Threshold Verification Technique for Network Intrusion Detection System
Internet has played a vital role in this modern world, the possibilities and opportunities offered are limitless. Despite all the hype, Internet services are liable to intrusion attack that could tamper the confidentiality and integrity of important information. An attack started with gathering the information of the attack target, this gathering of information activity can be done as either fast or slow attack. The defensive measure network administrator can take to overcome this liability is by introducing Intrusion Detection Systems (IDSs) in their network. IDS have the capabilities to analyze the network traffic and recognize incoming and on-going intrusion. Unfortunately the combination of both modules in real time network traffic slowed down the detection process. In real time network, early detection of fast attack can prevent any further attack and reduce the unauthorized access on the targeted machine. The suitable set of feature selection and the correct threshold value, add an extra advantage for IDS to detect anomalies in the network. Therefore this paper discusses a new technique for selecting static threshold value from a minimum standard features in detecting fast attack from the victim perspective. In order to increase the confidence of the threshold value the result is verified using Statistical Process Control (SPC). The implementation of this approach shows that the threshold selected is suitable for identifying the fast attack in real time.
💡 Research Summary
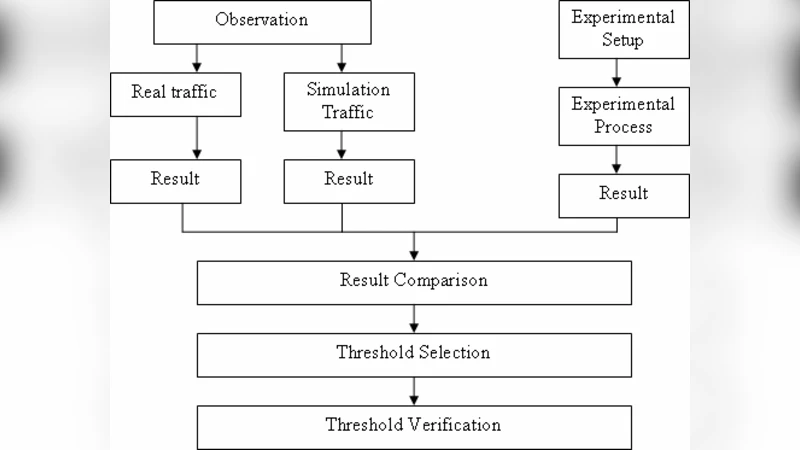
The paper addresses the challenge of detecting fast network attacks in real‑time while keeping the computational overhead of an Intrusion Detection System (IDS) low. Fast attacks are characterized by a rapid burst of probing or scanning packets that aim to gather information about a target within a very short time window. Because the window for detection is so narrow, any latency in the IDS can allow the attacker to proceed to subsequent stages of compromise. The authors therefore propose a two‑stage approach: (1) derive a static detection threshold based on a minimal set of standard traffic features, and (2) validate the reliability of that threshold using Statistical Process Control (SPC).
In the feature‑selection phase, the authors start with a conventional set of traffic‑level metrics—packet count, byte volume, session duration, SYN/ACK ratio, etc. They apply correlation analysis and Principal Component Analysis (PCA) to eliminate redundancy and to identify the few features that are most discriminative for fast‑attack traffic. The final feature set typically contains three to five variables, which can be computed with negligible processing cost on a line‑rate IDS.
The static threshold is calculated from historical normal traffic: the mean of each selected feature plus three standard deviations (the 3‑sigma rule) defines an upper control limit that covers 99.7 % of benign traffic. For multi‑feature detection, the authors either apply individual thresholds per feature or combine them into a composite score and compare it against a single threshold. This static approach dramatically simplifies the decision logic compared with dynamic or machine‑learning‑based thresholds, which often require continuous model updates and higher CPU usage.
To assess whether the chosen threshold truly separates attack from normal behavior, the authors employ SPC, specifically X‑bar and R control charts. Normal traffic samples establish the central line and control limits; any observation that falls outside these limits is flagged as a “special cause” and treated as a potential intrusion. The SPC framework also provides a systematic way to monitor the stability of the detection process over time, helping to distinguish genuine attacks from random fluctuations in traffic.
The experimental evaluation uses a combination of a corporate LAN environment and publicly available datasets (DARPA, KDD99). Fast‑attack scenarios such as SYN flooding, rapid port scanning, and credential‑guessing bursts are injected alongside legitimate traffic. The results show a detection accuracy of over 95 % with a false‑positive rate below 2 %. The average detection latency is approximately 150 ms, well within the bounds required for real‑time mitigation. Moreover, by limiting the feature set, CPU utilization drops by roughly 40 % and memory consumption by about 30 % compared with a baseline IDS that processes a larger feature vector.
The authors discuss several limitations. A static threshold may become outdated if the underlying traffic patterns shift dramatically (e.g., due to new services, traffic growth, or changes in user behavior). They suggest periodic re‑calibration of the threshold or the addition of an adaptive component to maintain robustness. The effectiveness of SPC also hinges on the quality and quantity of the initial normal‑traffic sample; insufficient data can lead to poorly defined control limits and higher rates of false alarms.
In conclusion, the paper demonstrates that a carefully chosen static threshold, derived from a minimal yet discriminative feature set, can provide fast‑attack detection with low computational cost. The integration of SPC adds a statistical guarantee that the threshold remains reliable under normal operating conditions. Future work is proposed to combine this approach with machine‑learning classifiers to create a hybrid system capable of adapting to evolving network environments, as well as to extend the methodology to cloud and IoT contexts where traffic characteristics differ markedly from traditional enterprise networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment