Secrecy capacity of a class of orthogonal relay eavesdropper channels
The secrecy capacity of relay channels with orthogonal components is studied in the presence of an additional passive eavesdropper node. The relay and destination receive signals from the source on two orthogonal channels such that the destination al…
Authors: Vaneet Aggarwal, Lalitha Sankar, A. Robert Calderbank
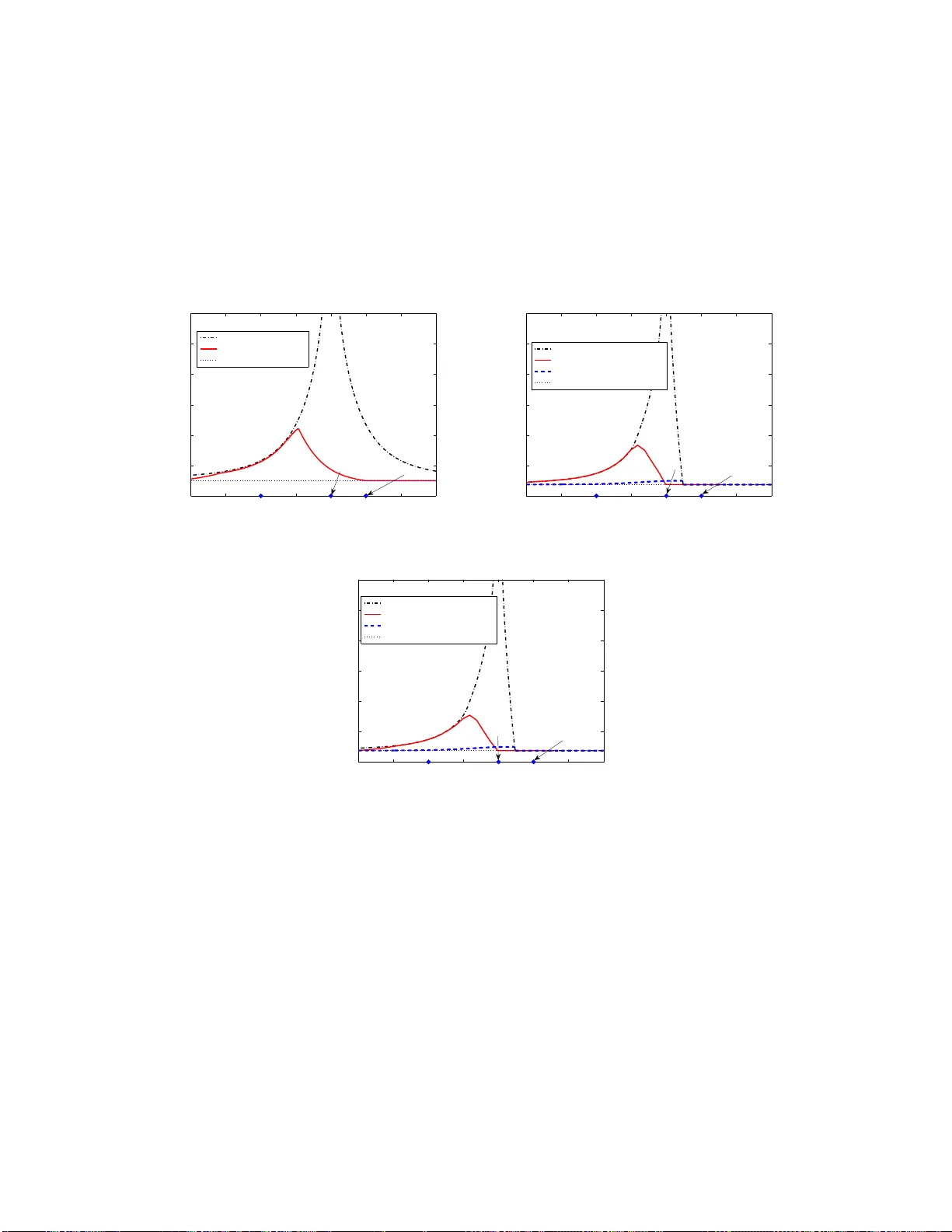
1 Secrec y capacit y of a class of orthogonal rela y ea v esdropper channels V aneet Aggarwal, Lalitha S ankar , A. Rober t Calder bank, and H. V incent Poor Abstract The secrecy capacity of relay chann els w ith orthog onal com ponents is studied in the pr esence of an additional passive eaves dropp er node. The relay and destinatio n rec ei ve signals f rom th e source on two orthog onal chan nels su ch that the destinatio n also receives transm issions from the relay on its ch annel. The eav esdropp er can overhear either on e or bo th of the orthog onal channels. Inner a nd outer bounds o n the secrecy c apacity are d ev eloped fo r both the discrete memor yless an d the Gaussian channe l m odels. For th e discrete mem oryless case, the secrecy capacity is shown to be achieved by a partial d ecode-a nd- forwar d (PDF) sch eme when the eavesdropper c an overhear o nly on e of th e two orthogo nal chan nels. T w o ne w ou ter boun ds are presented for the Gaussian model using recent capacity results for a Gaussian multi-anten na p oint-to-p oint c hannel with a multi-antenna eavesdropper . The outer bo unds are sho wn to be tight fo r two sub-classes of chann els. The first sub-class is one in which the sou rce and relay are clustered and the and the eaves dropp er r eceiv es signals only on the chan nel fr om the source and the relay to the destination, for which the PDF stra tegy is op timal. The second is a sub-c lass in which the source does not tran smit to the relay , for which a noise-for warding strategy is op timal. The authors are w ith the Department of Electrical Engineering, Princeton Uni versity , Princeton, NJ, US A. The work of V . Aggarwal and A. R. Calderbank was supported in part by NSF under grant 0701226, by ONR under grant N00173-06 -1-G006, and by AFOSR under grant F A9550-05-1-04 43. The work of L. Sankar and H. V . Poor was supported i n part by t he National Science Foundation under grant CNS-06-25637. The material in this paper was presented in part at the Information T heory and Applications W orkshop, San Di ego , CA, Feb 2009 and at the IEE E International Symposium on Information Theory , Seoul, K orea, Jun 2009. 2 I . I N T R O D U C T I O N In wireless networks for which nodes can benefit from cooperation and packet-forw arding, there is also a need to preserve the confidentiality of transmitted i nformation from untrusted nodes. Informati on priv acy i n wireless networks has traditionally been t he domain of the higher layers of the protocol st ack vi a the u se o f cryptog raphically secure schemes. In h is semi nal p aper on the three-node wi retap channel, W yner showed t hat p erfect secrec y of transm itted data from the source node can be achieved when the physical channel to the eav esdropper is noisier than the channel to the intended destinat ion, i.e., when the channel i s a degraded broadcast channel [ 1]. This work w as l ater extended by Csisz ´ ar and K ¨ orner to all broadcast channels wi th confidential messages, in which the source node sends common information to both the destination and the wiretapper and confidential inform ation only to the destination [2]. Recently , t he problem of secure communications has also b een studied for a v ariety of mul ti- terminal n etworks; see, for example, [3–10], and the references therein. In [11], the authors show that a relay node can facilitate the transmissio n of confident ial m essages from the source t o the destination in the presence of a wiretapper , often referred to as an ea vesdropper in the wireless setting. T he a uthors de velop the rate-equi vocation region for this f our node relay-ea vesdropper channel and introduce a noise forwarding scheme in which the relay , even if it is unable to aid th e source in its t ransmissions, transm its codewords independent of the s ource to confuse the ea vesdropper . A sp ecial case where the eavesdropper receiv es a degraded version of the destination’ s signal is s tudied in [12]. In contrast, the relay channel wit h confidential messages in whi ch the relay node acts as both a helper and eavesdropper i s stu died in [13]. Note that in all th e three papers, the relay is assumed to be ful l-duplex, i.e., i t can transm it and receiv e simultaneous ly over the entire bandwidth. In this paper , we stu dy th e s ecrec y capacity of a relay chann el with ortho gonal com ponents in the presence of a p assiv e eavesdropper node. The orthogonalit y comes from t he fact that the relay and desti nation recei ve signals from the sou rce on orthogonal channels; furthermore, the destination also receives t ransmissions from the relay on its (the desti nation’ s) channel. T he orthogonal model i mplicitly i mposes a half-duplex t ransmission and reception constraint on the relay . For this channel, in the absence of an eave sdropper , El Gamal and Zahedi showed that a partial decode-and-for war d (PDF) strategy in whi ch the source transmits two messages on t he 3 two orthogonal channels and the relay d ecodes its recei ved si gnal, achie ves the capacity . W e study t he secrecy capacity of this channel for both the discrete memoryless and Gaussian channel mo dels. A s a first step towards this , we develop a PDF strategy for the ful l-duplex relay ea vesdropper channel and extend it to t he orthogo nal m odel. Further , since t he ea vesdropper can recei ve signals from either ortho gonal channel or both, three cases arise in the development of the secrecy capacity . W e specialize the outer b ounds dev eloped in [11] for the orthogonal case and show t hat for the dis crete memoryless channel, PDF achiev es th e secrecy capacity for th e two cases where the eav esdropper recei ves signals in only one of the two orthog onal channels. For th e Gaussian model, we deve lop two new outer bounds usin g recent result s on the secrec y capacity of the Gaussian multipl e-input m ultiple-output channels i n t he presence of a mul ti- antenna eav esdropper (MIMOME) in [4–6]. The first outer bound is a genie-aided b ound that allows the source and relay to cooperate perfectly resulting in a Gaussian MIMOME channel for which join tly Gaussian inputs maxim ize the capacity . W e s how that these bou nds are tight for a sub-class of chann els in which the mult iaccess channel from the s ource and relay t o the destination i s the bottleneck l ink, and the eav esdropper is limit ed