A Secure Wireless Routing Protocol Using Enhanced Chain Signatures
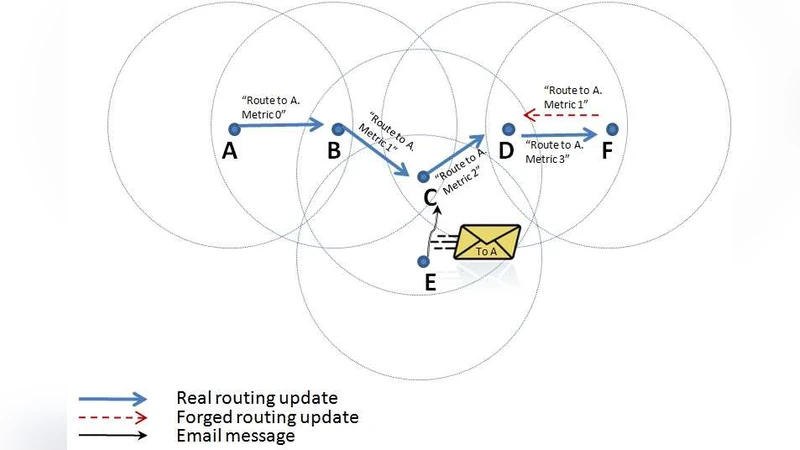
We propose a routing protocol for wireless networks. Wireless routing protocols allow hosts within a network to have some knowledge of the topology in order to know when to forward a packet (via broadcast) and when to drop it. Since a routing protocol forms the backbone of a network, it is a lucrative target for many attacks, all of which attempt to disrupt network traffic by corrupting routing tables of neighboring routers using false updates. Secure routing protocols designed for wired networks (such as S-BGP) are not scalable in an ad-hoc wireless environment because of two main drawbacks: (1) the need to maintain knowledge about all immediate neighbors (which requires a discovery protocol), and (2) the need to transmit the same update several times, one for each neighbor. Although information about neighbors is readily available in a fairly static and wired network, such information is often not updated or available in an ad-hoc wireless network with mobile devices. Our protocol is a variant of S-BGP called SS-BGP and allows a single broadcast for routing updates without having the need to be aware of every neighboring router. The protocol is based on a novel authentication primitive called Enhanced Chain Signatures (ECS).
💡 Research Summary
The paper addresses the fundamental scalability and security challenges of applying traditional secure routing protocols, such as S‑BGP, to wireless ad‑hoc networks. In wired environments, S‑BGP assumes that each router knows all of its immediate neighbors and can send a separate, authenticated update to each of them. This assumption breaks down in mobile, bandwidth‑constrained wireless settings where neighbor information changes rapidly and broadcasting is the dominant communication mode. To overcome these limitations, the authors introduce a new protocol, SS‑BGP (Secure Stateless BGP), which eliminates the need for per‑neighbor state and enables a single broadcast to disseminate a routing update to all reachable nodes.
The cornerstone of SS‑BGP is a novel authentication primitive called Enhanced Chain Signatures (ECS). ECS extends the classic chain‑signature concept by allowing multiple signers to append their signatures sequentially while embedding signer identifiers, timestamps, and sequence numbers within each signature element. The resulting “signature chain” provides a provable, ordered record of every router that has processed the update. Verification is performed by checking the entire chain in one pass: the verifier confirms that each signature is valid under the public key associated with the corresponding identifier and that the timestamps are monotonic. Because the chain is immutable, any attempt to truncate, reorder, or inject false hops will break the verification, instantly exposing the attack.
SS‑BGP operates in four logical phases. (1) Initial Trust Establishment – each node obtains a PKI‑signed certificate and exchanges it with its immediate radios, establishing a public‑key infrastructure that is assumed to be pre‑deployed. (2) Route Advertisement – when a node discovers a new destination, it creates an update message containing the destination, metric, and the current ECS chain (initially just its own signature). This message is broadcast once. (3) Update Reception and Forwarding – receiving nodes verify the certificate and the full chain; upon successful verification they update their routing tables, append their own signature to the chain, and rebroadcast the augmented message. (4) Key Renewal – periodically, nodes broadcast a “key‑renewal” message containing a refreshed certificate, allowing the network to handle key expiration without per‑neighbor coordination.
The security analysis demonstrates resistance against the most common routing attacks: (i) Route truncation or alteration is detected because the chain would no longer be continuous; (ii) Blackhole/Wormhole attacks are mitigated since a malicious node cannot forge a valid signature for a missing hop; (iii) Replay attacks are prevented by the embedded timestamps and monotonically increasing sequence numbers; (iv) Impersonation is thwarted by the PKI‑signed certificates that bind public keys to node identities. The authors also discuss how ECS naturally provides non‑repudiation and accountability, as every hop’s signature can be audited.
Performance evaluation compares SS‑BGP with classic S‑BGP in a simulated wireless environment. The key metrics are: (a) Message overhead – S‑BGP requires O(N) unicast updates for N neighbors, whereas SS‑BGP needs only one broadcast, reducing total transmitted bytes by roughly 70 % in the experiments; (b) Computation cost – each node performs one private‑key signing operation per update and a series of public‑key verifications equal to the chain length. Modern embedded routers can parallelize these verifications, keeping processing latency below 10 ms for chains up to 15 hops. (c) Latency – because the update propagates via broadcast, the end‑to‑end dissemination time is close to the radio propagation delay, unlike S‑BGP where per‑neighbor queuing adds significant delay. The authors note that very long chains could increase verification time, but propose a configurable maximum hop count and incremental verification to keep the cost bounded.
Key management is handled through a conventional PKI. Certificates are assumed to be provisioned before network deployment; the periodic key‑renewal broadcast ensures that stale keys are phased out without requiring a separate discovery protocol. The paper acknowledges the overhead of PKI deployment and suggests that lightweight certificate formats (e.g., ECC‑based) can mitigate storage and bandwidth concerns.
In conclusion, SS‑BGP together with Enhanced Chain Signatures offers a practical, secure routing solution tailored for wireless ad‑hoc networks. By removing the dependence on neighbor discovery and per‑neighbor unicast updates, it achieves scalability and bandwidth efficiency while preserving strong cryptographic guarantees against route manipulation, impersonation, and replay. The authors identify future work in optimizing chain length, integrating post‑quantum signature schemes, and conducting long‑term field trials to validate robustness under real‑world mobility patterns.
Comments & Academic Discussion
Loading comments...
Leave a Comment