We Can Remember It for You Wholesale: Implications of Data Remanence on the Use of RAM for True Random Number Generation on RFID Tags (RFIDSec 2009)
Random number generation is a fundamental security primitive for RFID devices. However, even this relatively simple requirement is beyond the capacity of today’s average RFID tag. A recently proposed solution, Fingerprint Extraction and Random Number Generation in SRAM (FERNS) [14, 15], involves the use of onboard RAM as the source of “true” randomness. Unfortunately, practical considerations prevent this approach from reaching its full potential. First, this method must compete with other system functionalities for use of memory. Thus, the amount of uninitialized RAM available for utilization as a randomness generator may be severely restricted. Second, RAM is subject to data remanence; there is a time period after losing power during which stored data remains intact in memory. This means that after a portion of memory has been used for entropy collection once it will require a relatively extended period of time without power before it can be reused. In a usable RFID based security application, which requires multiple or long random numbers, this may lead to unacceptably high delays. In this paper, we show that data remanence negatively affects RAM based random number generation. We demonstrate the practical considerations that must be taken into account when using RAM as an entropy source. We also discuss the implementation of a true random number generator on Intel’s WISP RFID tag, which is the first such implementation to the authors’ best knowledge. By relating this to the requirements of some popular RFID authentication protocols, we assess the (im)practicality of utilizing memory based randomness techniques on resource constrained devices.
💡 Research Summary
The paper investigates the feasibility of using on‑chip SRAM as a true random number generator (TRNG) for low‑cost RFID tags, focusing on the FERNS (Fingerprint Extraction and Random Number Generation in SRAM) approach. Random numbers are essential for authentication, key exchange, and privacy‑preserving protocols, yet conventional TRNGs are too expensive or power‑hungry for typical passive tags. FERNS promises to extract entropy from the inherent process variations of uninitialized SRAM cells without additional hardware, making it attractive for ultra‑lightweight devices.
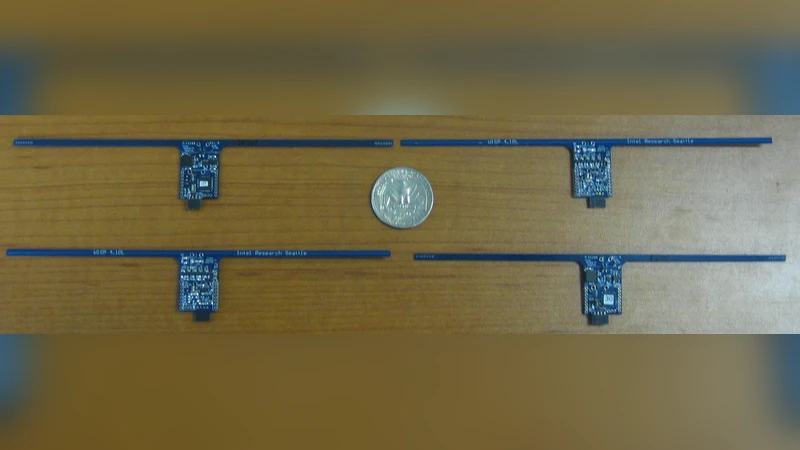
The authors identify two practical obstacles that severely limit FERNS’s effectiveness in real RFID deployments. First, SRAM is a shared resource. An RFID tag must store protocol state, sensor readings, and possibly application data, so only a fraction of the available memory can be dedicated to entropy collection. Reducing the allocated region directly lowers the number of bits that can be harvested per power‑up and may degrade statistical quality. Second, SRAM exhibits data remanence: after power loss, stored charge decays slowly, preserving the previous “fingerprint” for seconds to minutes. Consequently, once a memory block has been used for randomness, it cannot be reused until the residual data has fully dissipated. The authors experimentally quantify this effect on an Intel WISP 3.0 platform, allocating 2 KB of an 8 KB SRAM array to FERNS. They repeatedly cycle power and measure the min‑entropy of the extracted bits. The results show that a minimum of roughly 30 seconds of power‑off is required before the memory can be considered “fresh” again. This latency is orders of magnitude larger than the sub‑millisecond response times expected in typical RFID authentication exchanges.
To assess real‑world impact, the paper maps the entropy requirements of several widely cited RFID authentication schemes (e.g., HB+, LMAP, PUF‑based protocols) onto the observed capabilities of the SRAM‑based TRNG. Lightweight challenge‑response protocols often need only 64 bits of randomness per session, which could be satisfied if the tag can afford the 30‑second reset interval. However, more demanding schemes—especially those involving public‑key operations or multi‑round blind signatures—require 128 bits or more per session, making the SRAM‑only solution impractical for timely operation.
The authors propose mitigation strategies: (1) dynamic memory management that schedules entropy collection only during idle periods; (2) protocol redesign that explicitly incorporates the required power‑off interval, perhaps by batching multiple sessions after a single entropy harvest; and (3) hybrid designs that combine SRAM‑derived bits with other low‑power entropy sources such as on‑chip thermal noise generators, physical unclonable functions (PUFs), or sensor‑derived randomness. They argue that while SRAM‑based randomness can contribute to a cost‑effective security layer, it cannot, by itself, meet the stringent latency and entropy demands of modern RFID security protocols.
In conclusion, the study demonstrates that data remanence and limited memory availability fundamentally constrain the use of RAM as a sole entropy source on passive RFID tags. Future work should explore ultra‑low‑power noise circuits, optimized power‑cycling schedules, and algorithmic techniques for entropy amplification to overcome these barriers and enable robust, real‑time cryptographic operations on highly constrained devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment