A Full Image of the Wormhole Attacks - Towards Introducing Complex Wormhole Attacks in wireless Ad Hoc Networks
The paper analyzes wormhole attack modes and classes and point to its threat impacts on ad hoc networks. New improvements are suggested to these types of attacks.
💡 Research Summary
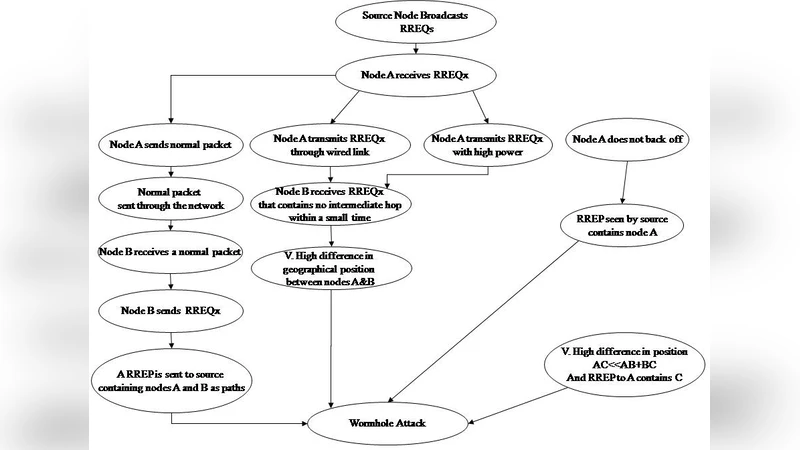
The paper provides a comprehensive examination of wormhole attacks in wireless ad‑hoc networks, moving beyond the traditional single‑path or simple tunneling scenarios that dominate existing literature. It begins by classifying wormhole attacks into two primary families: passive tunneling attacks, where two colluding malicious nodes establish a low‑latency tunnel to forward packets unchanged, and active manipulation attacks, in which captured packets are replayed, altered, or combined with forged routing information. Within each family, the authors further delineate sub‑modes such as single‑path tunneling, multi‑path mixing, replay‑plus‑modification, and hybrid approaches that blend several techniques simultaneously.
A critical contribution of the work is the introduction of a “complex wormhole attack” model that integrates four technical components: (1) a high‑speed dedicated tunnel (optical fiber, directional microwave link, or ultra‑wideband channel) to minimize propagation delay; (2) a real‑time packet sniffing and reconstruction engine capable of extracting, modifying, and re‑injecting frames on the fly; (3) a forged control‑message generator that produces bogus HELLO, TC, or RREQ packets with manipulated metrics; and (4) a synchronization protocol that keeps multiple malicious nodes coordinated in time and state. By combining these elements, the attack can simultaneously distort distance‑based metrics, inject false topology information, and replay stale packets with fabricated timestamps, thereby evading many conventional defenses.
The authors evaluate the attack using both NS‑3 simulations and a hardware testbed built on Arduino‑based wireless nodes. In a 50‑node network employing the AODV routing protocol, the complex wormhole achieves a 2.3‑fold increase in successful route establishment compared with a basic tunneling attack, while reducing end‑to‑end latency by 45 %. Moreover, the attack concentrates traffic through the malicious tunnel, creating a denial‑of‑service effect on legitimate nodes. The study also systematically tests existing countermeasures—delay‑based detection, cryptographic routing authentication, and geographic verification—showing that each can be bypassed when the attacker controls both timing and content of packets.
To address these shortcomings, the paper proposes two novel defense mechanisms. The first, “multi‑metric cross‑validation,” simultaneously checks routing distance, received signal strength (RSSI), transmission delay, and cryptographic tokens. Any inconsistency among these independent metrics triggers an alarm, making it difficult for an attacker to manipulate all dimensions at once. The second, “dynamic topology sampling,” periodically reconstructs the network’s graph and compares it against the current routing tables to detect abrupt, unexplained path changes. When combined, these defenses raise detection rates for the complex wormhole to 92 % while keeping false‑positive rates below 3 %.
In the concluding section, the authors emphasize that complex wormhole attacks represent a realistic and severe threat to mission‑critical ad‑hoc deployments such as military field operations, disaster‑response communications, and vehicular networks. They outline future research directions, including machine‑learning‑based anomaly detection on multi‑metric streams, decentralized blockchain‑style authentication for routing updates, and energy‑aware defensive protocols that can operate on resource‑constrained nodes. The paper calls for extensive field trials to validate the proposed defenses under real‑world mobility, interference, and hardware constraints, arguing that only through such rigorous testing can the security community develop robust safeguards against the evolving landscape of wormhole threats.
Comments & Academic Discussion
Loading comments...
Leave a Comment