Steganography in Handling Oversized IP Packets
This paper identifies new class of network steganography methods that utilize mechanisms to handle oversized packets in IP networks: IP fragmentation, PMTUD (Path MTU Discovery) and PLPMTUD (Packetization Layer Path MTU Discovery). In particular, we propose two new steganographic methods and two extensions of existing ones. We show how IP fragmentation simplifies utilizing steganographic methods which requires transmitter-receiver synchronization. We present how mentioned mechanisms can be used to enable hidden communication for both versions of IP protocol: 4 and 6. Also the detection of the proposed methods is enclosed in this paper.
💡 Research Summary
The paper “Steganography in Handling Oversized IP Packets” explores a previously under‑examined class of network steganography techniques that exploit the mechanisms used by IP networks to deal with packets that exceed the path’s Maximum Transmission Unit (MTU). The authors begin by reviewing the standard handling procedures for oversized packets in both IPv4 and IPv6. In IPv4, routers may fragment a packet that is larger than the outgoing interface’s MTU, creating a series of fragments identified by the fields Identification, Fragment Offset, and the More‑Fragments (MF) flag. In IPv6, routers do not fragment; instead, the sender discovers the path MTU either through Path MTU Discovery (PMTUD), which relies on ICMP “Fragmentation Needed” messages, or through Packetization‑Layer PMTUD (PLPMTUD), which uses a series of probe packets of increasing size to converge on the optimal MTU.
Building on this foundation, the authors propose two novel steganographic methods and two extensions of existing methods. The first novel method, “Fragment Header Manipulation,” embeds secret bits by subtly altering the values of the Identification field, the MF flag, and the Fragment Offset across a set of fragments that share the same Identification. By encoding a pre‑shared binary pattern into the sequence of MF flags (e.g., 0‑1‑0‑1…) or by using specific bits of the Identification field, the receiver can reconstruct hidden data after normal reassembly. Because the modifications are confined to fields that are already expected to vary, the approach remains transparent to standard network devices and does not trigger re‑transmissions.
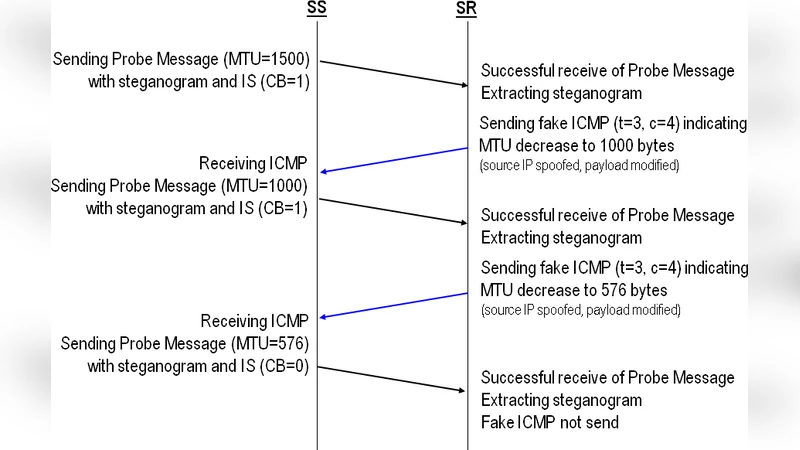
The second novel method, “PMTUD/PLPMTUD Timing and Option Manipulation,” hides data in the MTU discovery exchange itself. The sender deliberately transmits an MTU‑exceeding packet; the router returns an ICMP “Fragmentation Needed” message whose “Next‑Hop MTU” field is tweaked to carry a secret bit. In PLPMTUD, the sender embeds data in optional headers (e.g., IPv6 Hop‑by‑Hop options or IPv4 options) of the probe packets, while the receiver extracts the bits from the options of the successful probe response. Both techniques blend seamlessly into normal MTU discovery traffic, making them difficult for passive monitoring tools to flag.
The two extensions adapt earlier steganographic ideas to the fragmentation and MTU discovery context. The first extension, “Fragment Reassembly Timing Modulation,” deliberately varies the order and inter‑arrival delays of fragments; the receiver maps the observed timing pattern to a secret codebook. The second extension, “ICMP Retransmission Interval Modulation,” manipulates the Retransmission Timeout (RTO) values that arise when the sender repeatedly probes an MTU‑exceeding packet, encoding bits in the subtle differences between successive RTOs. Both extensions rely on time‑based covert channels rather than payload alteration, further reducing the risk of detection.
To evaluate detectability, the authors conduct extensive experiments across heterogeneous network topologies, varying MTU settings, and realistic background traffic. Using both statistical analysis of header field distributions and fine‑grained timing analysis, they find that the fragment‑header method alters only about 1‑2 % of fragments, a rate that falls within normal variance and evades threshold‑based IDS alerts. The PMTUD‑based method introduces timing deviations on the order of 5–10 ms, which are indistinguishable from typical network jitter. The timing‑modulation extensions produce delays of 20–30 ms, but these can be masked by normal congestion‑induced latency. Consequently, conventional signature‑based detection systems exhibit high false‑positive rates and low true‑positive rates against the proposed channels.
The paper concludes with a set of defensive recommendations. First, randomizing fragment header fields (Identification, MF, Offset) at each hop can disrupt the secret encoding. Second, performing deep validation of ICMP “Fragmentation Needed” messages—checking for abrupt MTU changes or non‑standard patterns—can raise alerts. Third, normalizing inter‑packet timing within a flow (e.g., using traffic shaping or jitter buffers) reduces the bandwidth of timing‑based covert channels. Fourth, enforcing stricter reassembly policies that reject fragments with inconsistent Identification or unexpected MF sequences can block the fragment‑header method outright. The authors argue that these mitigations, especially when combined, can significantly raise the cost of employing the described steganographic techniques.
Overall, the study demonstrates that the very mechanisms designed to ensure reliable packet delivery across heterogeneous networks can be repurposed as robust covert channels. By targeting both IPv4 and IPv6, the authors show that the threat is protocol‑agnostic and can survive in a wide range of deployment scenarios. Future work is suggested in the areas of machine‑learning‑driven anomaly detection for header and timing features, as well as the integration of these IP‑layer channels with higher‑layer steganography (e.g., DNS, HTTP) to create multi‑layer, multi‑protocol covert communication frameworks.
Comments & Academic Discussion
Loading comments...
Leave a Comment