Breaking a new substitution-diffusion based image cipher using chaotic standard and logistic maps
Recently, an image encryption scheme based on chaotic standard and logistic maps was proposed. This paper studies the security of the scheme and shows that it can be broken with only one chosen-plaintext. Some other security defects of the scheme are also reported.
💡 Research Summary
The paper conducts a thorough security analysis of the image encryption scheme proposed by Patidar, Pareek and Sud (2009), which combines a chaotic standard map and a logistic map in a substitution‑diffusion framework. The authors first describe the algorithm in detail. A secret key consists of three floating‑point numbers (x₀, y₀, K) and an integer L. From these values four 8‑bit XOR keys Xkey(0)…Xkey(3) are derived. The standard map (x = (x + K·sin y) mod 2π, y = (y + x + K·sin y) mod 2π) is iterated L + MN times to generate MN chaotic states (xᵢ, yᵢ). The logistic map (z = 4z(1−z)) is iterated the same number of times to obtain MN values zᵢ. The three sequences are scaled to 0‑255 and assembled into a chaotic‑key‑stream (CKS) image whose R, G, B components are CKSR(i,j), CKSG(i,j) and CKSB(i,j).
Encryption proceeds through four stages:
- Confusion I – each pixel’s R, G, B channels are XORed with the four Xkey values in a cyclic order.
- Diffusion I – a forward raster scan (row‑wise) XORs each pixel (except the first) with its immediate predecessor in the scan.
- Diffusion II – a backward column‑wise scan XORs each pixel (except the last) with the three channels of its predecessor.
- Confusion II – the result of the two diffusion steps is XORed with the CKS image, producing the final ciphertext.
Decryption simply reverses these operations.
The core of the cryptanalysis is a chosen‑plaintext attack. The authors prove (Lemma 1) that the effect of the two diffusion steps can be separated from the XOR keys, leading to the relation
I′ = Ĩ** ⊕ Ĩ**_Xkey ⊕ I_CKS
where Ĩ** denotes the image after the two diffusion steps, and Ĩ**_Xkey is the same diffusion applied to the XOR‑key image. By choosing a zero image I₀ (all pixel values equal to 0) as the plaintext, the first confusion step yields exactly the XOR‑key image, and after the diffusion steps the ciphertext becomes an “equivalent key” I′₀ = Ĩ**_Xkey ⊕ I_CKS. This I′₀ can be used to decrypt any other ciphertext encrypted with the same secret parameters: compute Ĩ** = I′ ⊕ I′₀ and then run the inverse diffusion to recover the original plaintext. The authors validate the attack experimentally with realistic parameters (x₀≈3.9823, y₀≈1.3453, K≈108.54, L=110) and successfully recover the classic “Lenna” image using only the zero‑image ciphertext.
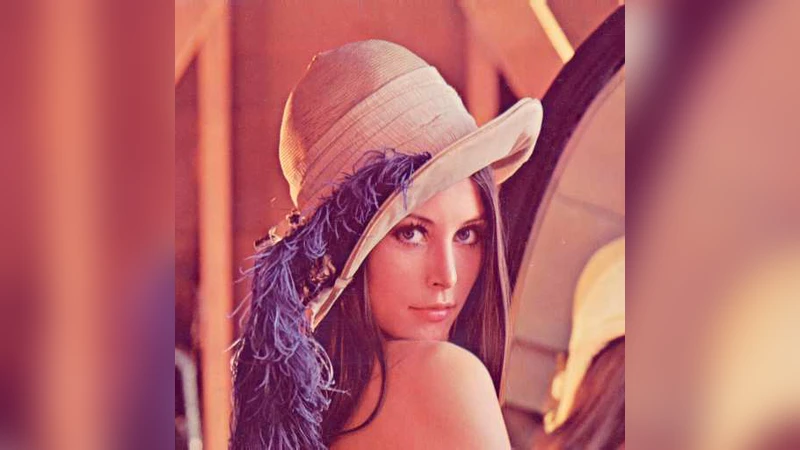
Beyond the chosen‑plaintext weakness, the paper examines two additional security flaws.
-
Insufficient randomness of the logistic‑map PRNS – The authors generate 100 pseudo‑random byte sequences of length 512 × 512 (262 144 bytes) using the logistic map with the fixed control parameter 4, each under a randomly chosen secret key. They subject these sequences to the NIST SP 800‑22 statistical test suite. The results show catastrophic failure: the Frequency, Block‑Frequency, Runs, Rank, Serial, Approximate Entropy and FFT tests all have pass rates far below the 99 % confidence level (often 0 %). This confirms that the logistic map, when used with a static parameter, produces highly correlated, non‑uniform outputs unsuitable for cryptographic purposes.
-
Lack of avalanche (plaintext sensitivity) – A fundamental requirement for a secure cipher is that flipping a single bit of the plaintext should, with probability ½, flip each bit of the ciphertext (the avalanche effect). The authors demonstrate that the scheme fails this test dramatically. Changing only the 6‑th bit of the red channel of a single pixel in the plaintext results in changes confined to the same bit position of the corresponding color channels in the ciphertext; only a few bits are altered, and the effect does not propagate to other pixels or other bit positions. This is a direct consequence of the scheme’s exclusive reliance on linear XOR operations and the absence of any nonlinear, key‑dependent mixing.
In conclusion, the paper identifies three decisive vulnerabilities: (1) a trivial chosen‑plaintext attack that yields an equivalent decryption key, (2) a pseudo‑random number generator derived from the logistic map that fails standard randomness tests, and (3) a design that lacks non‑linearity and avalanche, making it highly susceptible to differential attacks. The authors therefore advise against using this image cipher in any security‑critical application and suggest that future designs must incorporate robust key‑dependent diffusion, non‑linear transformations, and cryptographically sound PRNGs.
Comments & Academic Discussion
Loading comments...
Leave a Comment