t o recei ving signals on the channel from the so urce and the relay to the destinat ion. For a com plementary su b-class of channels i n which the s ource-relay li nk is unus able due to noise resulting in a deaf relay , we dev elop a genie-aided b ound where t he relay and desti nation act like a two-antenna receiv er . W e also show th at noise forwarding achie ves t his bound for this sub -class of channels. In [14], the aut hors st udy t he secrecy rate of the channel studi ed here under t he assum ption that the relay is co-located with the eavesdropper and the eavesdropper is completely cogni zant of the transmit and receive signals at the relay . The authors found that us ing the relay does not increase the secrecy capacity and hence t here i s no security advantage to using the relay . In this paper , we consi der t he ea vesdropper as a separate enti ty and show that usin g the relay increases the secrecy capacity in s ome cases. In the model of [14], the ea vesdropper can overhear on ly on the channel to the relay , while we consider three cases in which t he ea vesdropper can overhea r on either or both th e channels. The paper is organized as follows. In Section II, we present th e chann el models. In Section III, we dev elop the in ner and outer boun ds on the secrecy capacity of the discrete m emoryless model. W e illus trate these results with examples in Section IV. In Section V, we present inner and out er bounds for the Gaussian channel model and il lustrate our resul ts with examples. W e 4 conclude in Section VI. I I . C H A N N E L M O D E L S A N D P R E L I M I N A R I E S A. Discr ete Memoryless Model A discrete-memoryless relay e a vesdropper channel is denoted by ( X 1 ×X 2 , p ( y , y 1 , y 2 | x 1 , x 2 ) , Y × Y 1 × Y 2 ) such that t he input s to the channel in a given channel use are X 1 ∈ X 1 and X 2 ∈ X 2 at the source and relay , respectively , the outpu ts of the chann el are Y 1 ∈ Y 1 , Y ∈ Y , and Y 2 ∈ Y 2 , at the relay , destin ation, and ea vesdropper , respective ly , and th e channel transition p robability is given by p Y Y 1 Y 2 | X X 2 ( y , y 1 , y 2 | x, x 2 ) [11]. The channel is assum ed to be mem oryless, i.e. t he channel outputs at tim e i depend o nly on channel inputs at time i . The source t ransmits a message W 1 ∈ W 1 = { 1 , 2 , · · · , M } to the destinati on using the ( M , n ) code consisti ng o f 1) a s tochastic encoder f at t he source such that f : W 1 → X n 1 ∈ X n 1 , 2) a set of relay encoding functi ons f r,i : ( Y 1 , 1 , Y 1 , 2 , · · · , Y 1 ,i − 1 ) → x 2 ,i at every tim e instant i , and 3) a decodi ng function at the dest ination Φ : Y n → W 1 . The a verage error probability of the code i s defined as P n e = X w 1 ∈W 1 1 M Pr { Φ( Y n ) 6 = w 1 | w 1 was sent } . (1) The equ iv ocation rate at the eav esdropper is defined as R e = 1 n H ( W 1 | Y n 2 ) . A perfect secrecy rate of R 1 is achieve d if for any ǫ > 0 , there exists a sequence of codes ( M , n ) and an int eger N s uch that for all n ≥ N , we hav e R 1 = 1 n log 2 M , (2) P n e ≤ ǫ and (3) 1 n H ( W 1 | Y 2 ) ≥ R 1 − ǫ. (4) The secr ecy capacity is the maximu m rate satisfying (2) -(4). The model described abo ve consi ders a relay that trans mits and receiv es si multaneously in t he same orthogonal channel . Inner and outer bounds for this m odel are dev eloped in [11, Theorem 1]. In this paper , we consider a relay ea vesdropper channel with orthogonal component s in which the relay receiv es and transmits on two orthogo nal channels . The source transmits on both 5 encoder decoder eavesdropper relay Y 1 X 2 Y W 1 W 1 ∧ Y 2,2 Y 2,1 p(y,y 1 ,y 2 |x R ,x D ,x 2 ) X R X D Fig. 1. The relay-eavesdrop per channel wit h orthogonal components. channels, one of which is re cei ved at the r elay and the other at the destination. The relay transmit s along wi th the s ource on the channel received at the destinatio n. Thus, the source si gnal X 1 consists of two parts X R ∈ X R and X D ∈ X D , transmitted to the relay and the destination , respectiv ely , such that X 1 = X D × X R . The eav esdropper can recei ve transmissi ons in one o r both orthogonal chann els such that Y 2 ,i ∈ Y 2 ,i denotes the receiv ed signal at th e eav esdropper in o rthogonal channel i , i = 1 , 2 , and Y 2 = Y 2 , 1 × Y 2 , 2 . M ore form ally , the relay eave sdropper channel with orthogo nal com ponents is defined as foll ows. Definition 1: A discrete-memo ryless relay eavesdropper channel is said to have orthog onal components if the sender alphabet X 1 = X D × X R and the channel can be expressed as p ( y , y 1 , y 2 | x 1 , x 2 ) = p ( y 1 , y 2 , 1 | x R , x 2 ) · p ( y , y 2 , 2 | x D , x 2 ) . (5) Definition 1 assumes t hat the eavesdropper can receiv e signals in bot h channels. In general, the secrecy capacity bounds for t his channel depend on t he recei ver capabilit ies of the eavesdropper . T o this end, we explicitly include the following two definitions for th e cases in which the ea vesdropper can recei ve si gnals in only one of t he channels. Definition 2: The ea vesdropper is lim ited to receiving s ignals o n the channel from the source to the relay , if p ( y , y 1 , y 2 , 1 , y 2 , 2 | x R , x D , x 2 ) = p ( y 1 , y 2 , 1 | x R , x 2 ) · p ( y | x D , x 2 ) · p ( y 2 , 2 ) . (6) 6 Definition 3: The ea vesdropper is lim ited to receiving s ignals o n the channel from the source and the relay to t he destination, if p ( y , y 1 , y 2 , 1 , y 2 , 2 | x R , x D , x 2 ) = p ( y 1 | x R , x 2 ) · p ( y , y 2 , 2 | x D , x 2 ) · p ( y 2 , 1 ) . (7) Remark 1: In the absence of an ea vesdropper , i.e., for y 2 , 1 = y 2 , 2 = 0 , the channels in (5)-(7) simplify to that of a relay channel with orthogon al components. Thus, depending on th e receiv er capabilities at the eavesdropper , there are three cases that arise in deve loping the secrecy capacity bounds. For b re vity , we henceforth ident ify the t hree cases as cases 1 , 2 , and 3 , where cases 1 and 2 correspond t o Definiti ons 2 and 3, respectiv ely , and case 3 is th e general case where the eavesdropper receive s signals from bot h the channels. B. Gaussian Model For a Gaussian relay eav esdropper channel with orthogon al compon ents, the signals Y 1 and Y rece iv ed at the relay and the desti nation resp ecti vely in each time sy mbol i ∈ { 1 , · · · , n } , are Y 1 [ i ] = h s,r X R [ i ] + Z 1 [ i ] (8) and Y [ i ] = h s,d X D [ i ] + h r,d X 2 [ i ] + Z [ i ] (9) where h k ,m is the channel gain from transmit ter k ∈ { s, r } to receive r m ∈ { r , d } , and where Z 1 and Z are zero mean unit variance Gaussian random variables. The transm itted s ignals X R , X D , and X 2 are subject to aver age power const raints giv en by E [ x 2 R ] ≤ P R , E [ 1 n P n i =1 x 2 D ] ≤ P D , and E [ 1 n P n i =1 x 2 2 ] ≤ P 2 , (10) where E [ . ] denotes expectation of its argument. The signals at th e ea vesdropper are Y 2 , 1 [ i ] = h s,e, 1 X R [ i ] 1 e, 1 + Z 2 , 1 [ i ] (11) Y 2 , 2 [ i ] = h s,e, 2 x D [ i ] 1 e, 2 + h r,e X 2 [ i ] 1 e, 2 + Z 2 , 2 [ i ] (12) where h s,e, 1 and h s,e, 2 are the channel gains from the source to the eavesdropper in the two orthogonal channels, h r,e is the channel gain from the relay t o the ea vesdropper , Z 2 , 1 and Z 2 , 2 7 are zero-mean unit variance Gauss ian random variables assu med t o be i ndependent of th e source and relay signal s, and 1 e,j = 1 if the eav esdropper can eav esdrop in orthogonal channel j = 1 , 2 0 0 otherwise. Throughout the sequel, we assum e that the channel gains are fixed and known at all nodes. For a relay channel with orth ogonal com ponents, the autho rs of [15 ] show that a strategy where the source uses each channel to send an independent message and the relay decodes t he message t ransmitted i n its channel, achieves capacity . Due to the fact that the relay has partial access to the source transmissions , this strategy is someti mes also referred to as partial decode and forwar d (see [16]). The achiev able scheme in v olves block Markov superpositi on encoding while the conv erse is dev eloped using the max-flo w , min-cut b ounds. The fol lowing propositi on summarizes this result. Pr opos ition 1 ([15 ]): The capacity of a relay channel with ort hogonal compon ent is given b y C = max min ( I ( X R ; Y 1 | X 2 ) + I ( X D ; Y | X 2 ) , I ( X R X D X 2 ; Y ) ) (13) where the maxim um is ov er all input distributions of t he form p ( x 2 ) p ( x R | x 2 ) p ( x D | x 2 ) . (14) For the Gaussian model, the bounds in (13) are maximized by jointl y Gaussian inputs transmit ting at the maximum power and subject to (14). Remark 2: While the con verse allows for all po ssible j oint distributions of X R , X D , and X 2 , from the form of the mutual inform ation expressions in (13), it suffices to cons ider distributions only of the form given by (14). W e use the standard no tation for entropy and mutual i nformation [17] and take all logarithm s to the base 2 so t hat our rate u nits are bi ts. For ease of exposition, we writ e C ( x ) to denote 1 2 log (1 + x ) , and write x + to d enote max( x, 0) . W e also write random variables with uppercase letters (e.g. W k ) and their realizations with t he corresponding lowercase lett ers (e.g. w k ). W e drop subscripts on probability distributions if the arguments are lowercase versions of t he corresponding rando m v ariabl es. Finall y , for bre vity , w e henceforth refer to the channel studied here as the ortho gonal relay ea vesdropper channel. 8 I I I . D I S C R E T E M E M O RY L E S S C H A N N E L : O U T E R A N D I N N E R B O U N D S In thi s sectio n, we develop outer and inner bounds for the secrecy capacity of the discrete- memoryless orthogonal relay eav esdropper chann el. The proof of the outer bounds follows along the same lines as that in [11, Theorem 1] for the full-duplex relay-eave sdropper channel and is specialized for t he orthogon al model considered here. The following theorem s ummarizes the bounds for the three cases in which the ea vesdropper can receive in eit her on e or both ort hogonal channels. Theor em 1: An outer bound on the secrecy capacity of the relay eav esdropper channel wi th orthogonal component s i s giv en by Case 1 : C s ≤ max[min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V R ; Y 2 | U )] + Case 2 : C s ≤ max[min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V D V 2 ; Y 2 | U )] + Case 3 : C s ≤ max[min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V R V D V 2 ; Y 2 | U )] + (15) where U, V D , V R and V 2 are auxiliary random variables, and the m aximum is over all jo int distributions sati sfying U → ( V R , V D , V 2 ) → ( X R , X D , X 2 ) → ( Y , Y 1 , Y 2 ) . Pr oof: Th e proof is extended from t he outer bound i n [11, Theorem 1] to include auxili ary random variables corresponding to each of the t ransmitted signals and is deve loped in Ap pendix A. Follo wing Proposition 1, a natural quest ion for the relay-eav esdropper channel wit h orthogonal components is whether the PDF strategy can achie ve the secrecy capacity . T o this end, we first dev elop the achiev abl e PDF secrecy rates for th e class of full-duplex relay-ea vesdropper channels and then specialize t he result for the orthogo nal model. The following theorem summarizes the inner bounds on the secrecy capacity achieved by PDF for the full-du plex (non-ortho gonal) relay-ea vesdropper channels. Theor em 2: An inner bound on th e secrecy capacity of a f ull-duplex relay eave sdropper channel, achiev ed using partial decode and forward, is given by C s ≥ min { I ( X 1 ; Y | X 2 , V ) + I ( V ; Y 1 | X 2 ) , I ( X 1 X 2 V ; Y ) } − I ( X 1 X 2 ; Y 2 ) (16) for all joi nt distributions of the form p ( v ) p ( x 1 | v ) p ( x 2 | v ) p ( y 1 , y | x 1 , x 2 ) . (17) 9 Pr oof: The proof is de veloped in Appendix B and uses block Markov superposition encoding at the source such that in each block, the relay decodes a part of the so urce message while the ea vesdropper has access to both source m essages. The following theorem specializes Theorem 2 for the ort hogonal relay-ea vesdropper channel. Theor em 3: An inner bound on the secrecy capacity of t he ort hogonal relay eav esdropper channel, achie ved using parti al decode and forward over all joint distributions of the form p ( x R , x D , x 2 ) , is given by Case 1 : C s ≥ min { I ( X D X R ; Y Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R ; Y 2 ) Case 2 : C s ≥ min { I ( X D X R ; Y Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X D , X 2 ; Y 2 ) Case 3 : C s ≥ min { I ( X D X R ; Y Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R ; Y 2 | X 2 ) − I ( X D , X 2 ; Y 2 ) (18) Pr oof: The proof is developed in Appendix C and in volves specializing th e bounds in Theorem 2 for the orth ogonal model. It i s further shown that the input dist ribution can be generalized to all joi nt probability distributions p ( x R , x D , x 2 ) . The bounds in (18) can be g eneralized by random izing the channel inputs . W e now prove that PDF with randomi zation achie ves the secrecy capacity . Theor em 4: The s ecrec y capacity of the relay chann el with orthogonal complements is Case 1 : C s = max[min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V R ; Y 2 | U )] + Case 2 : C s = max[min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V D V 2 ; Y 2 | U )] + Case 3 : C s ≤ max[min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V R V D V 2 ; Y 2 | U )] + (19) where U, V D , V R and V 2 are auxiliary random variables, and the m aximum is over all jo int distributions satisfyin g U → ( V R , V D , V 2 ) → ( X R , X D , X 2 ) → ( Y , Y 1 , Y 2 ) . Furthermore, for Case 3, C s ≥ [min { I ( V D V R ; Y Y 1 | V 2 U ) , I ( V D V 2 ; Y | U ) } − I ( V R ; Y 2 | V 2 U ) − I ( V D , V 2 ; Y 2 | U )] + (20) for all joi nt distributions satisfying U → ( V R , V D , V 2 ) → ( X R , X D , X 2 ) → ( Y , Y 1 , Y 2 ) . Pr oof: The upper bounds fol low from Theorem 1. For the lower bound, we prefix a mem- oryless channel wit h inputs V R , V D , and V 2 and transition probabil ity p ( x R , x D , x 2 | v R , v D , v 2 ) (this prefix can potent ially in crease th e achiev able s ecrec y rates as in [2, 11]). The time-sharin g random variable U ens ures that the set of achiev able rates is con vex. 10 Remark 3: In contrast to the non s ecrec y case, where t he ortho gonal channel model simplifies the cut-set bounds to match the inner PDF bounds, for the orthogonal relay-ea vesdropper model in which the eavesdropper receiv es in bot h channels, i.e., w hen the orthogo nal recei ver restrictions at the relay and int ended destination d o not apply to the ea vesdropper , in general, t he outer bound can be strictl y lar ger than the inner PDF bo und. In the following s ection, we illustrate these results wit h three examples. I V . E X A M P L E S Example 1: Consider a ort hogonal relay eav esdropper channel with X R = X D = X 2 = { 0 , 1 } . The outputs at the relay and destination are given by Y 1 = X R and (21) Y = X D X 2 , (22) while the output at the ea vesdropper is Y 2 , 1 = X R ( channel 1) and Y 2 , 2 = 1 if X D ≤ X 2 0 otherwise ( channel 2) . (23) Since th e desti nation can recei ve at most 1 bit in ev ery us e of the channel, the secrecy capacity of t his channel is at m ost 1 bit per channel use. W e now show t hat this secrec y capacity can be achie ved. In each channel u se, let the source send bit w ∈ { 0 , 1 } such th at X R = 0 , X D = w , and X 2 = 1 . Since X 2 = 1 , the receiver obtains w while the eavesdropper receiv es Y 2 , 1 = 0 and Y 2 , 2 = 1 irrespective of th e value of b it w . Hence, a perfect s ecrec y capacity o f 1 can be achie ved. The code design i n Exampl e 1 did not require random ization. W e now present an example where randomization is necessary . Example 2: Consider an orth ogonal relay eave sdropper channel where all the inpu t and output alphabets are the same and give n by { 0 , 1 } 2 . W e write X R = ( a R , b R ) , X D = ( a D , b D ) , and X 2 = ( a 1 , b 1 ) to denote the vector binary signals at the source and the relay . The outputs of this 11 channel, shown in Figure 2(a), at the relay , desti nation, and the ea vesdropper are given by Y = ( a D , b D ⊕ a 1 ) , (24) Y 1 = ( a R , b R ) , (25) Y 2 , 1 = ( a R , b R ) and (26) Y 2 , 2 = ( a 1 , b 1 ⊕ a D ) , (27) where ⊕ denotes the binary XOR operation. The capacity of this channel is at m ost 2 bits per channel use as the dest ination, via Y , can recei ve at most 2 bits per channel use. W e will now show that a secrecy capacity of 2 bits per channel use can be achie ved. Cons ider the following coding scheme. In ev ery chann el us e, the relay flips an unbiased coin to generate a bit n ∈ { 0 , 1 } such that its transm itted signal is X 2 = (0 , n ) . In ev ery use of the channel, the source transm its 2 bits, denoted as w 1 and w 2 , using X R = (0 , 0) and X D = ( w 1 , w 2 ) . For these transmitted signals, the receiv er and ea vesdropper recei ve Y = ( w 1 , w 2 ) , (28) Y 2 , 1 = (0 , 0) and (29) Y 2 , 2 = (0 , n ⊕ w 1 ) . (30) Thus, the receiv er receives b oth bits while the eavesdropper is unable to decode any information due to the randomness of n . This is an example wh ere transmitti ng a random code from the relay is required to achie ve the s ecrec y capacity . In the above two examples, th e source to relay l ink was compl etely av ailable to the eav es- dropper and hence the relay could at best be just used t o send random bits. In t he next example, we show that the secrecy capacity is achieve d by the relay transmi tting a p art o f the message as well as a random si gnal. Example 3: Consider an orthogonal relay eav esdropper chann el where the in put and output signals at the source, relay , and destinati on are bi nary two-tuples whil e Y 2 , 1 and Y 2 , 2 at the 12 Y X 2 a R b R a D b D Y 1 a 1 b 1 Y 2,2 Y 2,1 X R X D (a) E xample 2 Y 1 Y X D a D X R a R b R b 1 X 2 a 1 Y 2,2 Y 2,1 (b) E xample 3 Fig. 2. Orthogonal relay eavesdropp er channel model of Examples 2 and 3. ea vesdropper are binary alph abets. W e write X R = ( a R , b R ) , X D = a D and X 2 = ( a 1 , b 1 ) to denote the vector b inary sig nals at the s ource and t he relay . Th e o utputs at the relay , dest ination and the eav esdropper are also vector binary signals given by Y = ( a 1 , a D ) , (31) Y 1 = ( a R , b R ) , (32) Y 2 , 1 = ( b R ) and (33) Y 2 , 2 = ( b 1 ⊕ a D ) , (34) as shown i n Figure 2(b). As in the previous example, the capacity of t his channel is also at most 2 bits per channel use. W e now show that a secrecy capacity of 2 bits per channel use can b e achie ved for th is e xample channel. Consider the following coding scheme: in the i th use of the channel, the source encodes 2 bits, denoted as w 1 ,i and w 2 ,i as X R = ( w 1 ,i , 0) and X D = ( w 2 ,i ) . The relay recei ves w 1 ,i − 1 in the pre vious use of the channel. Furthermore, in each channel use, it also generates a u niformly random bit n i , and transmits X 2 = ( w 1 ,i − 1 , n i ) . (35) 13 W ith these transmitted signals, the receiv ed signals at the receiv er and the ea vesdropper are Y = ( w 1 ,i − 1 , w 2 ,i ) , (36) Y 2 , 1 = (0 ) and ( 37) Y 2 , 2 = ( n i ⊕ w 2 ,i ) . (38) Thus, over n + 1 uses o f the channel the destination recei ves all 2 n + 1 bits transmit ted by t he source. On the o ther hand, in eve ry use of th e chann el, the ea vesdropper cannot decode either source bit. V . G AU S S I A N M O D E L A. Inner and Outer Bounds W e now deve lop inner and outer bounds for the Gaus sian orthogon al relay eav esdropper channel. Determini ng the opt imal input di stribution for all the auxiliary rando m variables i n the outer bounds in T heorem 4 is not st raightforward. T o this end, we dev elop new outer bo unds using a recent result on the s ecrec y capacity of the class of Gauss ian mu ltiple inp ut, m ultiple output, multi -antenna eav esdropper channels (see [4–6]). The class of MIMOM E channels is characterized by a sin gle source with an m × 1 vector input X and k × 1 and t × 1 vector o utputs Y and Y e at the int ended destination and eav esdropper , respectiv ely , given by Y [ i ] = HX [ i ] + Z [ i ] and Y e [ i ] = H e X [ i ] + Z e [ i ] (39) where in every channel u se i , Z [ i ] and Z e [ i ] are zero-mean Gaussian vectors wit h id entity cov ariance matrices that are independent across time symbols. The channel input satisfies an a verage transmit power constraint : 1 