Understanding the spreading patterns of mobile phone viruses
We model the mobility of mobile phone users to study the fundamental spreading patterns characterizing a mobile virus outbreak. We find that while Bluetooth viruses can reach all susceptible handsets with time, they spread slowly due to human mobility, offering ample opportunities to deploy antiviral software. In contrast, viruses utilizing multimedia messaging services could infect all users in hours, but currently a phase transition on the underlying call graph limits them to only a small fraction of the susceptible users. These results explain the lack of a major mobile virus breakout so far and predict that once a mobile operating system’s market share reaches the phase transition point, viruses will pose a serious threat to mobile communications.
💡 Research Summary
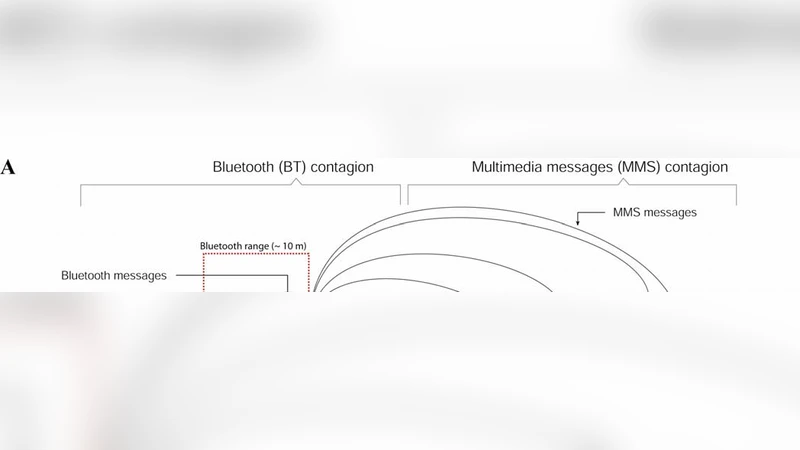
The paper presents a quantitative investigation of mobile phone virus propagation by explicitly modeling user mobility and communication patterns. Two dominant infection pathways are examined: short‑range Bluetooth spread, which requires physical proximity, and long‑range multimedia messaging service (MMS) spread, which exploits the underlying call‑graph of phone numbers and message exchanges. Using large‑scale mobility traces and call‑detail records, the authors construct two distinct networks. In the Bluetooth scenario, contacts are generated whenever two users are co‑located within a short distance. Simulations reveal that, given enough time, a small seed of infected handsets can eventually reach every susceptible device, but the average time to full infection spans days to weeks. This sluggish pace is a direct consequence of human movement being spatially constrained and the limited opportunities for a handset to encounter new devices. Consequently, there is ample window for deploying countermeasures such as antivirus updates, forced OS patches, or user education before the virus can cause widespread damage.
In contrast, the MMS pathway bypasses physical proximity entirely. The call‑graph exhibits a scale‑free topology with a few highly connected hubs that link large portions of the user base. By coupling a classic susceptible‑infected‑recovered (SIR) epidemic model with percolation theory, the authors demonstrate that the spread of an MMS‑based worm undergoes a phase transition when the market share of a particular mobile operating system (OS) exceeds a critical threshold. Below this threshold, the graph remains fragmented; the worm can only infect a small isolated component, explaining why real‑world MMS worms have historically infected only a tiny fraction of devices. Once the OS’s market share surpasses roughly 30–40 % (the exact value depends on the degree distribution), a giant connected component emerges, and the worm can percolate through the entire network in a matter of hours. This rapid, distance‑independent diffusion poses a far greater threat than Bluetooth worms.
The authors synthesize these findings to explain the conspicuous absence of a major mobile virus outbreak to date: Bluetooth viruses are throttled by human mobility, while MMS viruses are currently constrained by the fragmented structure of the call‑graph. However, the situation is precarious. As the market consolidates around a single OS, the system approaches the percolation threshold, at which point MMS‑based malware could achieve epidemic scale almost instantaneously.
Policy implications are drawn from the analysis. Diversifying the OS ecosystem can keep any single platform’s market share below the critical point, thereby preserving the fragmented nature of the call‑graph and limiting MMS worm reach. For Bluetooth threats, timely distribution of security patches and user‑level antivirus tools remains an effective mitigation strategy because of the long infection timelines. Moreover, telecom operators are encouraged to monitor the evolving topology of the call‑graph and to issue early warnings when a platform’s market share nears the percolation point.
In summary, the study provides a dual‑lens framework—mobility‑driven proximity networks and topology‑driven communication networks—to elucidate why mobile viruses have not yet caused a large‑scale crisis, while also forecasting a looming vulnerability tied to OS market concentration. These insights furnish concrete guidance for security practitioners, OS vendors, and policymakers aiming to preempt the next generation of mobile malware epidemics.
Comments & Academic Discussion
Loading comments...
Leave a Comment