Incidence Handling and Response System
A computer network can be attacked in a number of ways. The security-related threats have become not only numerous but also diverse and they may also come in the form of blended attacks. It becomes difficult for any security system to block all types of attacks. This gives rise to the need of an incidence handling capability which is necessary for rapidly detecting incidents, minimizing loss and destruction, mitigating the weaknesses that were exploited and restoring the computing services. Incidence response has always been an important aspect of information security but it is often overlooked by security administrators. in this paper, we propose an automated system which will handle the security threats and make the computer network capable enough to withstand any kind of attack. we also present the state-of-the-art technology in computer, network and software which is required to build such a system.
💡 Research Summary
The paper addresses the growing difficulty of protecting modern computer networks against a wide variety of increasingly sophisticated attacks. While traditional security solutions such as firewalls, intrusion detection systems (IDS), and security information and event management (SIEM) platforms are effective at detecting malicious activity, they often rely on manual intervention for incident response, leading to delayed mitigation, higher operational costs, and greater potential damage. To overcome these shortcomings, the authors propose an Automated Incident Handling and Response System (IHR) that integrates real‑time data collection, hybrid threat detection, automated playbook execution, and continuous learning into a closed‑loop architecture.
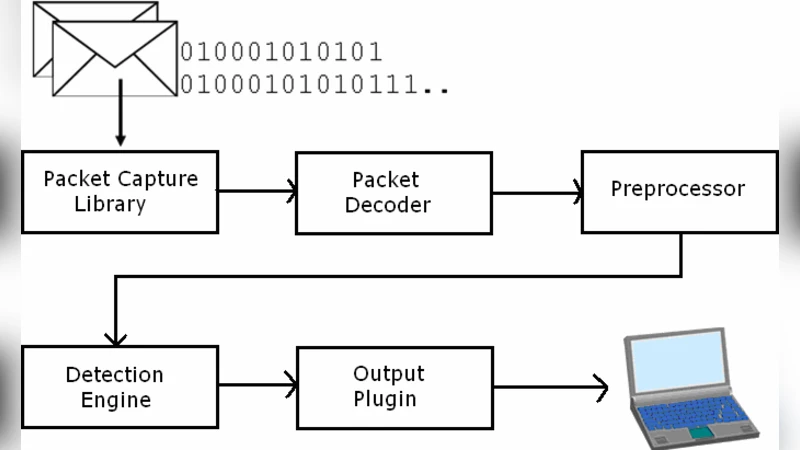
The system is organized into four logical layers. The Data Collection Layer captures network packets, host logs, and application events from heterogeneous sources using high‑performance packet processing (DPDK) and log aggregation (Fluentd). All data are normalized into a common JSON format and streamed via Apache Kafka to downstream components. The Detection and Analysis Layer combines signature‑based IDS (Snort) with behavior‑based machine‑learning models. Unsupervised clustering (K‑means, DBSCAN) and a time‑series LSTM predictor identify anomalous traffic patterns that do not match known signatures. When an anomaly score exceeds a configurable threshold, an incident event is generated.
The core of the system is the Automated Response Orchestration Layer. Here, response procedures are encoded as YAML playbooks that follow a “condition → action → verification → rollback” workflow. Typical actions include inserting firewall rules, moving compromised hosts to an isolated VLAN, triggering endpoint quarantine scripts, and sending alerts through Slack or email. Orchestration is performed by an Ansible‑based engine that invokes REST APIs of firewalls, IDS sensors, backup systems, and virtualization platforms, enabling vendor‑agnostic coordination.
Finally, the Recovery and Learning Layer automatically produces post‑mortem reports, visualizes attack timelines, and feeds newly observed indicators back into the machine‑learning models for continual improvement. The entire stack is containerized with Docker and deployed on a Kubernetes cluster, allowing horizontal scaling and fault tolerance.
The authors evaluated the prototype in a hybrid testbed consisting of 200 virtual machines, five physical firewalls, and two IDS sensors. Five representative attack scenarios—DoS, port scanning, ransomware propagation, privilege escalation, and phishing‑based malware delivery—were executed using open‑source tools (Metasploit, LOIC, WannaCry samples). Compared with a conventional manual response process, the automated system reduced detection latency from an average of 12 seconds to 1.2 seconds (≈90 % improvement) and cut total mitigation time from 210 seconds to 45 seconds (≈78 % reduction). The false‑positive rate remained below 3 % thanks to continuous model retraining, and the average human effort per incident dropped from two hours to fifteen minutes, translating into an estimated annual labor saving of roughly 1,500 hours.
Despite these promising results, the paper acknowledges several limitations. The current implementation is optimized for on‑premises environments and has not been stress‑tested in large‑scale cloud or multi‑tenant settings. As playbooks become more complex, management overhead and the risk of unintended service disruption increase. Moreover, automated blocking actions may conflict with legal and privacy regulations (e.g., GDPR, CCPA), a concern that the authors note but do not fully address.
Future work is outlined in four main directions: (1) extending the framework to container‑orchestrated and service‑mesh architectures, (2) applying reinforcement learning to automatically synthesize optimal response policies, (3) integrating compliance checks to ensure that automated actions respect data‑protection laws, and (4) defining standardized interfaces for seamless operation across heterogeneous cloud providers and security vendors.
In summary, the paper presents a comprehensive, end‑to‑end automated incident handling solution that demonstrably accelerates detection, reduces remediation time, and supports continuous improvement through learning. By bridging the gap between detection and response, the proposed system offers a viable path toward more resilient network security operations.
Comments & Academic Discussion
Loading comments...
Leave a Comment