n X n i =1 k x k 2 ≤ P . (40) In app lying t he multi -antenna secrecy capacity results, we de velop an outer bound in which the source and relay are mo deled jointly as a multi -antenna transm itter . Howe ver , unlike t he ave rage power constraint for the MIMOME channels in (40), our outer b ound requi res a per antenna power constraint. T o this end, we appl y the resul ts dev eloped in [5] in which a more g eneral transmitter cova riance constraint is considered such that 1 n X n i =1 x [ i ] x T [ i ] S (41) 14 where S is a positive s emidefinite matrix and A B denotes that B − A is a posi tiv e semidefinite matrix. The secrecy capacity of this channel is su mmarized in the following theorem. Lemma 1 ([5]): The secrecy capacity of the MIMOME channel of (39) subject to (41) is giv en b y C s = max 0 K X S 1 2 log det I + HK X H T − 1 2 log det I + H e K X H T e . (42) Remark 4: The expression i n (42) can also be written as C s = max[ I ( X ∗ ; Y ) − I ( X ∗ ; Y e )] (43) where he maximu m is ov er all X ∗ ∼ N (0 , K X ) . W e now present an ou ter bound on the Gaus sian orthogonal relay ea vesdropper channel u sing Lemma 1. Theor em 5: An outer bound on th e secrecy capacity of the Gaussian orthogonal relay eaves- dropper channel is given by Case 1 : C s ≤ max[ I ( X D X 2 ; Y ) − I ( X R ; Y 2 )] (44a) Case 2 : C s ≤ max[ I ( X D X 2 ; Y ) − I ( X D X 2 ; Y 2 )] (44b) Case 3 : C s ≤ max[ I ( X D X 2 ; Y ) − I ( X R X D X 2 ; Y 2 )] (44c) where t he maxim um is over all [ X R X D X 2 ] T ∼ N (0 , K X ) where K X = E [ XX T ] has di agonal entries that satisfy (10). Remark 5: In (44a) and (44c), t he X ∗ R maximizing the outer bound on the secrecy capacity is X ∗ R = 0 . On th e other hand, X ∗ R can be chosen to be arbitrary for (44b). Pr oof: An outer bound on the secrecy capacity of the relay eavesdropper channel results from assu ming that the source and relay can cooperate over a noiseless link without causality constraints. Un der this assumpti on, the problem reduces to that of a MIMOME chann el. Thus , applying Lemma 1 and usi ng t he form i n (43), for X = [ X R X D X 2 ] T ∼ N (0 , K X ) , th e secrecy capacity can be upper bounded as C s ≤ max[ I ( X R X D X 2 ; Y ) − I ( X R X D X 2 ; Y 2 )] (45) = max[ I ( X D X 2 ; Y ) + I ( X R ; Y | X D X 2 ) − I ( X R X D X 2 ; Y 2 )] (46) = max[ I ( X D X 2 ; Y ) − I ( X R X D X 2 ; Y 2 )] (47) 15 where (47 ) fol lows from th e orthogonal mod el in (5). Finally , applying th e cond itions on the ea vesdropper rece iv er for the three cases s implifies the bounds in (47) t o (44). The PDF inner bounds dev eloped i n Section III for the discrete m emoryless case can be applied to the Gaussian model with Gaussian inputs at the source and relay . In fact, for all three cases, the inner bou nds require taking a mi nimum of two rates, one achiev ed jointly by the sou rce and relay at the dest ination and t he other achiev ed by the source at the relay and destinatio n. Comparing the inn er bounds in (18) with the outer bounds in (44), for those channels in which the so urce and relay are clustered close enough that the b ottle-neck link i s the combined source- relay link to the d estination and the eav esdropper overhear s on ly the channel from the s ource and the relay to the dest ination, the secrecy capacity can be achiev ed. This is summarized in the following theorem. Theor em 6: For a class of clustere d orthogonal Gauss ian relay channels with I ( X D X 2 ; Y ) < max p ( x R | x D ,x 2 ) I ( X D X R ; Y Y 1 | X 2 ) , (48) the secrecy capacity for case 2 is achieved by PDF and is given by Case 2 : C s = max[ I ( X D X 2 ; Y ) − I ( X D , X 2 ; Y 2 )] (49) where the maxim um is ov er X = [ X R X D X 2 ] T ∼ N (0 , K X ) . For a relay channel wi thout secrecy constraints, the cut-set outer bounds are equiv alent to two mu ltiple-input m ultiple-outpu t (MIMO) bounds, one t hat results from assum ing a noiseless source-relay link and the other t hat results from assum ing a noiseless relay-destinat ion li nk. Under a secrecy constraint , t he ou ter bound in Theorem 5 is b ased on t he ass umption of a noiseless s ource-relay link. The corresponding bound with a nois eless relay-destination l ink remains unknown. W e now consider a sub -class of Gaus sian orthogon al relay eav esdropper channels for which h s,r = 0 . For this su b-class, the s ource does not send any messages on channel 1 , i.e., X R = 0 . Such a sub-class is a sub set of a larger sub-class of channels with very noisy unreliable links from the sou rce to the relay . W e present an up per bound on the secrecy capacity for this sub- class and show that the noise-forwarding strategy i ntroduced in [11] achiev es this outer bound. Central to our proof is an additi onal constraint introduced in d e veloping t he outer bounds on the ea vesdropper that it does not decode the relay transmissi ons. Clearly , limiting the eavesdropper 16 capabilities can only improve the secrecy rates, and thus, an outer bound for this channel with a constrained ea vesdropper is also an ou ter bound for the original channel (with h s,r = 0 in both cases) with an uncons trained eav esdropper . W e show that the outer bound for the constrained channel can be achieved by the strategy of noise-forwarding deve loped for t he unconstrained channel. Theor em 7: The secrecy capacity of a s ub-class of G aussian orthogonal relay eav esdropper channels with h s,r = 0 for Cases 2 and 3 is given by C s = max E [ X D ] 2 ≤ P D ,E [ X 2 ] 2 ≤ P 2 min C | h s,d | 2 E [ X 2 D ] + | h r,d | 2 E [ X 2 2 ] − C | h s,e, 2 | 2 E [ X 2 D ] + | h r,e | 2 E [ X 2 2 ] , C ( | h s,d | 2 E [ X 2 D ]) − C | h s,e, 1 | 2 E [ X 2 D ] / (1 + | h r,e | 2 E [ X 2 2 ]) . (50) Pr oof: Outer B ound : An outer b ound on the secrec y capacity is ob tained b y applying Theorem 5 for Cases 2 and 3 as C s ≤ max[ I ( X D X 2 ; Y ) − I ( X D X 2 ; Y 2 )] (51) = max E [ X D ] 2 ≤ P D ,E [ X 2 ] 2 ≤ P 2 [ C ( | h s,d | 2 E [ X 2 D ] + | h r,d | 2 E [ X 2 2 ]) − C ( | h s,e, 2 | 2 E [ X 2 D ] + | h r,e | 2 E [ X 2 2 ])] (52) where (52) holds because h s,r = 0 implies X R = 0 . This foll o ws from th e fact that du e to a lack of a comm unication l ink between the s ource and the relay , i.e., h s,r = 0 , th e relay is oblivious to the source transmissions. Since t he relay and the sou rce do not share common random ness, one can set X R = 0 . Further , s ince X 2 depends o n X D only via X R and X R = 0 , X 2 is independent of X D . Finally , the optimality of Gaussian signalin g follows from Theorem 5. W e now develop a second outer bound und er t he assumptio n t hat the relay and the destin ation hav e a n oiseless channel such that t hey act like a two-antenna receiv er . One can alt ernately view this as an improved channel that resul ts from having a genie that shares