports chain of custody management, access control policies, and batch operation of its included tools in order to facilitate and accelerate the investigation. The environment itself and its tools are configurable as well and is based on Eclipse.
💡 Research Summary
The paper presents a comprehensive Software Requirements Specification (SRS) for Ftklipse, an extensible, Eclipse‑based thick‑client platform designed to support the full lifecycle of digital forensic investigations. The authors begin by outlining the motivation behind the project: existing forensic tools are often single‑purpose, lack integration, and provide limited extensibility. Ftklipse addresses these gaps by leveraging the Eclipse Rich Client Platform (RCP) to obtain a modular architecture, plug‑in management, and a rich user‑interface framework that can be customized for diverse investigative scenarios.
The system is divided into four primary subsystems:
-
Evidence Management – Organizes digital evidence into a hierarchical model of cases and items. Each item stores immutable metadata (collection timestamp, hash values, custodian, etc.) in a relational database. All state transitions and access events are recorded in an append‑only, tamper‑evident log to satisfy chain‑of‑custody requirements.
-
Access Control – Implements a Role‑Based Access Control (RBAC) scheme. Users, groups, and roles are defined, and fine‑grained permissions (read, write, delete, execute) are assigned per role. This enables multiple investigators to work concurrently while preserving legal integrity of the evidence.
-
Analysis & Batch Processing – Wraps external forensic utilities (e.g., Autopsy, Sleuth Kit, FTK Imager) behind a standardized plug‑in interface. A batch engine models workflows as Directed Acyclic Graphs (DAGs), automatically handling dependencies, queuing, and result attachment to evidence items. The engine also supports scheduled execution, facilitating large‑scale, repeatable analyses.
-
Reporting & Export – Generates investigation reports in HTML, PDF, and XML using template‑driven rendering. Reports automatically embed evidence hashes, custody logs, and analysis snapshots, thereby enhancing reproducibility and courtroom readiness.
Security considerations are woven throughout the specification. All network communication is protected by TLS 1.2 or higher, while stored data is encrypted with AES‑256 and integrity‑checked using HMAC‑SHA‑256. Plug‑ins must be digitally signed; the platform validates signatures at load time to prevent malicious code injection. The immutable log is reinforced with a Merkle‑Tree structure, and any tampering attempt triggers an immediate alert.
The SRS distinguishes functional requirements (FR) from non‑functional requirements (NFR). Key functional requirements include creation and editing of evidence items, dynamic plug‑in loading, batch job scheduling, and automated report generation. Each FR is accompanied by detailed input‑process‑output scenarios, success criteria, and failure handling. Non‑functional requirements cover performance (support for 20 concurrent users with average response time < 2 seconds), scalability (each plug‑in ≤ 150 MB memory footprint), availability (99.5 % annual uptime), and maintainability (≥ 80 % code coverage in automated tests).
Testing strategy comprises unit, integration, system, and forensic readiness tests. Particular emphasis is placed on verifying the immutability of custody logs using the Merkle‑Tree approach, and on ensuring that access‑control policies are enforced correctly across plug‑ins.
Deployment is envisioned as an open‑source offering distributed via the Eclipse Marketplace, encouraging community contributions. Build automation is supported through Maven/Gradle scripts, allowing developers to package and publish new plug‑ins with minimal friction. The roadmap includes future extensions such as cloud‑based evidence storage, machine‑learning‑driven automated analysis modules, and mobile device forensic support.
In summary, the paper delivers a detailed blueprint for building a robust, flexible, and legally defensible forensic workstation. By combining Eclipse’s modularity with rigorous chain‑of‑custody management, granular access control, automated batch processing, and multi‑format reporting, Ftklipse aims to become a reusable foundation for a wide range of digital forensic investigations. The SRS serves as a precise contract between stakeholders and developers, ensuring that the final product meets both technical and evidentiary standards required in modern cyber‑crime investigations.
Comments & Academic Discussion
Loading comments...
Leave a Comment