perfectly the transmitted and receive d si gnals at the relay wi th the destinat ion. Since X 2 is i ndependent of X D , the dest ination can perfectly cancel X 2 from it s recei ved sig nal, and th us, from (9), the ef fecti ve received si gnal at the destination can be written as Y ′ = h s,d X D + Z . (53) On the other hand for the constrained ea vesdropper , since the relay’ s signal X 2 acts as in terference and is independent of X D , t he information received at the ea vesdropper is mi nimized when X 2 17 is the worst case noise, i.e., when it is Gaussian di stributed [18, Th eorem II.1]. The equiv alent signal receiv ed at the eav esdropper is then Y ′ 2 , 2 = h s,e, 2 X D + q | h r,e | 2 E [ X 2 2 ] + 1 Z ′ 2 , 2 (54) where Z ′ 2 , 2 is Gaus sian wi th zero mean and uni t variance. Thu s, the constrained ea vesdropper channel sim plifies to a MIMOM E channel wi th a single-antenna sou rce transmitti ng X D and single-antenna recei ver and eavesdropper receiving Y ′ and Y ′ 2 , 2 , respectiv ely . For this channel, from Lemm a 1 , the s ecrec y capacity of this constrained eavesdropper channel is upper bound ed as C s ≤ max E [ X D ] 2 ≤ P D ,E [ X 2 ] 2 ≤ P 2 [ C ( | h s,d | 2 E [ X 2 D ]) − C | h s,e, 1 | 2 E [ X 2 D ] / (1 + | h r,e | 2 E [ X 2 2 ]) ] . (55) Finally , since (55) is an up per bo und for t he channel with an eavesdropper constrained t o ignore X 2 , it is als o an upper bound for th e channel in which the eav esdropper is not constrained. Inner Bound : The lower bo und follows from th e noi se forwarding strategy int roduced in [11, Theorem 3]. In this strategy , the relay sends codewords independent of the source m essage, which helps in confus ing the eave sdropper . The noise forwarding strategy transforms the relay- ea vesdropper channel into a compound mul tiple access channel , where the so urce/relay t o the recei ver is the first mul tiple access channel and the source/relay to the ea vesdropper is t he second one. B. Illustration of Results W e ill ustrate ou r results for the Gaussian model for a cl ass of l inear networks in which the source is placed at the origin and the destinati on i s unit distance from the source at (1 , 0) . The ea vesdropper is at (1 . 5 , 0) . The channel gain h m,k , between transmitt er m and recei ver k , for each m and k , is modeled as a d istance dependent path-loss gain given by h m,k = 1 d α/ 2 m,k for all m ∈ { s, r } , k ∈ { r , d, e } (56) where α is the path-loss exponent. Th e m aximum achiev able PDF secrecy rate is plotted as a function of the relay position along the li ne connecting the so urce and the eavesdropper as shown in Figure V -B. Furthermore, as a baseline assum ing th e relay does not transmit, i.e., X R = 0 , the secrecy capacity of the resulting direct li nk and the wire-tap channel for cases 2 18 and 3 , respecti vely , are included in all three plots in Fig. V - B. The rates are plotted in separate sub-figures for t he three cases in which the eav esdropper receive s signals in only one or both channels. In all cases, the pat h loss exponent α is set to 2 and t he ave rage power constraint on X R , X D , and X 2 is set t o unity . In addition to PDF , the secrecy rate achieved by noise forwarding (NF) is also plott ed. −1 −0.5 0 0.5 1 1.5 2 2.5 0 1 2 3 4 5 6 Location of the relay Secrecy Rate Upper Bound − Case 1 Lower Bound − Case 1 Direct link Eavesdropper Destination Source (a) C ase 1. −1 −0.5 0 0.5 1 1.5 2 2.5 0 1 2 3 4 5 6 Location of the relay Secrecy Rate Upper Bound − band 2 Lower Bound − band 2 (PDF) Lower Bound − band 2 (NF) Wiretap Channel Eavesdropper Destination Source (b) Case 2. −1 −0.5 0 0.5 1 1.5 2 2.5 0 1 2 3 4 5 6 Location of the relay Secrecy Rate Upper Bound − band 2 Lower Bound − band 2 (PDF) Lower Bound − band 2 (NF) Wiretap Channel Eavesdropper Destination Source (c) C ase 3. Fig. 3. Source is at (0 , 0) , destination at (1 , 0) and eavesdrop per is at (1 . 5 , 0) . A distance fading model with α = 2 is taken and po w er constraints for X R , X D and X 2 are all unity . In Fig V -B , for all three cases, t he PDF secrecy rates are o btained by cho osing t he inp ut sign al X = [ X R X D X 2 ] T to be G aussian di stributed and n umerically optim izing the rates over the cov ariance matrix K X = E [ XX T ] (more precisely t he three variances of X R , X D , X 2 and th e pairwise correlation among these three variables). W e observe that the numerical results m atch the theoretical capacity result for Case 2 that PDF is opti mal when t he relay i s close to the source. Further , the upper bo unds for Case 2 and Case 3 are the same as seen also in (44b)- 19 (44c). On the other hand, when th e relay is farther aw ay than the ea vesdropper and destination are from t he source, there are no gains achieve d by using the relay relative to th e non-relay wiretap secrecy capacity . Finally , for cases 2 and 3 , NF performs b etter t han PDF when t he relay is closer to the d estination. V I . C O N C L U S I O N S W e ha ve de veloped bound s on t he secrec y capacity of relay eavesdropper channels wi th orthogonal components in the presence of an additi onal p assiv e ea vesdropper for both th e discrete memoryl ess and Gaus sian channel m odels. Our results depend on the capability of the ea vesdropper to ov erhear either or both of the two orthogonal channels that the source uses for its transmissions. For t he discrete m emoryless model, wh en the eavesdropper is restricted to recei ving in only one of the two channels, we have shown that the secrecy capacity is achie ved by a partial decode-and-forward strategy . For the Gaussian model, we hav e dev eloped a new outer bound using recent results on the secrecy capacity of Gauss ian MIMOME channels. When the eavesdropper is restricted to overhea ring on t he channel from the source and the relay t o the destin ation, our bo und is tight fo r a sub-class of channels where the source and the relay are clustered such th at the combined l ink from t he source and the relay to the destinati on is the bottleneck. Furthermore, for a sub-class where t he source-relay link is no t used, we hav e developed a new MIMOME-based outer bou nd that matches the secrecy rate achieve d by the noise forwarding strategy . A natu ral extension to t his model is to stu dy t he secrecy capacity of orthogonal relay channels with multip le relays and mu ltiple eavesdroppers (see, for example, [19 ]). Al so, the problem of dev eloping an additi onal ou ter b ound that considers a noiseless relay desti nation link remains open for the channel s tudied here. V I I . A C K N OW L E D G E M E N T S The authors wish to thank Elza Erkip of Polytechnic Institute of NYU and Lifeng Lai and Ruoheng Liu of Princeton University for u seful discussions related to this paper . A P P E N D I X A 20 P RO O F O F T H E O R E M 1 In thi s section, we will prove the upper bounds on t he secrecy capacity for all th e three cases. Follo wing a proof similar to that in [11, Theorem 1], we bound th e equi v ocation as nR e ≤ n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + nδ n . (57) Now , let J be a random v ariabl e uniforml y dis tributed over { 1 , 2 , · · · , n } and set U = J Y i − 1 Y n 2 ,i +1 , V R = J Y 2 ,i +1 W 1 , V D = J Y n 2 ,i +2 W 1 , V 2 = J Y i − 1 , Y 1 = Y 1 ,J , Y 2 = Y 2 ,J and Y = Y J . W e speciali ze the bounds in (57) separately for each case. A. Case 1 From (57), we hav e R e ≤ 1 n n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +2 , Y i − 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y 2 ,i +1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = I ( V D , V 2 ; Y | U ) − I ( V R ; Y 2 | U ) + δ n . (58) Furthermore, R e ≤ 1 n n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y 2 ,i +1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n ≤ 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y i , Y 1 ,i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y 2 ,i +1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = I ( V D , V R , V 2 ; Y , Y 1 | V 2 , U ) − I ( V R ; Y 2 | U ) + δ n . (59) This proves the upp er bound for case 1. 21 B. Case 2 From (57), we hav e R e ≤ 1 n n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +2 , Y i − 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y n 2 ,i +2 , Y i − 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = I ( V D , V 2 ; Y | U ) − I ( V D , V 2 ; Y 2 | U ) + δ n . (60) Furthermore, R e ≤ 1 n n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y n 2 ,i +2 , Y i − 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n ≤ 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y i , Y 1 ,i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y n 2 ,i +2 , Y i − 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = I ( V D , V R , V 2 ; Y , Y 1 | V 2 , U ) − I ( V D , V 2 ; Y 2 | U ) + δ n . (61) This proves the upp er bound for case 2. C. Case 3 From (57), we hav e R e ≤ 1 n n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +2 , Y i − 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = I ( V D , V 2 ; Y | U ) − I ( V R , V D , V 2 ; Y 2 | U ) + δ n . (62) 22 Furthermore, R e ≤ 1 n n X i =1 [ I ( W 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n ≤ 1 n n X i =1 [ I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y i , Y 1 ,i | Y i − 1 , Y n 2 ,i +1 ) − I ( W 1 , Y n 2 ,i +1 , Y i − 1 ; Y 2 ,i | Y i − 1 , Y n 2 ,i +1 )] + δ n = I ( V D , V R , V 2 ; Y , Y 1 | V 2 , U ) − I ( V D , V 2 ; Y 2 | U ) + δ n . (63) This proves the upper bound for case 3. For perfect s ecrec y , s etting R 1 = R e yields the upper bound on the secrecy capacity . A P P E N D I X B P RO O F O F T H E O R E M 2 : P D F F O R R E L A Y E A V E S D R O P P E R C H A N N E L Random Coding: 1) Generate 2 n ( I ( X 2 ; Y ) − ǫ ) independent and identi cally distributed (i.i.d.) x 2 ’ s, each with prob- ability p ( x 2 ) = Π n i =1 p ( x 2 i ) . Label them x 2 ( m ) , m ∈ [1 , 2 n ( I ( X 2 ; Y ) − ǫ ) ] . 2) For ea ch x 2 ( m ) , generate 2 nR 1 i.i.d. v ’ s, each with probability p ( v | x 2 ( m )) = Π n i =1 p ( v i | x 2 i ( m )) . Label these v ( w ′ | m ) , w ∈ [1 , 2 nR 1 ] . 3) For ev ery v ( w ′ | m ) , generate 2 nR 2 i.i.d. x 1 ’ s, each with probability p ( x 1 | v ( w ′ | m )) = Π n i =1 p ( x 1 i | v i ( w ′ | m )) . Label these x 1 ( w ′′ | m, w ′ ) , w ′′ ∈ [1 , 2 nR 2 ] . Random P artit ion : Randoml y partition the set { 1 , 2 , ..., 2 nR 1 } into 2 n ( I ( X 2 ; Y ) − ǫ ) cells S m . Encoding : Let w i be th e message to be sent in bl ock i where the t otal numb er of m es- sages is 2 n ( R 1 + R 2 − I ( X 1 X 2 ; Y 2 )) . Further , l et g i = ( w i , l i ) where l i ∈ { 1 , 2 , ..., 2 nI ( X 1 X 2 : Y 2 ) } . W e can furt her partit ion g i into two p arts ( w ′ i , w ′′ i ) of rates R 1 and R 2 respectiv ely . Assume that ( y 1 ( i − 1) , v ( w ′ i − 1 | m i − 1 ) , x 2 ( m i − 1 )) are jointly ǫ − typical and w ′ i − 1 ∈ S m i . Then the codew ord ( x 1 ( w ′′ i | m i , w ′ i ) , x 2 ( m i )) will be t ransmitted in block i . Decoding : At the end of blo ck i , we have the fol lowing: 1) The receiver estimates m i by l ooking at jointly ǫ -typical x 2 ( m i ) wi th y i . For sufficiently lar ge n , this decoding step can be done with arbitrarily sm all probabil ity of error . Let the estimate of m i be ˆ m i . 23 2) The recei ver calculates a set L 1 ( y ( i − 1)) of w ′ such that w ′ ∈ L 1 ( y ( i − 1)) if ( v ( w ′ | m i − 1 ) , y ( i − 1)) are jo intly ǫ -typical. The receive r then declares that w ′ i − 1 was sent in block i − 1 if ˆ w ′ i − 1 ∈ S m i ∩ L 1 ( y ( i − 1)) . The probability that ˆ w ′ i − 1 = w ′ i − 1 with arbitrarily high probability provided n is suffi ciently large and R 1 < I ( X 2 ; Y ) + I ( V ; Y | X 2 ) − ǫ . 3) The recei ver declares that w ′′ i − 1 was s ent in block i − 1 if ( x 1 ( ˆ w ′′ i − 1 | ˆ m i − 1 , ˆ w ′ i − 1 ) , y ( i − 1)) are joint ly ǫ − typical. ˆ w ′′ i − 1 = w ′′ i − 1 with high probabili ty if R 2 = I ( X 1 ; Y | X 2 , V ) − ǫ and n is sufficiently lar ge. 4) The relay upon receiving y 1 ( i ) declares that ˆ w ′ was re cei ved if ( v ( ˆ w ′ | m i ) , y 1 ( i ) , x 2 ( m i )) are jointly ǫ − typical. w ′ i = ˆ w ′ with hi gh probability if R 1 < I ( V ; Y 1 | X 2 ) and n i s sufficiently lar ge. Th us, the relay knows t hat w ′ i ∈ S m i +1 . Thus, we obtain R 1 < I ( X 2 ; Y ) + I ( V ; Y | X 2 ) − ǫ, (64) R 1 < I ( V ; Y 1 | X 2 ) and (65) R 2 = I ( X 1 ; Y | X 2 , V ) − ǫ. (66) Therefore, the rate of transm ission from X 1 to Y is bounded by R = R 1 + R 2 − I ( X 1 X 2 ; Y 2 ) (67) = min { I ( X 1 ; Y | X 2 , V ) + I ( V ; Y 1 | X 2 ) , I ( X 1 X 2 V ; Y ) } − I ( X 1 X 2 ; Y 2 ) . (68) Equivocation Computation : From [11, Theorem 2, Equation (41)], we have H ( W 1 | Y 2 ) ≥ H ( X 1 ) − I ( X 1 , X 2 ; Y 2 ) − H ( X 1 , X 2 | W 1 , Y 2 ) . (69) Consider H ( X 1 , X 2 | W 1 , Y 2 ) . Since we know W 1 , the on ly uncertainty is the knowledge of l i which can be decoded f rom Y 2 with a rbitrarily small probabi lity of err or since l i ∈ { 1 , .., 2 nI ( X 1 X 2 ; Y 2 ) } . Hence, H ( W 1 | Y 2 ) ≥ n ( R 1 + R 2 ) − I ( X 1 , X 2 ; Y 2 ) = nR (70) thus giving R e = R and hence we get perfect secrecy . Thus, the secrecy rate is give n by R = min { I ( X 1 ; Y | X 2 , V ) + I ( V ; Y 1 | X 2 ) , I ( X 1 X 2 V ; Y ) } − I ( X 1 X 2 ; Y 2 ) . (71) 24 A P P E N D I X C P RO O F O F T H E O R E M 3 : P D F F O R R E L A Y E A V E S D R O P P E R C H A N N E L W I T H O RT H O G O N A L C O M P O N E N T S From Theorem 2, a secrecy rate of R = min { I ( X 1 ; Y | X 2 , V ) + I ( V ; Y 1 | X 2 ) , I ( X 1 X 2 V ; Y ) } − I ( X 1 X 2 ; Y 2 ) (72) can be achieve d by partial decode and forward. Let X 1 = ( X R , X D ) and V = X R such that the inpu t distribution i s of t he form p ( x 2 ) p ( x R | x 2 ) p ( x D | x 2 ) . The achie va ble secrecy rate is t hen giv en b y R = min { I ( X R X D ; Y | X 2 , X R ) + I ( X R ; Y 1 | X 2 ) , I ( X R X D X 2 ; Y ) } − I ( X R X D X 2 ; Y 2 ) (73) = min { I ( X D ; Y | X 2 , X R ) + I ( X R ; Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R X D X 2 ; Y 2 ) (74) = min { I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R X D X 2 ; Y 2 ) . (75) The equality in (75) follows from the fact that X D − X 2 − X R is a Markov chain. W e further specialize the bounds for th e three cases based on the recei ving capability of the eave sdropper . A. Case 1 R = min { I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R ; Y 2 ) . (76) The maximizatio n of the expression to the right of the equ ality i n (76) over p ( x D , x R , x 2 ) = p ( x 2 ) p ( x R | x 2 ) p ( x D | x 2 ) is equi va lent to maximizing over the more general distribution p ( x D , x R , x 2 ) , and hence forth, without l oss of generality we consider the general probability distrib ution p ( x D , x R , x 2 ) . W e no w prov e that I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) ≥ I ( X D X R ; Y Y 1 | X 2 ) which completes t he 25 proof of thi s p art of the theorem. W e hav e I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) = H ( Y | X 2 ) − H ( Y | X 2 X D ) + I ( X R ; Y 1 | X 2 ) ≥ H ( Y | X 2 Y 1 ) − H ( Y | X 2 X D ) + I ( X R ; Y 1 | X 2 ) = H ( Y | X 2 Y 1 ) − H ( Y | X 2 X D X R Y 1 ) + I ( X R ; Y 1 | X 2 ) = I ( Y ; X D X R | X 2 Y 1 ) + I ( X R ; Y 1 | X 2 ) (77) = I ( Y ; X D X R | X 2 Y 1 ) + I ( X D ; Y 1 | X 2 X R ) + I ( X R ; Y 1 | X 2 ) = I ( Y ; X D X R | X 2 Y 1 ) + I ( X R X D ; Y 1 | X 2 ) = I ( Y Y 1 ; X D X R | X 2 ) . (78) B. Case 2 R = min { I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X D X 2 ; Y 2 ) . Note that maximizati on of above term over p ( x D , x R , x 2 ) = p ( x 2 ) p ( x R | x 2 ) p ( x D | x 2 ) is equiv- alent to maxim izing over general p ( x D , x R , x 2 ) and henceforth, witho ut los s of generalit y we consider the general probabil ity distribution p ( x D , x R , x 2 ) . W e no w prov e that I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) ≥ I ( X D X R ; Y Y 1 | X 2 ) which completes t he proof of thi s p art of the theorem. W e hav e I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) = H ( Y | X 2 ) − H ( Y | X 2 X D ) + I ( X R ; Y 1 | X 2 ) ≥ H ( Y | X 2 Y 1 ) − H ( Y | X 2 X D ) + I ( X R ; Y 1 | X 2 ) = I ( Y Y 1 ; X D X R | X 2 ) , (79) where the last step follows as was sho wn earlier in (77). C. Case 3 R = min { I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R ; Y 2 | X 2 X D ) − I ( X D X 2 ; Y 2 ) = min { I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) , I ( X D X 2 ; Y ) } − I ( X R ; Y 2 | X 2 ) − I ( X D X 2 ; Y 2 ) . (80) 26 Note that maximizati on of above term over p ( x D , x R , x 2 ) = p ( x 2 ) p ( x R | x 2 ) p ( x D | x 2 ) is equiv- alent to maxim izing ov er general p ( x D , x R , x 2 ) . W e no w prov e that I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) ≥ I ( X D X R ; Y Y 1 | X 2 ) which completes t he proof of thi s p art of the theorem. W e hav e I ( X D ; Y | X 2 ) + I ( X R ; Y 1 | X 2 ) = H ( Y | X 2 ) − H ( Y | X 2 X D ) + I ( X R ; Y 1 | X 2 ) ≥ H ( Y | X 2 Y 1 ) − H ( Y | X 2 X D ) + I ( X R ; Y 1 | X 2 ) = I ( Y Y 1 ; X D X R | X 2 ) , (81) where the last step follows as was sho wn earlier in (77). R E F E R E N C E S [1] A. W yner , “The wire-tap channel, ” Bell Syst. T ech. J . , vol. 54, no. 8, pp. 1355–138 7, 1975. [2] I. Csisz ´ ar and J. K ¨ orne r , “Broadcast channels with confidential messages, ” IE EE T ran s. Inform. Theory , vol. 24, no. 3, pp. 339–34 8, May 1978. [3] E. T ekin and A. Y ener, “The general Gaussian multiple access and two-way wi re-tap channels: Achie v able rates and cooperati ve jamming, ” IEE E T rans. Inform. Theory , vol. 54, no. 6, pp. 2735–2751 , Jun. 2008. [4] A. Khisti and G. W . W ornell, “T he MIMOME channel, ” in P r oc. 45th Annual Allerton Conf. Comm., Contr . and Computing , Monticello, IL, S ep. 2007. [5] T . Liu and S. Shamai, “ A note on the secrecy capacity of the multi-antenna wir etap channel, ” arXi v:0710.41 05v1 , Oct. 2007. [6] F . Oggier and B. Hassibi, “The secrecy capacity of t he MIMO wiretap channel, ” in Pr oc. IEEE International Symposium on Information T heory , T oronto, ON, Canada, Jul. 2008, pp. 524–528 . [7] M. Bloch and A. Thangaraj, “Confidential messages to a cooperativ e relay , ” in Proc . IEEE Information T heory W orkshop , Porto, Portugal, May 2008, pp. 154–158. [8] Y . L iang and H. V . P oor , “Multiple-access channels with confidential messages, ” IEE E Tr ans. Inform. Theory , vol. 54, no. 3, pp. 976–1002, Mar . 2008. [9] Y . Liang, H. V . Poor, and S . Shamai, “Secure communication ov er fading channels, ” IEEE T rans. Inform. Theory , vol. 54, no. 6, pp. 2470–2492, Jun. 2008. [10] Y . Liang, A. Somekh-Baruch, H. V . Poor , S. Shamai, and S. V erd ´ u, “Capacity of cognitive interference channels w ith and without secrecy , ” IEEE T rans. Inform. T heory , vol. 55, no. 2, pp. 604–619 , Feb . 2009. [11] L. Lai and H. El Gamal, “The relay-eavesdrop per channel: cooperation for secrecy , ” IEEE T rans. Inform. Theory , vol. 54, no. 9, pp. 4005–4019, Sep. 2008. [12] M. Y uksel and E . Erkip, “The rel ay channel with a wire-tapper , ” in Proc. 41st Annual Conferen ce on Information Sciences and Systems (CISS) , Mar . 2007, pp. 13–18. [13] Y . O ohama, “Relay channels with confidential messages, ” arXiv , vol. abs/cs/06111 25, 2006. [14] X. He and A. Y ener , “On the equiv ocation region of relay channels with orthogonal components, ” in P r oc. 41st Annual Asilomar Conf. Signals, Systems, and Computers , Pacific Grove , CA, Nov . 2007. 27 [15] A. El Gamal and S . Zahedi, “Capacity of r elay channels with orthogonal components, ” IEE E T rans. Inform. Theory , vol. 51, no. 5, pp. 1815–1817, May 2005. [16] G. Kramer , “Models and theory for relay channels with receive constraints, ” in Pr oc. 42nd Annual Allerton C onf. on Commun., C ontr ol, and Computing , Monticello, IL, Sep. 2004. [17] T . M. Cov er and J. A. Thomas, Elements of Information Theory . Ne w Y ork: John W iley and Sons, Inc., 1991. [18] S. Diggav i and T . Cover , “The worst additiv e noise under a cov ariance constraint, ” IEEE Tr ans. Inform. T heory , vol. 47, no. 7, pp. 3072–3081, Nov . 2001. [19] V . Aggarwal, L. Sankar , A. R. Calderbank, and H. V . P oor , “Information secrecy from multiple eavesd roppers in orthogonal relay channels, ” in P r oc. IEEE International Symposium on Information Theory , S eoul, Korea, Jun.-Jul. 2009.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment